multiple lans
-
Hi all,
I am wanting to finally switch over from an ipcop firewall as that project has been inactive for some time. Right now i have 1 red (what is wlan here) 1 green, and 1 blue network. The green network is for our normal network, and the blue is for our guest wifi. If i make 2 LAN networks when i set up pfsense, will they automatically not be able to talk to each other, or do i have to set firewall rules to make them that way?
thanks,
jason -
With pfSense, only LAN gets a rule that allows all its clients access to anywhere. All other LANs (OPT1, OPT2, OPTx...) start with no rules and need to have at least one rule added to allow access to anything.
-
If you buy, or build a box that has pfsense on it, you can get one that has as little as 3 ports. You say nothing about using VLANs, so I would assume that you may or may not know how those work. If you do, a 2 port pfsense box would work just fine. You just have to have a smart VLAN capable switch on your network and setup pfsense to have a VLAN network on it. It's pretty easy to do.
Anyway, the green network you could use for your LAN network. This network by default can talk to anything else on the pfsense box. If you setup a separate LAN connection for guests (your blue network), it will be able to talk to NOTHING until you setup some firewall rules to pass and/or block traffic. Where you want that network to go, and what you want it to talk to, is completely up to you.
Jeff
-
-
@kirshman said in multiple lans:
will they automatically not be able to talk to each other, or do i have to set firewall rules to make them that way?
And in addition to @KOM: If you later add rules for your WiFi or Guest WiFi network and want it to be able to access anything on the internet but no internal things at all, you'd have to do it with at least two rules. One blocking access to any internal networks (hint: create an RFC1918 alias and add all private networks there and use that as destination) and a second one (like the allow any default rule on LAN) that allows traffic to "any" (not WAN network -> that is NOT the internet!)
Greets
Jens -
@JeGr said in multiple lans:
you'd have to do it with at least two rules.
You "could" do it with one rule - depending ;) You could use a ! rfc1918 rule, which states as long as not rfc1918 allow, etc. But this is not always the best way to do it, and if using vips could cause problems, and would also depend on what client is using for dns which might not work if dns they are using is on different rfc1918 network then client, and or say pfsense IP ;)
Generally speaking yes it is better to use a explicit block, and then allow in 2 rules.
-
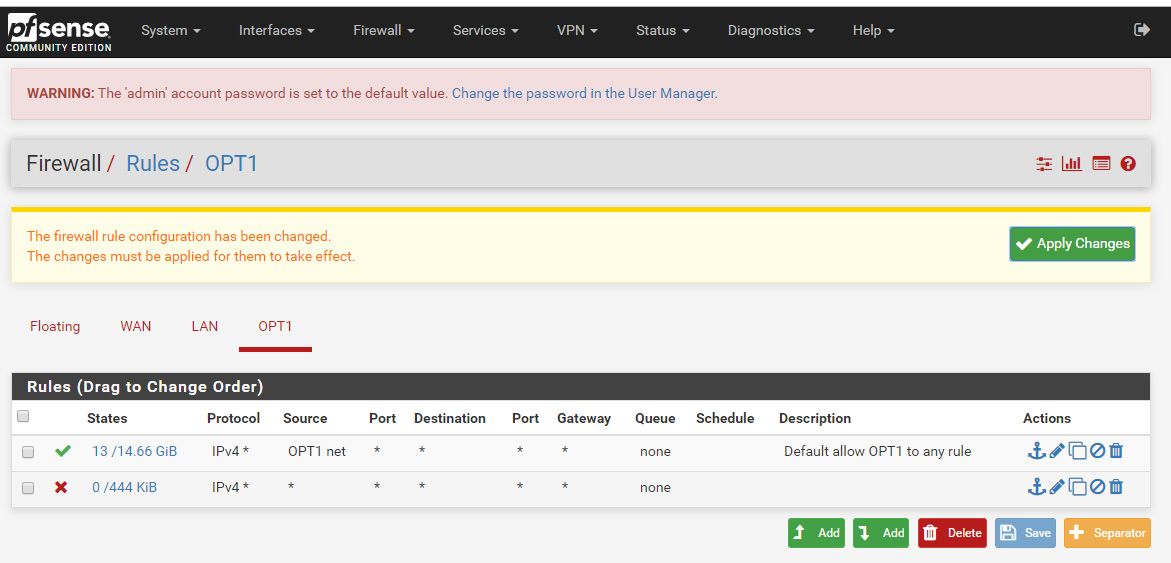
alright, thanks for all the help so far! i'm new to firewall rues. it was just install and go with ipcop. does this look right to have my opt1 network connect to the internet but nothing else? Ignore the default password warning, that has been changed sense this screenshot :)
-
No
Rules are evaluated top down, first rule to trigger wins, no other rules evaluated. For that 2nd rule to show hits means your getting traffic to that interface that does not fall into OPT1 network.. Which really shouldn't happen.. Do you have downstream networks, are you running more than 1 L3 on this L2 network?
Here is how you would normally just allow internet.
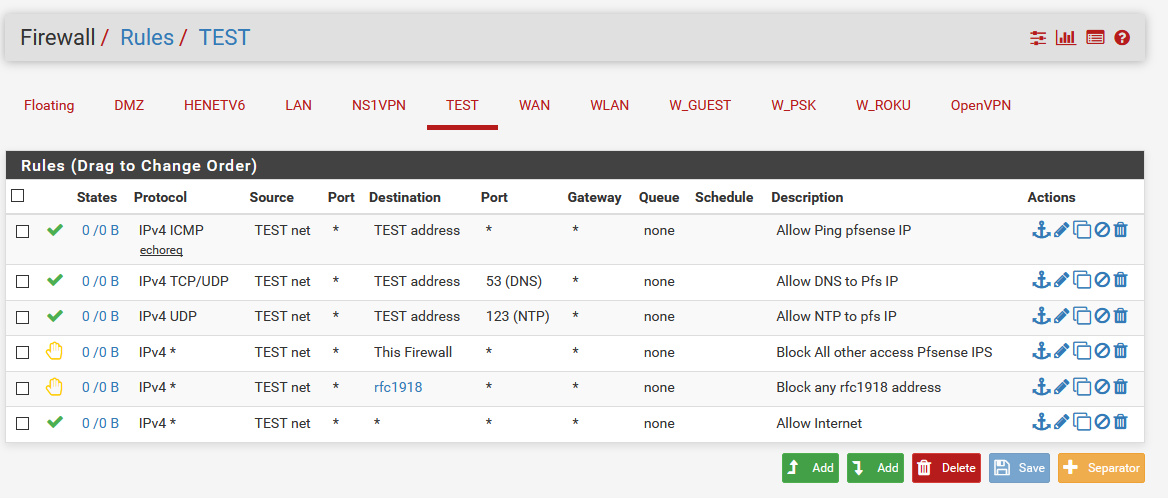
You can adjust for your own needs.
So first rule allows ping pfsense IP, so you can validate connectivity.
Next allows to ask pfsense IP for dns
Next allows to ask pfsense IP for ntp
Next blocks all other access to ANY pfsense IP, even wan IP.
Next blocks all access to any rfc1918 address (this is alias with 10/8, 192.168/16 and 172.16/12)
Next allows access to anything else - ie internetYou can use block if you don't want rejects, but reject can help with local clients knowing instantly they can not get there without waiting for timeout and sending retrans.
Adjust as you see fit for your own wants.. Maybe you don't want clients to ask pfsense for dns or ntp? Then pull those out, your block to this firewall would then prevent such access, even to pfsense wan IP, even when it changes, etc. etc.
Just remember that rules are evaluated top, down and stops evaluating when it hits an allow or block rule. So think about where your going IP and port, and walk down your rules. If you do not hit a rule that allows, or blocks and you get to the end then the traffic would be blocked by the default deny rule (that is hidden)
-
thanks for that detailed response. Really helps me get my head around this!!
