Setting up VLAN: pfSense and UniFi Gear (150w PoE switches, EdgeSwitch 16XG, UniFi Controller, 13 UniFi APs)
-
Hey everyone,
I'm having a tremendously difficult time setting up something that seems like it should be easy: VLANS with a pfSense gateway and a bunch of Ubiquiti UniFi gear. The frustrating thing is I've set this up before with a pfSense gateway and UniFi APs, but with a bunch of different switches.
Below I will to be as thorough as possible explaining the architecture of my Network and documenting our setup so someone could possibly see what I may have messed up.
1st, here is a JPEG of a VISO drawing I made showing the Network overview:

Important Info:
I am able to SSH into the EdgeSwitch 16XG and ping the gateways of the VLANS (10.10.30.1 and 10.10.40.1). But if I try to login to the wireless networks using these VLANs no IP is given via DHCP on the pfSense appliance. Also, if I try to assign a port on any of my switches to only use a specific VLAN and then connect a laptop to that switch via RJ45 I do not get an IP (just APIPA address and ipconfig /release, ipconfig /renew does not help).Moving on...
Here is all the configuration I have performed:
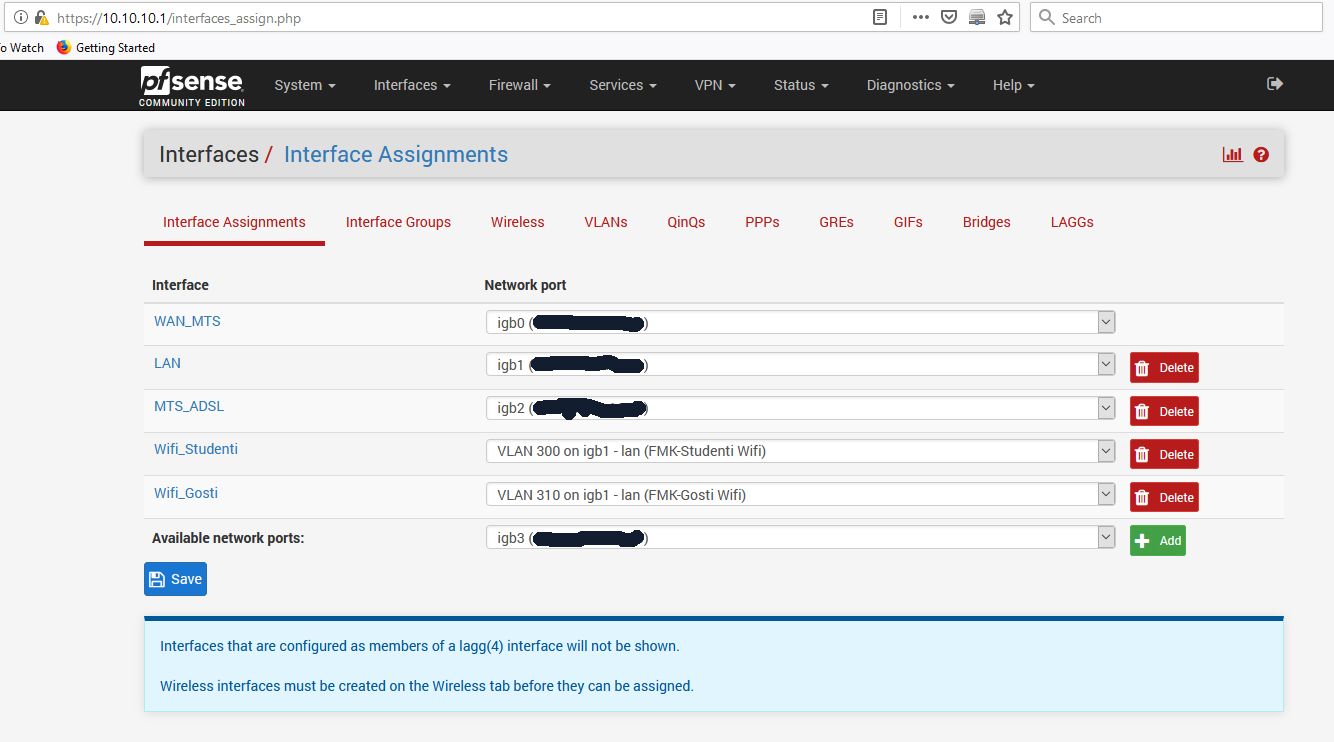
Interface assignments in pfSense. The Student Wifi will have VLAN 300, and the Guest Wifi will have VLAN 310. They are tied to the lan port (whcih you can physically see in the overview of the network above).
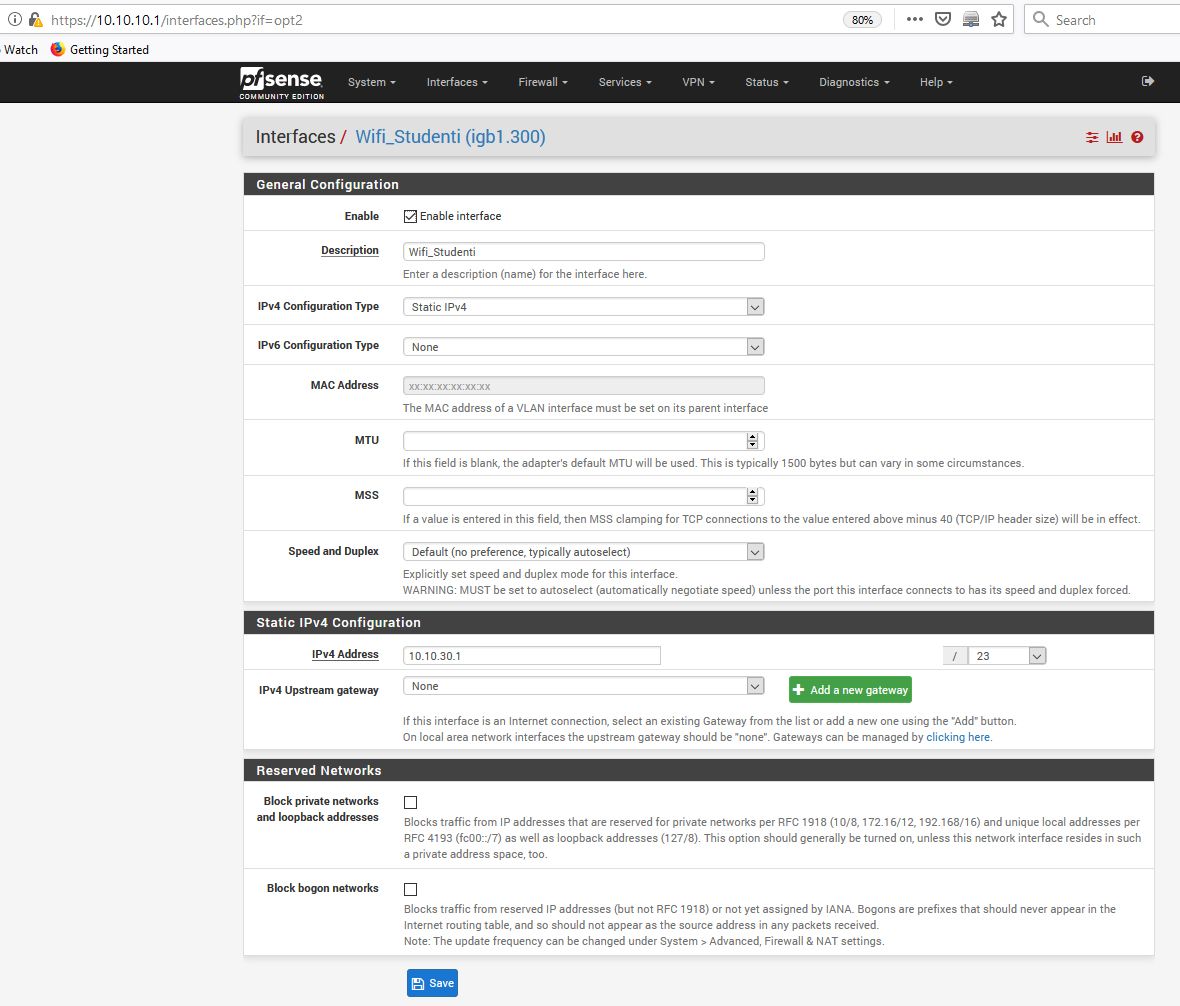
Screenshot of the settings within the Student Wifi interface for VLAN 300:
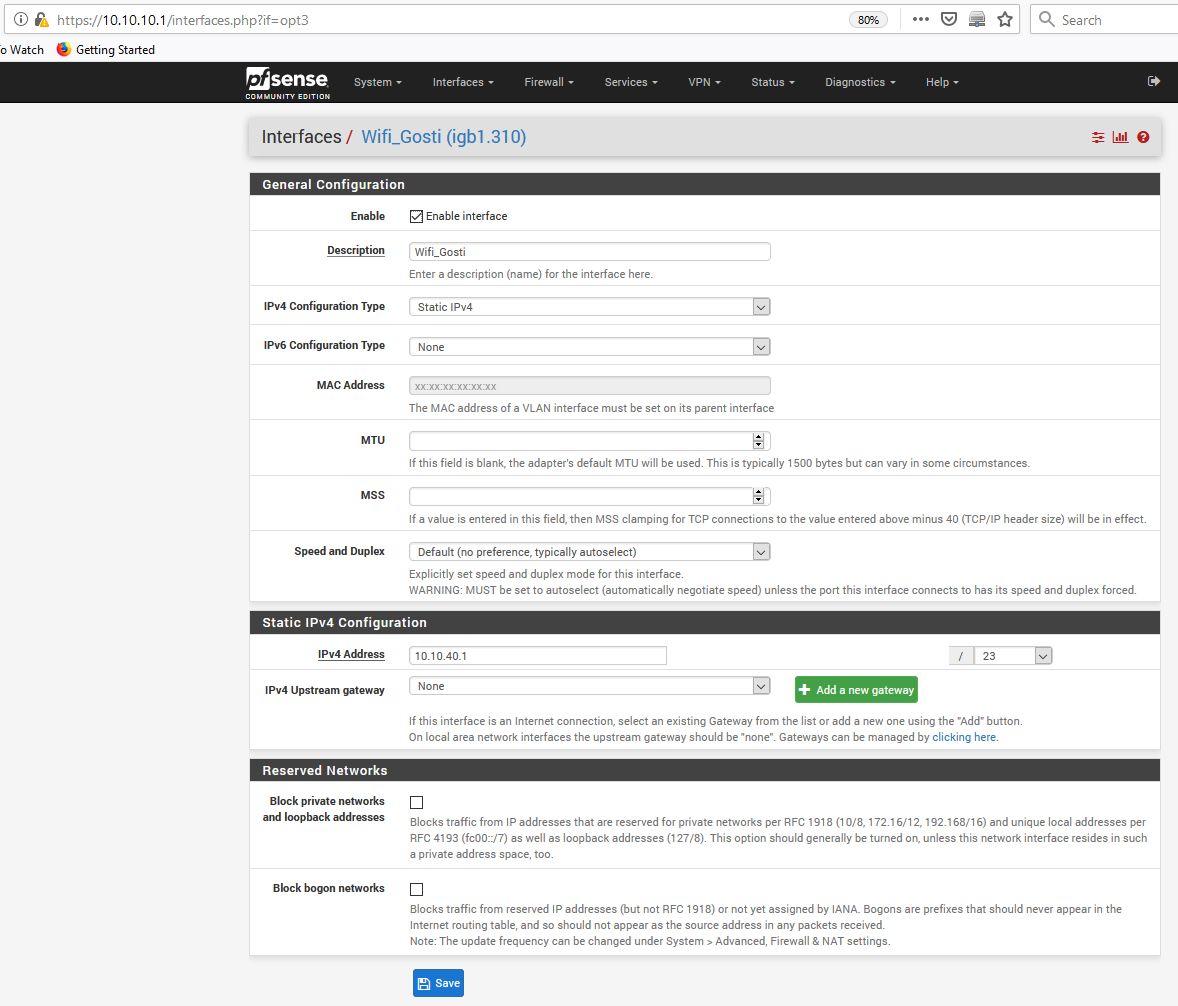
Screenshot of the settings within the Guest Wifi interface for VLAN 310:
Here is the screenshot for the VLANs under "Interface Assignments":
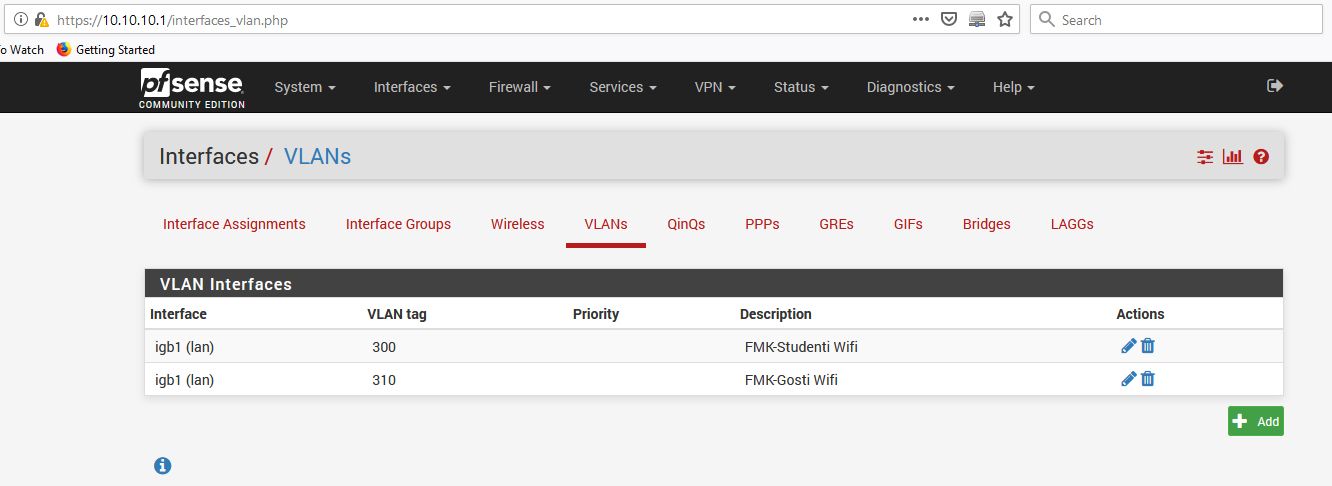
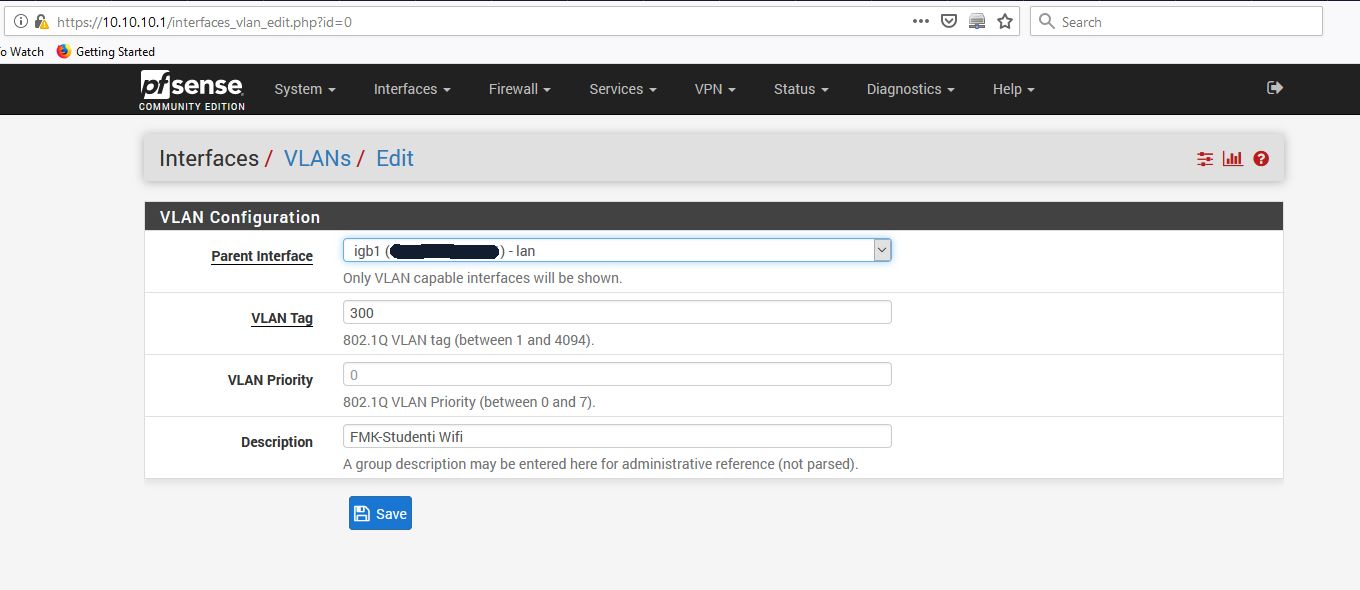
Screenshot for igb1 (lan) - VLAN 300 under "VLAN Interfaces":
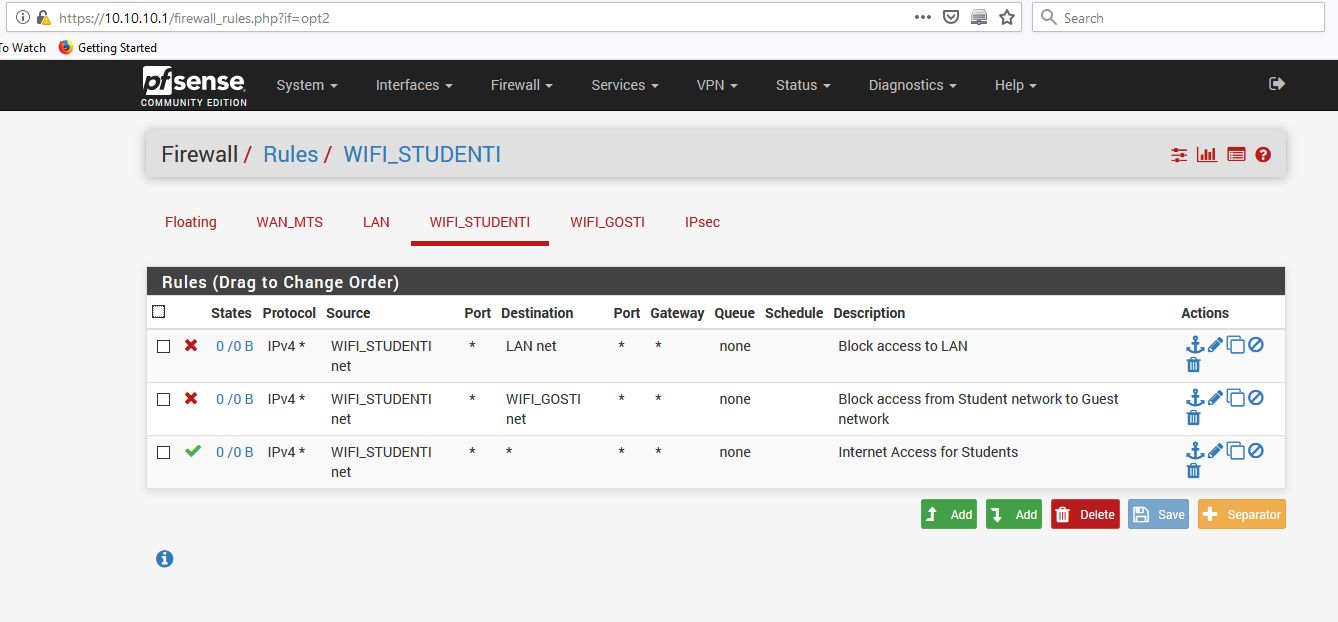
Screenshot for Firewall Rules - VLAN 300 (Student Wifi):
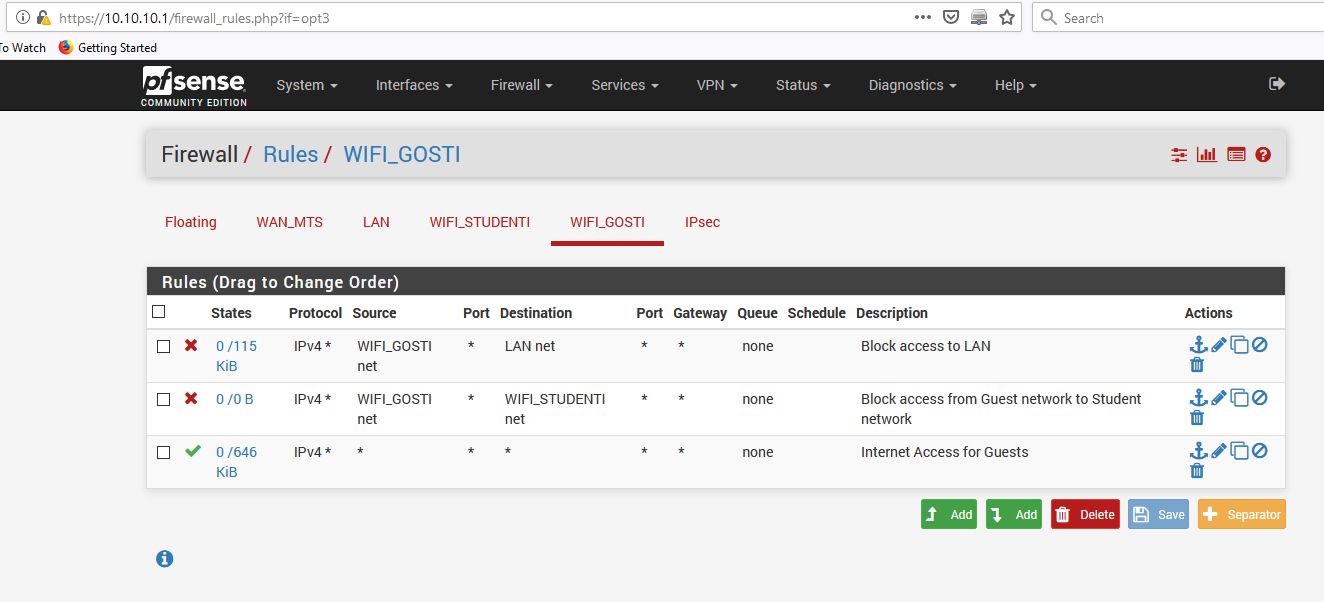
Screenshot for Firewall Rules - VLAN 310 (Guest Wifi):
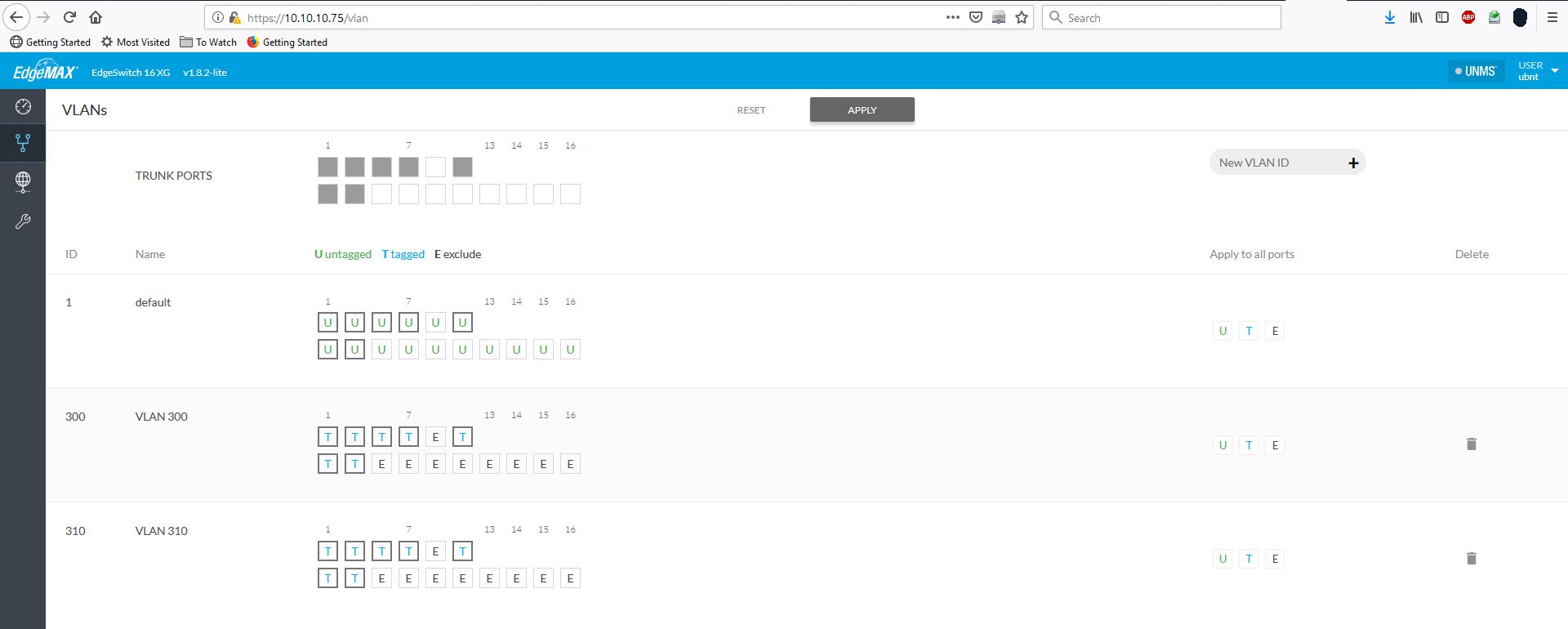
Screenshot of settings in the EdgeSwitch 16XG:
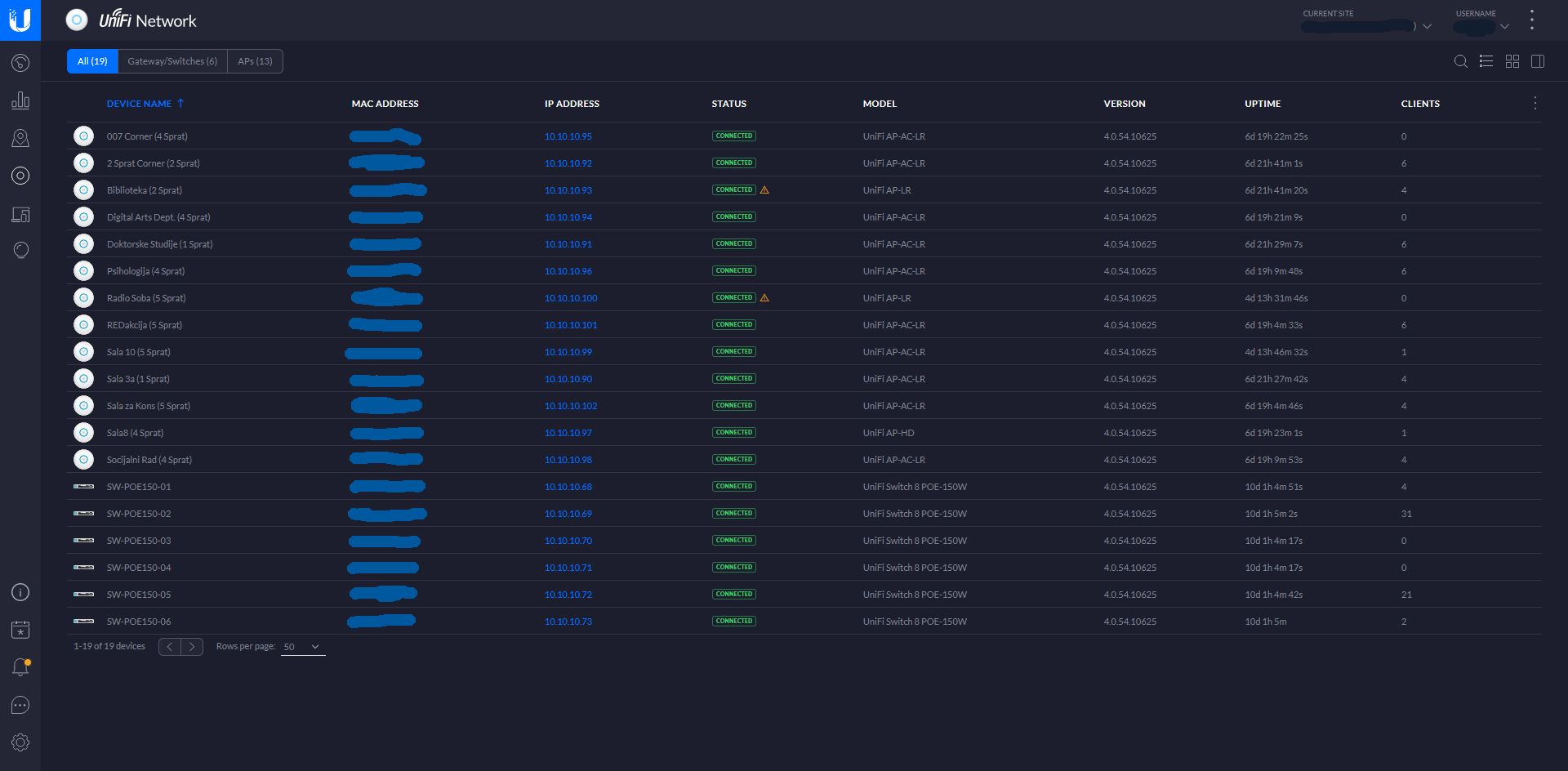
Screenshot of "Devices" in the Unifi Controller (o1/o3):
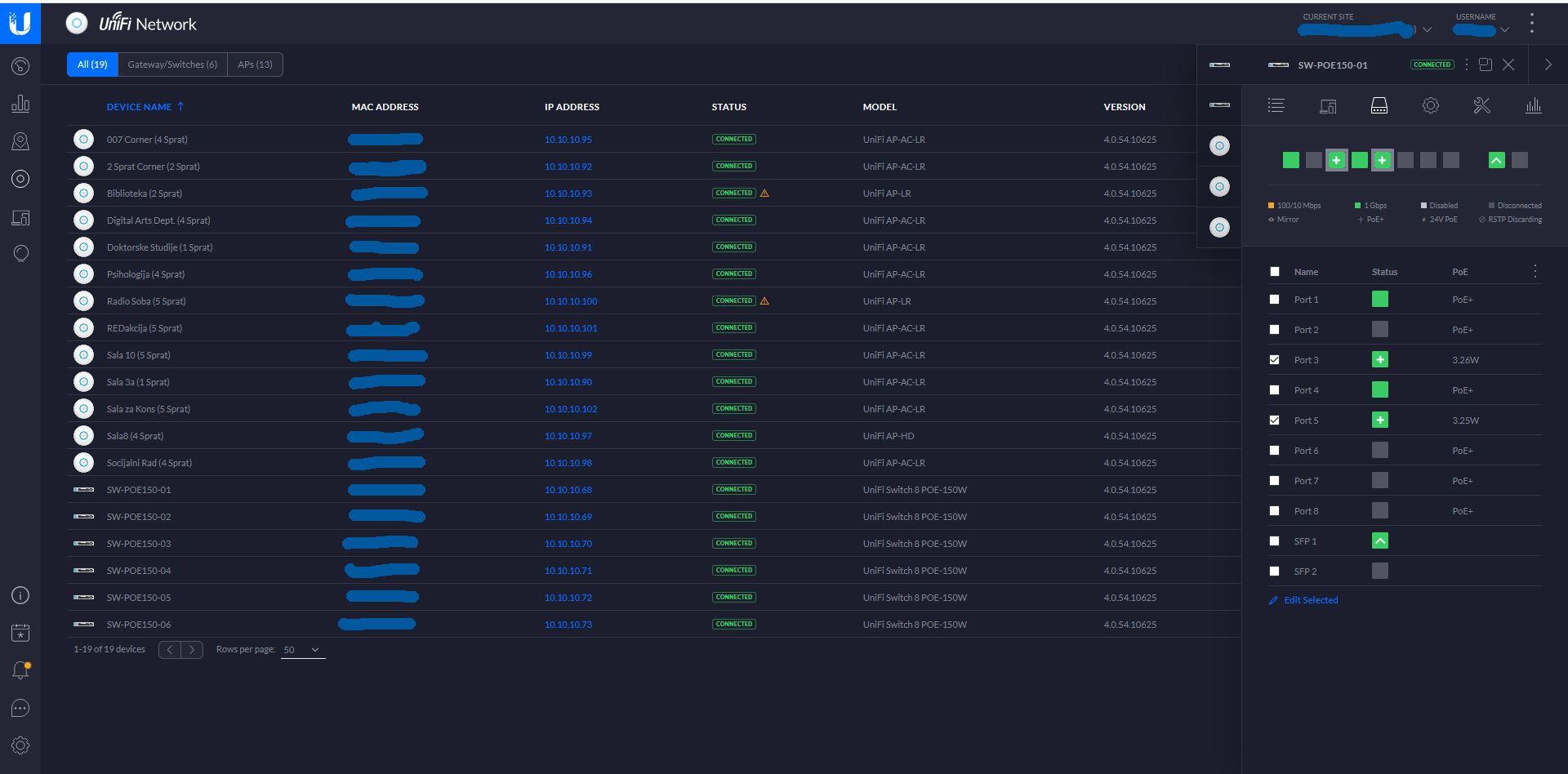
Screenshot of "Devices" in the Unifi Controller (o2/o3) - Looking at settings for one of the PoE switches:
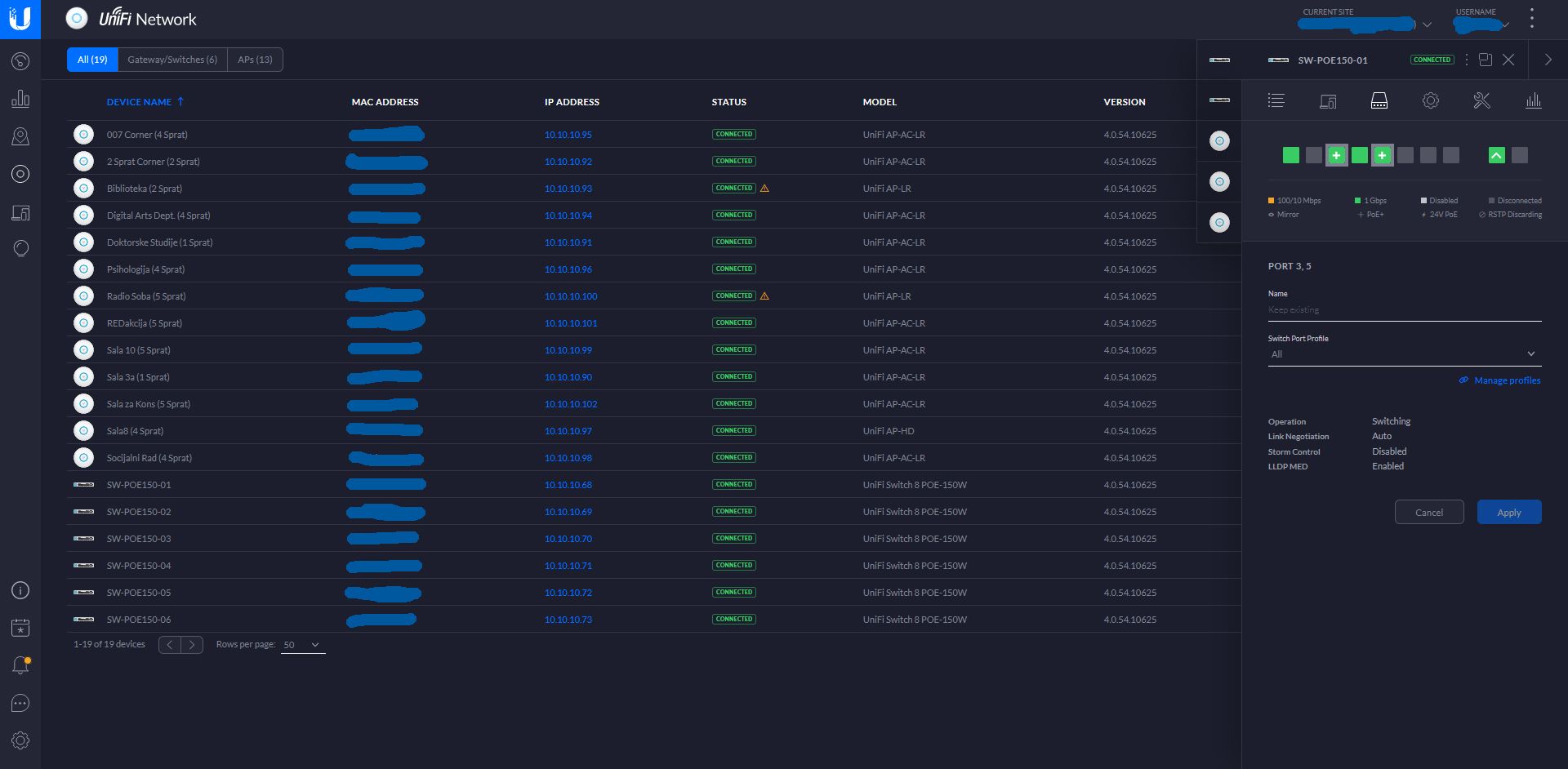
Screenshot of "Devices" in the Unifi Controller (o3/o3) - All VLANs set to pass through the ports on this PoE switch which goes out to the APs:
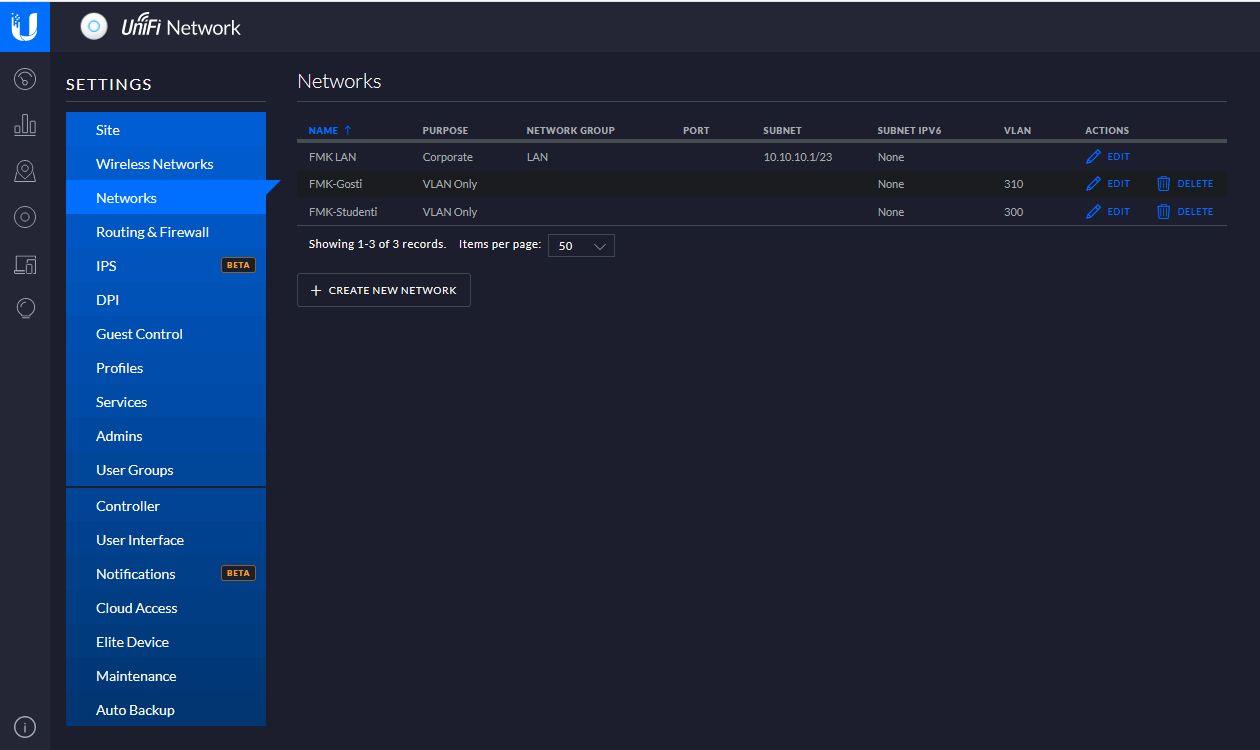
Screenshot of UniFi Controller (Settings --> Networks):
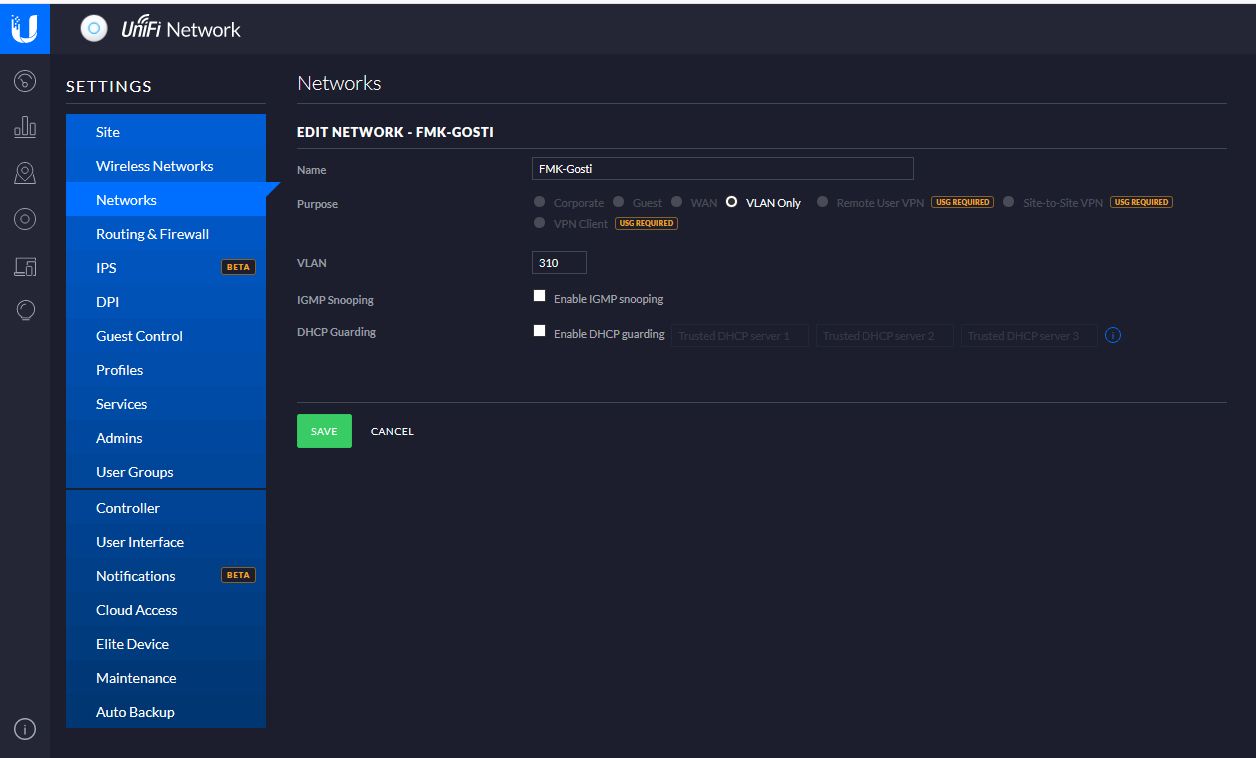
Screenshot of UniFi Controller (Settings --> Networks, Editing VLAN 310):
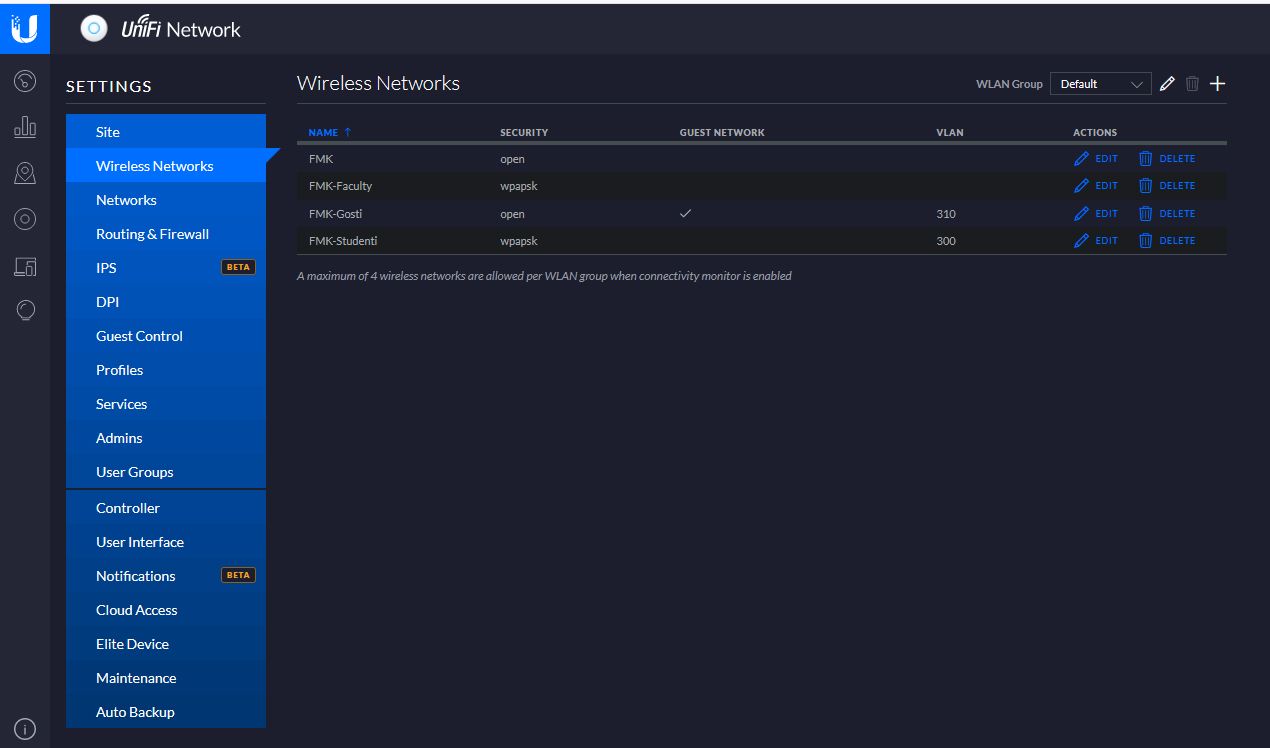
Screenshot of UniFi Controller (Settings --> Wireless Networks):
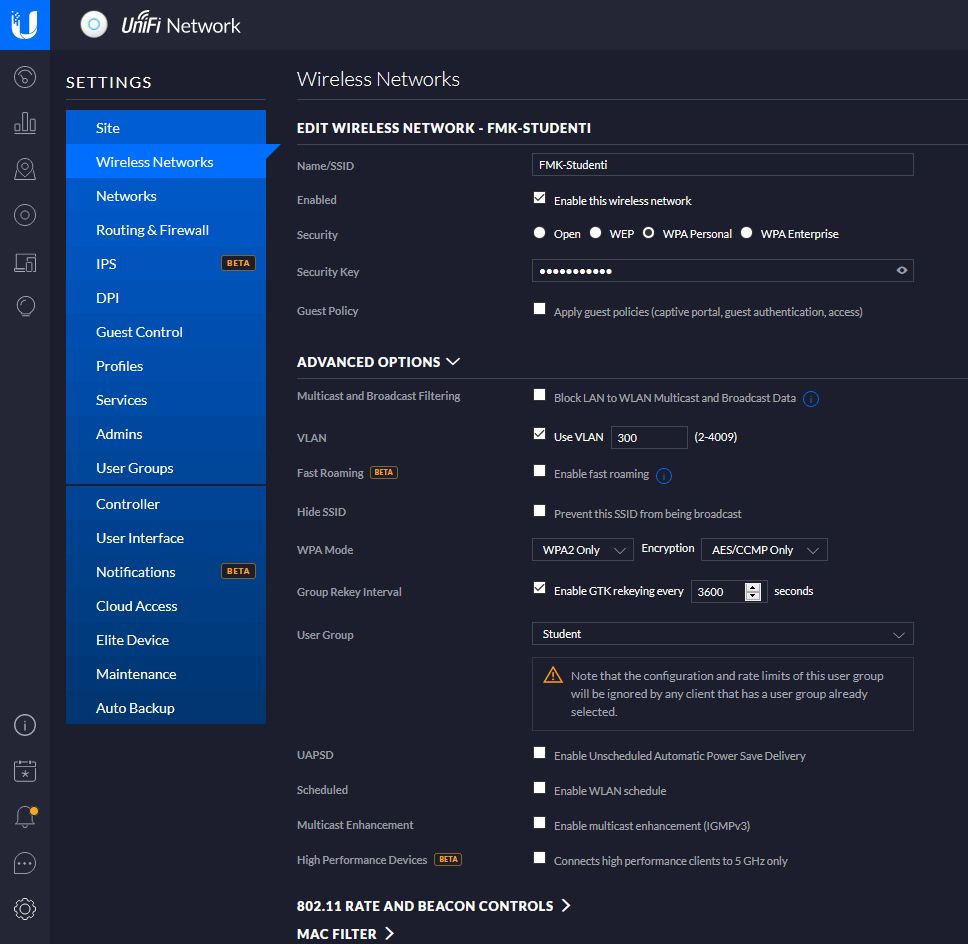
Screenshot of UniFi Controller (Settings --> Wireless Networks, Editing VLAN 300):
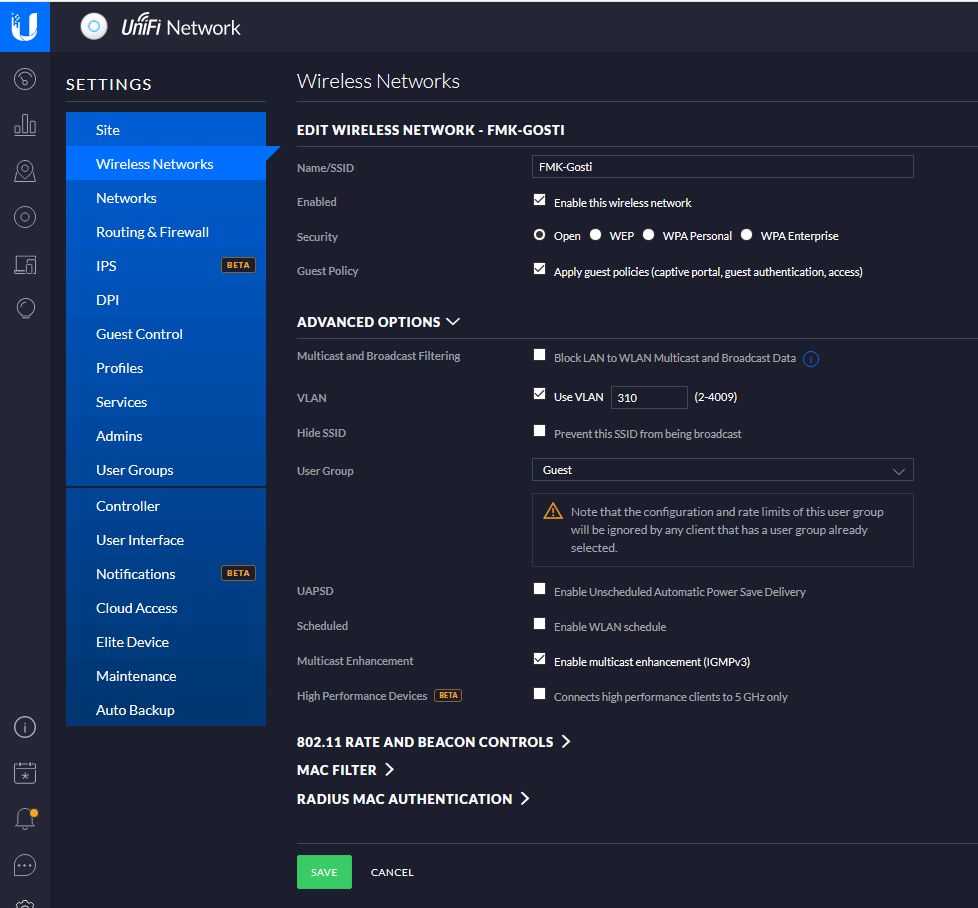
Screenshot of UniFi Controller (Settings --> Wireless Networks, Editing VLAN 310):
Ok, that is all. Have I misconfigured something? What am I doing wrong? Why can't my devices get an IP address when connecting to the Wifi attributed with these two VLANs?
-
I solved this issue myself. For any having similar issues you should try running the VLANs on a separate physical port - separate from the main LAN port. I'm lucky that our gateway/firewall has 6 ports and many are not in use ;)
So, to recap:
All the configuration in the above post is correct. All I did was make a new interface on a different physical port (specifically, igb3). This separated my VLANs from my LAN port on igb1. All worked after that as it should. -
For future reference there is no issue doing the untagged LAN interface plus tagged VLANs on the same interface.
You do have to configure the switchport correctly.
-
I run multiple interfaces where there is a native (untagged) and then tagged vlan on top of that.. There is no issues with doing it this way..
-
@Derelict said in Setting up VLAN: pfSense and UniFi Gear (150w PoE switches, EdgeSwitch 16XG, UniFi Controller, 13 UniFi APs):
For future reference there is no issue doing the untagged LAN interface plus tagged VLANs on the same interface.
That's often the way VoIP phones are configured, with the phone on a VLAN and computer port on native. Also, access points with multiple SSIDs.
As mentioned above, there is no reason why a VLAN cannot share the wire with a native LAN. The only difference between a VLAN frame and native is the contents of the Ethertype field, plus an additional 4 bytes for the tag.