How to find spambot? Got network abuse report from my ISP
-
Yes sorted by port to show my mail fetch from my workstation on top.
But you can see on the left the date and time. 17:30 to 17:45
-
Run a packet capture on your WAN, filter by 88.152.35.103. Do you see anything?
Is the MAC correct? Is it incoming somehow?
Steve
-
Sorry Steve. What MAC?
And how do i make the capture? In pfSense?I never had to deal with this kind of stuff and never did it before.
That whole netflow and logging thing and PRTG is new to me.Edit
Thanks to YouTube i found it:18:11:54.688369 IP 88.152.35.103.53026 > 104.47.14.33.25: tcp 34 18:11:54.710712 IP 88.152.35.103.37882 > 104.47.10.33.25: tcp 0 18:11:54.712622 IP 88.152.35.103.53026 > 104.47.14.33.25: tcp 0 18:11:54.747653 IP 88.152.35.103.22 > 5.188.87.57.62114: tcp 32 18:11:54.748718 IP 88.152.35.103.53026 > 104.47.14.33.25: tcp 0 18:11:54.754257 IP 88.152.35.103.22 > 185.182.193.169.34202: tcp 476 18:11:54.754967 IP 88.152.35.103.55854 > 104.47.12.33.25: tcp 19 18:11:54.769614 IP 88.152.35.103.22 > 5.188.87.57.62114: tcp 0 18:11:54.783064 IP 88.152.35.103.22 > 5.188.87.57.62114: tcp 784 18:11:54.788164 IP 88.152.35.103.55854 > 104.47.12.33.25: tcp 0 18:11:54.789740 IP 88.152.35.103.22 > 212.8.249.191.59922: tcp 0 18:11:54.790913 IP 88.152.35.103.47617 > 184.30.210.217.80: tcp 0 18:11:54.801843 IP 88.152.35.103.22 > 185.182.193.169.34202: tcp 244 18:11:54.802527 IP 88.152.35.103.47617 > 184.30.210.217.80: tcp 0 -
Under diagnostic menu, packet capture..
edit: So that 88.152.35.103 is now pfsense IP?
edit2: Is pfsense VM on some other host... I don't see how your IP keeps changing... When you showed your pfsense wan it was not that IP.
That 104 address is MS
NetRange: 104.40.0.0 - 104.47.255.255
CIDR: 104.40.0.0/13
Organization: Microsoft Corporation (MSFT)Are you using MS for email? Not sure why you would be talking to MS on 25?? Even if you were using outlook or something it should be sending via ssl port. Most likely say 587
-
Its not a VM at the moment. Its a standalone machine until we find out whats going on.
And as you can see in the netflow/ipfix log that IP is used when i fetch my mails.
No MS or outlook. Mail provider is Runbox and i use Thunderbird.My father has a Windows Phone and i believe there is a MS account.
I don't know if this thing is doing something in the background.
And if yes it would show up in the firewall alerts because the ports are blocked? -
Add that host IP as a filter in the packet capture and will show only packets matching that.
Given that's not an IP on the firewall I don't expect to see any but......Setting the view to 'full' will show the MAC address on any packets with that IP that are captured. You can check it's the correct MAC for any NICs you have.
You can select 'full' view after the pcap has completed, just hit 'view capture' again to see it.Steve
-
So how is it your IP is 176.x.x.x but when you sniffed you saw traffic from an 88.x address? Makes zero sense!!! Clearly some piece of the puzzle is missing here..
BTW - when you posted that spam, it did show iphone as the sender if I recall... Is that link still up with the report? You could click on the details button, and pretty sure it said something about iphone??
-
Capture:
18:11:54.712622 10:c3:7b:45:b4:8c > 00:01:5c:69:ba:46, ethertype IPv4 (0x0800), length 66: (tos 0x0, ttl 64, id 30008, offset 0, flags [DF], proto TCP (6), length 52) 88.152.35.103.53026 > 104.47.14.33.25: Flags [.], cksum 0x08c3 (correct), seq 53, ack 548, win 5840, options [nop,nop,TS val 65650188 ecr 175959191], length 0 18:11:54.747653 10:c3:7b:45:b4:8c > 00:01:5c:69:ba:46, ethertype IPv4 (0x0800), length 98: (tos 0x0, ttl 64, id 29672, offset 0, flags [DF], proto TCP (6), length 84) 88.152.35.103.22 > 5.188.87.57.62114: Flags [P.], cksum 0x151b (correct), seq 1:33, ack 13, win 2896, options [nop,nop,TS val 65650191 ecr 1761297416], length 32 18:11:54.748718 10:c3:7b:45:b4:8c > 00:01:5c:69:ba:46, ethertype IPv4 (0x0800), length 66: (tos 0x0, ttl 64, id 30009, offset 0, flags [DF], proto TCP (6), length 52) 88.152.35.103.53026 > 104.47.14.33.25: Flags [.], cksum 0x08be (correct), seq 53, ack 549, win 5840, options [nop,nop,TS val 65650192 ecr 175959191], length 0 18:11:54.754257 10:c3:7b:45:b4:8c > 00:01:5c:69:ba:46, ethertype IPv4 (0x0800), length 530: (tos 0x0, ttl 64, id 14653, offset 0, flags [DF], proto TCP (6), length 516) 88.152.35.103.22 > 185.182.193.169.34202: Flags [P.], cksum 0x0eeb (correct), seq 1588:2064, ack 749, win 3878, length 476 18:11:54.754967 10:c3:7b:45:b4:8c > 00:01:5c:69:ba:46, ethertype IPv4 (0x0800), length 85: (tos 0x0, ttl 64, id 62438, offset 0, flags [DF], proto TCP (6), length 71) 88.152.35.103.55854 > 104.47.12.33.25: Flags [P.], cksum 0x1819 (correct), seq 0:19, ack 118, win 5840, options [nop,nop,TS val 65650192 ecr 175553073], length 19: SMTP, length: 19 EHLO hottmail.com 18:11:54.769614 10:c3:7b:45:b4:8c > 00:01:5c:69:ba:46, ethertype IPv4 (0x0800), length 66: (tos 0x0, ttl 64, id 29673, offset 0, flags [DF], proto TCP (6), length 52) 88.152.35.103.22 > 5.188.87.57.62114: Flags [.], cksum 0x3e18 (correct), seq 33, ack 877, win 2896, options [nop,nop,TS val 65650194 ecr 1761297497], length 0 18:11:54.783064 10:c3:7b:45:b4:8c > 00:01:5c:69:ba:46, ethertype IPv4 (0x0800), length 850: (tos 0x0, ttl 64, id 29674, offset 0, flags [DF], proto TCP (6), length 836) 88.152.35.103.22 > 5.188.87.57.62114: Flags [P.], cksum 0x9137 (correct), seq 33:817, ack 877, win 2896, options [nop,nop,TS val 65650195 ecr 1761297497], length 784 18:11:54.788164 10:c3:7b:45:b4:8c > 00:01:5c:69:ba:46, ethertype IPv4 (0x0800), length 66: (tos 0x0, ttl 64, id 62439, offset 0, flags [DF], proto TCP (6), length 52) 88.152.35.103.55854 > 104.47.12.33.25: Flags [.], cksum 0x54a3 (correct), seq 19, ack 314, win 5840, options [nop,nop,TS val 65650195 ecr 175553246], length 0 18:11:54.789740 10:c3:7b:45:b4:8c > 00:01:5c:69:ba:46, ethertype IPv4 (0x0800), length 60: (tos 0x0, ttl 64, id 51477, offset 0, flags [DF], proto TCP (6), length 40) 88.152.35.103.22 > 212.8.249.191.59922: Flags [.], cksum 0xf381 (correct), seq 1946193243, ack 2318528876, win 2920, length 0 18:11:54.790913 10:c3:7b:45:b4:8c > 00:01:5c:69:ba:46, ethertype IPv4 (0x0800), length 74: (tos 0x0, ttl 64, id 1071, offset 0, flags [DF], proto TCP (6), length 60) 88.152.35.103.47617 > 184.30.210.217.80: Flags [S], cksum 0xcb9c (correct), seq 672643643, win 5840, options [mss 1460,sackOK,TS val 65650196 ecr 0,nop,wscale 1], length 0 18:11:54.801843 10:c3:7b:45:b4:8c > 00:01:5c:69:ba:46, ethertype IPv4 (0x0800), length 298: (tos 0x0, ttl 64, id 14654, offset 0, flags [DF], proto TCP (6), length 284) 88.152.35.103.22 > 185.182.193.169.34202: Flags [P.], cksum 0x81fe (correct), seq 2064:2308, ack 785, win 3878, length 244 18:11:54.802527 10:c3:7b:45:b4:8c > 00:01:5c:69:ba:46, ethertype IPv4 (0x0800), length 66: (tos 0x0, ttl 64, id 1072, offset 0, flags [DF], proto TCP (6), length 52) 88.152.35.103.47617 > 184.30.210.217.80: Flags [.], cksum 0x9a2e (correct), seq 672643644, ack 1508780897, win 2920, options [nop,nop,TS val 65650197 ecr 3260228584], length 0Where does 10:c3:7b:45:b4:8c come from?
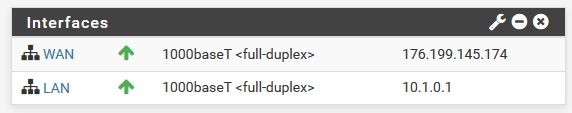
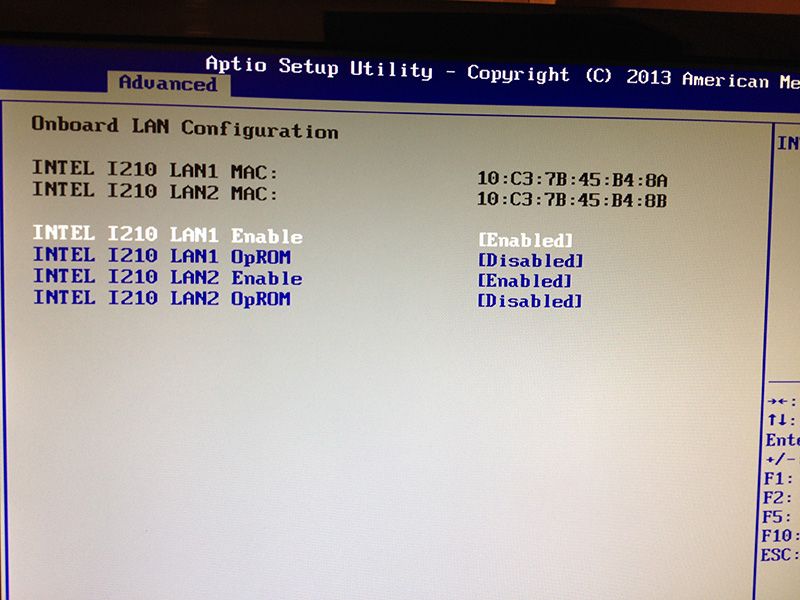
The board has 2 NIC's and show up in pfSense like this:
WAN NIC 10:c3:7b:45:b4:8a
LAN NIC 10:c3:7b:45:b4:8bFrom the DOCSIS modem:
Cable MAC 90:5C:44:3D:1D:07
MAC 90:5C:44:3D:1D:09 -
Aha! Well the consecutive MACs there look like it's something else on the same host.
You have IPMI on that device? Is it wide open?
The fact it's all outgoing TCP is a bit odd. It all looks suspicious TBH....
-
@MrGlasspoole said in How to find spambot? Got network abuse report from my ISP:
10:c3:7b:45:b4:8c
Yeah that is ASUS - didn't they have some ipmi issues? Wasn't there a bios fix they pushed? That was years and years ago - how old is this system?
Yeah quick google, from back in 2012
https://pedromadias.wordpress.com/2012/06/25/all-your-asus-servers-ikvmipmi-may-belong-to-other/ -
What the hell is IPMI?

Yes its a ASUS P9D-I
Talk to me like i never heard the word network before
I'm not a network god like you people
-
IPMI is a management protocol - problem is that there are security issues with it... So when enabled on a nic that is connected to the public internet - it can be exploited and give control of the system..
this might help
https://www.itworld.com/article/2708437/ipmi--the-most-dangerous-protocol-you-ve-never-heard-of.htmlGrabbing the manual
https://dlcdnets.asus.com/pub/ASUS/mb/socket1150/P9D-I/Manual/E8351_P9D-I.pdfI would suggest you go in and disable the IPMI stuff
And make sure you update bios and firmware...
Until you get it disabled/fixed - I would pull that hardware off the network!!!
-
When you started this thread was it not running on a VM? Was that in this same hardware though?
That is a painful discovery. Better to have discovered it though...
Steve
-
No the Hyper-V stuff is running on a ASRock Rack board.
To make sure its not Hyper-V/Windows i installed pfSense on that Asus board.
I have this Asus board since a half year but never used it until now.
Bought it for a NAS build.The BIOS is the latest. But i cant figure out how to disable that IPMI stuff.
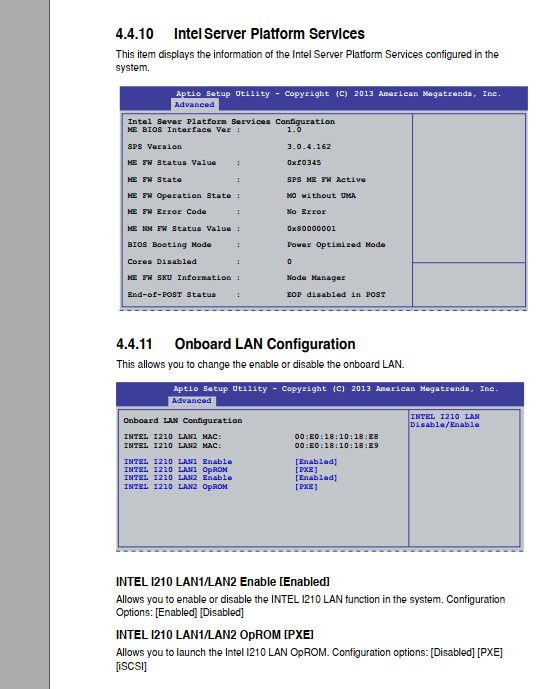
If i go to "Intel Server Platform Services" there are no settings, only information.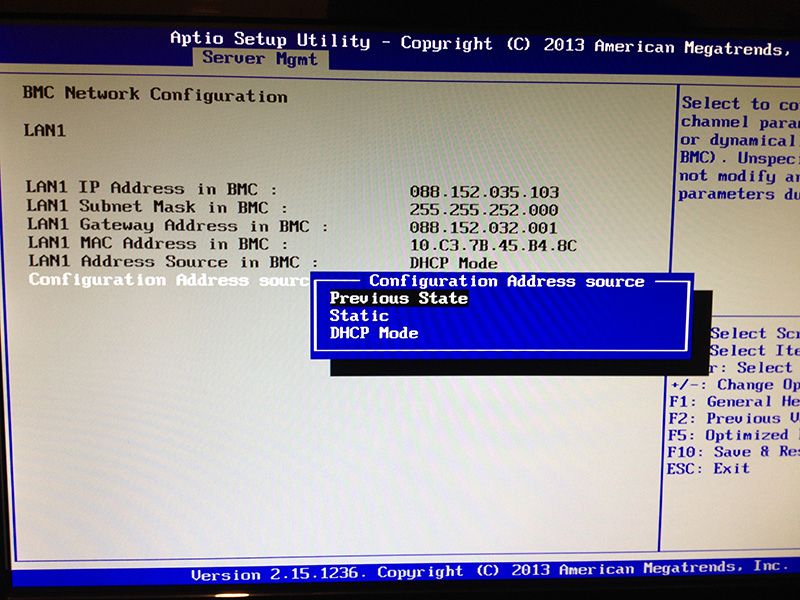
Damn. Had to move around monitors because that old 1440x900 i normally use for testing does not work.
First time i have a BIOS that only works on 1080p. -
The BMC stuff is what you want. If you can't set it as disable you can just set it to static and put in some bogus IP that is unreachable.
The BMC shares LAN1 on the board according to the manual so you should use that for LAN. It must be WAN currently if it's got a public IP.
The fact it's sending spam though, or seems to be, is highly worrying! If you can't disable the BMC entirely I would consider if that's possible to use. the BMC has access to everything on the board.
As I understand it you were seeing these spam reports before you had this board connected at all though?
Steve
-
Adding to where Steve is going -- where else was this hardware that now has pfSense on it? Was this same hardware in use elsewhere on the network? Might the LAN1 port have had access to the WAN side of your network before it was re-purposed to be a pfSense platform?
-
I cant remember what pfSense (this board or Hyper-V) was running when i had the first spam report.
What i did is switching the NICs (WAN/LAN) and did login to that ASMB7-iKVM thing.
I did disable all services except "web".
I did create a new user, changed the admin password and disabled login for the admin.
I also disabled IPv6 and set IPv4 to static.The last 2 hours there are only ~4 entries in the IPFIX log.
For example scanners.labs.rapid7. com (88.202.190.135) on port 25.
But i guess that's normal that some bots are trying to come in.I cant believe that there are boards where something like that is on by default with a default user/password.
I found this: https://homeservershow.com/forums/topic/9350-asus-p9d-i/
Looks like there is a jumper to disable it. I need to check that with the flashlight because there is nothing in the manual.I let it run now for a view hours and then i will see what happens.
So it means the bots did hijack the BIOS/IPMI to send spam?
@bmeeks, I never used that board before.
EDIT
Found it but i still can invoke that web management site
EDIT again
You need to remove power when switching the jumper that it works.
So its off now. -
This makes for a good case study indeed!
-
Ooooh.
Not a hacked modem after all.
Hacked BIOS (sort-of) motherboard ....Impressive.
-
@NollipfSense said in How to find spambot? Got network abuse report from my ISP:
This makes for a good case study indeed!
Yeah. No one is completely useless; he can always serve as a bad example.

Every day you learn something new.
Computer since C64 and never heard of IPMI before...Thanks to everybody here. Never would i had figure that out myself.
The good thing is i have PRTG now. A while back i was looking at Zappix and found it complicated.
This are the softflowd entries from the last 12 hours:
Not sure right now what 10.1.2.3 is. But my parents have yahoo mail. They are away since 2 hours for 3 days and it can be a phone/tablet.
Any tips what you would log for a certain time (2, 3, 5 days) in a home network?
At the moment I'm logging just the blocked outgoing mail firewall ports on LAN (System Logs Remote Logging) and
this ports on WAN.