Using printer on a separate subnet/vlan
-
I have a pfsense installation at home with two vlans, vlan10 and vlan20.
vlan10 has a HP LJ100 printer attached (LAN-cable) with ip 192.168.10.7.
I'd like to use this printer from a wireless PC connected to vlan20 with ip 192.168.20.20.
The printer works fine as long as I am on the same subnet, but I cannot sort out how to allow the necessary traffic (or even ping) between wifi-pc and printer. I have tried to play with some FW rules to pass some traffic without luck, so I hope someone can help me out with hints or complete solution. -
i think that the easier solution would be a rules like
vlan20:
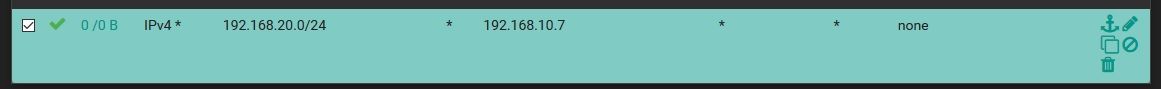
vlan10:
the same but with source ip 192.168.10.7 and destination 192.168.20.0/24 -
Thanks!
Placed one rule on each vlan like you recommended (using defined alias for net and printer) on the top of the list. Still no ping coming through.
Checked the firewall tab in system log and it still showed a lot of icmp blocking between the two units ip addresses, referring to the default deny rule.So I added a rule above yours to let icmp pass (on both interfaces).
Then there is no more blocking of icmp in firewall, but for some other protocols (UDP:53 etc.). And still no ping is passing through.So I changed my icmp rule to pass any protocol to printer. That stops the blocking according to system log, but pinging my printer from the wifi-pc still fails.
Any idea?
-
make a screeshot of your rules so we can understand better what's wrong
-
@pfsensitive said in Using printer on a separate subnet/vlan:
but pinging my printer from the wifi-pc s
You need to post all your rules if you want anyone to help you figure out what is going on. Rules are evaluated top down, first rule to trigger wins, no other rules are evaluated. Its impossible to know what is going on without seeing the full rule set.
Maybe your sending traffic out a gateway, vpn setup maybe with policy routing?
Does your printer even have a gateway setup.. Does it use a different gateway than pfsense. What else is going on in your network, maybe you have a asymmetrical routing problem.
All that is normally required, in your typical network is allow for icmp.. Here I am pinging my printer on another subnet without any issues at all.
$ ping brother.local.lan Pinging brother.local.lan [192.168.2.50] with 32 bytes of data: Reply from 192.168.2.50: bytes=32 time=2ms TTL=254 Reply from 192.168.2.50: bytes=32 time=1ms TTL=254 Reply from 192.168.2.50: bytes=32 time=1ms TTL=254I'm on the 192.168.9/25 network..
-
Thanks again! I understand that it is harder to help without all the rules at hand, and I'll see if I can show you more. But now I suspect this not to be a firewall rule issue, but something else:
I removed any rule for vlan10 <-> vlan20 in both interfaces and replaced it with one rule allowing any traffic (any protocol, any destination) on both of these interfaces. Then I can reach all (LAN and Wifi) units in vlan10 from vlan20 except my printer. Strange...
I have checked that the printers static network settings is complete with ip, netmask, gw and dns,I can also ping units on other vlans as well when I pass that traffic on their respective interfaces, as expected.
So for now I have two questions:
- In a simple setup, do you all agree that kiokoman's suggestion should work? (I do...)
- Are there any specific properties to a printer that could make this fail?
-
@pfsensitive said in Using printer on a separate subnet/vlan:
Are there any specific properties to a printer that could make this fail?
Yeah sure there are
- Doesn't even answer ping.. Can you ping it from devices on the same network?
- Doesn't have gateway set, or gateway is wrong or something other than pfsense, so it can not answer back
- Gateway is set, but mask is wrong, so it thinks that IP is on its own network and doesn't send traffic back to gateway.
3A) example of this would be printer 192.168.10.7 pointing to pfsense 192.168.10.1 for example as its gateway. But you set the mask as say /16 vs /24.. So something pinging it from 192.168.20.x would look to the printer like its local, and would not send its reply back to pfsense at 192.168.10.1
As to just an allow rule for pinging the printer, sure that works just fine. As long as no rules above it that block it before that rule gets evaluated, etc.
You do not need a rule on the other vlan, unless you want that printer or whatever to be able to create unsolicited to where your allowing it.
You do not need return rules.. Return traffic is allowed by the state that is created when traffic is allowed through the source interface..
If I want to allow traffic xyz from vlan 10 to vlan 20. I only need a rule that allows it on vlan 10, vlan 20 could have zero rules and vlan 10 could create the traffic into vlan 20 and get a response.. But vlan 20 would not be able to "create" traffic into vlan 10 unless there were rules on vlan 20 to allow it into vlan 10
-
OK. That explains a lot, johnpoz!
Since the printer did not respond as expected, I configured pfsense's dhcp to handle the printers ip instead of setting it static on the printer it self. Solved everything, it seems…
Thanks all!
Case closed (or I will start a new one if necessary). -
So maybe a typo on the gateway or mask when you setup the printer.. Depending on the printer their interfaces for setting up IP are not all that fun.. So yeah could of been easy to typo a octet or have it default to /16 vs /24, etc..
-
Man, I understand you because I tried to set up my printer for a very long time and as a result I realized that the problem can be not only in the wrong connection, but in the router itself. Tell me the model number and brand and I will try to make a guide for you. If you can’t solve your problem, you will need to find another printer. I would purchase a high-quality printer from Brother (mrdepot.ca) and this printer is very easy to use and connect.