acme when dns provider does not allow dns challenge
-
@johnpoz valid point. We're talking about a .com address here.
-
@JeGr thanks for the pointer!
-
Well .com has been dnssec for a long time ;) And every accredited registrar is required to provide the support to do dnssec.. So yeah you should be able to use any registrar - yet that is not the case for sure.. And while some say they support it - you can not get it to work ;)
You shouldn't have any issues with cloudflare..
-
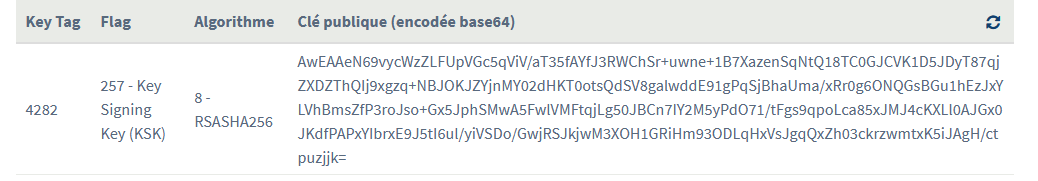
@johnpoz I've requested a DS record at my current registrar and sent them the data Cloudflare has provided me with: It goes like
"example.com. IN DS 62910 7 1 1D6AC75083F3CEC31861993E325E0EEC7E97D1DD"
While my provider says they've done what's necessary, a website check produces the following error: Fatal error: DNSKEY 2371 signs DNSKEY RRset, but no confirming DS RR in the parent zone found. No chain of trust created.
Did I overlook something here or is the ball back in the registar's court?If the latter is the case, I'll initiate a domain transfer and do everything within Cloudflare. - The whole affair is taking way too long..
-
@tn1rpi3 said in acme when dns provider does not allow dns challenge:
Did I overlook something here or is the ball back in the registar's court?
Looks like that's the case.
Use https://dnsviz.net/d/12bfree.com/dnssec/ - it's far more 'visual'..Most registrars these days use GUI's so "you can help yourself" - or better : APIed everything.
The registrar will then your domain settings - most often fully automated.
While your at it, check you IPV6 glue.
-
@Gertjan said in acme when dns provider does not allow dns challenge:
- Looks like that's the case.
I'm sorry, I don't understand.
There's no GUI at my registar's page. All I can do is send them the DS record data, which I did.I'm trying to figure out if the registar made a mistake impementing the DS record, or if somethings missing on my side.
-
@tn1rpi3 To me it looks like the registar made a mistake implementing the DS record:
https://dnssec-analyzer.verisignlabs.com/12bfree.com
says something similar: "None of the 2 DNSKEY records could be validated by any of the 1 DS records" -
@tn1rpi3 said in acme when dns provider does not allow dns challenge:
Did I overlook something here or is the ball back in the registar's court?
My answer :
@Gertjan said in acme when dns provider does not allow dns challenge:
Looks like that's the case.
Valid for both answers, because I don't know what you overlooked (to hand over to the registrar) - it it most probably boils down to : it's up to the registrar to put your DS in place ....
Btw : how you hand this over ? By mail ? Seems rather dangerous to me.
If some one impersonates you nu y mail, your domain will disappear from the net.Btw : DS operation do take time.
-
@Gertjan Thanks. I got it. -
I handed it over while logged in to their website (created a ticket) two days ago. -
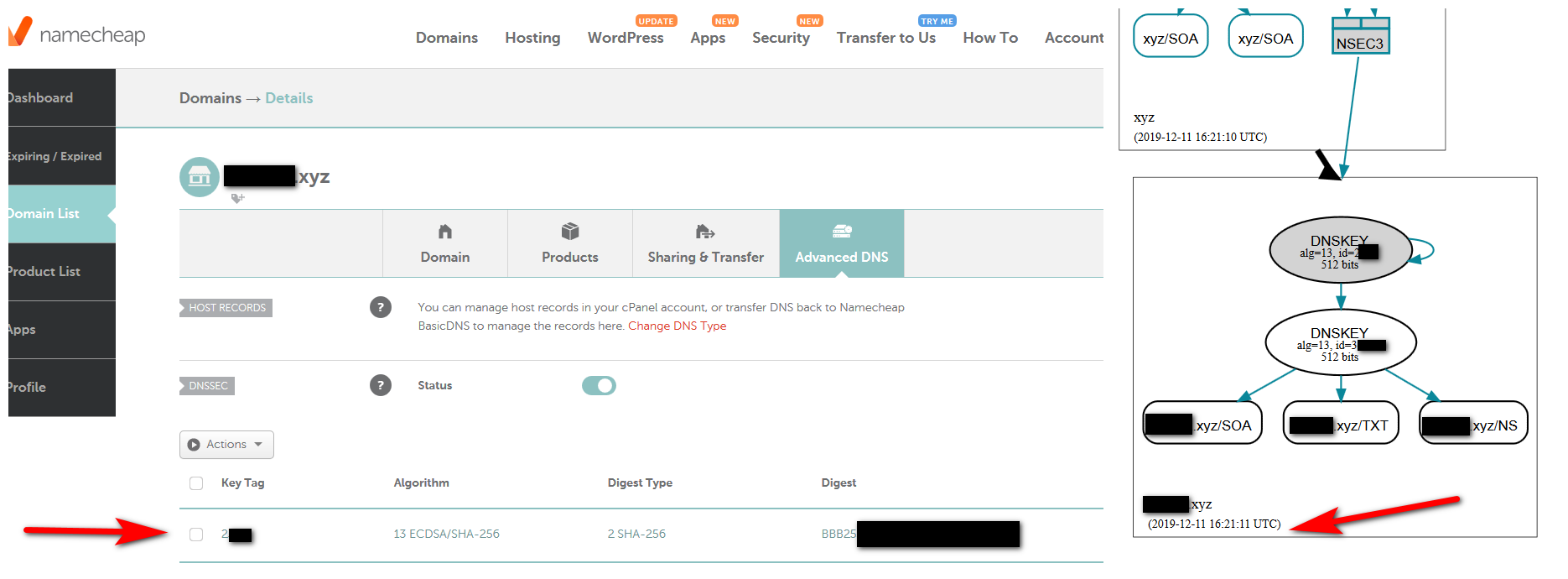
Ok - I just enabled dnssec on one of my domains I have pointed to cloudflare from namecheap... It took less than 2 minutes to setup.. And is working now and showing valid
-
@johnpoz I realize I've been trying this the hard way, relying on my current registrar. - I think I'll finally transfer the domain to Cloudflare. This limbo situation must end..
-
I know it sucks - but not all registrars are created equal that is for sure...
Have no issues with dnssec with namecheap or dynadot.. Namecheap was late to the table to even support it, but currently it seems to work real easy with simple to use gui..
I don't have anything with cloudflare as a registrar - but do have some domains pointing there.. And as you can see works real easy.. Now the domain I use for my plex is dnssec signed ;) hehehe
-
@tn1rpi3 :
Where did this one came from :
root@ns311465:~# whois 12bfree.com | grep 'DNSSEC' DNSSEC: signedDelegation DNSSEC DS Data: 60191 13 2 307DC191192735F5DF76FE364F6F6C1F18B108C43835315A74E450D64E4106A1Never ever delete - on your local domain name server - references to this '60191' DS.
Rotating KSK keys is a real sport. -
@Gertjan My best guess is that this is old data from before I transferred to Cloudflare. When I rechecked today (yes, the registrar was sluggish once again) the grep on whois finall returned the correct DS entry. -- On the other hand the certificate renewal still fails when the process arrives at the subdomain *.12bfree.com returning "invalid domain". Under SERVICES/ACME Certificates I entered *.12bfree.com for 'Domainname' - anything wrong with that, perhaps? BTW: a dig on e.g. lime.12bfree.com is successful and returns an IP from the Cloudflare realm.
-
@johnpoz I was one small step away from transferring to Cloudflare as a registrar when World4You finally came up with a working config today (as usual taking their time to do so). - I fully agree on your impressions on Cloudflare. They've got a clean interface, their online documentation is flawless and their basic subscription is free of charge.
-
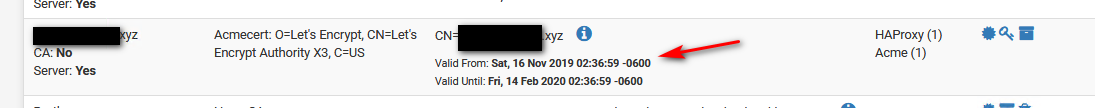
@johnpoz DNS SEC is working alright now. Interestingly, ACME Certificate renewal is not. The job finishes with an error saying 'domain not found'.
On a closer look parent-DS with algorithm 13 produces a valid chain of trust, but for 'TXT-entries' the check-up says 'perhaps wrong' for '_acme-challenge.12bfree.com.12bfree.com' and '_acme-challenge.www.12bfree.com.12bfree.com' (see screenshot)

ACME Certificates with Cloudflare does not allow for TXT entries to be used for ownership validation. It uses account ID, key + token.
I'm out of ideas..
BTW: For check-up I used https://check-your-website.server-daten.de/?q=12bfree.com this time. -
well that sure doesn't look correct... the _acme-challenge fqdn would be _acme-challenge.domain.tld.. you seem to have _acme-challenge.domain.tld.domain.tld and www.domain.tld.www.domain.tld not sure why you think those would work?
-
@johnpoz I fully agree; My API entries for domainname are 12bfree.com and *.12bfree.com
I don't see how the doubling could take place, unless I can't see the wood for all the trees.. -
Why not just manually create the TXT records in cloudflare?
I believe I am using acme for a cert via cloudflare - let me check, I know I played with it some time ago when I was doing reverse proxy through them... But might have killed it when I stop doing that..
edit: Yeah still using one, it renewed all not that long ago on its own, I didn't have to do anything..
This offloads the https for my ombi setup in haproxy.
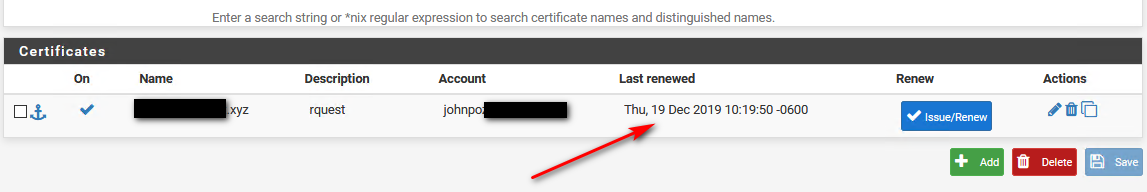
edit2: here is what I have set in the acme client on pfsense
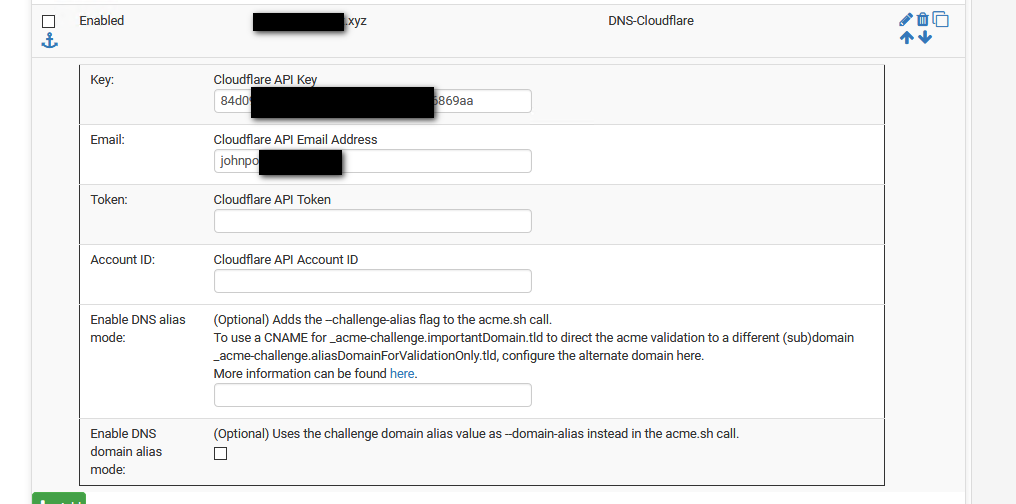
edit3: here it just renewed when I clicked the issue/renew button
-
@johnpoz Curious.
I left Token + Account ID empty, reran the script and wham-bam, success!
Thanks a lot for the screenshot!