RESOLVED: Captive Portal - One Time Password Help
-
Evening,
Last few days I've been playing with the captive portal(and FreeRadius) and throughout this adventure played with the One Time Password Authentication.
I do have OTP setup, albeit possibly something is not correct, as with the test username and the password(pin+OTP) I AM able to get through Captive Portal Auth page. A few minutes later(or seconds sometimes) the device connected using OTP is disconnected and deauthed from Captive Portal.
Worth noting that devices connecting to Captive Portal just using typical authentication(regular username and pass) are NOT disconnected until soft/hard limits defined in Captive Portal are hit.
I tried to catch the disconnects in logs if it is of any help and I will attach them.
Is it a simple setting somewhere I have wrong? Anyone else played with OTP for Captive Portal? I believe its relatively new feature; perhaps it's a new bug I didnt find in my Google endeavors of this topic?
Any and all advice and comment is welcome.
-
Hi,
Dumping logs on a phone screen ?
Are you setting also setting up OTP using a phone ?
Do yourself a favor : don't.You'll be needing a classic console (ssh) access first.
Then, in the GUI? stop FreeRadius.
In the console, option 8, start FreeRadius withradiusd -XYou'll be seeing the entire freeradius logs on you screen in real time.
The initial "OPT" authentication, and also the re authentication, some 300 seconds (default) after that. -
This post is deleted! -
@Gertjan said in Captive Portal - One Time Password Help:
Hi,
Dumping logs on a phone screen ?
Are you setting also setting up OTP using a phone ?
Do yourself a favor : don't.You'll be needing a classic console (ssh) access first.
Then, in the GUI? stop FreeRadius.
In the console, option 8, start FreeRadius withradiusd -XYou'll be seeing the entire freeradius logs on you screen in real time.
The initial "OPT" authentication, and also the re authentication, some 300 seconds (default) after that.@Gertjan I think I did this right? It's weird because you can see it being authed but then on renew key or something not found. No idea If I'm getting these posted right... if I didnt please let me know.
No idea wtheck I'm doing wrong but for life of me cant figure out how to post snippet of code.
Never the less...
-
@blaine07 said in Captive Portal - One Time Password Help:
No idea wtheck I'm doing wrong but for life of me cant figure out how to post snippet of code.
Consider piping output of
radiusd -X
to a file - pr make Putty remember the last 10 thousand lines and copy these ^^Big logs don't belong on the forum anyway - and will get refused. That issue was solved in the late nineties, when pastebin.com (and com parables) came alive.
The issue is shown clearly (I guess) :
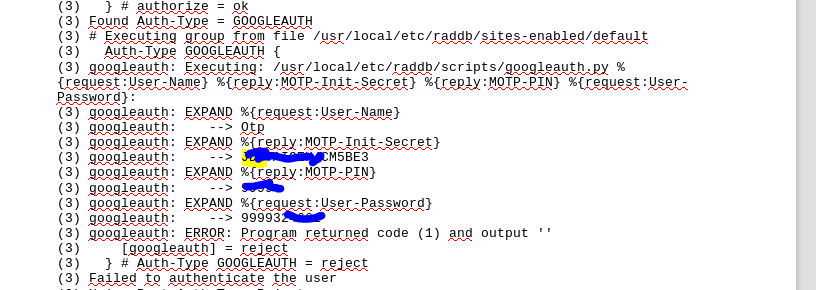
although it might be worth it to check what this means :
Btw : I'm not an Google OTP user ...
-
@Gertjan yeah I just wasnt sure if pastebin was preferred here or not; thank you!
Yeah I seen the same as you just dont understand why device is initially authenticated then later cant be re-uathenticated. I've googled the last few lines you said to look into until I'm blue in face and turned up nothing useful other than basic make sure time is synced etc stuff

-
Found this https://forum.netgate.com/topic/135424/solved-two-factor-authentication-for-admin-login
There is also a official video talking about Google OTP, you'll find it in the same thread.
-
Will watch slide video shortly found in linked thread.
Seems most of the talk about OTP is in relation to VPN or PFSense admin page. Is it THAT different to integrate OTP into the Captive Portal versus the other two? I mean this doesn’t seem terribly difficult so not entirely sure what’s going wrong versus if I was using OTP to authenticate a VPN user.



 ️
️ -
@Gertjan said in Captive Portal - One Time Password Help:
Found this https://forum.netgate.com/topic/135424/solved-two-factor-authentication-for-admin-login
There is also a official video talking about Google OTP, you'll find it in the same thread.
Alright watched that hangout and skimmed through thread. Didnt lead me to any new conclusions. Tried a few new things and no progress so far :-( Maybe OTP just isnt meant to be used with CP


 ️
️ -
I realized this is VPN but I suspect it may be related. A command, reneg-sec, as what they describe is pretty much identical to my problem. Get connected but cant stay.
What's equivalent of "reneg-sec" for captive portal?
The exert: One more thing: OpenVPN renegotiates the authentication every 3600 seconds. But a Google Authenticator code is only valid for 30 seconds. So then renegotiation will fail and you will be disconnected and asked to re-enter your password (your PIN + your current Google Authenticator code). That’s ok and it works but you may want to change that behaviour.
The relevant setting is reneg-sec and you must set it to the number of seconds after which you want the negotionation to occur. 3600 is the default but you could set it to a higher value like a day. Use 0 to disable it altogether. Here I’m using 0; use however many you like.
Found here(towards bottom of guide): https://vorkbaard.nl/how-to-set-up-openvpn-with-google-authenticator-on-pfsense/
-
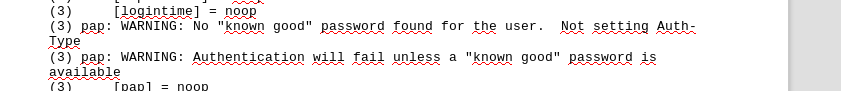
Also : remember I was talking about the "pap" error ?
Check out the video at the end, jimp is also talking about this "pap".
-
@Gertjan said in Captive Portal - One Time Password Help:
Also : remember I was talking about the "pap" error ?
Check out the video at the end, jimp is also talking about this "pap".
Yes its type is set to PAP. :-(
Any other ideas?


-
So, turned this off/unchecked(in pfSense Captive Portal Settings) and so far it seems to have fixed everything. In captive portal I have a 45min timeout set and a 60min hard timeout set. With this every minute check disabled after 60min will it still toss the OTP users off as it would before, when it was checking every minute?
 What exactly is turning this toggle off going to do or what else will it effect?
What exactly is turning this toggle off going to do or what else will it effect?Thanks!
-
Alright used it for a hour. Turning that check box, Reauthenticate Users, under Captive Portal Configuration OFF appears to have no other adverse effects. Idle timeout and hard timeout, again on Captive Portal Configuration page, are respected still as well.
So I guess the moral is, anyone looking to utilize OTP with Captive Portal...make sure above mentioned box IS UNCHECKED(toggled off). :-)
Thank you for all the help and tips @Gertjan; I appreciate your time.
