Website won't load: operation timed out
-
could be a dns problem, what are you using as dns ? do you have another pc to try on the same lan?
-
Also a VPN ?
It's time to detail your setup.
-
@kiokoman
DNS server(s)
127.0.0.1
195.130.130.5
195.130.131.5
10.0.0.10
195.130.130.1110.0.0.10 is our local DNS-server
195.130.130.11 is the DNS of our provider.Allow DNS servers to be overridden by DHCP/PPP on WAN is Enabled
That's the reason why 195.130.130.5 & 195.130.131.5 is enabled.@Gertjan Not a VPN on the router, I used another VPN to check if it's accessible from outside the problemnetwork. What else do you need to know?
-
DNS resolution works well on pfSense ( use SSH or console access to test ).
Same thing for LAN devices ?Btw : p3 is out for a while now.
-
try to set 8.8.8.8 as dns on your network interface as a test
-
-
So squid is not installed, and you can still not resolve?
Out of the box pfsense "resolves" it doesn't forward.. Can pfsense resolve site your trying to go to?
Are you forwarding to 10.0.0.10 - why would that be on your list of dns?
Do a simple test on pfsense, can it resolve say google?
Once you have validated pfsense can resolve, then you need to check if client is asking pfsense for dns, and does it resolve?
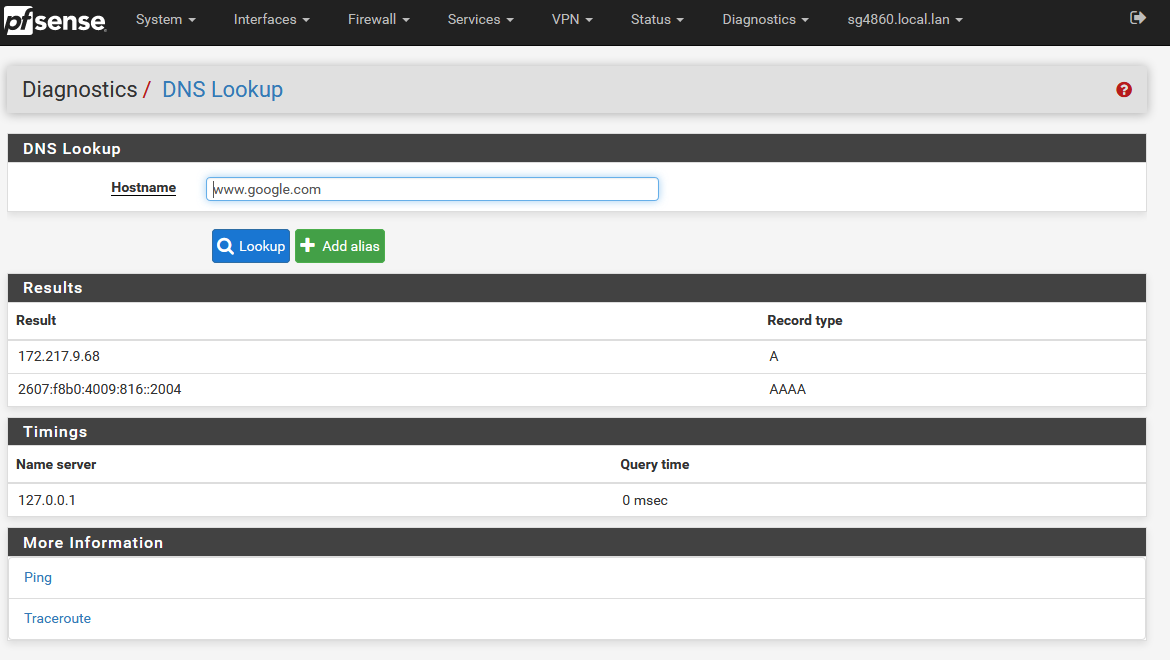
$ nslookup www.google.com Server: sg4860.local.lan Address: 192.168.9.253 Non-authoritative answer: Name: www.google.com Addresses: 2607:f8b0:4009:816::2004 172.217.9.68 -
I get this as result for DNS lookup on the pfsense for the problemdomain:
91.*.*.235 A127.0.0.1 0 msec 8.8.8.8 17 msec 10.0.0.10 32 msecWhen I do an nslookup, I get this:
nslookup google.com Server: UnKnown Address: 10.0.0.10 Non-authoritative answer: Name: google.com Addresses: 2a00:1450:400e:80e::200e 216.58.208.110 -
What is this 10.0.0.10, so your forwarding not resolving..
Did you setup some vpn client? Did you mess with your outbound nat?
Clients are using pfsense as their gateway? Do a simple traceroute from your clients to an outside IP.. Can you ping say 8.8.8.8 from your clients?
What are you lan rules on pfsense?
$ tracert -d 8.8.8.8 Tracing route to 8.8.8.8 over a maximum of 30 hops 1 <1 ms <1 ms <1 ms 192.168.9.253 2 10 ms 9 ms 9 ms 50.4.132.1 3 18 ms 9 ms 10 ms 76.73.191.106 4 8 ms 19 ms 10 ms 76.73.164.142 5 22 ms 13 ms 12 ms 76.73.164.154As you there from my client, its first hop is pfsense, and then next hop is outside to isp..
-
Yes, the gateway is the ip of the PFsense (10.0.0.254).
I can ping and has this as a result for tracert of 8.8.8.8
Tracing route to 8.8.8.8 over a maximum of 30 hops 1 1 ms 1 ms 4 ms 10.0.0.254 2 24 ms 12 ms 11 ms 81.83.0.1 3 10 ms 19 ms 13 ms 213.224.201.81 4 15 ms 14 ms 15 ms 213.224.250.117 5 23 ms 16 ms 33 ms 74.125.32.88 6 * * * Request timed out. 7 20 ms 18 ms 17 ms 8.8.8.8 Trace complete.And for the problemwebsite this is the result:
Tracing route to 235.*.belgacom.be [91.*.*.235] over a maximum of 30 hops: 1 1 ms 1 ms 1 ms 10.0.0.254 2 86 ms 16 ms 11 ms d51530001.static.telenet.be [81.83.0.1] 3 12 ms 11 ms 8 ms dd5e0c951.access.telenet.be [213.224.201.81] 4 15 ms 14 ms 25 ms dd5e0fa75.access.telenet.be [213.224.250.117] 5 * * * Request timed out. 6 18 ms 16 ms 14 ms 80.84.23.95 7 * * * Request timed out. 8 * 17 ms 17 ms svc10030.epemar7.isp.proximus.com [91.183.246.197] 9 * * * Request timed out. 10 24 ms 23 ms 34 ms 235.*.belgacom.be [91.*.*.235]I had OpenVPN installed, but not anymore.. I removed it a while ago.
Outbound NAT Mode is Automatic.
Rules:Automatic Rules: Interface Source Source Port Destination Destination Port NAT Address NAT Port Static Port Description WAN 127.0.0.0/8 ::1/128 10.0.0.0/16 * * 500 WAN address * Auto created rule for ISAKMP WAN 127.0.0.0/8 ::1/128 10.0.0.0/16 * * * WAN address * Auto created rule -
well clearly you leaving pfsense and getting to the wan via trace.
So what are you rules on your lan?
Don't understand the use of /16 for your local network - do you have 65K clients? But that is not going to be cause of your problem.
Is your browser still pointing to proxy? From your traceroute and your able to resolve.
So lets be clear is this ALL websites or just 1 or a couple?
And for the problemwebsite
That would indicate to me its just 1 site?
-
I will post the rules on Monday. (no remote accesss).
/16 is a gift from the past (schoolnetwork that grow very fast). For the moment we have +- 500 devices).
Of record: The whole network should be reconfigured. It's a work in progress, but not yet possible, as it is in use most of the time and I'm the only IT'er.The problem is with "some" websites. Most of the time we didn't notice it (thinking it's a bad website), but this time it is the website of an important supplier. So we need this website every day.
-
@Finduilas said in Website won't load: operation timed out:
"browser time out" error.
That doesn't seem like DNS unless it's resolving wrong. Assuming that really is the error seen on clients.
But yeah still unclear what clients are using for DNS here; is it pfSense?
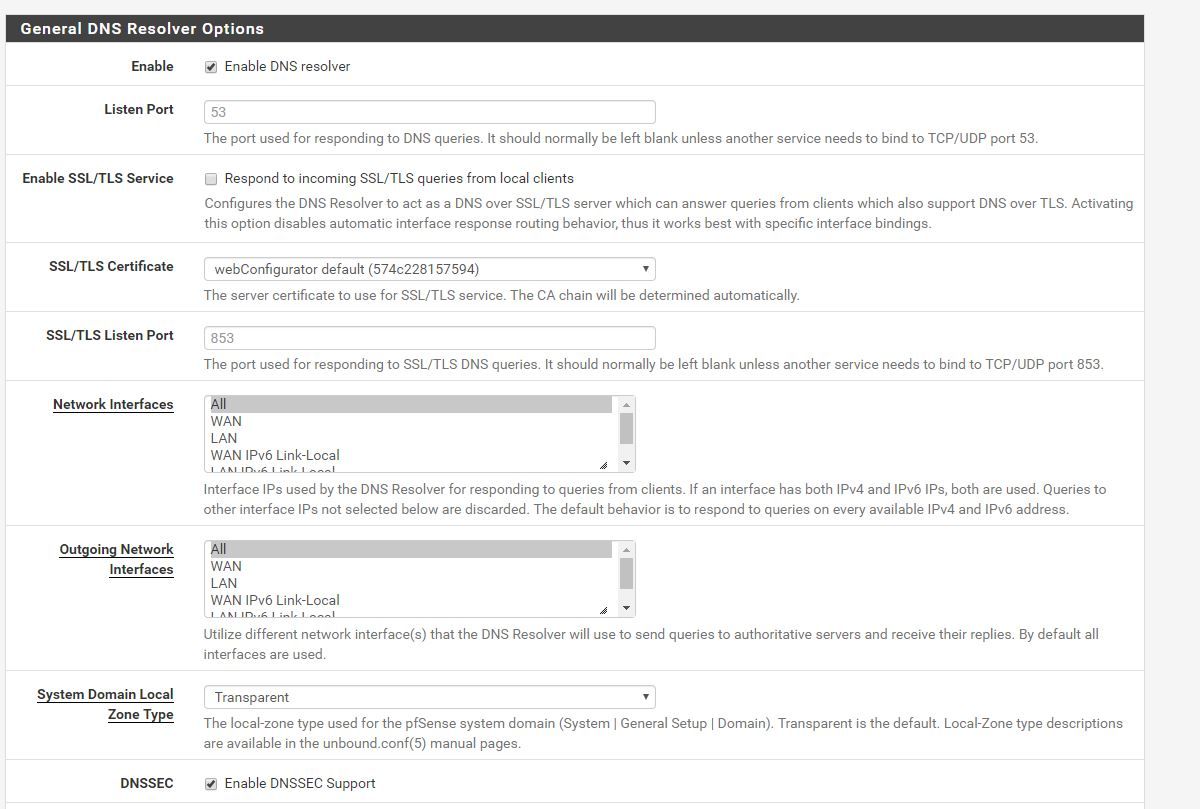
And what mode pfSense is using for DNS; is it using the DNS Forwarder? The DNS Resolver in forwading mode or the default Resolver settings?
Steve
-
@Finduilas said in Website won't load: operation timed out:
but this time it is the website of an important supplier.
But you are resolving this website to its IP.. So unless that is wrong? And your accessing other websites, and your not using proxy or ips.. How would the issue be related to pfsense?
Since on pfsense wan when you try and access this site - does pfsense sense the syn out its wan, what do you get back - if anything?
-
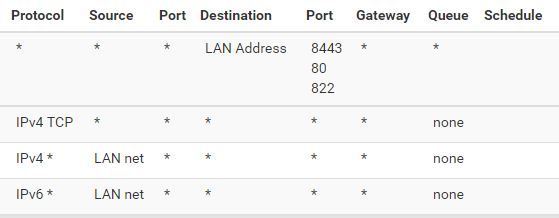
Picture of LAN-rules:
DNS-server 10.0.0.10 is an Windows Server. But the PFSense router is "new", configured by someone else (can't get in touch anymore).
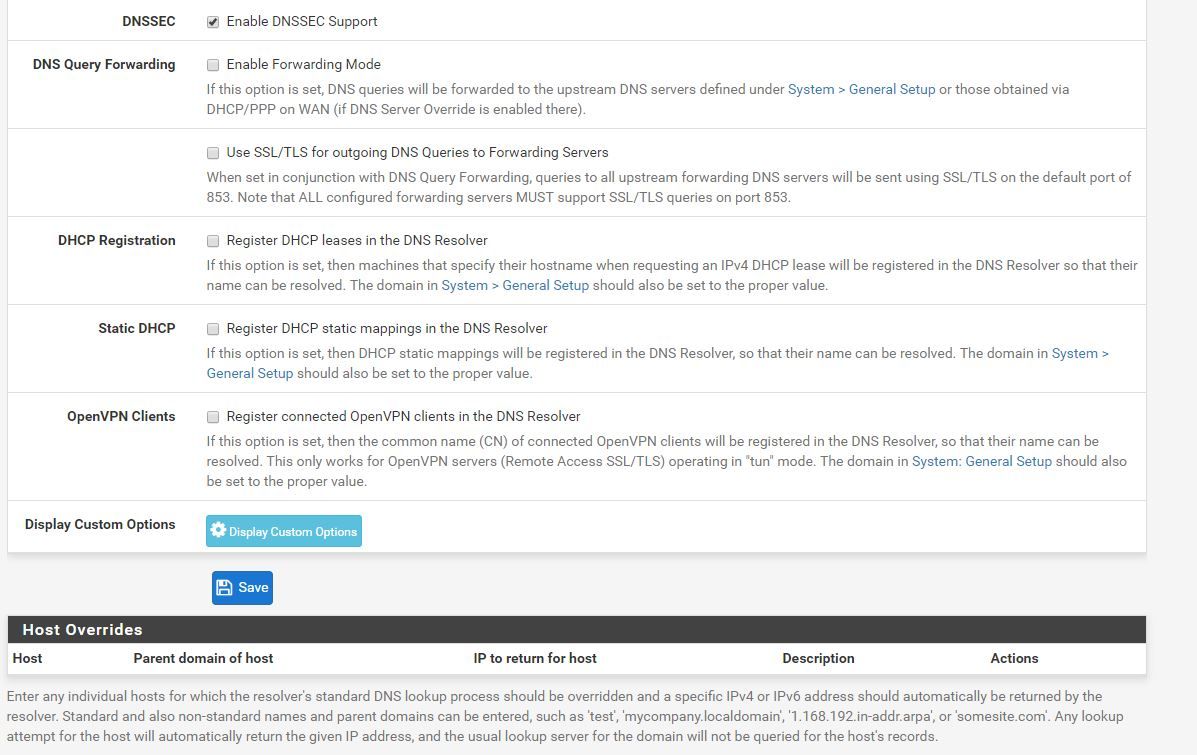
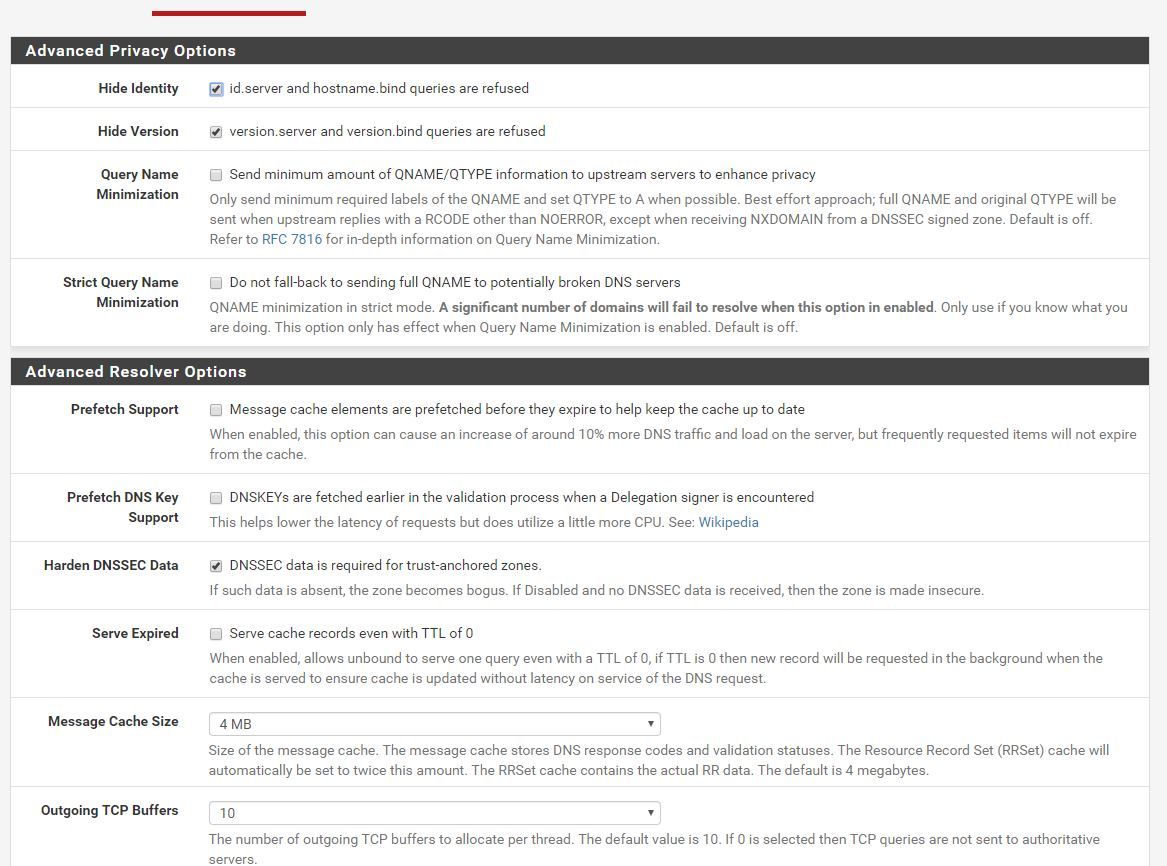
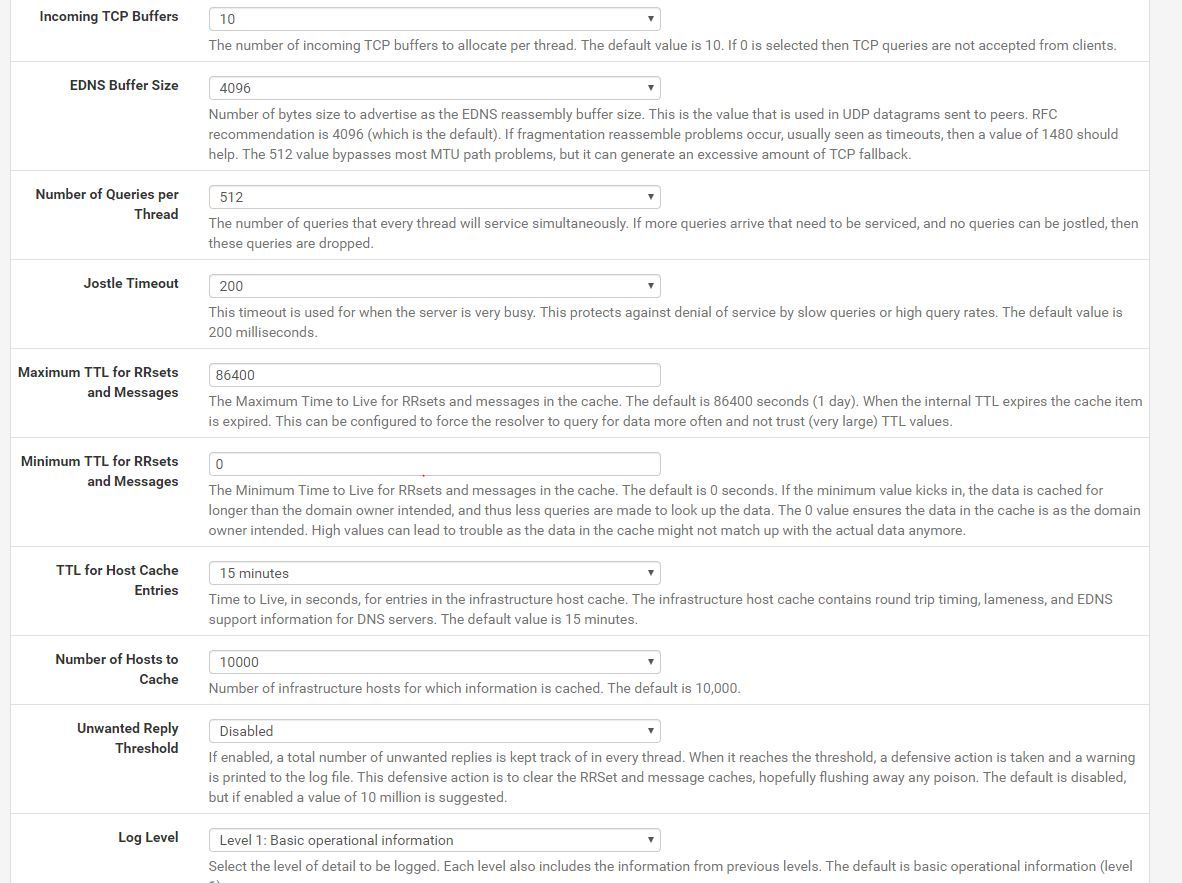
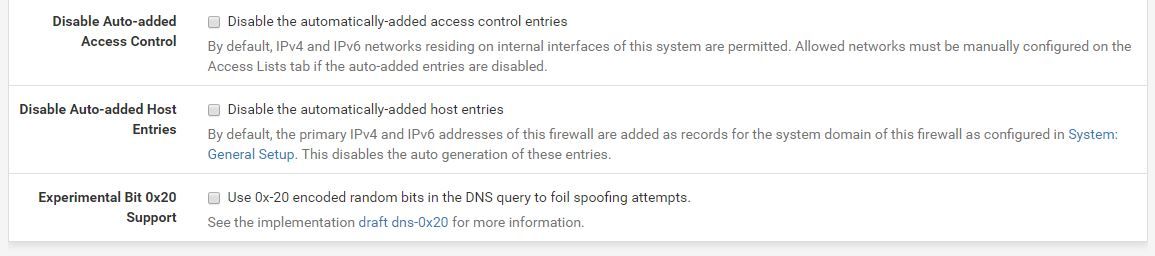
DNS-resolver was enabled, default settings (normally, see screenshots). DNS forwarding is disabled.
-
LAN rules :
The second rule is overlapped by the third rule - remove that second rule, because it's TCP only, thus very strange at best.
Rule 3 and 4 - the last 2 - handle all traffic just fine.@Finduilas said in Website won't load: operation timed out:
DNS forwarding is disabled.
So pfSense doesn't use 10.0.0.10 to resolve. It goes directly to "the source".
Are you using DHCP on your LAN ? How is the DNS setup on your LAN clients ? Static ? By DHCP ? Check the DHCP server page : what is the DNS to hand over to LAN clients (if set) ?Btw : why suing this local "10.0.0.10" DNS server (which probably forwards to again another DNS server, or it resolves directly, as pfSense does )?
-
Again - if you can resolve it, and just doesn't answer.. Unless your using proxy or ips.. pfsense not going to be doing anything different with traffic going there vs going to google.com
I would do a packet capture to prove to yourself pfsense is sending on your syn or not to the site.. There is nothing in your setup that you have shown that would stop one site over another site.
-
If you're using Squid/Squidguard you should really make sure both Squid and clients coming through it are using the same DNS server(s). If you are handing 10.0.0.10 to clients to use you should set that in Squid also.
However that would not explain why it still fails with Squid disabled. I agree I think a packet capture showing the failed connection would be the next step here.
Steve
-
@Finduilas said in Website won't load: operation timed out:
10 24 ms 23 ms 34 ms 235..belgacom.be [91..*.235]
He seems to be able to trace there, so unless he is running proxy or ips - its not going to be pfsense issue.. Maybe a mtu problem getting there?
Might be helpful if actually posted the site fqdn.. So we could test it even.. What is the big deal about posting some public site on the internet... If I had problem going to say www.cnn.com how would saying I can not get to www.cnn.com be any sort of privacy concern? Unless this is some sort of p0rn site or something you don't want anyone knowing you visit ;)
-
We are using a DNS server (10.0.0.10) because we have a domain. The public DNS of that server is 195.130.130.5.
The url of the problem site is:
||http://order.hanssens.be/order/||The lanrules are changed. (no overwrites anymore).
@johnpoz packet capture
15:51:27.776037 IP my.ip.. > 91.183.206.235.80: tcp 0
15:51:27.777709 IP my.ip.. > 91.183.206.235.80: tcp 0
15:51:28.025853 IP my.ip.. > 91.183.206.235.80: tcp 0
15:51:30.776740 IP my.ip...16614 > 91.183.206.235.80: tcp 0
15:51:30.778734 IP my.ip..29026 > 91.183.206.235.80: tcp 0
15:51:31.026104 IP my.ip...41937 > 91.183.206.235.80: tcp 0