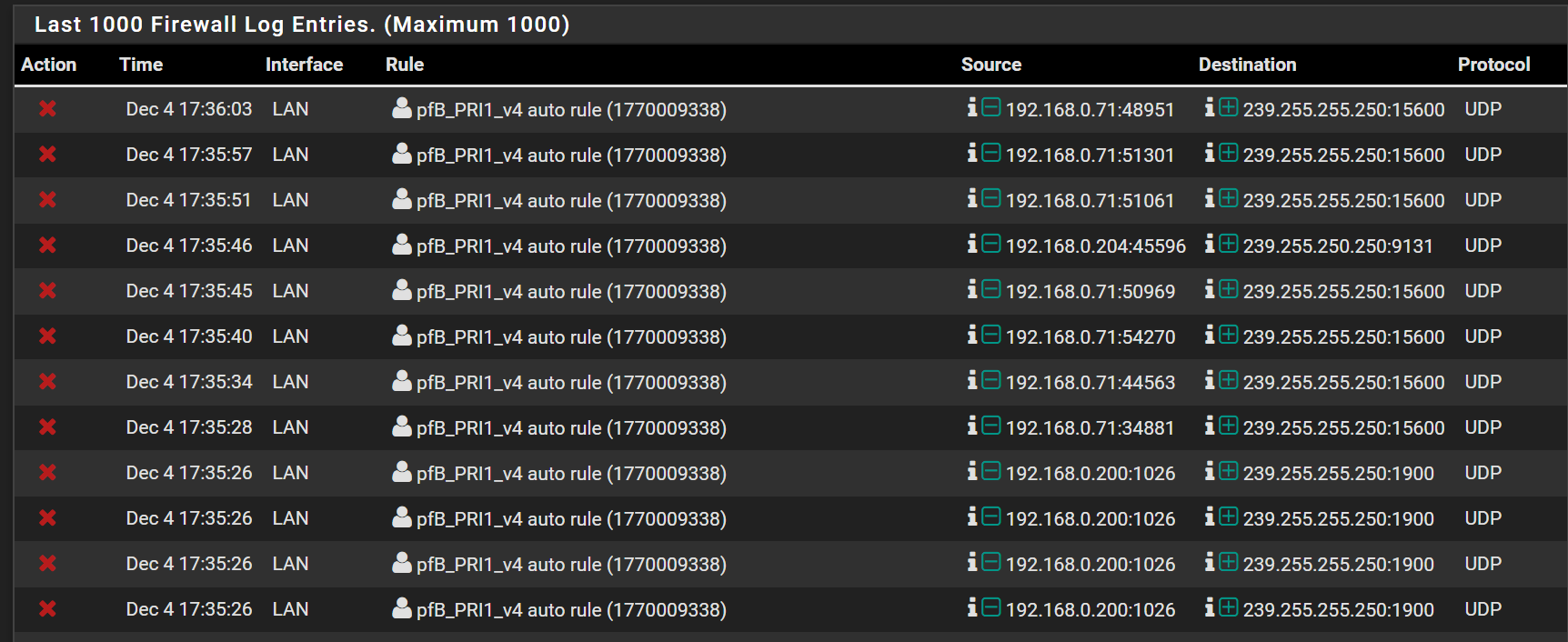
Multicast address log spam
-
I'm getting a ton of FW log spam for clients contacting multicast addresses on UDP. It's being blocked by pfB_PRI1_v4. Should I just disable logging for that rule or is there a better way to cut down the noise?
-
Just put a rule above that doesn't log that dest range. You could put it in floating if need be - not sure why that range would be in that list anyway?
-
@johnpoz Thanks for the reply. I put a rule above the pfB rules to allow LAN UDP to 224.0.0.0/4 (no log) which worked until pfB updated. At that time, the rule was pushed below the pfB LAN rules. Tried to put in floating, but no effect. I'll try to find which list is causing it.
EDIT - OK, looks like a list I added from http://sanyalnet-cloud-vps.freeddns.org/mirai-ips.txt contains 224.0.0.0/3.
Does that network also contain 224.0.0.0/4?
Sorry, subnetting has never been my forte... :( -
EDIT - OK, looks like a list I added from http://sanyalnet-cloud-vps.freeddns.org/mirai-ips.txt contains 224.0.0.0/3.
Does that network also contain 224.0.0.0/4?
Sorry, subnetting has never been my forte... :(224.0.0.0/3 = 224.0.0.0 - 255.255.255.255
224.0.0.0/4 = 224.0.0.0 - 239.255.255.255
Why the heck does the list have multicast addresses in ?
-
@NogBadTheBad Thanks, that explains it. Go figure. Not even sure whyI picked it. Their other blocklist includes 224.0.0.0/4, too.
http://sanyalnet-cloud-vps.freeddns.org -
Why would a block list contain a multicast address? Is a good question - list maintainer is an idiot?? Would be my guess ;)
I personally not a fan of any sort of auto rules that get generated by some package to be honest, I just use pfblocker to create the aliases, and then use them in my own rules. This way you do not have to worry about rules being put into different orders.
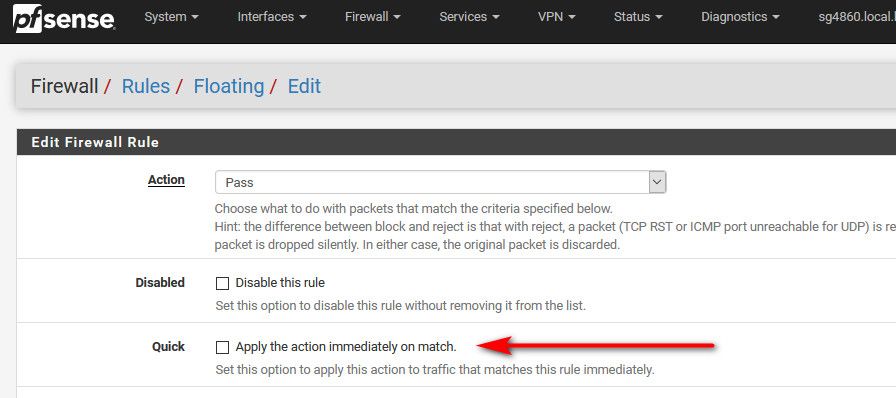
But floating rules are evaluated before interface rules, as long as you mark them "quick" so my guess is when you created the floating you didn't mark "quick" on it..
-
@johnpoz said in Multicast address log spam:
But floating rules are evaluated before interface rules, as long as you mark them "quick" so my guess is when you created the floating you didn't mark "quick" on it..
Yes, you're right. Thanks for the tip.