why is snort alerts not responding for the respective portscan as expected ???
-
i have setup something as below on virtualbox to understand how pfsense together with snort function to detect and alert intrusions
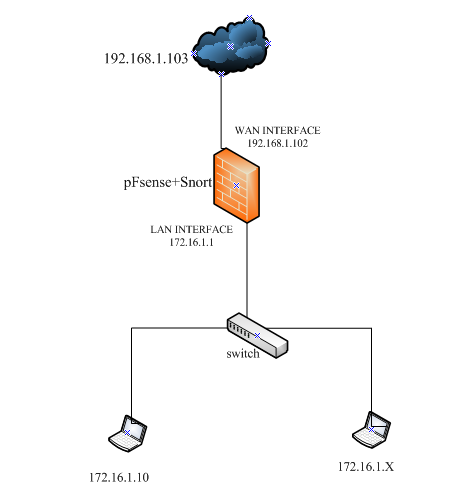
I have install and configure pfsense + snort and setup the two interfaces shown above in other to detect port scan and dos attack and alert.- Firstly when i do a port scan with nmap from 1992.168.1.X to 172.16.1.X it shows host seems down on terminal (given that the host is actually up) with no snort alert display for the WAN interface
From my understanding, it is actually suppose to display an intrusion alert for portscan and i don,t know why it does not ?????
-secondly, when i do a portscan with nmap from 172.16.1.X to 192.168.1.X it shows all host ports are closed on terminal but it doesn't display any snort alert for the LAN interface
From my understanding, after showing all host port are closed on terminal it is suppose to display an intrusion alert for portscan on the LAN interface but that is not is the case and i don't know why ???
Pls any help !!!!!!
-
What firewall rules do you have in place on the pfSense box? Is Snort running on the LAN interface? I am going to assume "yes" since you say in your last sentence that you are expecting to see the scan alert from the LAN.
pfSense firewalls, out of the box, will block all unsolicited inbound traffic. So any port scan you initiate from that 192.168.1.x network is never going to even get by the WAN interface on pfSense unless you have specifically added a rule to allow the traffic. Since the scan can't get through the WAN interface, then it is never going to show up on the LAN interface for Snort to see.
-
@bmeeks i understand that by default pfSense firewalls block all unsolicited inbound traffic as u mention, but from my expections after running Snort on the WAN interface as i configured, it is suppose so show up alerts on the WAN interface for a port scan initiated from 192.168.1.X to 172.16.1.X.
Eventhough it is blocking traffic, i though i will detect which intrusion attack( portscan) has being attempted......
This is what i'am getting below on the terminal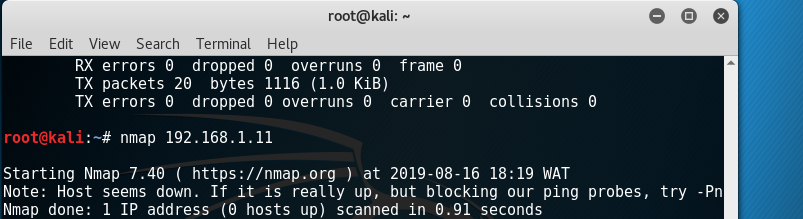
-
Do you have the portscan preprocessor enabled in Snort? It is not enabled by default because it is quite prone to false positives in today's networks. There are also some tuneable settings for the preprocessor that control its sensitivity.
The short version is that in my humble opinion the portscan stuff is way overrated. And to boot, the detection for it is very prone to false positives with the way today's network connectivity works with regards to all the various applications out there. So my suggestion is to stop wasting time playing with the portscan detection.
If you want to actually test Snort, then turn on the Emerging Threats Scan rules and then direct an
nmapscan towards a host behind Snort. You will see alerts then. That's actually how I test the package when adding new features.Finally, I don't think your
nmapcommand is complete. You seem to be missing the arguments to tellnmapexactly what you want it to do. I usually have it perform specific types of scans using the -S switch. -
@oldrik bmeeks is the package maintainer for pfSense's Snort and Suricata so you should definitely listen to him. And I also agree with him that worrying about doorknob-rattlers is a waste of time and resources. Trust your WAN rules to block unsolicited inbound traffic. If you're port-forwarding servers then you need to pay attention to traffic crossing the firewall, but otherwise just forget about it. There is constant noise on the Internet and you're going to be scanned several times a day from bots and other things. Blacklisting those IP addresses is useless if you're already blocking all unsolicited traffic to WAN.
-
Tried doing a port scan on the WAN IP using shields up ?Scrub that your WAN interface is using RFC 1918 address space.
-
@KOM u are actually right on what u are saying.....but i'm still learning PfSense+snort to understand how it function. So that is why i wanted to see the alert
-
@bmeeks said in why is snort alerts not responding for the respective portscan as expected ???:
If you want to actually test Snort, then turn on the Emerging Threats Scan rules and then direct an nmap scan towards a host behind Snort. You will see alerts then. That's actually how I test the package when adding new features.
For understanding purposes, i turn on Emerging Threats scan rules as u said above, but this is what i get below on terminal with no alert on WAN interface for a port scan behind snort...
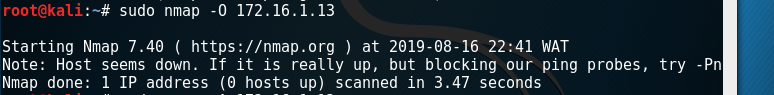
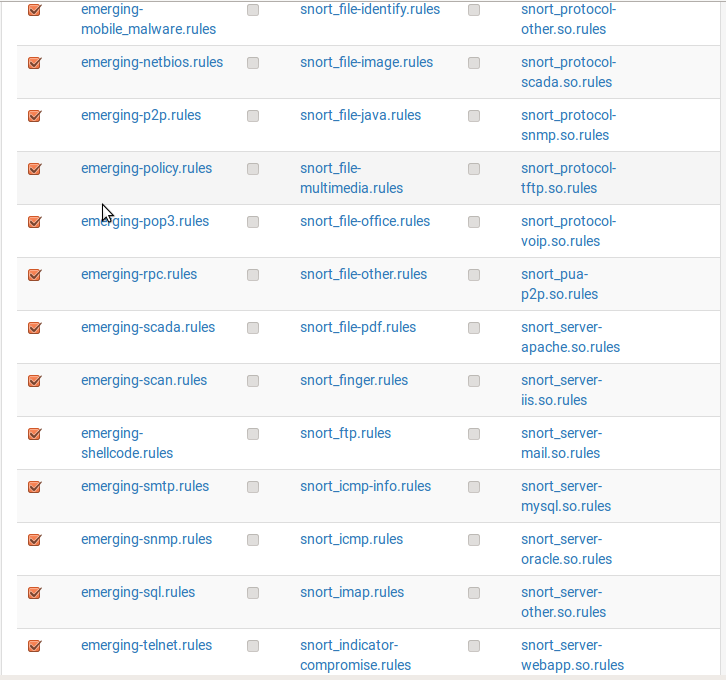
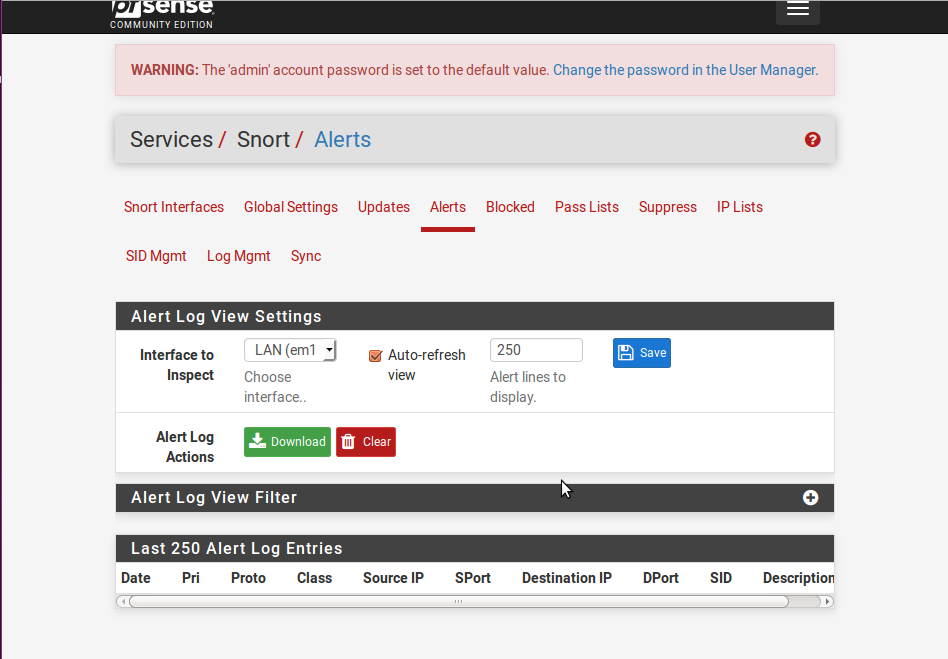
This what i get for on pfSense.
-
@bmeeks said in why is snort alerts not responding for the respective portscan as expected ???:
The short version is that in my humble opinion the portscan stuff is way overrated. And to boot, the detection for it is very prone to false positives with the way today's network connectivity works with regards to all the various applications out there. So my suggestion is to stop wasting time playing with the portscan detection.
Ok pls what other ruless apart for portsacn can u suggest me for clear understanding and testing purposes bcuz i'm actually working on small project to actually show how pfSense+Snort function to detect and prevent intrusions attacks.......thnks