Acme DNS-NSupdate / RFC 2136 issue
-
@dansgul said in Acme DNS-NSupdate / RFC 2136 issue:
THISNSUPDATE_ZONE
I've looked for this one before.
It's used before its initialized, so that explains :@dansgul said in Acme DNS-NSupdate / RFC 2136 issue:
It appears accountconf.conf contains an NULL NSUPDATE_ZONE (and is overwritten by dns_nsupdate.s
very well.
Better yet : can't find "THISNSUPDATE_ZONE" here https://github.com/Neilpang/acme.sh/blob/master/dnsapi/dns_nsupdate.sh
-
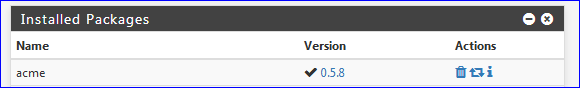
Are you on the latest version of the ACME package? There was a bug with that a while back IIRC.
The
THISNSUPDATE_<x>stuff is just in pfSense. The stock files from acme.sh don't easily support multiple RFC2136 entries on a single cert the way pfSense uses them. -
@jimp said in Acme DNS-NSupdate / RFC 2136 issue:
Are you on the latest version of the ACME package? There was a bug with that a while back IIRC.
The
THISNSUPDATE_<x>stuff is just in pfSense. The stock files from acme.sh don't easily support multiple RFC2136 entries on a single cert the way pfSense uses them.Ah, ok.
Have a look at this "THISNSUPDATE_ZONE" in dnsapi/dns_nsupdate.sh - shouldnt it be init (= read) before used and written ? -
Yeah, I thought it was but I'm not seeing it now, either. I'll look into it.
-
I just pushed a new version of ACME that should fix this. Give it a try when it shows up for you (0.6)
-
Saw it.
Tested !
Worked !
-
Hi there, this still isn't working for me; I've upgraded to 0.6
I still see "NSUPDATE_ZONE" as empty and the issue fails. (I know our DNS server needs to have the zone sent for this to work)[Wed Aug 7 17:23:39 BST 2019] d='login.cnet.sgul.ac.uk' [Wed Aug 7 17:23:39 BST 2019] _d_alias [Wed Aug 7 17:23:39 BST 2019] txtdomain='_acme-challenge.login.cnet.sgul.ac.uk' [Wed Aug 7 17:23:39 BST 2019] base64 single line. [Wed Aug 7 17:23:39 BST 2019] txt='_WaKP7V9YAEUOHv0Y6MJWEhq7KPImm7n8t6WcSwPqZE' [Wed Aug 7 17:23:39 BST 2019] d_api='/usr/local/pkg/acme/dnsapi/dns_nsupdate.sh' [Wed Aug 7 17:23:39 BST 2019] dns_entry='login.cnet.sgul.ac.uk,_acme-challenge.login.cnet.sgul.ac.uk,,dns_nsupdate,_WaKP7V9YAEUOHv0Y6MJWEhq7KPImm7n8t6WcSwPqZE,/usr/local/pkg/acme/dnsapi/dns_nsupdate.sh' [Wed Aug 7 17:23:39 BST 2019] Found domain api file: /usr/local/pkg/acme/dnsapi/dns_nsupdate.sh [Wed Aug 7 17:23:39 BST 2019] dns_nsupdate_add exists=0 [Wed Aug 7 17:23:39 BST 2019] Adding txt value: _WaKP7V9YAEUOHv0Y6MJWEhq7KPImm7n8t6WcSwPqZE for domain: _acme-challenge.login.cnet.sgul.ac.uk [Wed Aug 7 17:23:39 BST 2019] APP [Wed Aug 7 17:23:39 BST 2019] 5:NSUPDATE_SERVER='ns1.sgul.ac.uk' [Wed Aug 7 17:23:39 BST 2019] APP [Wed Aug 7 17:23:39 BST 2019] 6:NSUPDATE_SERVER_PORT='' [Wed Aug 7 17:23:39 BST 2019] APP [Wed Aug 7 17:23:39 BST 2019] 7:NSUPDATE_KEY='/tmp/acme/testing/login.cnet.sgul.ac.uknsupdate_acme-challenge.login.cnet.sgul.ac.uk.key' [Wed Aug 7 17:23:39 BST 2019] APP [Wed Aug 7 17:23:39 BST 2019] 8:NSUPDATE_ZONE='' [Wed Aug 7 17:23:39 BST 2019] adding _acme-challenge.login.cnet.sgul.ac.uk. 60 in txt "_WaKP7V9YAEUOHv0Y6MJWEhq7KPImm7n8t6WcSwPqZE" [Wed Aug 7 17:23:39 BST 2019] error updating domain [Wed Aug 7 17:23:39 BST 2019] Error add txt for domain:_acme-challenge.login.cnet.sgul.ac.uk [Wed Aug 7 17:23:39 BST 2019] _on_issue_err -
OK, I missed a couple bits. I just pushed ACME pkg v 0.6.2 which should work now. I didn't test it completely but I did confirm at least that the zone makes it into the account config and logs where it was missing before.
-
Working now after upgrade to 0.6.2
Many thanks jimp!
-
 N NollipfSense referenced this topic on
N NollipfSense referenced this topic on
-
 N NollipfSense referenced this topic on
N NollipfSense referenced this topic on
-
 N NollipfSense referenced this topic on
N NollipfSense referenced this topic on
-
The problem is still present in the latest version. 0.8_1.
Failures on expected a TSIG or SIG(0) even though it's implemented.
Regards
-
Humm. I'm using 'nsupdate' = DNS-NSupdate / RFC 2136.
Works just fine.nsupdate didn't change for years.
-
@Gertjan are you using BIND9?
-
@Gertjan are you using BIND9?
-
-
@Gertjan could you post your config?
-
@VioletDragon said in Acme DNS-NSupdate / RFC 2136 issue:
@Gertjan are you using BIND9?
Yes.
Debian 11.10... no .11 just right now.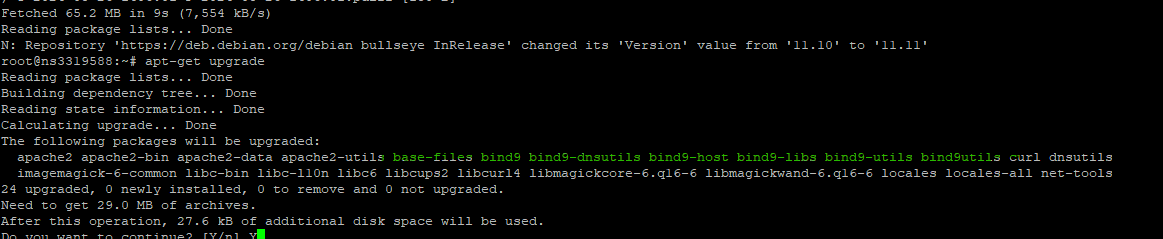
I can't re test my acme renewal, as I'm in the grace period : a renewal will work and no DNS checks will be done.
But : I'm also using RFC2136 for my pfSense WAN side host name = DynDNS.
Logs on server = bind9 side :
01-Sep-2024 13:21:27.416 update-security: client @0x7f4884148ed0 82.127.99.108#59810/key update: signer "update" approved 01-Sep-2024 13:21:27.416 update: client @0x7f4884148ed0 82.127.26.108#59810/key update: updating zone 'bhf.tld/IN': deleting rrset at 'home.bhf.tld' A 01-Sep-2024 13:21:27.416 update: client @0x7f4884148ed0 82.127.26.108#59810/key update: updating zone 'bhf.tld/IN': adding an RR at 'home.bhf.tld' A 82.135.26.118 01-Sep-2024 13:21:27.416 update: client @0x7f4884148ed0 82.127.26.108#59810/key update: updating zone 'bhf.tld/IN': deleting rrset at 'home.bhf.tld' AAAA 01-Sep-2024 13:21:27.416 update: client @0x7f4884148ed0 82.127.26.108#59810/key update: updating zone 'bhf.tld/IN': adding an RR at 'home.bhf.tld' AAAA 2a01:cb19:beef:dead:92ec:77ff:fe29:392a -
@Gertjan how did you set it up? As I got it working with Certbot but not Acme.
-
@Gertjan Problem seems to be with the acme.sh package, works fine with Certbot with the HMAC key but Acme seems to be ignoring the Key whether you put the key in or not.
Error that keeps showing dns_request_getresponse: expected a TSIG or SIG(0)
same happens with acme.sh on a fresh install of BSD so i think the package is broken.
-
The last acme.sh update is several or more weeks old.
nsupdate or RFC2136 is probably the most used update method.
It's also the very first, most documented update method.The pfSense acme packet uses probably not the latest 3.0.8
The nsupdate method itself hasn't been update for a long time.@VioletDragon said in Acme DNS-NSupdate / RFC 2136 issue:
Error that keeps showing dns_request_getresponse: expected a TSIG or SIG(0)
Imho, that's not a message from acme.sh ....
Can you show in what context this message is shown ? -
I can do better. This is the full log taken from acme.
Sat Aug 31 13:52:37 BST 2024] response='{"identifier":{"type":"dns","value":"domain.uk"},"status":"pending","expires":"2024-09-07T12:52:36Z","challenges":[{"type":"http-01","url":"https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/18bUeQ","status":"pending","token":"ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs"},{"type":"dns-01","url":"https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/hpELDw","status":"pending","token":"ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs"},{"type":"tls-alpn-01","url":"https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/AUEJVQ","status":"pending","token":"ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs"}]}' [Sat Aug 31 13:52:37 BST 2024] response='{"identifier":{"type":"dns","value":domain.uk"},"status":"pending","expires":"2024-09-07T12:52:36Z","challenges":[{"type":"http-01","url":"https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/18bUeQ","status":"pending","token":"ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs"},{"type":"dns-01","url":"https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/hpELDw","status":"pending","token":"ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs"},{"type":"tls-alpn-01","url":"https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/AUEJVQ","status":"pending","token":"ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs"}]}' [Sat Aug 31 13:52:37 BST 2024] _d='domain.uk' [Sat Aug 31 13:52:37 BST 2024] _authorizations_map='domain.uk,{"identifier":{"type":"dns","value":"domain.uk"},"status":"pending","expires":"2024-09-07T12:52:36Z","challenges":[{"type":"http-01","url":"https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/18bUeQ","status":"pending","token":"ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs"},{"type":"dns-01","url":"https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/hpELDw","status":"pending","token":"ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs"},{"type":"tls-alpn-01","url":"https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/AUEJVQ","status":"pending","token":"ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs"}]}#https://acme-staging-v02.api.letsencrypt.org/acme/authz-v3/13812135463 ' [Sat Aug 31 13:52:37 BST 2024] d='domain.uk' [Sat Aug 31 13:52:37 BST 2024] Getting webroot for domain='domain.uk' [Sat Aug 31 13:52:37 BST 2024] _w='dns_nsupdate' [Sat Aug 31 13:52:37 BST 2024] _currentRoot='dns_nsupdate' [Sat Aug 31 13:52:37 BST 2024] _is_idn_d='rdomain.uk' [Sat Aug 31 13:52:37 BST 2024] _idn_temp [Sat Aug 31 13:52:37 BST 2024] _candidates='domain.uk,{"identifier":{"type":"dns","value":"domain.uk"},"status":"pending","expires":"2024-09-07T12:52:36Z","challenges":[{"type":"http-01","url":"https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/18bUeQ","status":"pending","token":"ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs"},{"type":"dns-01","url":"https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/hpELDw","status":"pending","token":"ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs"},{"type":"tls-alpn-01","url":"https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/AUEJVQ","status":"pending","token":"ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs"}]}#https://acme-staging-v02.api.letsencrypt.org/acme/authz-v3/13812135463' [Sat Aug 31 13:52:37 BST 2024] response='{"identifier":{"type":"dns","value":"domain.uk"},"status":"pending","expires":"2024-09-07T12:52:36Z","challenges":[{"type":"http-01","url":"https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/18bUeQ","status":"pending","token":"ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs"},{"type":"dns-01","url":"https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/hpELDw","status":"pending","token":"ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs"},{"type":"tls-alpn-01","url":"https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/AUEJVQ","status":"pending","token":"ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs"}]}#https://acme-staging-v02.api.letsencrypt.org/acme/authz-v3/13812135463' [Sat Aug 31 13:52:37 BST 2024] _authz_url='https://acme-staging-v02.api.letsencrypt.org/acme/authz-v3/13812135463' [Sat Aug 31 13:52:37 BST 2024] base64 single line. [Sat Aug 31 13:52:37 BST 2024] entry='"type":"dns-01","url":"https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/hpELDw","status":"pending","token":"ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs"' [Sat Aug 31 13:52:37 BST 2024] token='ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs' [Sat Aug 31 13:52:37 BST 2024] uri='https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/hpELDw' [Sat Aug 31 13:52:37 BST 2024] keyauthorization='ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs.Gs37H2DRQn4anpJP0dteohxeHULcMh5JS5ssdIbWSlM' [Sat Aug 31 13:52:37 BST 2024] dvlist='domain.uk#ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs.Gs37H2DRQn4anpJP0dteohxeHULcMh5JS5ssdIbWSlM#https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/hpELDw#dns-01#dns_nsupdate#https://acme-staging-v02.api.letsencrypt.org/acme/authz-v3/13812135463' [Sat Aug 31 13:52:37 BST 2024] d [Sat Aug 31 13:52:37 BST 2024] vlist='domain.uk#ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs.Gs37H2DRQn4anpJP0dteohxeHULcMh5JS5ssdIbWSlM#https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/hpELDw#dns-01#dns_nsupdate#https://acme-staging-v02.api.letsencrypt.org/acme/authz-v3/13812135463,' [Sat Aug 31 13:52:37 BST 2024] d='domain.uk' [Sat Aug 31 13:52:37 BST 2024] _d_alias [Sat Aug 31 13:52:37 BST 2024] txtdomain='_acme-challenge.domain.uk' [Sat Aug 31 13:52:37 BST 2024] base64 single line. [Sat Aug 31 13:52:37 BST 2024] txt='F93-7roSbnc3rfj9muIr3C5aVkahuRGFQFiSpc-FdFI' [Sat Aug 31 13:52:37 BST 2024] d_api='/usr/local/pkg/acme/dnsapi/dns_nsupdate.sh' [Sat Aug 31 13:52:37 BST 2024] dns_entry='domain.uk,_acme-challenge.domain.uk,,dns_nsupdate,F93-7roSbnc3rfj9muIr3C5aVkahuRGFQFiSpc-FdFI,/usr/local/pkg/acme/dnsapi/dns_nsupdate.sh' [Sat Aug 31 13:52:37 BST 2024] Found domain api file: /usr/local/pkg/acme/dnsapi/dns_nsupdate.sh [Sat Aug 31 13:52:37 BST 2024] dns_nsupdate_add exists=0 [Sat Aug 31 13:52:37 BST 2024] Adding txt value: F93-7roSbnc3rfj9muIr3C5aVkahuRGFQFiSpc-FdFI for domain: _acme-challenge.domain.uk [Sat Aug 31 13:52:37 BST 2024] APP [Sat Aug 31 13:52:37 BST 2024] 5:NSUPDATE_SERVER='ns1.domain.uk' [Sat Aug 31 13:52:37 BST 2024] APP [Sat Aug 31 13:52:37 BST 2024] 6:NSUPDATE_SERVER_PORT='' [Sat Aug 31 13:52:37 BST 2024] APP [Sat Aug 31 13:52:37 BST 2024] 7:NSUPDATE_KEY='/tmp/acme/domain/domain.uknsupdate_acme-challenge.domain.uk.key' [Sat Aug 31 13:52:37 BST 2024] APP [Sat Aug 31 13:52:37 BST 2024] 8:NSUPDATE_ZONE='' [Sat Aug 31 13:52:37 BST 2024] adding _acme-challenge.domain.uk. 60 in txt "F93-7roSbnc3rfj9muIr3C5aVkahuRGFQFiSpc-FdFI" [Sat Aug 31 13:52:37 BST 2024] error updating domain [Sat Aug 31 13:52:37 BST 2024] Error add txt for domain:_acme-challenge.domain.uk [Sat Aug 31 13:52:37 BST 2024] _on_issue_err [Sat Aug 31 13:52:37 BST 2024] Please check log file for more details: /tmp/acme/domain/acme_issuecert.log [Sat Aug 31 13:52:37 BST 2024] _chk_vlist='domain.uk.uk#ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs.Gs37H2DRQn4anpJP0dteohxeHULcMh5JS5ssdIbWSlM#https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/hpELDw#dns-01#dns_nsupdate#https://acme-staging-v02.api.letsencrypt.org/acme/authz-v3/13812135463,' [Sat Aug 31 13:52:37 BST 2024] start to deactivate authz [Sat Aug 31 13:52:37 BST 2024] Trigger domain validation. [Sat Aug 31 13:52:37 BST 2024] _t_url='https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/hpELDw' [Sat Aug 31 13:52:37 BST 2024] _t_key_authz='ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs.Gs37H2DRQn4anpJP0dteohxeHULcMh5JS5ssdIbWSlM' [Sat Aug 31 13:52:37 BST 2024] _t_vtype [Sat Aug 31 13:52:37 BST 2024] =======Begin Send Signed Request======= [Sat Aug 31 13:52:37 BST 2024] url='https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/hpELDw' [Sat Aug 31 13:52:37 BST 2024] payload='{}' [Sat Aug 31 13:52:37 BST 2024] Use cached jwk for file: /tmp/acme/domain/ca/acme-staging-v02.api.letsencrypt.org/directory/account.key [Sat Aug 31 13:52:37 BST 2024] base64 single line. [Sat Aug 31 13:52:37 BST 2024] payload64='e30' [Sat Aug 31 13:52:37 BST 2024] _request_retry_times='1' [Sat Aug 31 13:52:37 BST 2024] Use _CACHED_NONCE='vfo-J0TvfjHlz2bMKE551YAvMUFYuZqkrhfz2naON64CEGmUrLI' [Sat Aug 31 13:52:37 BST 2024] nonce='vfo-J0TvfjHlz2bMKE551YAvMUFYuZqkrhfz2naON64CEGmUrLI' [Sat Aug 31 13:52:37 BST 2024] protected='{"nonce": "vfo-J0TvfjHlz2bMKE551YAvMUFYuZqkrhfz2naON64CEGmUrLI", "url": "https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/hpELDw", "alg": "RS256", "kid": "https://acme-staging-v02.api.letsencrypt.org/acme/acct/161503273"}' [Sat Aug 31 13:52:37 BST 2024] base64 single line. [Sat Aug 31 13:52:37 BST 2024] protected64='eyJub25jZSI6ICJ2Zm8tSjBUdmZqSGx6MmJNS0U1NTFZQXZNVUZZdVpxa3JoZnoybmFPTjY0Q0VHbVVyTEkiLCAidXJsIjogImh0dHBzOi8vYWNtZS1zdGFnaW5nLXYwMi5hcGkubGV0c2VuY3J5cHQub3JnL2FjbWUvY2hhbGwtdjMvMTM4MTIxMzU0NjMvaHBFTER3IiwgImFsZyI6ICJSUzI1NiIsICJraWQiOiAiaHR0cHM6Ly9hY21lLXN0YWdpbmctdjAyLmFwaS5sZXRzZW5jcnlwdC5vcmcvYWNtZS9hY2N0LzE2MTUwMzI3MyJ9' [Sat Aug 31 13:52:37 BST 2024] base64 single line. [Sat Aug 31 13:52:37 BST 2024] _sig_t='FkRiy7U2h9RGIiziq5LU9NeGSJln9tIRLLGVDvlYo2Gp4PB/eaLi2zxZMn2GEfP9SGOn7hmxE9hbkd7bQkuFKSIwCUgnrrAVQ3IZ/IrCFH401qZ/Vbi56mGb260pIZhIpY2xV8lLya+7x9KxkUKEkn42wTqPyXOypl4e4Wws4ENwrg1npmn8dGxVxM5l1s8raRToUIHzB3ueibZnkv6wGiQsW43nbPFnfr9E3fb9vDF995h4fxpqW1IdgAuaH766GKPLaMdFowOcNtu+E3ep7QVB64/s9uUr5cdtu4LvrJs3g7TF1GWMi56Cn7aOiMqOcZ+/xg4C2Gesbz6Mij75xCdOO36asmC7VUK03MEMprZKk3l3gwXCz7xIo9ak3/dcV08K5GfrsMwwtOfbuzcQKAtRqNQwwjPTqANswue3jWpZLdKx97QFlEH8AQ9jw6vjSsEqNpTMrGbwp/GrG2Y9kzx6B5G1Ivp4iUQgC7b4PfIFeC8d+rPpQ7tOesTHK7EgZ5obK/L6UsS5G1fAf9ajx05rCkpk5ivYOpTS6p55X9nHSV+TGsADegxts4I7Zl40wSEaZAG70hI0xSK7mns/d70lb99SOYGKwGIKAZjCuG7U++28kvjjWk6jLNPrV7Rj6uPzDAl4xjcrsbzSzDnkgZMQZGAfHPLQZkQtV+czkdw=' [Sat Aug 31 13:52:37 BST 2024] sig='FkRiy7U2h9RGIiziq5LU9NeGSJln9tIRLLGVDvlYo2Gp4PB_eaLi2zxZMn2GEfP9SGOn7hmxE9hbkd7bQkuFKSIwCUgnrrAVQ3IZ_IrCFH401qZ_Vbi56mGb260pIZhIpY2xV8lLya-7x9KxkUKEkn42wTqPyXOypl4e4Wws4ENwrg1npmn8dGxVxM5l1s8raRToUIHzB3ueibZnkv6wGiQsW43nbPFnfr9E3fb9vDF995h4fxpqW1IdgAuaH766GKPLaMdFowOcNtu-E3ep7QVB64_s9uUr5cdtu4LvrJs3g7TF1GWMi56Cn7aOiMqOcZ-_xg4C2Gesbz6Mij75xCdOO36asmC7VUK03MEMprZKk3l3gwXCz7xIo9ak3_dcV08K5GfrsMwwtOfbuzcQKAtRqNQwwjPTqANswue3jWpZLdKx97QFlEH8AQ9jw6vjSsEqNpTMrGbwp_GrG2Y9kzx6B5G1Ivp4iUQgC7b4PfIFeC8d-rPpQ7tOesTHK7EgZ5obK_L6UsS5G1fAf9ajx05rCkpk5ivYOpTS6p55X9nHSV-TGsADegxts4I7Zl40wSEaZAG70hI0xSK7mns_d70lb99SOYGKwGIKAZjCuG7U--28kvjjWk6jLNPrV7Rj6uPzDAl4xjcrsbzSzDnkgZMQZGAfHPLQZkQtV-czkdw' [Sat Aug 31 13:52:37 BST 2024] body='{"protected": "eyJub25jZSI6ICJ2Zm8tSjBUdmZqSGx6MmJNS0U1NTFZQXZNVUZZdVpxa3JoZnoybmFPTjY0Q0VHbVVyTEkiLCAidXJsIjogImh0dHBzOi8vYWNtZS1zdGFnaW5nLXYwMi5hcGkubGV0c2VuY3J5cHQub3JnL2FjbWUvY2hhbGwtdjMvMTM4MTIxMzU0NjMvaHBFTER3IiwgImFsZyI6ICJSUzI1NiIsICJraWQiOiAiaHR0cHM6Ly9hY21lLXN0YWdpbmctdjAyLmFwaS5sZXRzZW5jcnlwdC5vcmcvYWNtZS9hY2N0LzE2MTUwMzI3MyJ9", "payload": "e30", "signature": "FkRiy7U2h9RGIiziq5LU9NeGSJln9tIRLLGVDvlYo2Gp4PB_eaLi2zxZMn2GEfP9SGOn7hmxE9hbkd7bQkuFKSIwCUgnrrAVQ3IZ_IrCFH401qZ_Vbi56mGb260pIZhIpY2xV8lLya-7x9KxkUKEkn42wTqPyXOypl4e4Wws4ENwrg1npmn8dGxVxM5l1s8raRToUIHzB3ueibZnkv6wGiQsW43nbPFnfr9E3fb9vDF995h4fxpqW1IdgAuaH766GKPLaMdFowOcNtu-E3ep7QVB64_s9uUr5cdtu4LvrJs3g7TF1GWMi56Cn7aOiMqOcZ-_xg4C2Gesbz6Mij75xCdOO36asmC7VUK03MEMprZKk3l3gwXCz7xIo9ak3_dcV08K5GfrsMwwtOfbuzcQKAtRqNQwwjPTqANswue3jWpZLdKx97QFlEH8AQ9jw6vjSsEqNpTMrGbwp_GrG2Y9kzx6B5G1Ivp4iUQgC7b4PfIFeC8d-rPpQ7tOesTHK7EgZ5obK_L6UsS5G1fAf9ajx05rCkpk5ivYOpTS6p55X9nHSV-TGsADegxts4I7Zl40wSEaZAG70hI0xSK7mns_d70lb99SOYGKwGIKAZjCuG7U--28kvjjWk6jLNPrV7Rj6uPzDAl4xjcrsbzSzDnkgZMQZGAfHPLQZkQtV-czkdw"}' [Sat Aug 31 13:52:37 BST 2024] POST [Sat Aug 31 13:52:37 BST 2024] _post_url='https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/hpELDw' [Sat Aug 31 13:52:37 BST 2024] body='{"protected": "eyJub25jZSI6ICJ2Zm8tSjBUdmZqSGx6MmJNS0U1NTFZQXZNVUZZdVpxa3JoZnoybmFPTjY0Q0VHbVVyTEkiLCAidXJsIjogImh0dHBzOi8vYWNtZS1zdGFnaW5nLXYwMi5hcGkubGV0c2VuY3J5cHQub3JnL2FjbWUvY2hhbGwtdjMvMTM4MTIxMzU0NjMvaHBFTER3IiwgImFsZyI6ICJSUzI1NiIsICJraWQiOiAiaHR0cHM6Ly9hY21lLXN0YWdpbmctdjAyLmFwaS5sZXRzZW5jcnlwdC5vcmcvYWNtZS9hY2N0LzE2MTUwMzI3MyJ9", "payload": "e30", "signature": "FkRiy7U2h9RGIiziq5LU9NeGSJln9tIRLLGVDvlYo2Gp4PB_eaLi2zxZMn2GEfP9SGOn7hmxE9hbkd7bQkuFKSIwCUgnrrAVQ3IZ_IrCFH401qZ_Vbi56mGb260pIZhIpY2xV8lLya-7x9KxkUKEkn42wTqPyXOypl4e4Wws4ENwrg1npmn8dGxVxM5l1s8raRToUIHzB3ueibZnkv6wGiQsW43nbPFnfr9E3fb9vDF995h4fxpqW1IdgAuaH766GKPLaMdFowOcNtu-E3ep7QVB64_s9uUr5cdtu4LvrJs3g7TF1GWMi56Cn7aOiMqOcZ-_xg4C2Gesbz6Mij75xCdOO36asmC7VUK03MEMprZKk3l3gwXCz7xIo9ak3_dcV08K5GfrsMwwtOfbuzcQKAtRqNQwwjPTqANswue3jWpZLdKx97QFlEH8AQ9jw6vjSsEqNpTMrGbwp_GrG2Y9kzx6B5G1Ivp4iUQgC7b4PfIFeC8d-rPpQ7tOesTHK7EgZ5obK_L6UsS5G1fAf9ajx05rCkpk5ivYOpTS6p55X9nHSV-TGsADegxts4I7Zl40wSEaZAG70hI0xSK7mns_d70lb99SOYGKwGIKAZjCuG7U--28kvjjWk6jLNPrV7Rj6uPzDAl4xjcrsbzSzDnkgZMQZGAfHPLQZkQtV-czkdw"}' [Sat Aug 31 13:52:37 BST 2024] _postContentType='application/jose+json' [Sat Aug 31 13:52:37 BST 2024] Http already initialized. [Sat Aug 31 13:52:37 BST 2024] _CURL='curl --silent --dump-header /tmp/acme/domain/http.header -L -g ' [Sat Aug 31 13:52:37 BST 2024] _ret='0' [Sat Aug 31 13:52:37 BST 2024] responseHeaders='HTTP/2 200 server: nginx date: Sat, 31 Aug 2024 12:52:37 GMT content-type: application/json content-length: 193 boulder-requester: 161503273 cache-control: public, max-age=0, no-cache link: https://acme-staging-v02.api.letsencrypt.org/directory;rel="index" link: https://acme-staging-v02.api.letsencrypt.org/acme/authz-v3/13812135463;rel="up" location: https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/hpELDw replay-nonce: VFujB6i1Gj9UXVGZtCBP2Gip24W5U0wZDJQCsFzinwHOc366KPo x-frame-options: DENY strict-transport-security: max-age=604800 ' [Sat Aug 31 13:52:37 BST 2024] code='200' [Sat Aug 31 13:52:37 BST 2024] original='{ "type": "dns-01", "url": "https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/hpELDw", "status": "pending", "token": "ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs" }' [Sat Aug 31 13:52:37 BST 2024] _json_decode [Sat Aug 31 13:52:37 BST 2024] _j_str='{ "type": "dns-01", "url": "https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/hpELDw", "status": "pending", "token": "ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs" }' [Sat Aug 31 13:52:37 BST 2024] response='{"type":"dns-01","url":"https://acme-staging-v02.api.letsencrypt.org/acme/chall-v3/13812135463/hpELDw","status":"pending","token":"ExZOHBOLdZQNMQwI53B9xUHYKu_HzSBAYS_UuXFciGs"}' [Sat Aug 31 13:52:37 BST 2024] pid [Sat Aug 31 13:52:37 BST 2024] No need to restore nginx, skip. [Sat Aug 31 13:52:37 BST 2024] _clearupdns [Sat Aug 31 13:52:37 BST 2024] dns_entries [Sat Aug 31 13:52:37 BST 2024] skip dns.