OpenVPN Server Gateway Redirect
-
I want to redirect my OpenVPN client thru my WAN IP address, That's my config.
persist-tun
persist-key
cipher AES-256-CBC
ncp-ciphers AES-128-GCM
auth SHA256
tls-client
client
remote vpn.******.net 1191 udp
auth-user-pass
remote-cert-tls server
redirect-gateway def1 -
Fine, should work. Is that all you want to tell us?
-
It's not working
 , public ip doesn't change, when connect to open VPN server with these settings.
, public ip doesn't change, when connect to open VPN server with these settings. -
So you're managing the OpenVPN server yourself?
The connection seems to be established?
Can you access remote devices?
Have you access to the internet on the client while the connection is up? -
So you're managing the OpenVPN server yourself? Yes, on Pfsense
The connection seems to be established? Yes, it does and works, but Public IP doesn't change on client side
Can you access remote devices? some yes some no
Have you access to the internet on the client while the connection is up? Yes -
@manjotsc said in OpenVPN Server Gateway Redirect:
Can you access remote devices? some yes some no
These one you can't maybe block access themselves by the OS firewalls.
What's your server config? Possibly it overrides the client settings.
Some clues in the client log? Probably it doesn't set the default route correctly.What is the client? A phone, Windows, Linux?
-
@viragomann The config https://drive.google.com/file/d/1DYdh8ikZ2x9JFrvlfViJlUBMwmvxxKJD/preview
I tried on Android Device using openvpn app.
-
So remove the "IPv4 Local Networks" and check "redirect gateway" in the server settings.
Consider that you also have to add a outbound NAT rule for the OpenVPN tunnel network for internet access from VPN clients.
-
@viragomann What that rule would be?
-
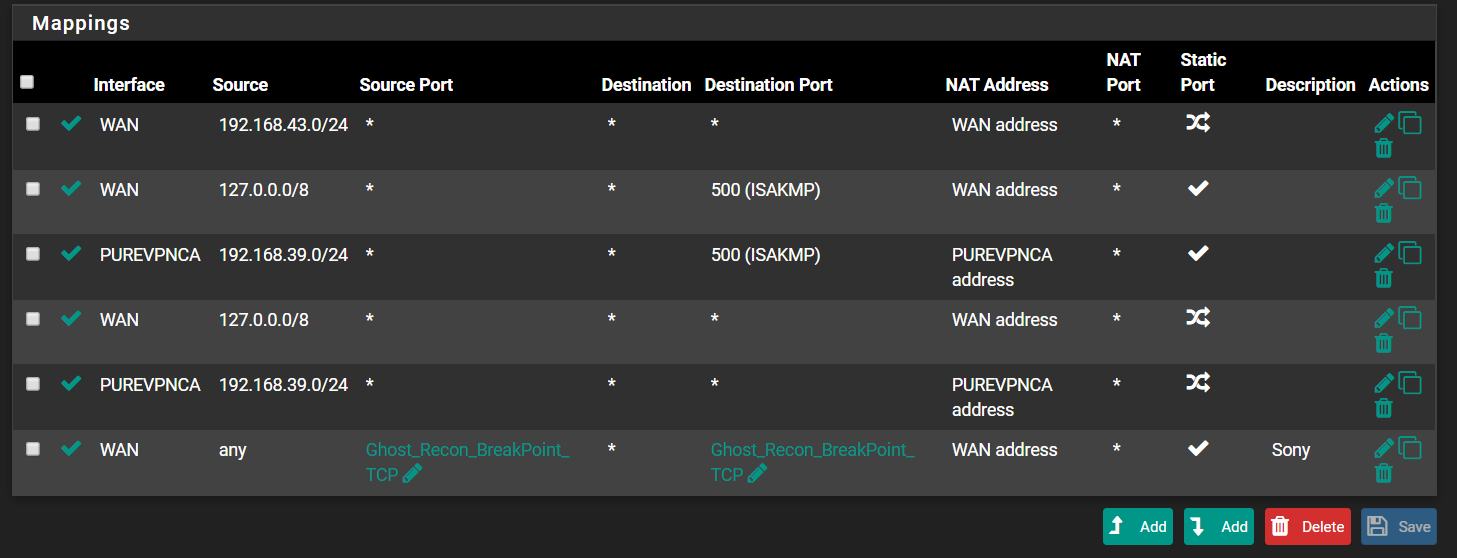
When packets from private sources are sent out to the internet, the router has to translate the source addresses into its WAN address.
pfSense does this automatically for internal subnets, but not for OpenVPN clients.To configure this, go to Firewall > NAT > Outbound
Assuming it is still working in automatic mode, switch to hybrid mode and save it at first.
Then add a new rule:
interface: WAN
source: <OpenVPN tunnel network>
destination: any
translation: interface address -
@viragomann Now I when connected can't visit any website
-
Try to reboot pfSense.
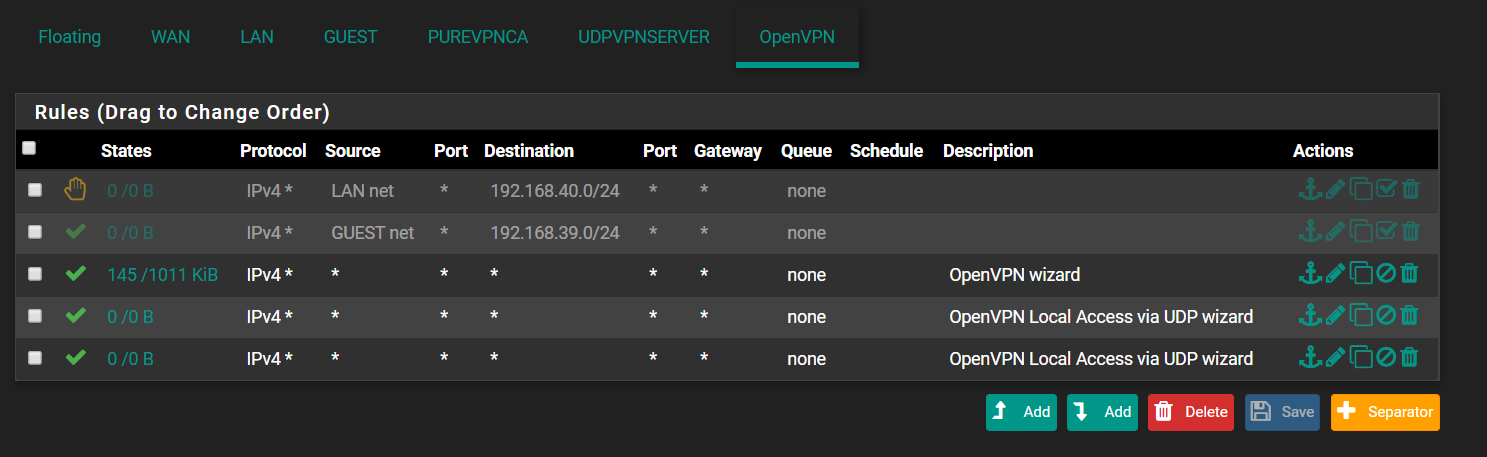
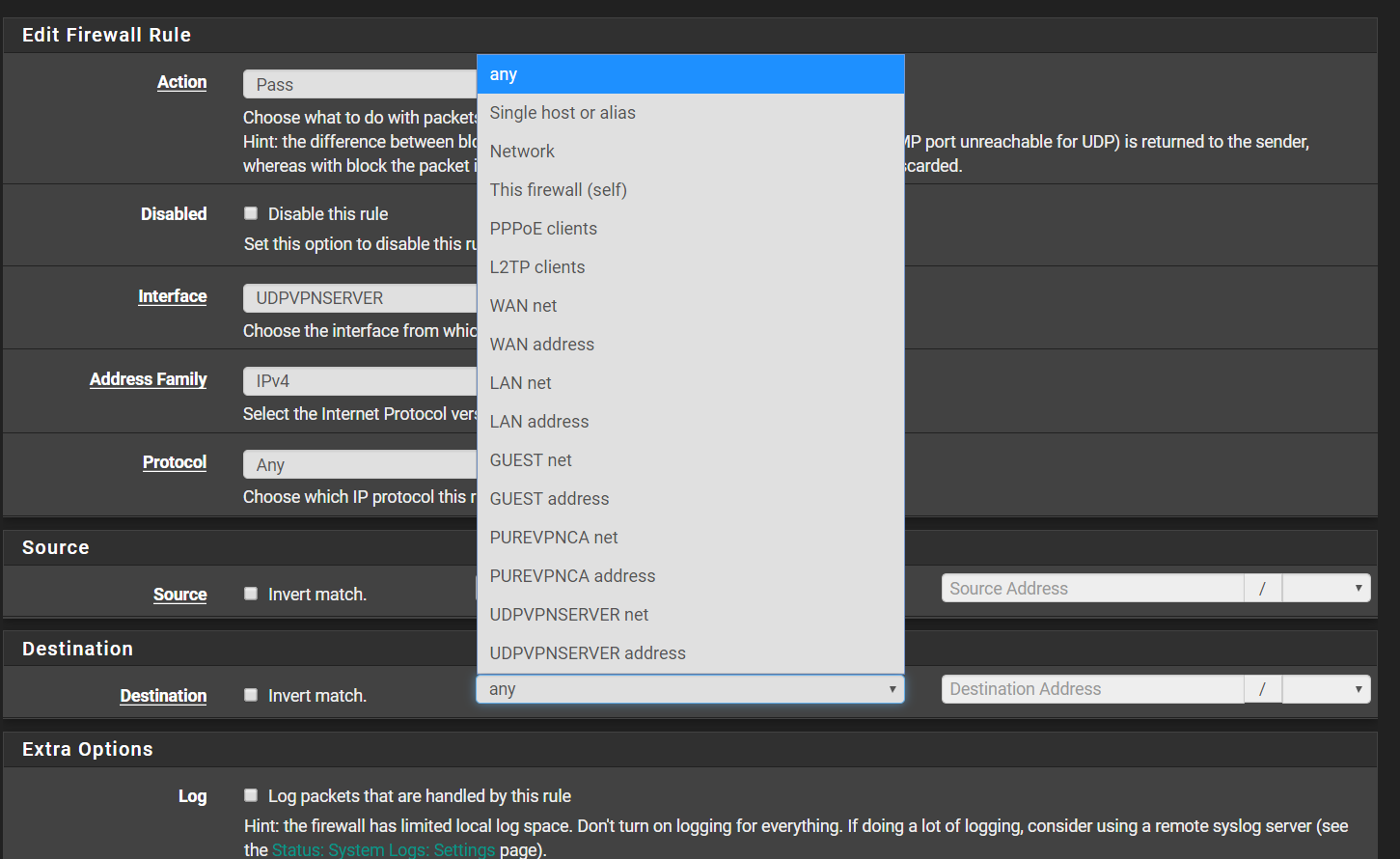
If that doesn't resolve, check the firewall rule on the OpenVPN tab.
-
-
Can't see, what's the rule for the OpenVPN tunnel, since I don't know the network.
You must not allow access from any to any, since you're obviously running VPN services. This way you open your network to the VPN service networks.
You have to restrict the access to your acess server clients. -
@viragomann
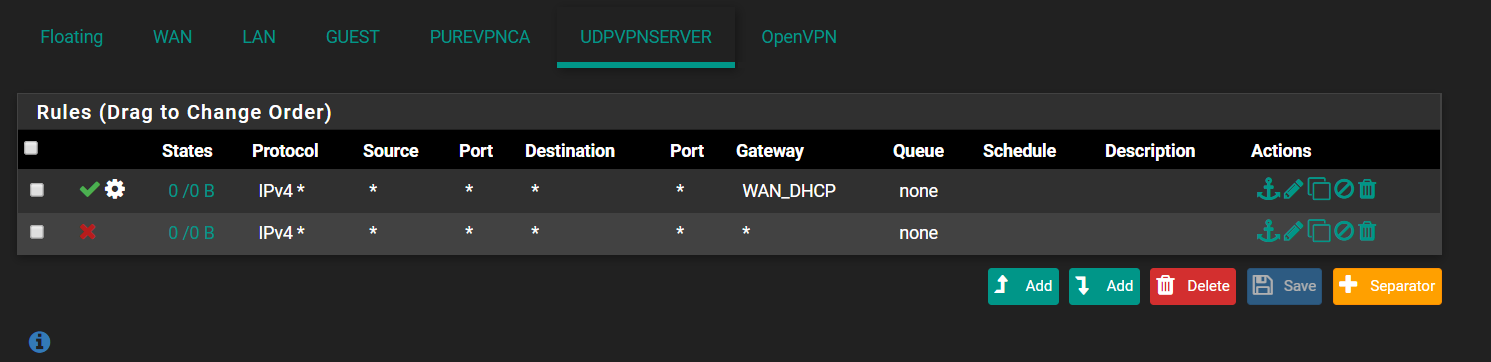 UDPVPNSERVER is the interface I created for The VPN Server,
UDPVPNSERVER is the interface I created for The VPN Server, -
But PUREVPNCA may be a VPN service you're connecting to.
-
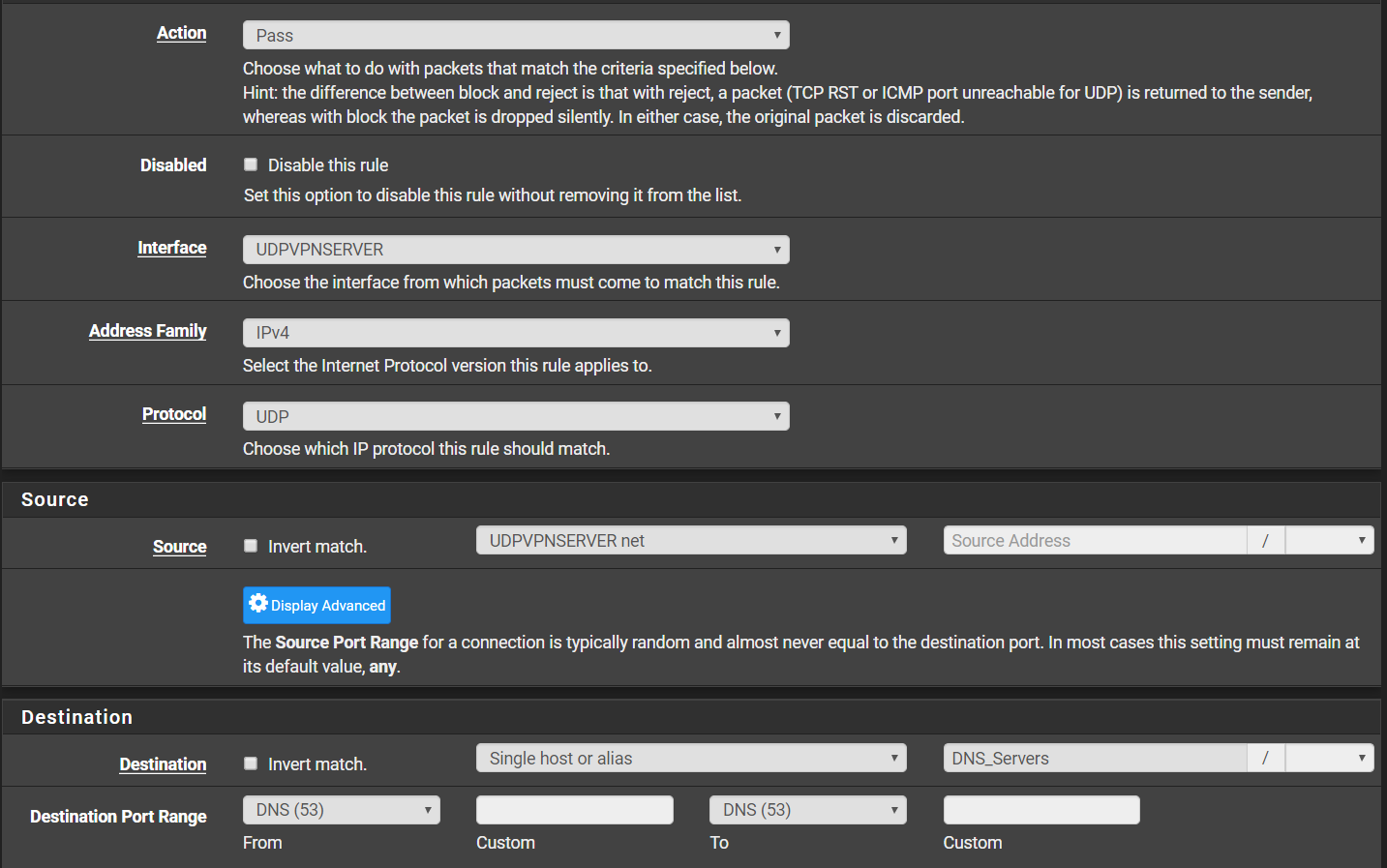
If you disable the rule on the OpenVPN interface you have to add a rule to the UDPVPNSERVER to allow access to your DNS server. The existing rule only allow access to the WAN gateway.
-
@viragomann What Should go in Source and Destination, for dns
-
The source should be the access server tunnel network.
The destination is the DNS servers you provide to the clients. Taking a look at your server settings, these are 192.168.40.4 and 192.168.40.1. -
@viragomann Still not working , DNS_Server is alias for DNS ip address,