-
Hello! I decided to switch away from OpenVPN/static routing to IPsec/OSPF (FRR) today. One of the routers now doing OSPF doesn't have a LAN connected to it that I can route. The LAN behind it is a subnet provided/mandated by my provider that conflicts elsewhere in my network.
When I was using OpenVPN it wasn't a problem because I put a route in the OpenVPN server for a netblock to route to the OpenVPN interface on the router then made that network a block of 'other' VIPs and 1:1 NATed them to the LAN IPs.
Now with IPsec and OSPF, I'm having issues. The first is that the VIPs don't appear in the routing table so I can't redistribute them naturally. I tried adding a static route to the local IPsec interface (not IPsec gateway) for them but that caused a loop. I tried adding a route pointing to localhost but that just failed. I tried adding a static route for them to the LAN interface and that can get me exactly one ping for any session.
The next issue I notice is that I can't attach 'other' VIPs to the IPsec tunnel interface. With OpenVPN I always had the VIPs on the LAN so I'm not sure if this is an issue but it definitely seems wrong. I know this is a little niche but that for your time anyways! -
Found my solution. For any future travelers: I had to switch my VIPs from 'Other' to 'IP Alias' and from WAN to Localhost. Thic being an IP Alias that adds the network as connected for OSPF to redistribute and the IP as bindable for 1:1 NAT. Definitely not idea but it works.
-
That is expected since 'other' and 'proxy arp' type VIPs don't actually exist on interfaces or in the routing table, they are GUI stubs/only for ARP responses.
You could also setup your OSPF config to treat your router as an ABR and then setup summary route(s) for the subnets you want to advertise, rather than letting it decide based on interfaces/subnets present in the OS.
-
Actually I might give that a try because I'm noticing only one of my 1:1 is working now.
-
If you search around or look back in the FRR category on the forum, I've gone over how to do that a couple times here and maybe also on the pfSense subreddit. Here is one instance: https://forum.netgate.com/topic/144818/frr6-filter-connected-routes-to-be-distributed-into-ospf/2
-
I'm not having an issue with FRR/OSPF specifically. I can get the route to propagate a couple ways. The issue I'm having is my 1:1 NAT rules aren't working now with IPsec.
-
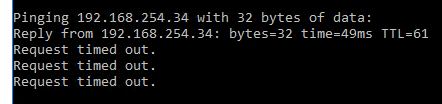
Update: If I put the 1:1 NATs on the IPsec interface and the VIPs as IP Aliases on Localhost I can get UDP and ICMP working. No TCP.
Copyright 2025 Rubicon Communications LLC (Netgate). All rights reserved.