openvpn unable to connect to anything on lan but pfsense itself
-
hi
users are able to connect ok, but cannot get to anything other than 10.10.0.254. the IP's i am using are on tap mode 10.10.0.30 through 10.10.0.36
they can browse through the vpn and out, whatismyip.com shows the proper WAN IP of the pfsense box so it is going through the vpn for internet traffic, just lan is not working.i even have a static route set to 10.10.0.1/24 manually on the tap interface, that did not work.
i also tried setting a lan gw on pfsense of 10.10.0.1 and the pfsense box can ping that, but the clients cannot, whether it is set manually or the lan tries to forward it.
using pfsense gui for configuration
i cannot ping anything on the local lan, only the 10.10.0.254 of the vpn vmx1 itself (vmware esxi, single virtual switch, 2 port groups, one with vlan for wan, one for vlan with lan).the port channel and vmware switch is working as i can browse on the lan to the pfsense box and ping it fine.
i had the same issue in tun mode, i could connect, ping the gateway i did get, however it wouldn't route me to my other firewall which gets me access to many vlans and subnets i need to get to.
what is the easiest way to do this?
i would prefer tap mode, i just need to be able to route through the pfsense lan not just to things on the same lan, but to many other subnets on a second gateway.
i also tried pushing routes but because i can't even ping or get to the second gateway that is on the lan, that doesn't work.all the firewall rules are set on the LAN and VPN of destination * source *
ideas? -
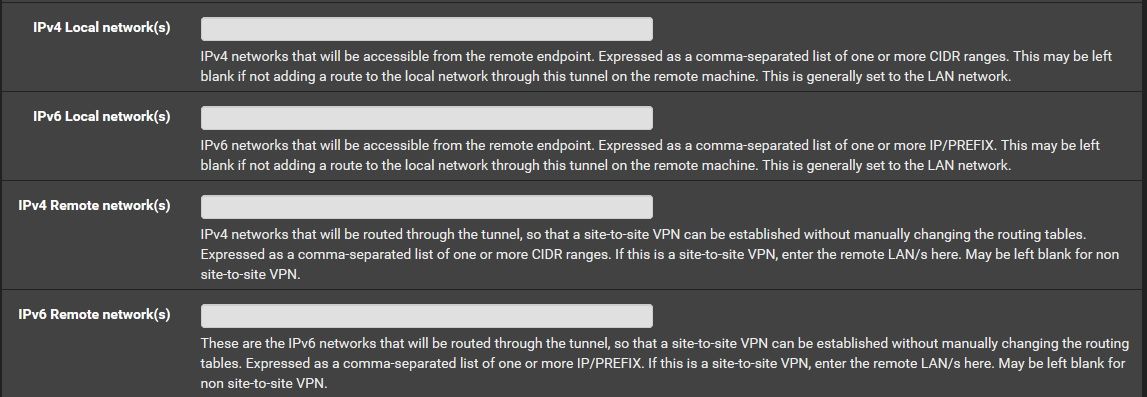
you just need to define the network you want to access here
-
@kiokoman
hi
I do have 10.10.0.0/24 added already on the ipv4 local networks
I also tried adding more like 10.1.1.0/24 and they didn't work at all.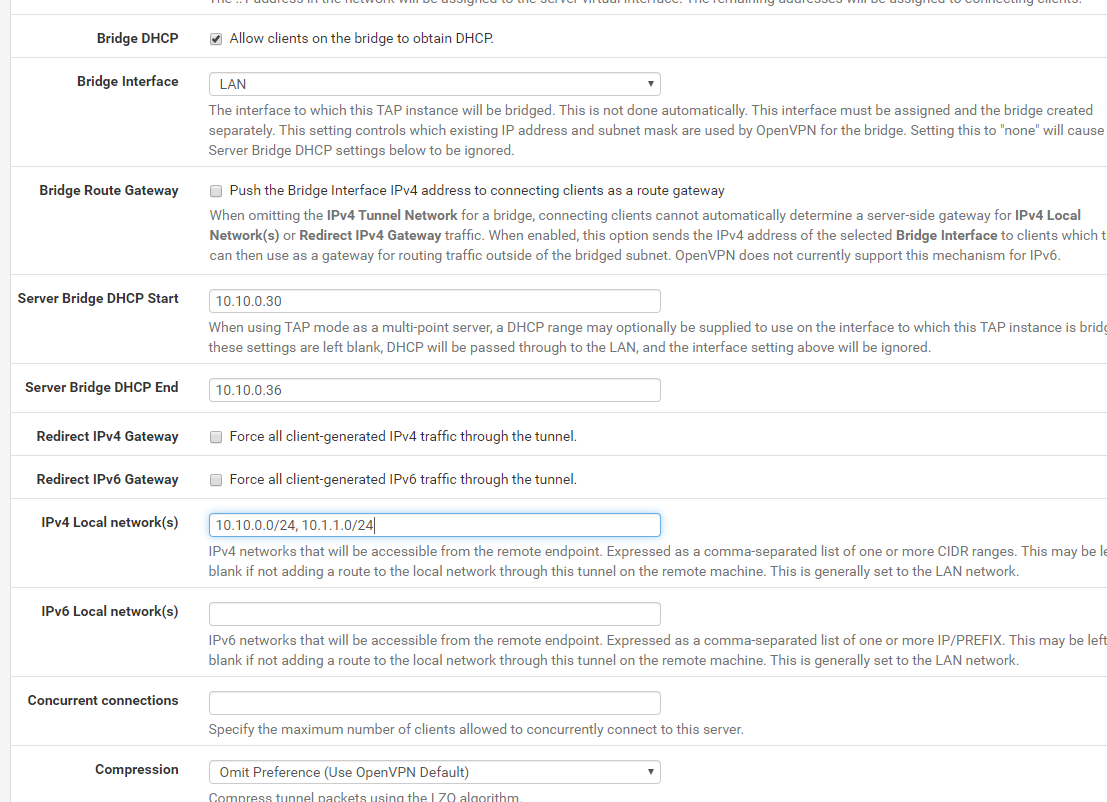
-
@darrenh I figured it out, it wasn't related to tun or tap mode at all, nor the VMware.
I found one other person had done it, buried in another forum from 5 years ago.
you have to setup a nat outbound rule by changing to hybrid mode, and setup the LAN interface, network being your vpn user subnet, and set the destination to either just the local lan, or in my case I set it to any, and use the fw interface as the masquerade.
that way the traffic from the vpn users gets masq'd as the local lan and not the 192.168.55.1 it auto assigned for the tunnel subnet.
as soon as I did that, I can get to everything fine :)