[Q] pfSense on Hyper-V 2012R2 - transparent mode - possible? {YES}
-
Hi, i have tried to get this to work without success. So, i ask:
Is it possible to run pfSense firewall on Hyper-V 2012R2 in transparent mode?
Thank you!EDIT: YEST, it is possible and it is working after i enapbled MAC Spoofing on both virtual NICs.
-
So setup as a transparent firewall? WAN and LAN bridged?
I see no reason why not. What have you tried? How did it fail?
Steve
-
Yes both bridged and the bridge gets the management ip..
I can not get the traffic to pass either way. -
Well how do you have it all connected from your physical network to your VM pfsense?
-
disable outbound nat
Tunable
net.link.bridge.pfil_bridge and set the value to 1
net.link.bridge.pfil_member to a value of 0
net.link.bridge.pfil_onlyip 0“Interfaces / WAN” disable/uncheck “Block private networks and loopback addresses” and “Block bogon networks“
the IPv4 and IPv6 configuration type must be set to None for WAN and LAN
Under Firewall / Rules select the WAN interface and create a rule that passes all traffic over the interface -
@kiokoman said in [Q] pfSense on Hyper-V 2012R2 - transparent mode - possible?:
All o f that i have done...no avial. I am pulling my hair out...and i don't have much :/
All virtual interfaces are connected to phisical NIC.
If i put another hdd in the VM with Untangle...it works just fine in transparent mode...
Please, any more ideas?
Thanks alot -
@mdalacu said in [Q] pfSense on Hyper-V 2012R2 - transparent mode - possible?:
All virtual interfaces are connected to phisical NIC.
And how and the F would that work? You mean multiple physical nics? With different L2 networks? You mean physical nic with different vlans on it.
Draw up how you have your network connected... And how this is tied to your VM network..
Untangle use ARP poisoning, which is just UTTER CRAP way to do anything... And that is not a bridge that is just poisoning the network so devices think untangle is the IP of the gateway..
Nobody can help you if you don't give details of how your setup..
-
Anything here that might help?
https://content.spiceworksstatic.com/service.community/p/post_attachments/0000161351/5355bf8a/attached_file/Transparent_Firewall-Filtering_Bridge_-_pfSense_2.0.2_By_William_Tarrh.pdf
Like this?13. Overview and Understanding of the Transparent Bridge I use the WAN as the management interface because I was unable to reach anything external, obtain updates or browse packages when the LAN or Bridge was configured as the management interface. -
This you can bridge
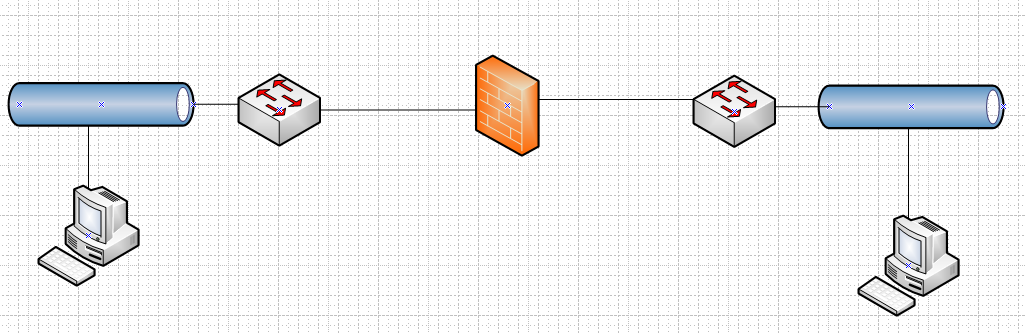
This can not
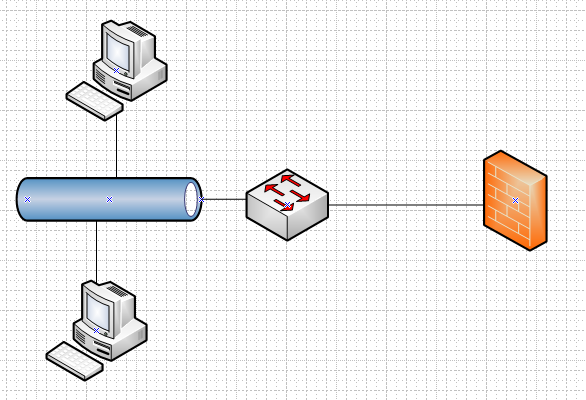
Are you trying to bridge 2 physical separate L2 networks, or are you 2 different layer 2 networks you wanting to bridge isolated via vlans on a switch, etc.
edit: Bridging is almost always the WRONG choice.. And should only be done if you can not do it any other way.. Why can you not just route? What exactly are you trying to accomplish via this bridge? Do you need to firewall devices from each other that have to reside in the same L2 for some reason only known to you?
Bridging is a solution when you have to combine L2 vs multiple types of interfaces.. Say wifi to wired, or fiber to ethernet.. And your bridging devices has the multiple interfaces, etc.
Or you want to do some sort of transparent firewall and can not alter the network in any other way, etc. etc..
Again bridging is almost always going to be the wrong choice..
What is the end goal here?? And we can discuss how to best accomplish that goal.
For example if your wanting wireless to be on the same L2 as your wired devices, vs using an interface on pfsense to connect or be your wifi you would use an AP and just connect it into the wired network of your switching infrastructure.
If your router has fiber interface and your switching infrastructure does not, and you want L2 connected via fiber to be on the same ethernet L2, it prob better to just get a media converter for like $50 bucks tops and connect that into your switching infrastructure. Or just get a fiber sfp or sfp+ to connect to your switch.
edit: The only time I would look to bridging on pfsense would be, all the computer stores are closed, or amazon can only get me the proper equipment in 2 days and I need it up NOW for production purposes.. ;)
If you think bridging is the solution to whatever your end goal is here, your more than likely looking at the problem from the wrong direction.
-
@johnpoz Hi! i manage it for a small firm..40 stations..remote ;) All are connected behind a small router in an unmanaged switch. From this i have to move...
The problem is that the management hired an security audit and concluded that the LAN is not considered safe anymore (someone could physically plug an rouge device and listen to passwords )...and i must implement a lost of things in order to separate servers form lan and also implement 802.1x. I have studied a little bit and conlcuded that pfSense is the winner in my situation. So, i have bought a managed switch and i will migrate one client at a time. Between the servers and the clients will be pfSense in transparent mode so i don't have to change a lot of things. All the servers and pfSense are residing on the same host. I use multiple NICs to achive this.
Short verion: I need pfSense in transparent FW mode with FreeRadius and a transparent proxy so i can filter web connections...in a virtual machine...
Do you think i am able to achive this? Thanks.Edit: I have the transparent FW part working. I had to enable in HyperV MAC Spoofing on each interface.
The transparent proxy is another thing...i can not do it. I need to get reports for web traffic and to be able to block some URL. I try to do it first on 80 then i will move to ssl inspection
As soon as i enable transparent proxy i can not reach anything on port 80...and yes, i have changed the web managemnet port. Squit and transparent both are listening on OPT1 brige. Do i have to enable somenting in tunabale or another firewall rule?I know it is phisically posible since Untagle is doing this by default.
Thanks agan -
@provels Yes this is the first thing that i ran into...then the phisical nics and then ...MAC Spoofing.
-
@mdalacu said in [Q] pfSense on Hyper-V 2012R2 - transparent mode - possible?:
I need pfSense in transparent FW mode with FreeRadius and a transparent proxy so i can filter web connections
Why would you think this, that is not the case at all.. There is a huge difference between running a transparent firewall and and a transparent proxy. Neither are normally a good choice.. And should only be done when there is no other way..
You have not given any reason why this could not just be routed with a explicit proxy. And sure you could do transparent proxy as well.. But to be honest would block vs allowing transparent.. And only do transparent for something that can not use a proxy.. Some stupid iot device or something that does not officially support proxy. And such devices should be on their own vlan anyway.,
Why can you not just use pfsense as normal L3 firewall router, and run proxy on this... Why do you think you need it to be transparent?
-
@johnpoz Because if all falls apart i just a cable away (putting it between SWitches or do some briging on the host)...and do it remotly...
And i am just one guy doing all this beside my office hours :-)) -
So your trying to set this all up remote? hehe dude you should be on site for such setup..
-
@johnpoz After i setup this on premises i will manage all remote like i have done for several years. But i need in case of FW failure to let people work with minimal disturbance and not wait for me to get there.
I really hope that i will be able to do the transparent proxy....right now i am stuck... -
You can't use Squid in transparent mode on a bridged firewall. The redirect rules do not function on bridged interfaces.
Or at least they did not last time I tested this:
https://redmine.pfsense.org/issues/1620You might also consider that the usefulness of a transparent proxy is limited anyway. Once encrypted SNI becomes widespread you will no longer be able to see or filter https traffic without full ssl intercept.
https://blog.cloudflare.com/encrypted-sni/Steve
-
@stephenw10 Thanks for answering!
I just wanted to make it work like untangle in transparent mode.
I will see what i can do....
The Freeradius part it is working...i hope squid will do to....but transparent.... -
Not if it's redirecting on a bridged interface. You can try the patch linked in that bug report. It's been a while since I tested it but I was never able to make it work despite trying every combination of things I could think of. Something may have changed since then.
Steve
-
@stephenw10 Yes, you are right...not working. I have tried everything that i can think off. I was hoping that fixing the problem i was having with Freeradius will also fix this, but no ( i had to manually add the name of the server in DNS overwrites) The patch seems to be merged since 2017...
What else could i try for transparent proxy to work on bridged interface?
Thanks. -
You could try a 2.5 snapshot. They are built on FreeBSD 12. Since this appears to be an upstream limitation in pf that may have been fixed.
Steve