VLANs without a 'Smart' Switch?
-
So I've been at this for a few days and I've gotten MOST things configured the way I want, but I've run into a wall and I'm wondering if what I'm attempting is even possible at this point.
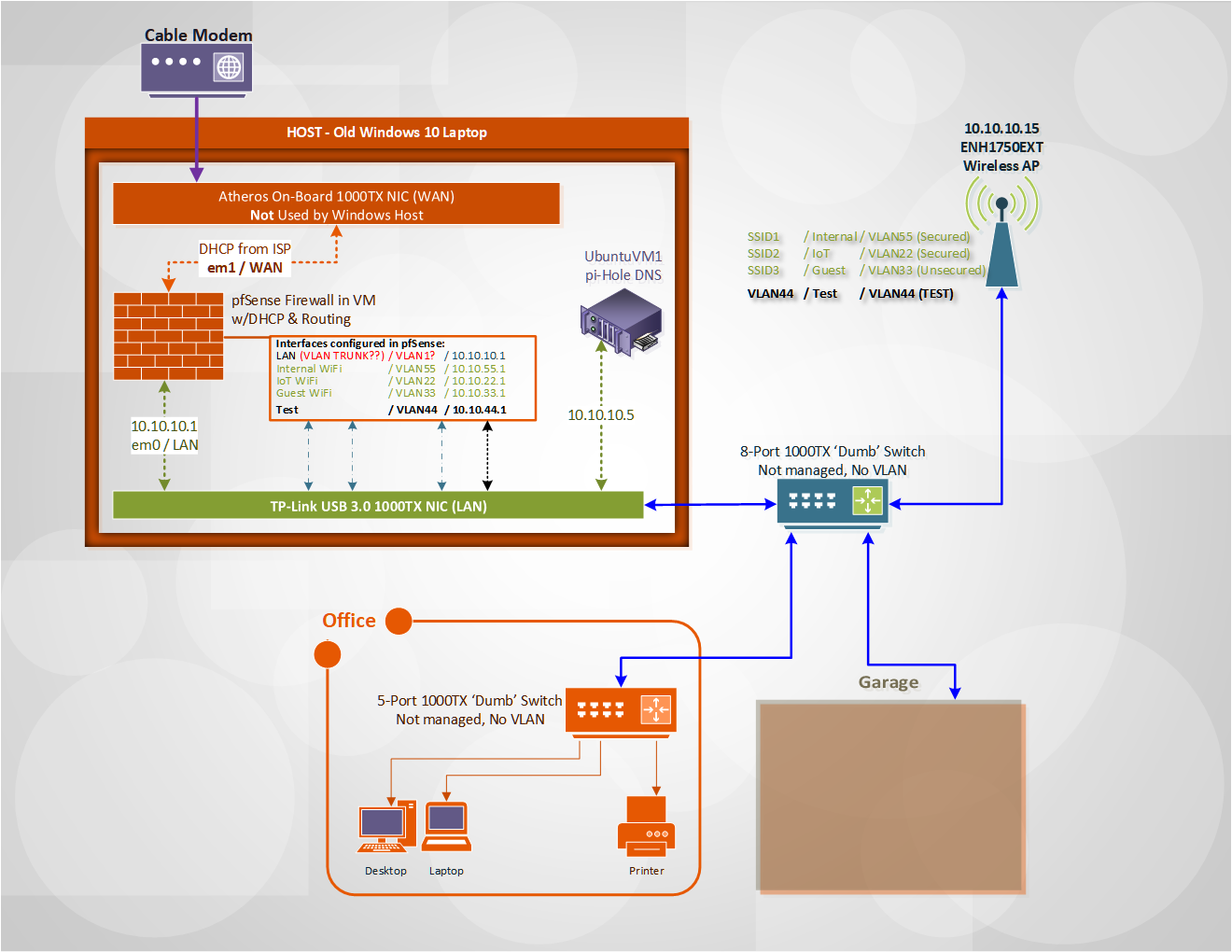
Without going into fantastic levels of detail, here's the diagram, and it's worth noting that my Access Point has the ability to Tag specific SSID traffic with a VLAN ID (that piece seems to be working fine)...
Ran a wire shark and could see the clients asking for DHCP, and the pfSense DHCP configured on the primary LAN (not VLAN44 as expected) was replying but apparently that message wasn't making it back up stream to the AP/Client on SSID VLAN44.
Will add more after I've had some food, but wanted to get this out there for some visibility in the mean time, in case someone has any great ideas!Thanks! :)
-
If your lan vs dhcpd running on vlan44 was seeing the dhcp discover.. Then you have something stripping the tags.. And no it wouldn't get back to your client on vlan 44..
So you running this on hyperV on windows 10.. You have to do some special stuff for vlans to work on hyper-v... And yes you still need a SMART switch that can do vlans!!
I did a few posts awhile back on how to do vlans on on hyper-v, you have to set them via the powershell.
-
here I dug up that old post - wow year ago.. time flies
https://forum.netgate.com/topic/139891/solve-hyperv-2012-vlans-support-hn0/8
-
@johnpoz actually using VirtualBox but I doubt that makes a difference (spent 3 days trying to get it setup in VMWare with no success even getting the NICs to bridge correctly... so much has changed in the last decade!)
I was curious about something stripping the tags, and even swapped the NIC with the USB NIC (on-board Atheros had reports of VLAN ID Stripping, and the USB NIC had more options in advanced driver functions in windows).
It's worth noting that the only thing enabled on both NIC in Windows is the adapter for VirtualBox - they don't even get an IP as far as Windows knows.
I do have one switch that's capable of handling VLANs, but I can't find the power adapter at the moment, and was hoping I could get by with this method since pfSense let's me assign VLANs as interfaces.
-
@johnpoz I'll have to read through that in a bit (or in a few days, at this point...)
I was wondering and poking around at maybe using something like vSwitch in a VM or even on the same Ubuntu VM w/ pi-hole, but hadn't made it that far down the rabbit hole yet.
I've got strong networking and general tech background, but still very new to VLANs, so mostly just trying to learn at this point.
-
Well have not setup any vlans with virtualbox.. I have it installed - guess I could fire it up and do some testing..
You could prob set it up with vswitch doing the tags in virtualbox. If your going to setup vlan on pfsense the tag has to get to pfsense, if pfsense sees the traffic with the tag, it will send the traffic back with the tag.
But if pfsense doesn't see the tagged traffic, then no it could never send it back with a tag..
There are a few ways to skin this cat - but while a dumb switch might not strip tags. If your going to pass vlan traffic over a dumb switch your not actually securing anything unless the switch can isolate actually isolate the traffic via the tags..
While you could do such a thing in a lab, or in a pinch for a test setup, etc. If your going to do vlans - your switches really need to understand them to actually do it correctly!!!
-
@johnpoz at the moment, my primary goal is to get the IOT traffic segmented away from the rest of the network (hence the multiple SSID w/ corresponding VLAN).
I'll eventually get a proper switch which will obviously help... just wasn't sure if this was even feasible as-is, or even how to tell whether or not the pfSense was getting the VLAN tag in the first place.
I'll try to get some screenshots of the config posted.
-
Well from a 2 minute browsing about virtualbox and vlans - looks like the physical nic can have issues with stripping the tags in a bridged setup..
This is going to be more complicated than prob thought to be honest.. You prob going to want multiple physical interfaces in your virtualbox host, and then do the vlans on your switch..
You prob have better luck with vlans if your host for virtualbox was linux based vs windows 10... I did run across a post about disable vlans and priority on realtek cards - which might have it pass the tags to the vm..
I don't really have time to dig into this at the moment.. And problem is don't have a lot of physical nics to play with - other than the realteks that are in my windows machine.. But seems your using usb nic?
Or if you just used hyper-v vs virtualbox..
When I get some time - prob trmw, I will fire up a vm on virtualbox and try passing it some tagged traffic to see if it sees it.
edit:
So another few minutes of research and does your interface in windows have a setting for vlan & priority (realtek does) and if you set it to disabled.. Its suppose to not strip the tags."The "Realtek PCIe GBE Family Controller" NIC can be configured to not strip the vlan tags, by going to the Adapter Settings and setting "Priority & VLAN" to "Priority & VLAN disabled". All the other values for this option will make the driver delete the VLAN tags from the frame."
-
@johnpoz I saw that earlier but forgot to go back and change it to see if it makes a difference... that was definitely one of the options that the newer USB NIC had that the on-board (2010) didn't have, so... cross your fingers!
-
@johnpoz Houston, we have liftoff!
Now I just have to start writing the firewall rules and get the rest of the vlan's configured... I'm sure I'll be back!
Thank you so much!

-
Great - while you "can" pass vlans over a dumb switch... It is not good setup and not secure.. You need to put actual smart switch(es) on your to buy list... They can be had for like $40 for 8 port gig... So they are not all that expensive..
Just highly suggest you stay away from the cheap tplink ones - they have issues with vlans... I would suggest say the dlink dgs-1100-08 as better choice.
currently see it on amazon for $40
https://www.amazon.com/D-Link-EasySmart-Gigabit-Ethernet-DGS-1100-08/dp/B008ABLU2I -
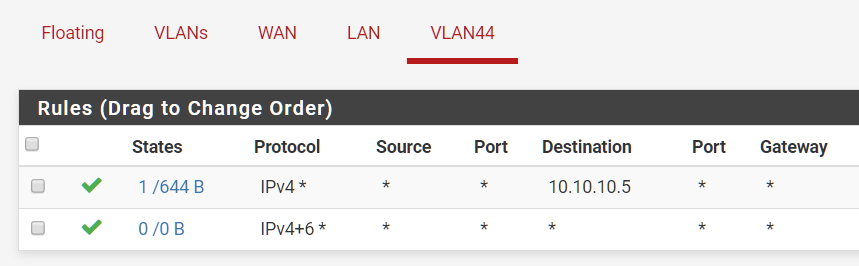
Wow, those are some huge screenshots lol.
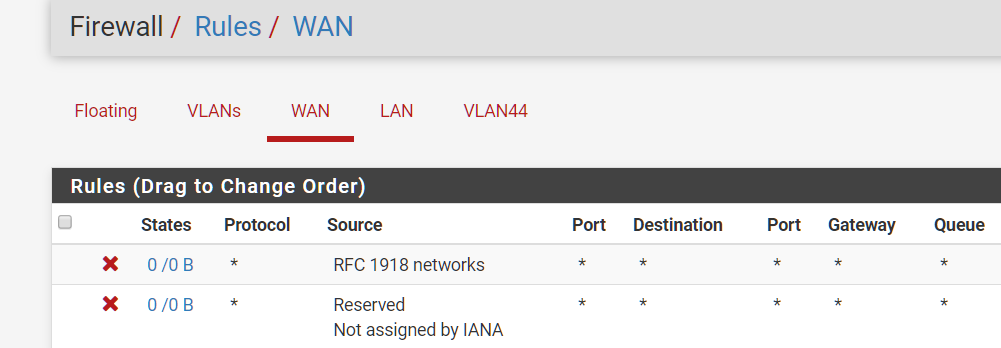
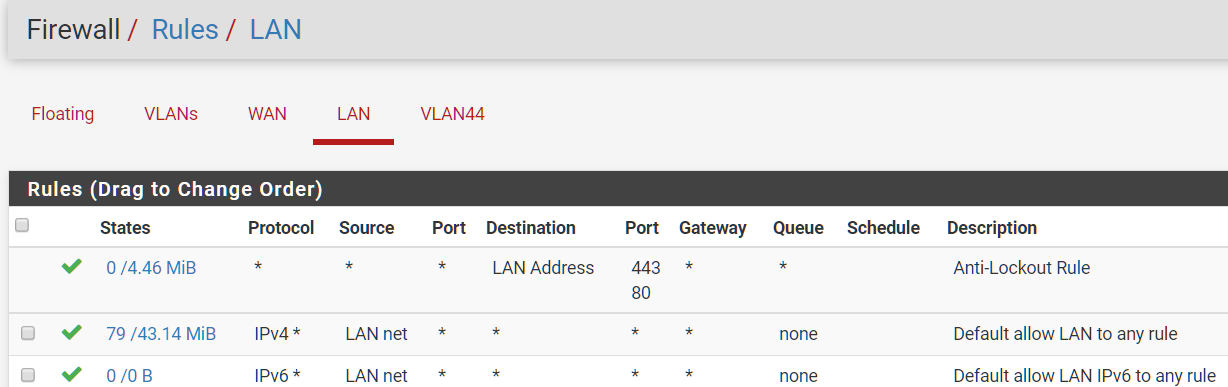
So, even though we're getting an IP from the correct DHCP now, I'm still not getting internet traffic through on that SSID... see firewall config below...
I assume I'm missing something obvious at this point

-
Did you mess with outbound nat? Auto would of auto added your vlans, but if you set it to manual for some reason that could cause you problems.
Can you ping pfsense vlan44 IP? Can you ping pfsense wan IP? From your vlan 44 client?
So while it looks like your allowing dns to that 10.10.10.5 address - does it actually return query for dns?
Can you ping 8.8.8.8 from the client.
-
I think I forgot to hit "apply" on that first screenshot, and those settings did work after I applied them...
However, this is how I intended to set it up (probably my own exhaustion and ignorance here), to only allow that SSID/VLAN (IOT devices) to access the internet through the firewall, but disallow them from accessing any other local networks / VLANs...
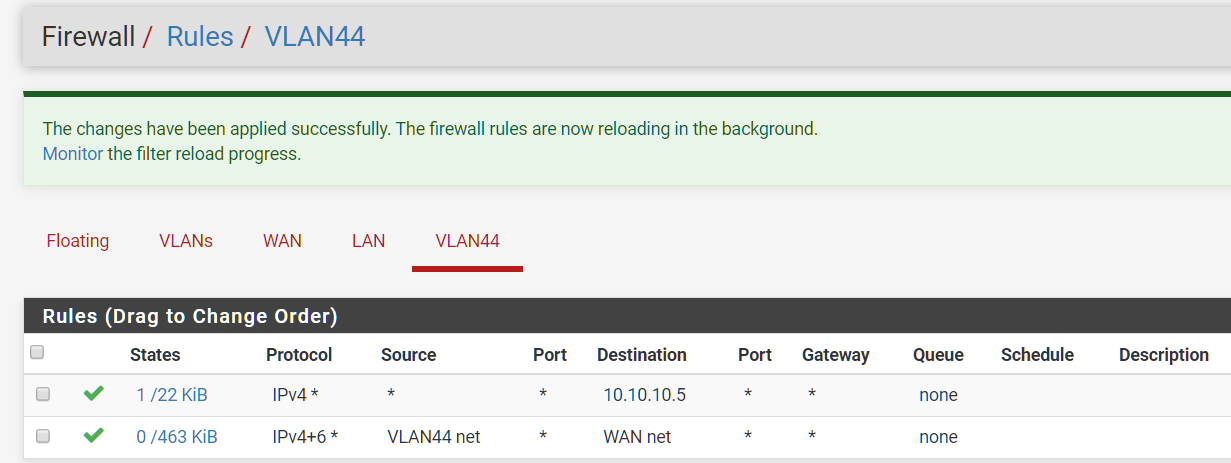
Also tried it like this...
Most everything I can ping from my phone, including the .5 DNS, just can't make it to the internet...
Here are my other configs, in case it matters...
-
I don't think I did a very good job answering, so I'll be thorough...
- Did you mess with outbound nat? No.
- Can you ping pfsense vlan44 IP? From my PC (LAN), no - also no from phone (VLAN44). I assumed that the interface just wasn't responding to pings in general.
- Can you ping pfsense wan IP? Yes, from PC (LAN) and Phone (VLAN44)
- From your vlan 44 client? Yes.
- So while it looks like your allowing dns to that 10.10.10.5 address - does it actually return query for dns? Haven't checked query, but I can ping it from my phone
- Can you ping 8.8.8.8 from the client. Phone (VLAN44), no.
-
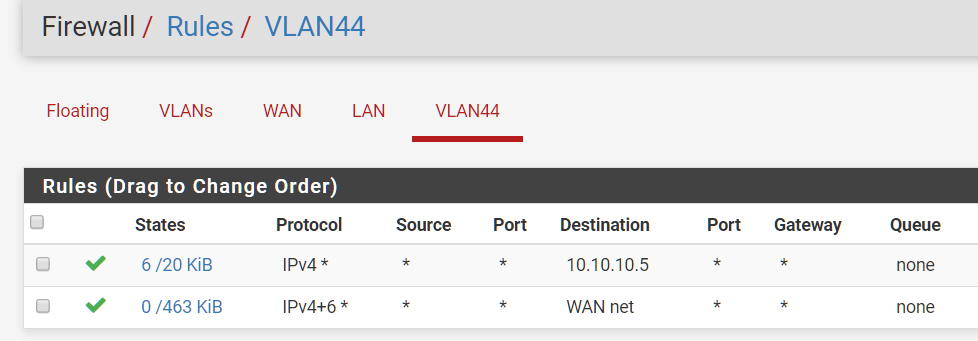
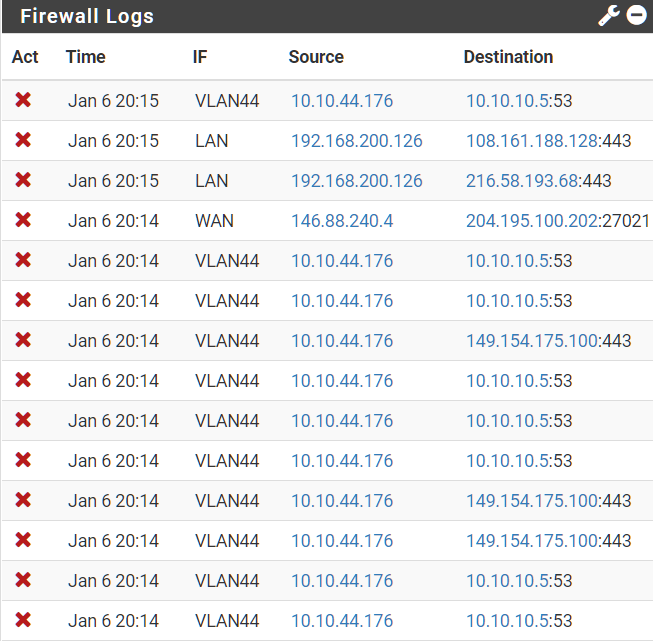
Just testing my own understanding at this point... adding the top line does allow me to ping 10.10.10.1 from VLAN44, but the second line does not.
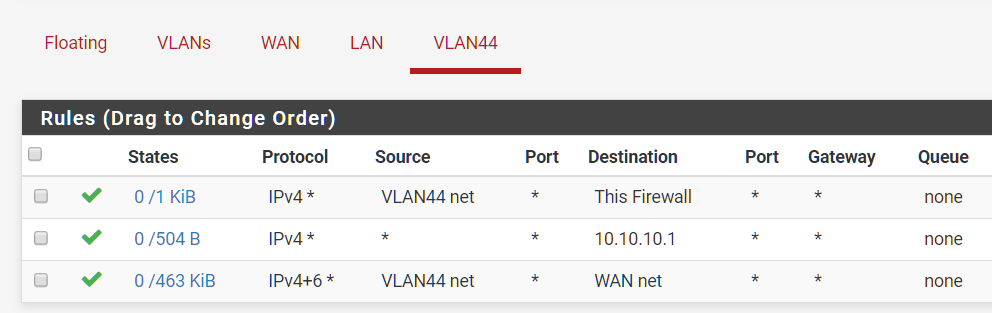
As I understand it, the bottom rule should be passing traffic between VLAN44 and WAN, but that doesn't appear to be the case...
Just noticed this in the firewall logs, probably related but I'll poke more...
-
If you want internet - internet is ANY, not wan or wan net, etc.
Rules are evaluated top down, first rule to trigger wins, no other rules are evaluated..
If you don't want vlan44 to get to other vlans, then put in a rule that blocks above the any allow rule.. Setup an alias with say all rfc1918 space..
Here is example I use to show users how it "can" be setup..
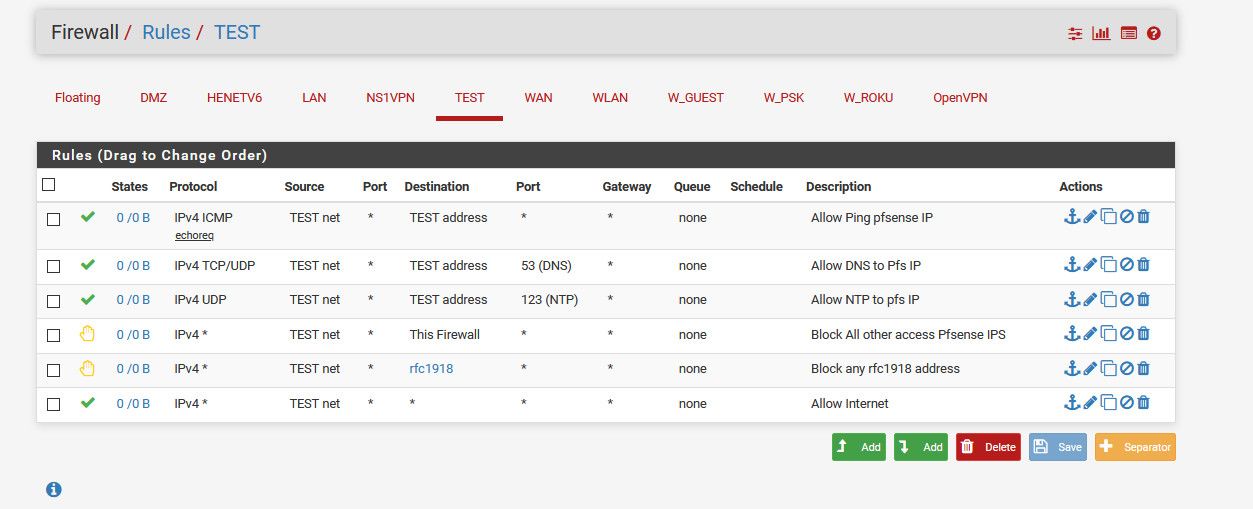
They are labeled what they do.
-
Okay, we're rolling... I need to get some rest, but truly appreciate all the help. I'm sure things will run along smoothly once I have a fresh set of eyes!

-
Great - any questions just ask, here to help.
Remember get those smart switch(es) on order! ;)