FRR - BGP RPKI patch
-
Hey folks,
I needed to support RPKI on my own little VPN mesh network, so I've made a patch that adds support in the GUI for RPKI, in BGP, on the lates (GA) pfSense/FRR version pair. As it turns out, pfSense ships with versions of FRR that support RPKI, and that package supports:
- RTR protocol support (non-TLS)
- SSH protocol support (RTR over SSH/TLS)
What is RPKI?
RPKI is a wonderful way to either secure your public internet routes against signed ROAs, or distribute your own route filtering/whitelist. FAQ on RPKI: https://www.apnic.net/get-ip/faqs/rpki/How do I use this in pfSense?
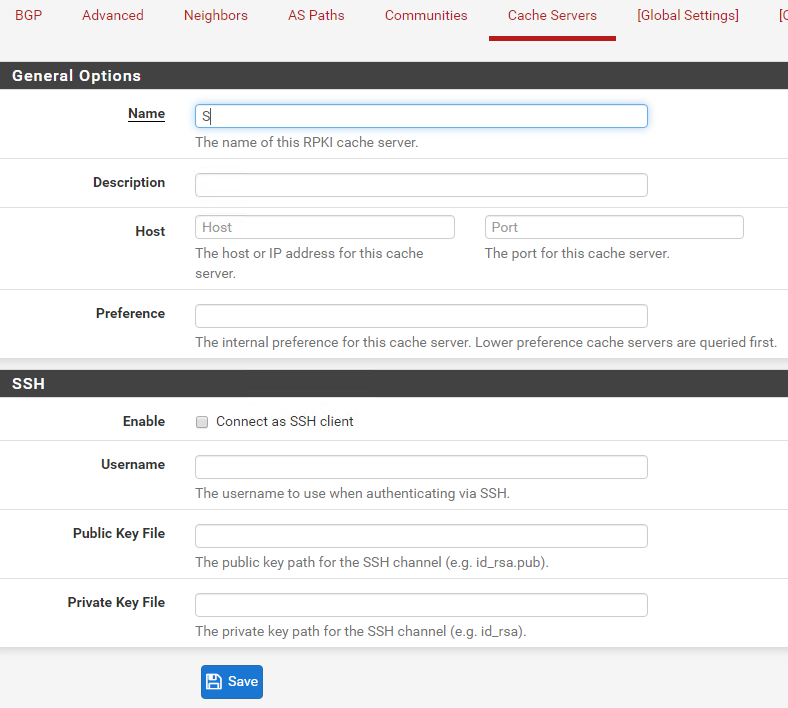
To turn on RPKI, go to BGP -> Advanced and, under the RPKI section, select the values you want. Then, add cache servers for the RPKI ROA cache servers. I recommend switching on RPKI debugging in that advanced section, as you can see log messages.
This patch does not have input validation yet. So, be mindful that you use/format IP addresses, host names, ports, timeout values, etc. correctly. Aside from that, business as usual.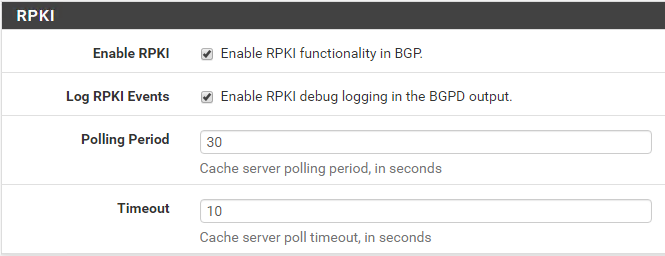
How do I run a RTR server?
You can run your very own RTR server (even in Docker!) with Cloudflare's project GoRTR: https://github.com/cloudflare/gortr. For example, I run mine against a custom ROA file (as it's an internal VPN) with:docker run -d --restart always -p 8282:8282 -v /etc/rpki/roas.json:/rpki.json cloudflare/gortr -checktime=false -verify=false -cache=/rpki.jsonWhich hosts a non-TLS bare RTR server that can be added in the Cache Servers section in the patched BGP configuration section. As an idea, you can even generate the ROAs on-the-fly for more real-time route filtering, if you want.
Patch
I'm open to suggestions, etc., as I'd like to make this into a pull request at some point (and add appropriate input validation) if it makes the most sense to do so.
Patch file: rpki.patch -
If you make a pull request for that we can certainly consider it for inclusion. Input validation would be nice but is not strictly required, since that's a work in progress throughout the FRR package.
-
@jimp Thanks Jim, I'll get started on the process of designing a PR soon.