An isolated interface with an access to the internet via an OpenVPN
-
I've asked about it in a different topic as a BTW question but it got messy and out of context and I feel like it deserves a new topic and to be asked in more simplified explanatory way.
Goal:
Creating an isolated Interface/VLAN.- It should be blocked from reaching any other interface on the network
and/or any other private addresses (RFC1918). - It should have access only to the Internet.
- It should access the Internet only via an OpenVPN client/group gateway.
- The OpenVPN client(s) obtain their own local virtual addresses of 10.x.x.x and these addresses may be changed/reassigned (by the VPN provider) due to a refresh/shut down/connection failure etc.
Current status:
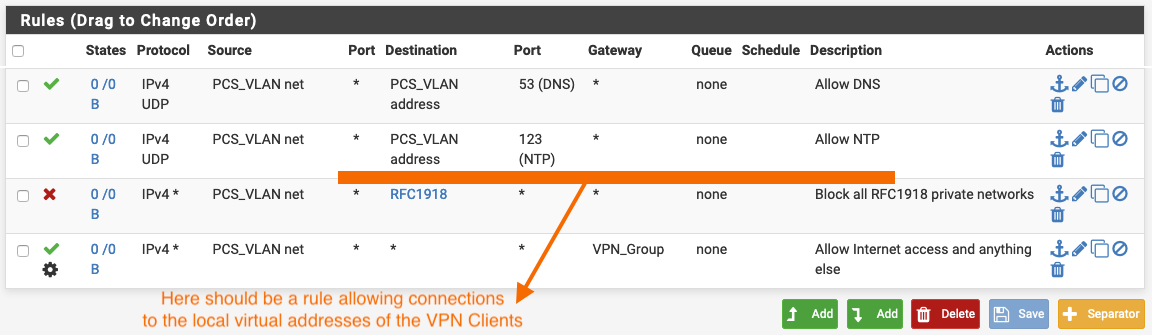
The orange colored statement in the screenshot maybe wrong but I doubt it...
Beginners question:
AFAIK, when connected to a VPN (without a leak) all traffic is being encrypted and sent via the VPN tunnel, including all DNS requests, which is also what my VPN provider says. So, in that case the use of the "Allow DNS" rule is local?
Perhaps I'm misunderstanding how DNS requests work exactly, idk... - It should be blocked from reaching any other interface on the network
-
If you want all DNS requests to go out the VPN_Group you have to set your clients to NOT use PCS_VLAN address as their DNS server. If you do that and set say 8.8.8.8 and 8.8.4.4 as the DNS servers the clients use, those queries will simply be more internet traffic and be policy routed to VPN_Group like everything else.
Generally people run an OpenVPN client on the firewall and not on the client hosts themselves. It's hard to tell exactly what you're doing based on your description.
The OpenVPN client(s) obtain their own local virtual addresses of 10.x.x.x and these addresses may be changed/reassigned (by the VPN provider) due to a refresh/shut down/connection failure etc.
That would be assigned to the tunnel on the firewall, not the PCS_VLAN hosts.
I would change that block rule to a reject rule so clients get feedback instead of just hanging if they attempt to connect to an RFC1918 address.
I would make a rule right above or below that that rejects traffic to destination This firewall (self).
-
I think we have a little misunderstanding...
@Derelict said in An isolated interface with an access to the internet via an OpenVPN:Generally people run an OpenVPN client on the firewall
^ That's exactly what I'm doing, only with a group of OpenVPN clients.
But let's forget for a moment about DNS. I wanna go step by step to keep it simple.
I have a working setup of a LAN interface with the default "Allow to any" rule with a VPN group selected as its gateway.
Now I want to add a VLAN that would be isolated from any other interface and have access only to the internet.@Derelict since we are on a different continent and go online on different hours, I'd appreciate it a lot if you could also answer my other question - https://forum.netgate.com/topic/148439/send-dns-queries-through-a-vpn-tunnel
I'd probably be sleeping by then.Thank you very much for your help,
-
I addresses that here.
-
@Derelict said in An isolated interface with an access to the internet via an OpenVPN:
I would change that block rule to a reject rule so clients get feedback instead of just hanging if they attempt to connect to an RFC1918 address.
I would make a rule right above or below that that rejects traffic to destination This firewall (self).That part? Ok...but I want to fully understand why we do what we do.
-
If the gateway is a VPN and under the VPN settings I use its IP and not url/name, why to allow DNS/NTP to that VLAN? Because otherwise all the DNS requests on that VLAN will be blocked by the RFC1918 before even getting to the VPN tunnel? By the logic of "first rule wins" seems to me that allowing DNS above the other rules will send it not through the VPN tunnel...or maybe I've just misunderstood it all haha, idk already...
-
Is rejecting "This firewall (self)" meant for restricting the users of this VLAN from accessing the pfSense box?
-
My OpenVPN client is running on the firewall. So...How do I force ALL (and also only for certain interfaces/users) DNS requests to go through the VPN, without setting the VPN as the only Outgoing Network Interfaces, like NordVPN suggets, which will of course prevent the VPN from reconnecting after a failure/shut down etc. and thus will need a human intervention...
-
I would also like to Redirect all DNS Requests to pfSense like mentioned in the DOCs...It's a good practice, right?
Thank you,
-
-
This post is deleted!