Can't reach my switch's management interface from my VLANs
-
Hello,
I'm trying to connect to the management web page of my switch with no success.- Switch IP is 10.0.0.2.
- 3 interfaces on my pfSense
em0 : 10.0.0.1
em0.100 : 192.168.0.1
em0.500 : 10.10.10.1
All my hosts on all my VLANs are able to ping the switch on 10.0.0.2 but none of my hosts that are connected on VLANs (100 & 500) are able connect to port 80.
A tcpdump listening on pfsense interface em0.100 shows the packets (192.168.0.5 > 10.0.0.2:80). A tcpdump listening on em0 shows no packets for the same source and destination. However I can see pings & replies passing through both interfaces.
I've checked firewall logs and I see nothing related. I also double checked that all my rules were logging.
I can reach 10.0.0.2:80 when connected directly on the switch port that carries the 10.0.0.1/24 network (no vlan).
Thanks
-
Hi,
As you found out / suspected already : has nothing to do with pfSense.
edit : hummm. You have (V)LAN's set up on pfSense. What are the firewall rules ? The web interface 10.0.0.2 port 80 TCP traffic needs a rule passing it on the right (V)LAN interface. Start with a pass all rule, and then work downwards (being more restrictive). Remember : on NON-LAN ports, only DHCP passes by default, nothing else.
The GUI of the switch is accessible on a dedicated LAN port and or any LAN port according to its settings.
Actually, I guess you have a good switch as its behaviour seems quiet obvious to me.Btw : without mentioning brand and type of your switch your question can't be really answered. What about RTFM ?
-
Hi @Gertjan,
" has nothing to do with pfSense." : I am not so sure. Packets dies IN pfSense firewall between the virtual interface em0.100 and the physical interface em0 (as the tcpdumps shows).on em0.100 we can see the incoming packet, no reply:
[2.4.4-RELEASE][root@pfSense.localdomain]/root: tcpdump -s0 -ni em0.100 "host 10.0.0.2" tcpdump: verbose output suppressed, use -v or -vv for full protocol decode listening on em0.100, link-type EN10MB (Ethernet), capture size 262144 bytes 10:43:46.020804 IP 192.168.0.5.58602 > 10.0.0.2.80: Flags [S], seq 1134121293, win 29200, options [mss 1460,sackOK,TS val 4282386755 ecr 0,nop,wscale 7], length 0 10:43:46.271859 IP 192.168.0.5.58604 > 10.0.0.2.80: Flags [S], seq 1486979214, win 29200, options [mss 1460,sackOK,TS val 4282387006 ecr 0,nop,wscale 7], length 0 10:43:47.050537 IP 192.168.0.5.58602 > 10.0.0.2.80: Flags [S], seq 1134121293, win 29200, options [mss 1460,sackOK,TS val 4282387785 ecr 0,nop,wscale 7], length 0 10:43:47.275025 IP 192.168.0.5.58604 > 10.0.0.2.80: Flags [S], seq 1486979214, win 29200, options [mss 1460,sackOK,TS val 4282388009 ecr 0,nop,wscale 7], length 0 10:43:49.070531 IP 192.168.0.5.58602 > 10.0.0.2.80: Flags [S], seq 1134121293, win 29200, options [mss 1460,sackOK,TS val 4282389805 ecr 0,nop,wscale 7], length 0on em0, we do not see any packet arriving:
[2.4.4-RELEASE][root@pfSense.localdomain]/root: tcpdump -s0 -ni em0 "host 10.0.0.2" tcpdump: verbose output suppressed, use -v or -vv for full protocol decode listening on em0, link-type EN10MB (Ethernet), capture size 262144 bytesI have a firewall rule on the very top allowing any source to go to 10.0.0.2:80 on the em0.100 firewall ruleset. I created the same rule on em0 ruleset just to be sure.

"The GUI of the switch is accessible on a dedicated LAN port and or any LAN port according to its settings." : I agree, however if I do a telnet from pfSense CLI and specify source ip (192.168.0.1) to 10.0.0.2 80, I get a connection (telnet -s 192.168.0.1 10.0.0.2 80), so the switch allows 192.168.0.1/24 to connect to the management GUI.
The switch is a TP-Link TL-SG108E. I'm running pfSense 2.4.4-RELEASE-p3.
Thanks
-
@echo4201 said in Can't reach my switch's management interface from my VLANs:
The switch is a TP-Link TL-SG108E
What hardware version what firmware - those switches had issue where they could not actually do vlans, since you couldn't remove vlan 1 from ports..
You understand now traffic would be sent to 10.0.0.2 out that interface if pfsense can not arp for it right... Do a sniff not calling out host.. Look in the arp table.. Does pfsense hold arp entry for 10.0.0.2?
When you sniff do you see arps for the ip? So for example sniffing on my guest network (vlan) I sent ping to non existent IP in that dest vlan 192.168.6.55... It never sends on the ping, because it can not find the dest..
You only see the arps for it..
10:00:44.617083 ARP, Request who-has 192.168.6.55 tell 192.168.6.253, length 28 10:00:49.471260 ARP, Request who-has 192.168.6.55 tell 192.168.6.253, length 28 -
@echo4201 said in Can't reach my switch's management interface from my VLANs:
The switch is a TP-Link TL-SG108E
Avoid TP-Link as some of their gear has problems working with VLANs. I have a TP-Link access point that I couldn't set up with a guest SSID, because of that issue.
-
Yes I do see 10.0.0.2 in the ARP table and the ARP requests does get replied.
[2.4.4-RELEASE][root@pfSense.localdomain]/root: arp -a | grep 10.0.0.2 ? (10.0.0.2) at 18:d6:c7:9a:8e:ff on em0 expires in 1151 seconds [ethernet]Reminder: I can reach 10.0.0.2:80 from my pfSense box (telnet -s 192.168.0.1 10.0.0.2 80) and pings do work.
TL-SG108E:
Firmware Version 1.0.2 Build 20160526 Rel.34615
Hardware Version TL-SG108E 2.0 -
@JKnott I have no other issue with VLANs with that switch, but yes it's not the best switch. I will avoid TP-Link for the future. It's for a homelab.
-
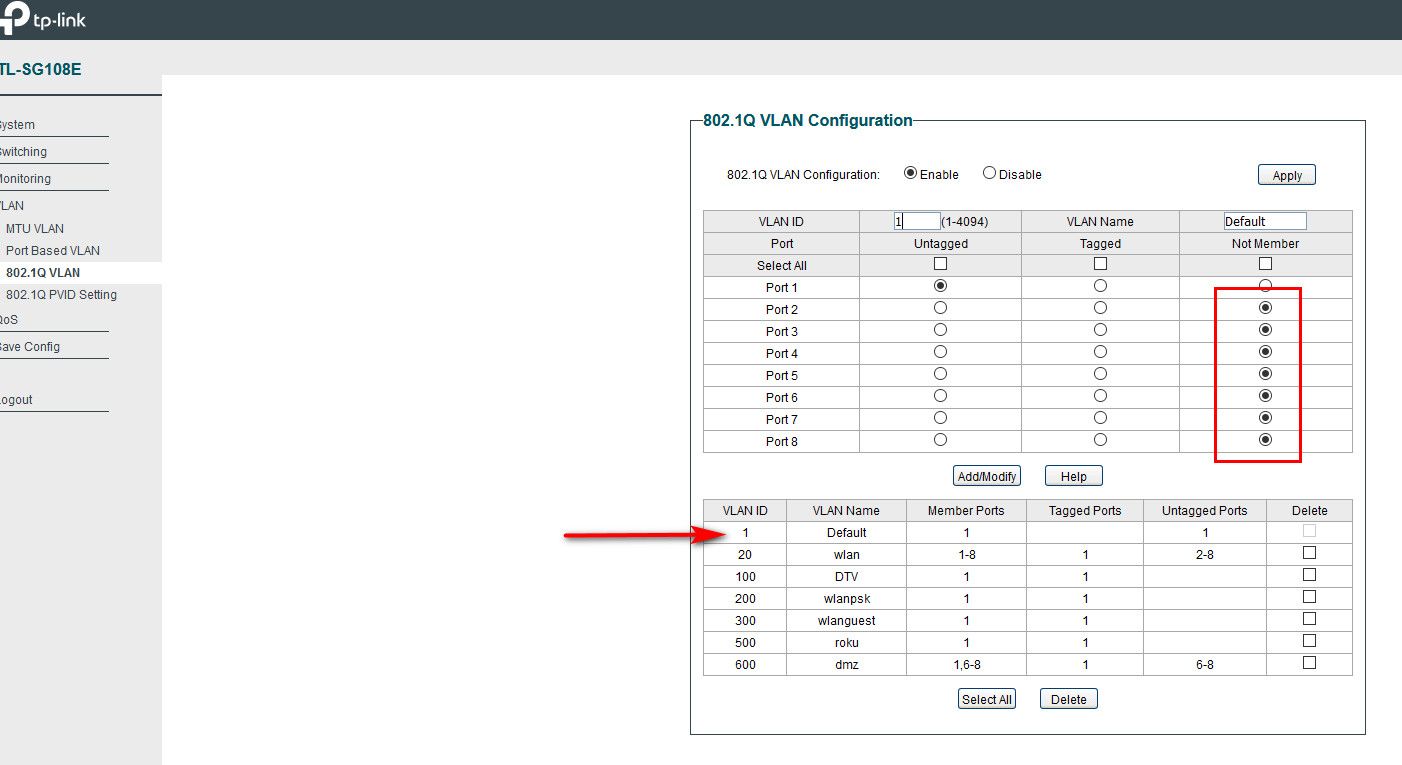
Well sorry to tell you but that switch is garbage... You can not remove vlan 1 from ports... So its pretty useless doing vlans
v3 has firmware fix, but v1, 2 are just F'd
You can use it for a dumb switch, but if your going to want to actually do vlans your going to need different switch.
here is thread over on their forums about it
https://community.tp-link.com/en/business/forum/topic/96245?page=1Took them forever to fix!! And they never fixed it for the older hardware
edit: I take its the same interface to the switch... So what mac do you see for the IP of the switch, and how many different interfaces do you see on.. Do you see it on your .100 as well?
Do you have a different switch you can use? That switch is just a POS... So you can never actually create an isolated L2.. all your doing amounts to running multiple L3 on the same L2..
-
Crap ok. You convinced me for the switch. I will try getting a new one soon.
The thing that baffles me, is that I'm at least expecting to see the packet exit em0 on pfSense, which I am not.
When doing an "arp -a" I only see 18:d6:c7:9a:8e:ff (TP-Link) on em0, not em0.100, which is expected unless I'm wrong?
Edit: it seems that I can upgrade to the V3 firmware according to TP-Link in that thread you gave me. I will try that.
-
You can use the v3 hardware firmware on the v2 hardware? Really? I have the v2 same switch on my self... I should try that.. Your saying it says that in that long has thread I linked too? Do you have a direct link - thanks!
going through that whole thread again, I don't see where you can use v3 firmware on v2 hardware.. I see this
Support told me to try the V3 firmware but it reports invalid image when I try. I advised them of this and they then said it wasn't compatible. Can the V3 firmware be made to work?
Makes no sense that you could do that, if it actually is the same firmware why would they not just back ported it so it can install on v2 hardware, etc..
Like I said that switch is CRAP, and I really wouldn't have anything to do with that company ever - if they can not get something like basic vlan isolation correct.
Only reason its on my shelf is people here complaining that vlans were not working, so I bought one myself to play with - and yup they were right.. It doesn't do vlans!!
I have a dlink and netgear that are in the same price point area that do them just fine.. This works fine for example
https://www.amazon.com/D-Link-EasySmart-Gigabit-Ethernet-DGS-1100-08/dp/B008ABLU2II used it for a short time to test, but currently none of those low end switches actually on my network.. I have cisco sg300-28 and sg300-10 currently... If your wanting to "lab" something in that price point would be much better ;) I got the 28 for like $180 a while back.. Can do L3 routing, etc. etc.
-
https://community.tp-link.com/en/business/forum/topic/96245?page=3
post 23 and 24. Rain is from TP-Link support according to post 20.
-
Well going to plug it in right now and give it a little test ;)
edit:
Well look at that!!
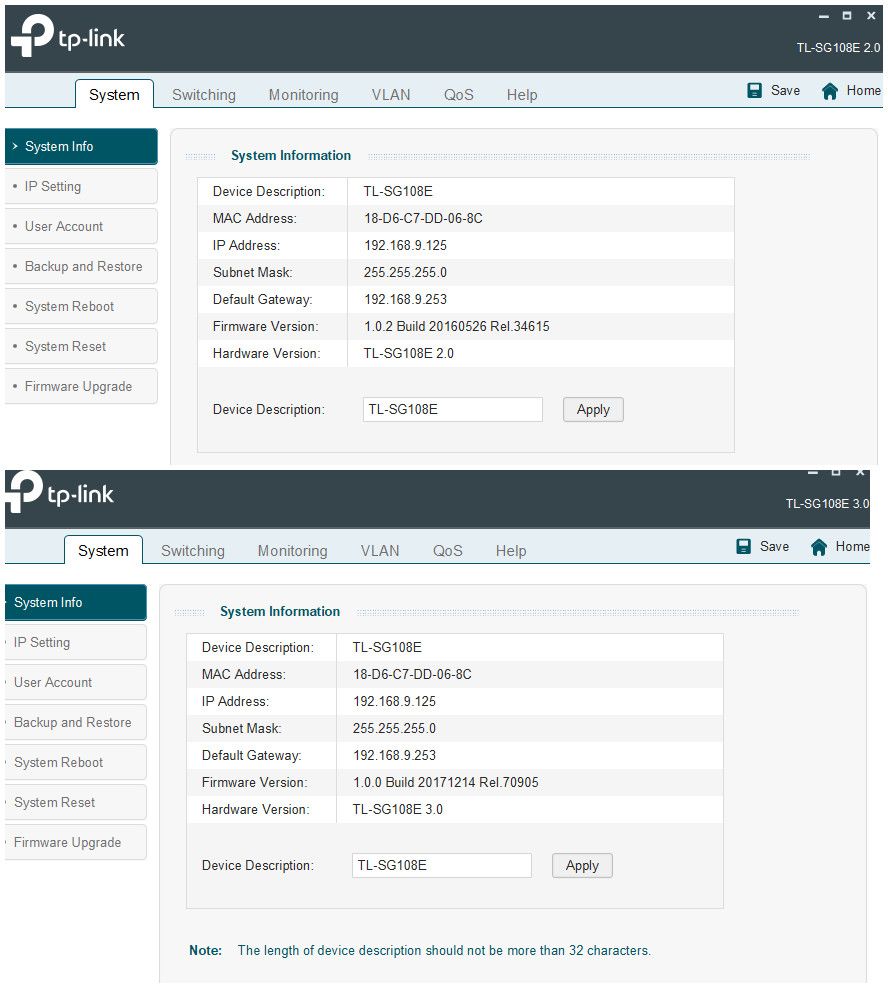
Hmmm - now to see if actually fixed the vlan issue.
edit2: Well the gui config application does not allow you to remove ports from vlan 1... But the web interface does..
-
That’s great news! I will try to upgrade it later today or this week. In the meanwhile, happy new year to everyone!
-
Wonder if I can put V4 firmware on it ;)
-
@johnpoz that's awesome, you did a firmware upgrade on this hardware:
TL-SG108E 2.0 and that even replaced your hardware to:
TL-SG108E 3.0
Tell me the trick and I'll try that with my car!
-
BTW: is the web interface of those switches reachable on all VLANs or do they have a management VLAN?
-
@jahonix from all VLANs and that’s hardcoded. Can’t limit which VLANs can access it.
-
Yeah that was there reasoning behind not being able to remove vlan 1 ;) Now that you can remove vlan 1 from ports - you should be able to limit from what network you can access the switch gui from.