Can 2.3 ASUS RT-AC68p connect to latest 2.4 pfSense FW?
-
(mods: sorry to post 2 in one day)
I now know why there are custom mods (merlin) for ASUS...
Experts,
I have, as you can imagine, an ASUS RT-AC68p wifi router that can do OpenVPN Client & Server. Precious little out there on client, tons on server. I also have the latest 2.4 pfSense, and am using OVPN for all VPNs.
Everything was fine until they handed this to me, wanting it to connect to HQ from a remote office.
Errors on the ASUS client were that it couldn't parse ncp-ciphers lines in the *.ovpn. Come to find out, they weren't around in 2.3. VPN > OpenVPN > Client Export says:
Servers configured with features that require OpenVPN 2.4 will not work with OpenVPN 2.3.x or older clients. These features include: AEAD encryption such as AES-GCM, TLS Encryption+Authentication, ECDH, LZ4 Compression and other non-legacy compression choices, IPv6 DNS servers, and more.OK. But is there ANY way to set up a dedicated port on my HQ pfSense/OVPN2.4 box so that it can talk to this ASUS 2.3 Client? Do I need to look to an OVPN alternate?
I assume this is a generic question about 2.3 clients connecting to 2.4 servers, but I'd rather ask on this one than assume... :)
TIA!
pat
:) -
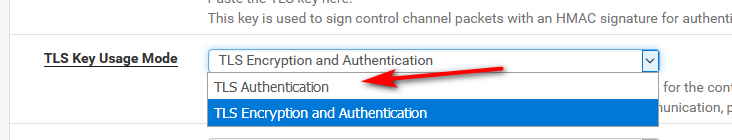
I don't think it's going to work. OpenVPN 2.4 requires tls-crypt which 2.3 lacks. Unless you can update that AP, I suspect you're out of luck.
-
-
2.4 does not "require" it - its just an option.. You can set it to just auth.
You just need to configure the 2.4 with server with settings that still work for older 2.3 clients.
You can for sure run the server on another port for the older clients, and different port for current settings.. You can run as many instances as openvpn server as want really.. Just need to use different ports.
-
Thanks John, I didn't realize that. I wonder if he will have to reissue configs for his other users though, or if switching TLS modes is transparent.
