pfSense as a DNS server
-
Hi,
I was wondering about using pfSense to act as sort of a local DNS server. If I enable the DNS Resolver to act as the DNS server of the firewall, how would it act?
According to what I've read it should act like this: pfSense/DNS Resolver will cache DNS results and for every DNS request, it would first search for an answer locally in the pfSense box and if nothing is found then it tries the DNS servers defined under General Setup. Is that correct?
Also, when using 127.0.0.1 as the default DNS server, will it use any DNS servers (external IPs) predefined internally by NetGate or only what I've defined under General Setup. I remember seeing weird results when using DNS-Leak test while 127.0.0.1 is in the DNS servers list...any idea?
-
@techtester-m said in pfSense as a DNS server:
I was wondering about using pfSense to act as sort of a local DNS server. If I enable the DNS Resolver to act as the DNS server of the firewall, how would it act?
Open a command line on your PC, and type
ipconfig -alland there is your answer.
pfSense, the task called 'unbound') is your DNS "up stream" DNS server.
So yes, bt default, pfSense acts like a dns cache and resolver for all your LAN's.
@techtester-m said in pfSense as a DNS server:
... then it tries the DNS servers defined under General Setup. Is that correct?
The default behaviour of pfSense (unbound ) it will question the 13 roots servers and drlils down from there.
@techtester-m said in pfSense as a DNS server:
Also, when using 127.0.0.1 as the default DNS server,
Actually, this 127.0.0.1 is meant for all the processes that run on pfSense that need to resolve an URL.
They can use 127.0.0.1 to talk to the local DNS cache/resolver (again = unbound).
unbound will then, if needed, question the roots on the Internet, etc - and cache the result.@techtester-m said in pfSense as a DNS server:
results when using DNS-Leak test
Leak ?
Well, yes, unbound will talk to DNS to and name servers all over the net. Normal. -
@Gertjan said in pfSense as a DNS server:
The default behaviour of pfSense (unbound ) it will question the 13 roots servers and drlils down from there
That's what I don't want. I want pfSense to go to whatever is defined under General Setup and not use its own routes/DNS server list etc.
-
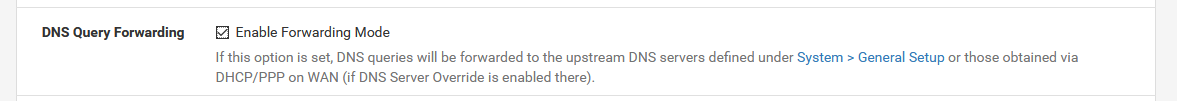
Go to the DNS resolver config page. Go to "DNS Query Forwarding"
Click the "Enable Forwarding Mode" box.
I believe this will do it.
-
@chpalmer Already using forwarding mode. My question is if with these settings pfSense would first try to resolve locally and then use what's defined under General Setup. I don't want pfSense to use its own logic/DNS server list.
-
@techtester-m said in pfSense as a DNS server:
My question is if with these settings pfSense would first try to resolve locally and then use what's defined under General Setup.
Have you readed this: https://docs.netgate.com/pfsense/en/latest/dns/unbound-dns-resolver.html
https://nlnetlabs.nl/projects/unbound/about/
Unbound is a validating, recursive, caching DNS resolver -
@ptt Yes I have but decided to also ask it here with a broader context of other settings. Some answers only confused me more. But ok, I understand. If Forwarding Mode is enabled then the user controls what DNS servers will be used.
-
@techtester-m said in pfSense as a DNS server:
pfSense would first try to resolve locally and then use what's defined under General Setup.
That's how all DNS servers usually work.
I don't want pfSense to use its own logic/DNS server list.
???
there is no "own logic" or "own DNS server list" in pfSense. It does exactly what your ISP, 1.1.1.1, 4.4.4.4, 8.8.8.8, 9.9.9.9, google-dns, OpenDNS or what have you do as well. Just without telling a third party in between. It's the "pure way" if you will. -
@Gertjan said in pfSense as a DNS server:
The default behaviour of pfSense (unbound ) it will question the 13 roots servers and drlils down from there
@jahonix Read what @Gertjan said above. I believe it also mentioned somewhere in the docs. If you don't enable Forwarding Mode the pfSense indeed will use it's own list of DNS servers to resolve. I don't want that.
@jahonix said in pfSense as a DNS server:
It does exactly what your ISP, 1.1.1.1, 4.4.4.4, 8.8.8.8, 9.9.9.9, google-dns, OpenDNS or what have you do as well. Just without telling a third party in between. It's the "pure way" if you will.
Does what exactly? Try to resolve locally? Yeah...I know. But pfSense still need to use some external DNS server and unless NetGate has one then....I'm using Cloudflare's.
Also, if you mean root DNS servers when you say "the pure way" then I'd have to ask if these root servers support DoT, DNSSEC etc. -
@techtester-m said in pfSense as a DNS server:
My question is if with these settings pfSense would first try to resolve locally
That normal. And needed : only the local (== pfSense) will know what devices you have on our LAN's.
No one else on planet Earth can resolve that/these for you : how would the know ?@techtester-m said in pfSense as a DNS server:
what's defined under General Setup
These are the ones where the resolver (unbound) forwards to - when you activate Forward mode :
@techtester-m said in pfSense as a DNS server:
I don't want pfSense to use its own logic/DNS server list.
This "own logic" is the standard behavior, as the Internet was designed since the beginning. This always works.
This "DNS server list" is the main DNS core list. Not some "Top Wall Street" company list.
( remember : you give them all your domain searches ....)
Btw : its's ok if you're ok with that.@techtester-m said in pfSense as a DNS server:
If Forwarding Mode is enabled then the user controls what DNS servers will be used.
.. and when Resolver mode is active then you use the independent root list :
The Internet itself :. 172800 IN NS a.gtld-servers.net. . 172800 IN NS b.gtld-servers.net. . 172800 IN NS c.gtld-servers.net. . 172800 IN NS d.gtld-servers.net. . 172800 IN NS e.gtld-servers.net. . 172800 IN NS f.gtld-servers.net. . 172800 IN NS g.gtld-servers.net. . 172800 IN NS h.gtld-servers.net. . 172800 IN NS i.gtld-servers.net. . 172800 IN NS j.gtld-servers.net. . 172800 IN NS k.gtld-servers.net. . 172800 IN NS l.gtld-servers.net. . 172800 IN NS m.gtld-servers.net.These are NOT controlled by some company or government. These 13 are the Internet.
-
@techtester-m ROFL
May I suggest you read a bit about how DNS works? Will help alot with understanding what you want and what you don't want.When understanding how DNS works (as Gertjan explained in basics) you will probably want to use DNS resolver not in forwarding mode.
-
@Gertjan said in pfSense as a DNS server:
These are NOT controlled by some company or government. These 13 are the Internet
I know, but why would people use Cloudflare's or Google's? There are advantages I imagine...
If I can disable Forwarding Mode and have the pfSense use DoT and DNSSEC with these 13 root DNS servers that'd be great, the question is things like: speed., support for protocols mentioned above etc.
-
@techtester-m said in pfSense as a DNS server:
but why would people use Cloudflare's or Google's?
They are ignorant
They have no clue
They read the wrong PC magazines
They are blinded by marketing "our DNS server protects you from..."
... -
This post is deleted! -
@techtester-m

This are NOT DNS servers (proxies) you put in your DNS server list. They ARE publicly available (otherwise name resolution on the internet wouldn't work at all).
Please read about how DNS on the internet works!!! -
@jahonix Ok...just found that list. Of course they are publicly accessible hahaha I didn't mean it like that...never mind.
Btw from their names and location, seems like the US controls the Internet LOL.
Anyway...I think Cloudflare's and others just maintain their servers better (more money and marketing etc.) and offer other services (to businesses) as well and that's another reason why people use them.
@jahonix said in pfSense as a DNS server:
This are NOT DNS servers (proxies) you put in your DNS server list
Ok...these are used when there are NO DNS server list defined by the user. I got it.
Now for the last part I wanna clarify. Do these 13 support DoT and DNSSEC?
Edit: Just pinged them and Cloudflare's are 3-5x faster than most of them. Few of them match Cloudflare's response speed. Can I assume that pfSense will use the fastest ones, those with the lowest latency? Maybe it will ask all of them and give me the first result? etc. Any efficiency behind the code? I know that their addresses are sent with every DNS request datagram or something but still....please clarify it for me.
Also, by removing any DNS server from General Setup I'm fixed? That's it? pfSense will now use these core 13 servers?
-
@techtester-m said in pfSense as a DNS server:
pfSense will use the fastest ones, those with the lowest latency? Maybe it will ask all of them and give me the first result?
@jahonix said in pfSense as a DNS server:
Please read about how DNS on the internet works!!!
-
@jahonix lol....you're killing me. Just clarify what I've asked with few plain and simple sentences. Please? :)
-
Nope.
That would mean I have to explain how DNS works. I don't wanna do that, there's enough written about it elsewhere.
First hit on a search engine: https://www.cloudflare.com/learning/dns/what-is-dns/
https://en.wikipedia.org/wiki/Domain_Name_System -
@jahonix I know how DNS itself works and I understand that when DNS Resolver is enabled, pfSense will act similar to other public DNS servers like Cloudflare, Google etc. The only question is what would be the caching behavior in pfSense compared to Cloudflare etc. so it would need to ask the root/tld servers as little as possible.
Thanks for the input anyway. Now I'll just test it and in the worst case scenario go back to using Cloudflare :)
Edit: Another possible down side is that the IP of your private resolver (which is the pfSense box) will be record as the one that asked all these servers (root, tld and name) instead of just asking Cloudflares. Now I don't know how exactly it works with these root servers and who has access to them, but it's not impossible that governments or other organizations would be able to tap them or come to them with a warrant etc. Especially when they are on American soil lol. Now...that might be a very paranoid scenario but still...not impossible. On the other hand Cloudflare would probably sell their data to the highest bidder hahaha.
That being said, even if all these root servers are guarded as the gates of heaven, being the Internet itself, a private resolver would still stand out since, I assume, the majority of resolver/IP who ask these root servers will belong to ISPs and public DNS servers like Cloudflare and Google etc.