Firewall directions
-
Hi,
I have a 2 part question but both within the same context.
Part 1
The pfSense documentation states that "Firewall rules on Interface and Group tabs process traffic in the Inbound direction...". So if we have these rules for the Inbound direction and the "NAT/Outbound" rules for the Outbound direction, why would the default "Allow LAN to any" rule would use 'LAN net' as the Source instead of '*' ?
It seems that this rule actually affects the Outbound direction, allowing (just as it says in the description) LAN users to go out to any destination.Also, I've seen many examples online were people just use '*' as the Source for most of their Block/Allow rules.
Part 2
There are 2 ways, that I know of, to block Interfaces from reaching each other or the main LAN net:
(1) Add a blocking rule for each one of them and at the end allow whatever you want (like Internet Access etc.).
(2) Add a Pass rule to the interfaces' gateway (for Internet access etc.), below that add RFC1918 Alias blocking rule and at the end allow whatever you want.According to my logic, the second approach would be more efficient and robust but less readable/user friendly and also too inclusive. Also, it sounds more logical to just block everything and then allow only what you want.
When you have a lot of Interfaces, choosing the second approach is almost a given, but what would you suggest using when having only 2-4 Interfaces? The more readable/user friendly solution or the more robust and efficient?Thank you,
-
-
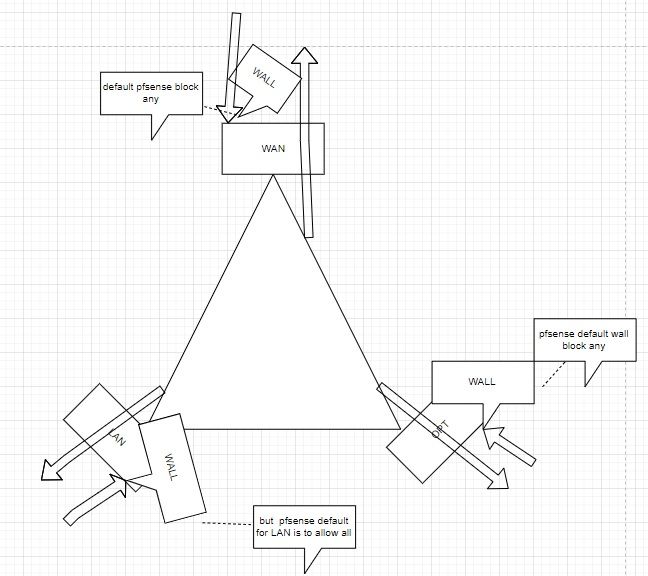
semantics, clients on your LAN generate traffic that enter the LAN interface of pfsense (inbound) and go out to the internet where "NAT/Outbound" rules take place or enter other interface.
why would the default "Allow LAN to any" rule would use 'LAN net' as the Source instead of ''* ? -> you will never see traffic generated by an interface other than LAN, both are correct -
what you say seems wrong to me, first rule that match win any other rules are not even readed
for example :
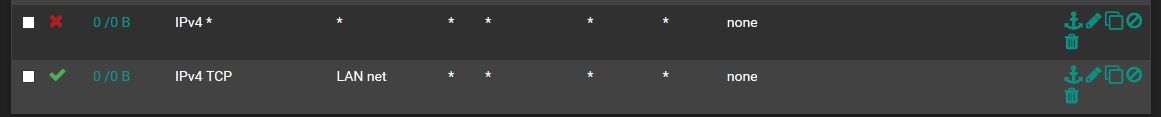
this rules are wrong
the traffic will always match the first block and never read the second rulethis is "correct"
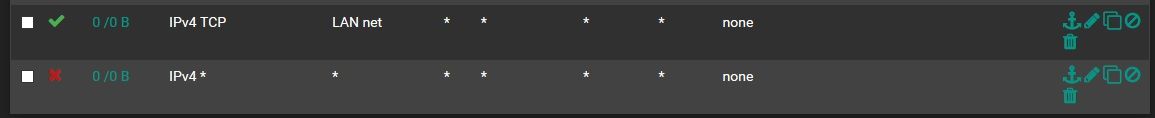
only tcp traffic are permitted any other are blocked (example udp icmp)on my 4 interfaces i allow what i need and block everything else at the end
-
-
@kiokoman Thank you for answering.
-
Ok :). Indeed, the semantics can be confusing. So, just to wrap it up - It should always be regarded as "bidirectional", meaning when the Source is LAN/Other Interface for example, then it would apply the rule to whatever "comes in" from that interface and "wanna go out" to the destination. When the Source is set to something that is outside our network then the semantics would actually be "(Inbound) Coming from the outside world --to--> our private network (Outbound)"? Inbound is basically who ever initiates the request/connection?
-
I understand the order of rules etc. but I've seen more than a few guides online were they set a blocking rule for each interface/VLAN, which seemed to me as weird and inefficient, so I was in favor of the second approach.
Going back to semantics - would blocking IPv4* for 'any' Source also block anything from the outside world or I shouldn't be worried about the "outside world" since firewalls automatically allow incoming connections originated in requests made by the LAN/other interface users?
It seems that the semantics confuse me. Could you explain in which scenarios the outside world/Internet would be regarded as the Inbound?
Thanks a lot, I appreciate your help!
-
-
I could have misunderstood what you mean here but rules are "monodirectional" in relation of the interfaces
let's say for example that we have WAN, LAN and OPT interfaces,
if i want OPT to be able to go to LAN i make a rule in the OPT tab, that permit traffic with source OPT and destination LAN,
afaik there is nothing that you need to do on the lan interface, traffic can now enter LAN from OPT and that source (OPT) can't be blocked on the LAN interface. the same is for WAN, default is to block everything that come from the "internet" but the traffic that has already come out of the LAN and OPT interface can't be blocked anymore.
so if you have a wrong NAT/rule that permit traffic from WAN to LAN
blocking IPv4* for 'any' Source in the LAN tab does not block anything coming from the outside world and you must be sure you don't have wrong rules / NAT on the other interfaces
this without taking in consideration floating/hidden rules and outbound NAT rules -
Sorry for not fully understanding what you're saying but please bear with me :)
- Any rule under interface X tab, would apply only for traffic generated from that interface and/or it's users? So, if I permit interface Y (under its tab of course) to go to interface X, there's nothing interface X can do about it...right?
@kiokoman said in Firewall directions:
so if you have a wrong NAT/rule that permit traffic from WAN to LAN
-
So, unless I have such NAT/rule, traffic coming from the internet/outside would be blocked by default and/or by blocking IPv4*?
-
According to my knowledge, every firewall blocks all incoming connections (from the Internet/outside) unless you've made a connection to that destination (initiated it). Correct?
-
If such permitting NAT/rule exists (I doubt it), where would I find it? Under what tab/section? Can you give an example for such rule that allows WAN to LAN?
Thanks,
-
1 right
2 right, on the wan interface it's a hidden rule
3 yes
4 firewall WAN interface / Firewall - NAT - Port Forward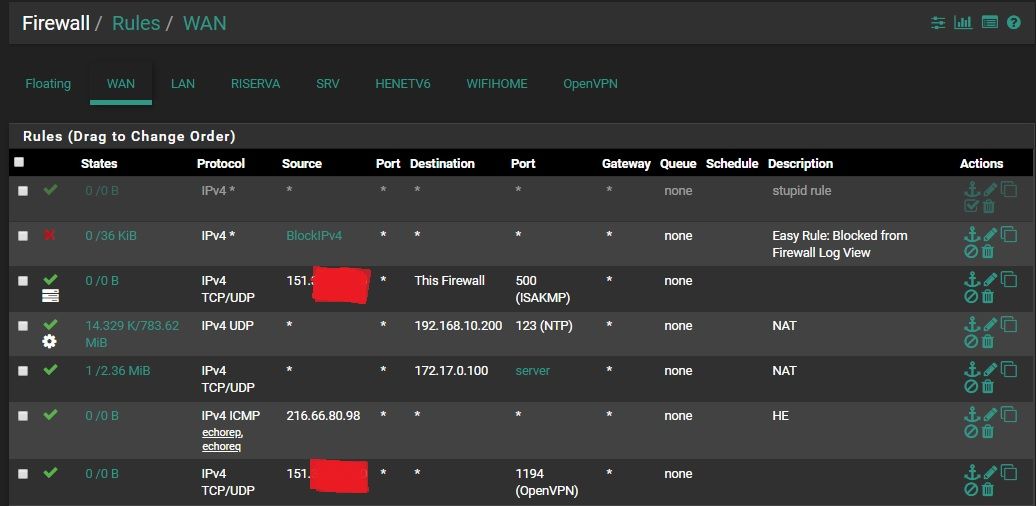
-
@kiokoman Thank you for your patience, now it's fully understood. Very nice and self explanatory drawing haha.
Still...One or maybe few more things if you may :)-
Besides port forwarding which is very known, other reasons for allowing WAN to LAN would be having behind the pfSense firewall things like: Public server, Plex/Media server etc. ?
-
The only difference between LAN and other interfaces is that pfSense automatically adds the "LAN to any" rule, right?
-
In order to achieve isolated Interfaces/VLANS that has only Internet access but nothing else, I could create the rules you've posted above - Allowing IPv4 TCP from LAN net, but blocking all other IPv4*...right?
-
If I'm correct on 3 (above) then what rule should I add to allow all the interfaces to connect to an OpenVPN server on UDP? The same rule just UDP instead of TCP or maybe even add Alias of the VPN servers?
Thank you,
-
-
Besides port forwarding which is very known, other reasons for allowing WAN to LAN would be having behind the pfSense firewall things like: Public server, Plex/Media server etc. ?
Or having an additional interface like a DMZ that hosts servers/services to be exposed to the internet.
@techtester-m said in Firewall directions:
The only difference between LAN and other interfaces is that pfSense automatically adds the "LAN to any" rule, right?
Not exactly. LAN is special in having the default LAN any-any allow rule (to make it simply work "out of the box") AND having the possibility for an anti-lockout rule that also is special to LAN only. To disable that you've got to remove the checkbox under advanced settings as it's an otherwise non-deletable rule that simply allows access from LAN to pfSense web - and if you enable ssh - port(s).
In order to achieve isolated Interfaces/VLANS that has only Internet access but nothing else, I could create the rules you've posted above - Allowing IPv4 TCP from LAN net, but blocking all other IPv4*...right?
Nah. To achieve that, you'd have to to like 3-4 rules. As an example let's create a "guest" network on OPT1, so you'd have to do
-
allow DNS/NTP from opt1_net (or guest_net whatever you called it) to connect to pfSense (to use ntpd or DNS resolver/forwarder)
-> allow udp/53 from opt1_net to opt1_addresss -
create an Alias like "RFC1918" or "private networks" and add all RFC1918 private networks to it: 10.0.0.0/8, 172.16.0.0/12 and 192.168.0.0/16
-
deny all clients on OPT to access any other private network (potential other LANs you create within a private network range)
-> reject any from opt1_net to <RFC1918> -
allow any client anything else (-> public internet space).
-> allow any from opt1_net to any
With blocking private IP space before and only allowing DNS/NTP to the firewall your clients on OPT1 get an IP via DHCP, can use DNS resolver and use NTPd for time services and can surf, ping, use the internet at will. Of course you could limit that further by only allowing e.g. tcp/443 instead of any in step 4 but that would be a bit "limited". Other possibilities are using the captive portal or other features ;)
-
-
@JeGr said in Firewall directions:
Nah. To achieve that, you'd have to to like 3-4 rules. As an example let's create a "guest" network on OPT1, so you'd have to do...
That's exactly what I had before but then I saw the example above and got confused...I guess each and his own. There's more than one way to achieve the same.
What about an OpenVPN client with address like: 10.x.x.x? This would just be the gateway and won't be affected these rules, right?
Thank you very much for the your help!
-
if you configure openvpn on the firewall you will find yourself with a new OpenVPN tab
where you will enter the rules following the same principle -
@kiokoman said in Firewall directions:
if you configure openvpn on the firewall you will find yourself with a new OpenVPN tab
where you will enter the rules following the same principleI've been using multiple OpenVPN servers for months now and never added any rule to their tabs, but I was connected through the LAN which has the default allow LAN to any rule. With the other Interfaces/VLANs, wouldn't I need to add rules under their tab only? Why to even touch the OpenVPN tab?
-
did you configure the openvpn on pfsense or under some pc/server you have on your lan ?
-
I configured an OpenVPN client on pfSense. In this case NordVPN.
I think I'll just create the rules I want and post a screenshot here. Then we'll proceed.
Thanks man,
-
then a client is not a server
as we said before you are able to enter that interface because the default rule for LAN interface is to allow all
the OpenVPN tab for you is like another WAN
openvpn is another monster that have different implementation -
Yeah...My bad. When I wrote VPN "Servers" I meant my OpenVPN clients, which in turn connect to an actual VPN server haha.
@kiokoman said in Firewall directions:
you are able to enter that interface because the default rule for LAN interface is to allow all
And what about allowing all the VLANs to use the OpenVPN client as well? Their RFC1918/IPv4* blocking rule won't affect it? The local virtual addressed of these VPNs are 10.x.x.x which fall under RFC1918......I thought I understand pfSense and firewall and everything is actually working, but the deeper I dig I get a headache LOL...
-
of course, if you want another interface to be able to use the vpn interface you need to create a rule that permit that.
RFC1918/IPv4* blocking rule inside an interface like OPT1/OPT2 etc will prevent it but you just need a previus rule like
"permit OPT1 net destinatio OpenVPN" before "block OPT1 net destination RFC1918". first rule win ! -
@kiokoman That's what I thought. Thanks a bunch!
-
@JeGr said in Firewall directions:
allow DNS/NTP from opt1_net
It's either or? Or should I allow both of them UDP/53, UDP/123?
-
i think it was just an example,
port 53 is for DNS (domain name system) pretty much mandatory if you want to resolv dns and surf the web
port 123 is for NTP (Network time protocol) useful but not mandatory, it's needed to sync the clock
that said the minimum port to be able to surf the web are udp/tcp 53 for dns tcp 80 for http and tcp 443 for https -
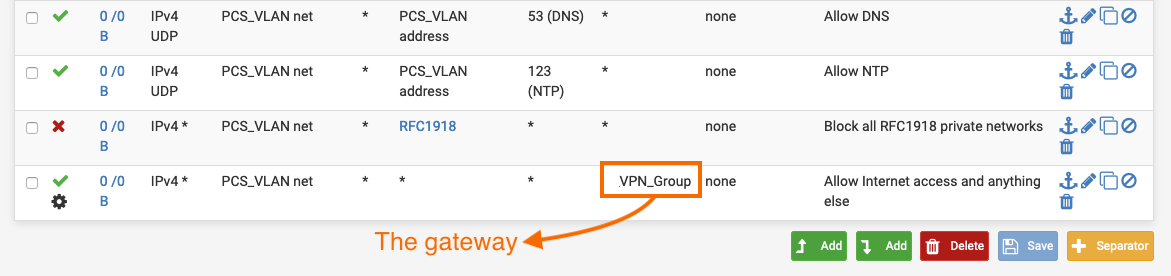
What about the VPN Group shown in the screenshot? I think that adding "Allow PCS_VLAN to OpenVPN(1194)" won't be enough, since the VPN clients' gateways are in the range of RFC1918 - 10.x.x.x.
What rule(s) exactly should I add in order for this VLAN to be: isolated from other interfaces, have internet access and connect to the internet via the VPN_Group (NO_WAN_EGRESS)?