Source IP-based rule failing to block traffic from iPad
-
Hi folks,
I have a simple rule to block all traffic from an iPad host (192.168.1.6). But it is failing to block all traffic from browsers or apps like YouTube app. Can someone please help me understand why traffic is not getting blocked based on this source IP filter-
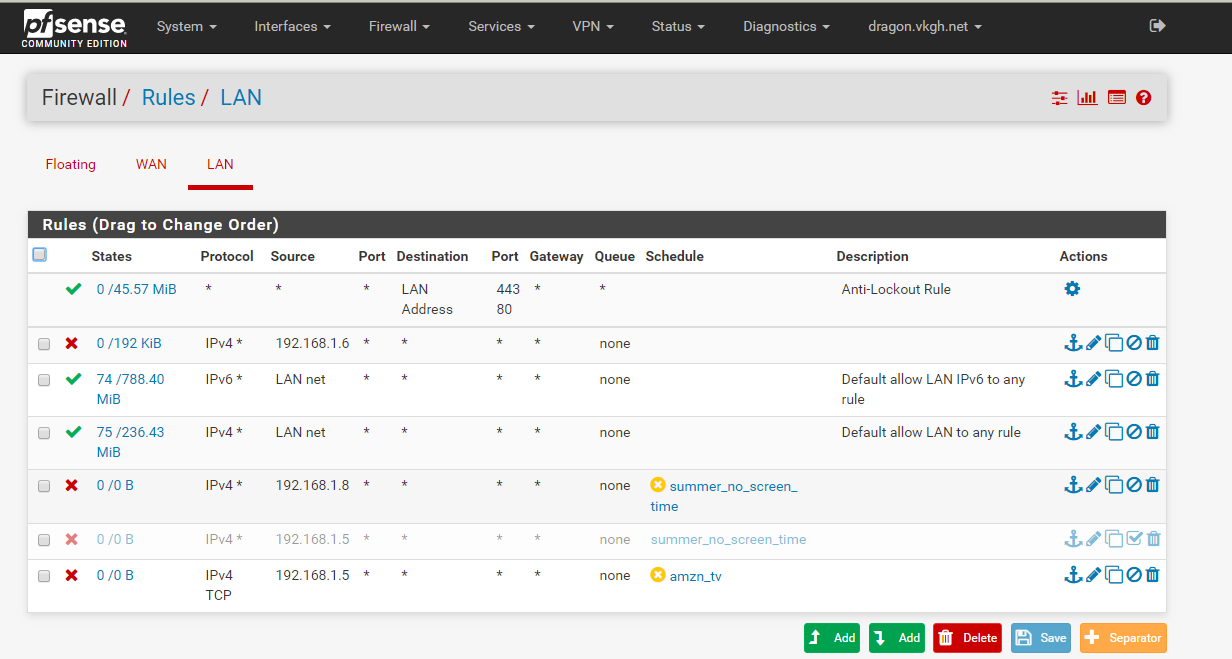
I believe I have the order of rules correct.
I did a packet capture and YouTube seems to be using normal port 443, so I have no idea how it is escaping this source IP-base firewall rule

Appreciate any pointers or feedback.
Thank you.
-
Maybe it is using IPv6 if it is enabled.
If you've just added that rule while the iPad was already online, consider that you have to delete the states. Already existing connections cannot be blocked by adding a block rule.
-
Yeah clearly see some hits on your block rule - but also 788MB of traffic through your ipv6 rule. With 74 active connections.
-
Thanks for the responses.
@viragomann I restarted iPad and also rebooted the firewall after the change to be sure
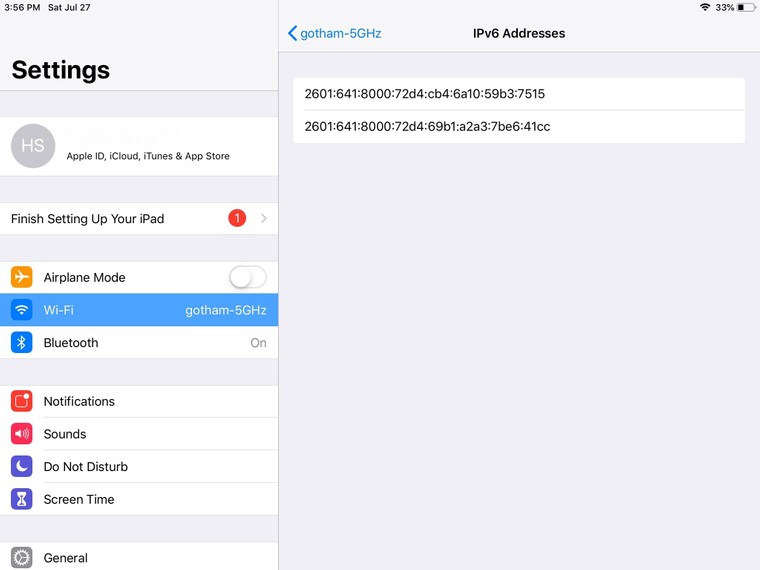
@johnpoz I have now disabled the DHCPv6 server. Here are my iPad IP addresses -
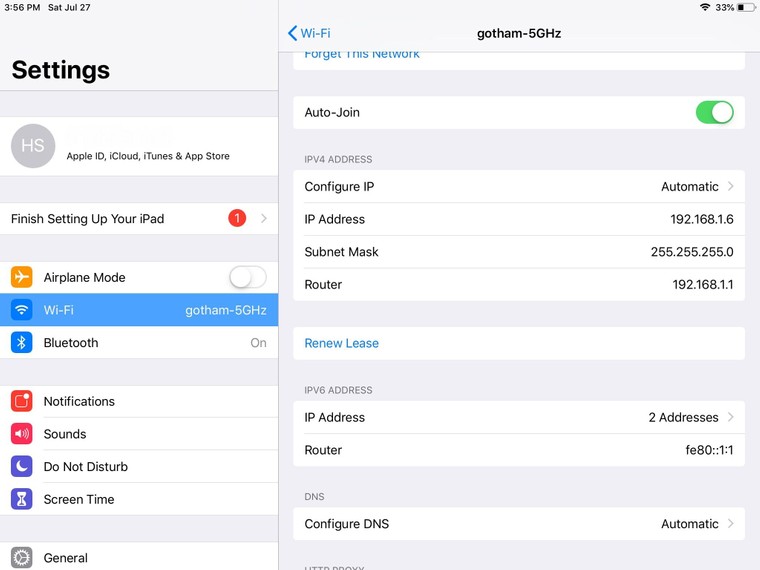
These IPv6 addresses cannot be used for Internet access, correct?App store is definitely getting blocked by this rule, but YouTube app and browser traffic is still getting through.
-
Update- I added rules for the IPv6 addresses picked up my iPad and is now blocking all traffic! Here is the rule-
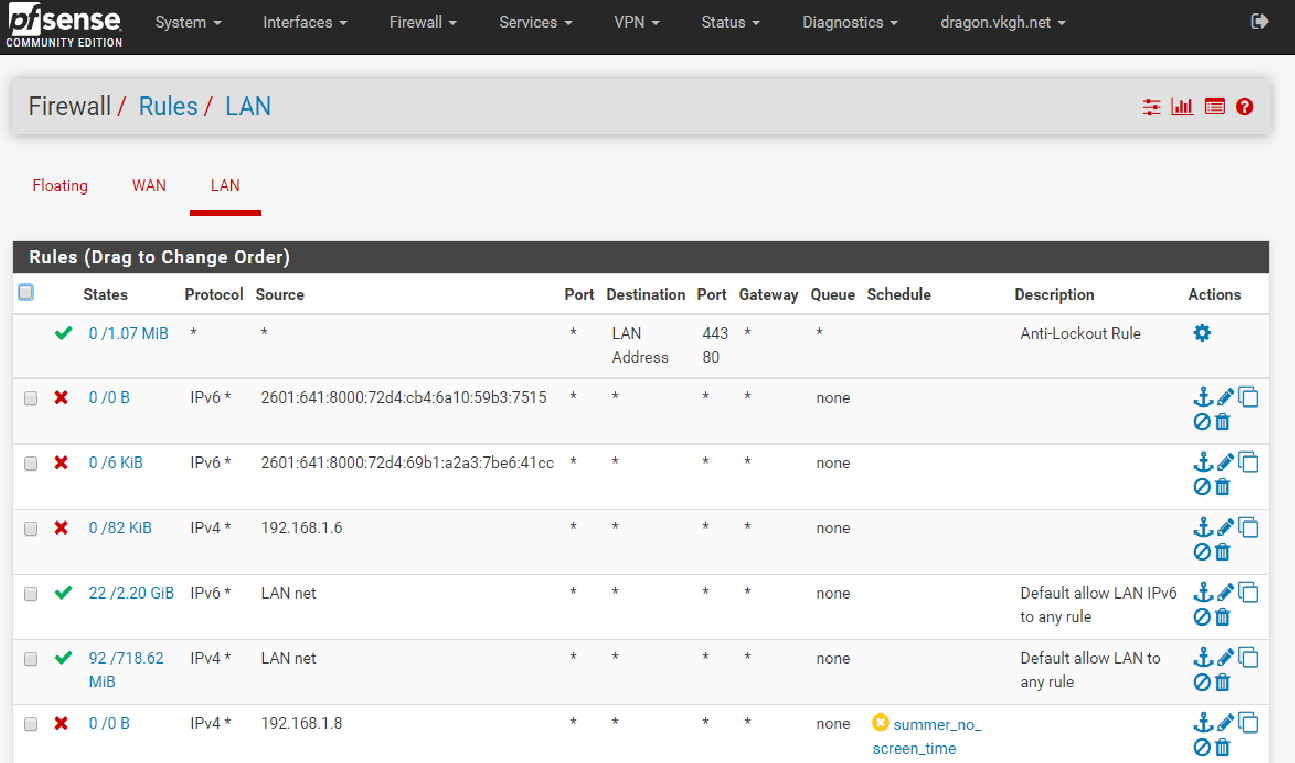
Can someone please tell me what is the right way to configure static IPv6? Since iPad is picking up 3 IPv6 address, even I configure one static v6, will not use the other v6 addresses it is picking up automatically? Sorry for my ignorance about ipv6.
Thanks
-
Really to be honest, ipv6 is a bit of learning curve when it comes to admin it from a security point of view..
And even from just how address are managed, and how it discovers stuff, etc
My opinion, which not everyone here agrees with (I know of 1) - but would solve your issue until such time that your up to speed. Its not really something your going to get out of reading a couple of posts or reading a guide or two ;)
Would be to just disable it completely.. See that ipv6 rule that is set to allow.. Just remove it or change it to block.. While yes ipv6 is the future, and yeah its slick as shit ;) Name one resource that requires you to have ipv6.. Just 1 that you need.. If you can not - then you have no current need of it - and it is causing you internal security issues. You want to block something from doing something, yet ipv6 is making that more difficult..
There is no way to disable ipv6 on an ipad.. If its available on the network it will use it.. So your best option overall is just disable it on pfsense. You could just block it with rule, but then clients would still be getting address and trying to use it.. even if you have dhcpv6 off.. You need to just not set an IPv6 address your lan address.. Set it to none, vs the tracking your prob currently doing.. And turn off both dhcpv6 and RA.. Now your clients wont even get an IPv6 they could use.
I only run ipv6 on one of my ssid that I use for testing, and another of my wired vlans. This allows me to control which devices can even get an IPv6..
-
@johnpoz , thanks for the suggestion. I blocked IPv6 completely and with v4-only traffic, Internet acccess is now under proper control.
Interestingly, I had blocked DHCPv6 but iPad was still picking up some IPv6 address automatically (one of those v6 address thingys I think) and it was slipping through the IPv6 allow rule. I suppose I need to read up on IPv6 more like John said :)
-
IPv6 doesn't even need dhcp - you will need to disable the RA for your interface if you don't want it to pick up auto IPv6 addresses.
-
This post is deleted!