Google play store and download blocked
-
Hi,
I am very new to the pfsense and installed it few days ago. While running it, I found that it is blocking google play store downloads and even google play store page from the desktop.
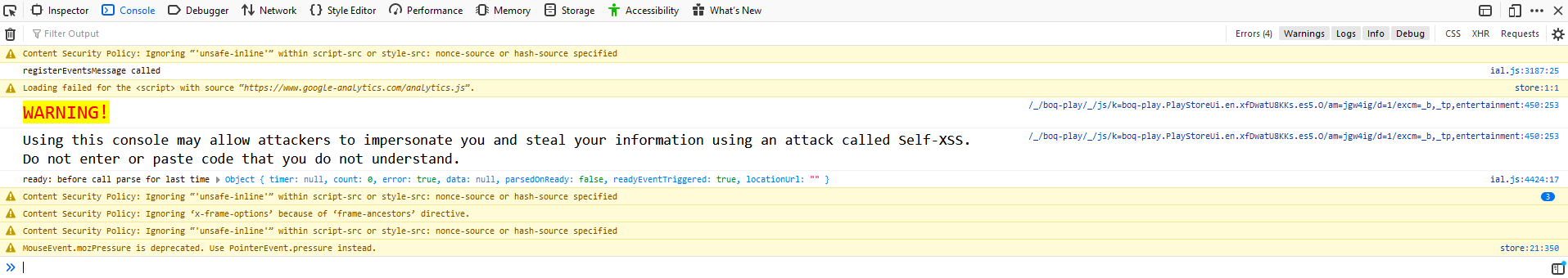
Here is what I see when I visit google play store page.
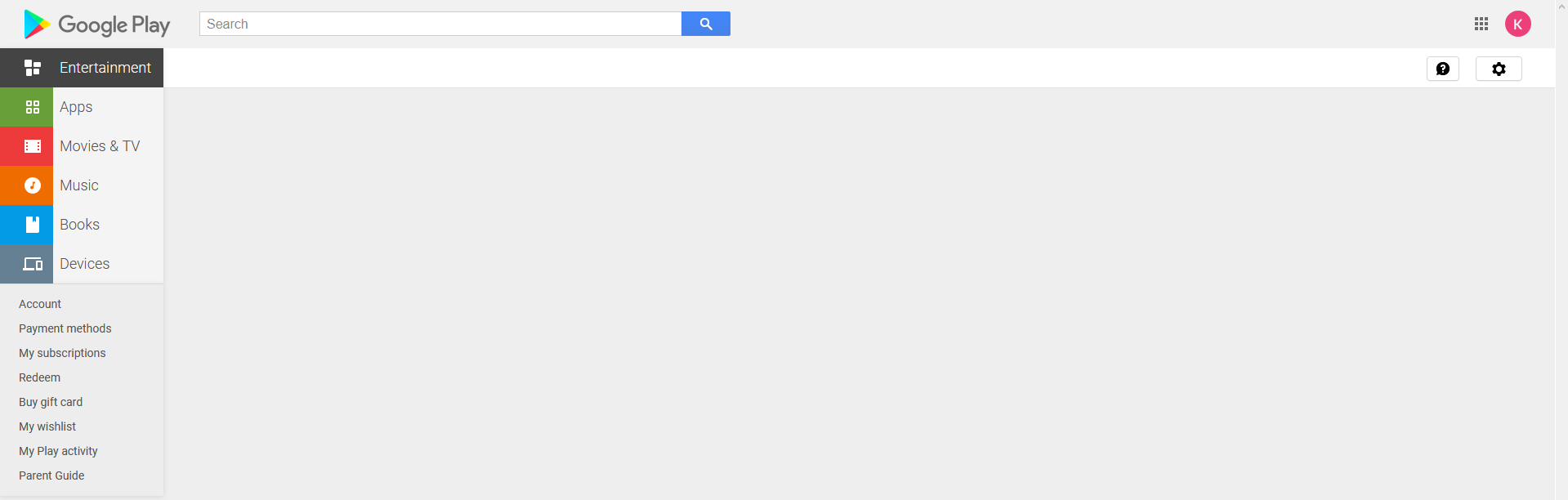
No console errors of any kind
From mobile, google play store loads but when I try to download any app, download never starts.
I have DNS resolver enabled and using opendns as my DNS server in General setup. I checked logs on opendns server and nothing is blocked there. I even try removing the DNS server from the general setup and use the google's. No luck. So looks like pfsense is blocking it somewhere.
How can I see what urls are being blocked for a particular device in real time?
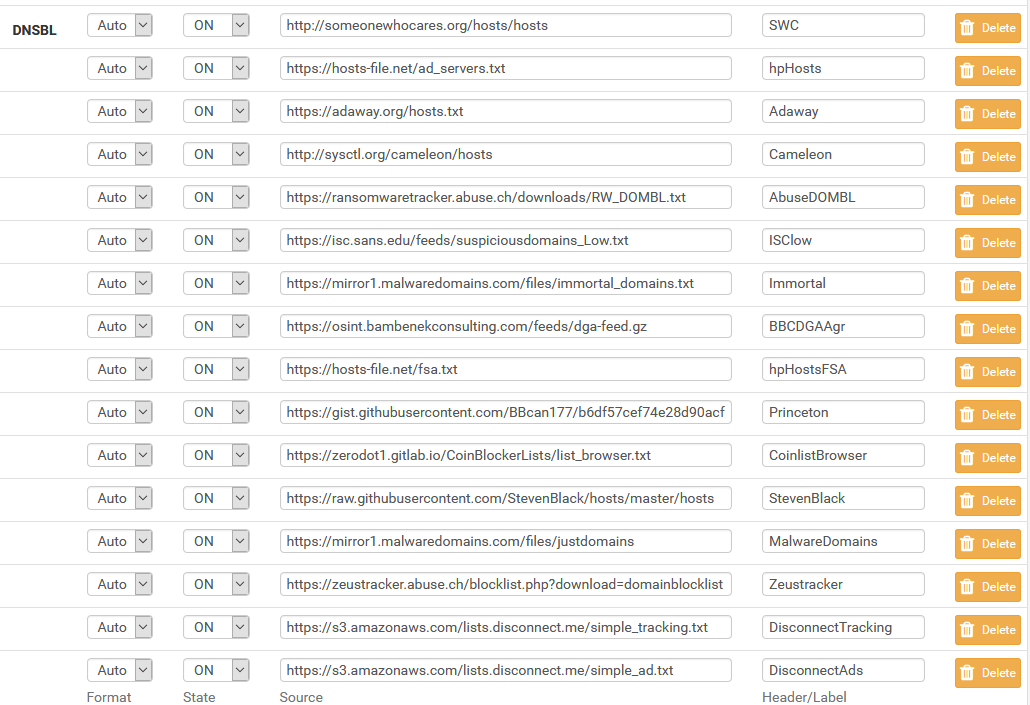
Also I have pfblockerng installed and enabled Easy list and Easy privacy list
Also here are my few custom feeds.
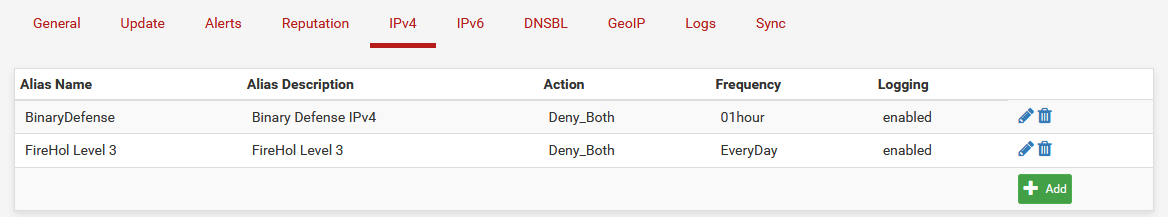
Here are my IPv4 rules
Can someone please help me figure out what is really blocking it? I will truly apprecviate it.
Thanks
-
Do you see anything in the firewall log when you try to connect?
Do you have logging enabled in pfBlocker-ng for it's rules? Enable it if not.
Do you see anything in the alerts in pfBlocker when you try to connect?
It's almost certainly something you're blocking in pfBlocker but you could just disable it to prove that.
Steve
-
Steve,
Thanks for your quick response.
I didn't enable the logs in pfblocker. I just enabled it.
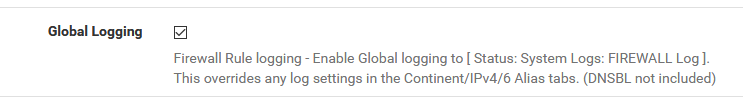
There are no alerts generated when I am trying to download an app from my cell phone. Here are the alerts I see:
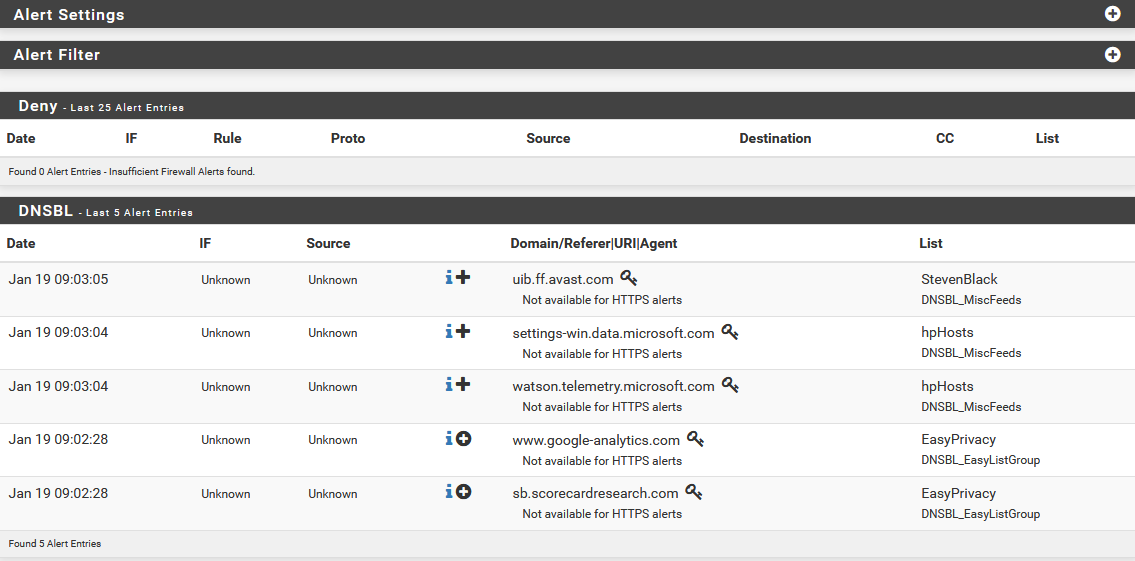
I tried completely disabling pfblockerNG and I still can't download anything
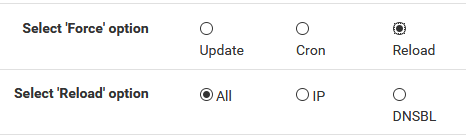
Do I need to do anything after diabling pfblocker? Clear cache of any kind OR run force update OR wait for few minutes?
Thanks
Andy -
If it was something in DNS-BL you might need to wait for any cached DNS responses to time-out on the host.
If it was blocked by a firewall rule without logging enabled that should apply immediately.
Steve
-
Steve,
I will keep my pfblocker to stay disabled and wait for some time to see if it fixes an issue. Once I know that pfblocker is causing an issue, I will slowly start enabling one feed at-a-time.
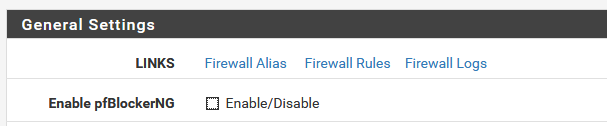
Here are my LAN rules
-
So if you have logging enabled on those pfBlocker rules (in pfBlocker) you should see anything rejected by them in the firewall log.
Anything blocked by DNS-BL should appear in the pfBlocker alerts.If you see neither of those it might be something else entirely.
https://docs.netgate.com/pfsense/en/latest/routing/unable-to-access-some-websites.htmlSteve
-
Steve,
I followed your guideline and also looked at everything mentioned in the url you specified. Still no luck. Is there any log do you want me to post to look at?
This is really a weird issue. Do you also want me to disable all feeds? Because, I removed DNS-BL rules from my IOTVLAN but it still exists on WAN.
I infact tried disabling it for few minutes and tryied it with no luck.
I didn't feel comfortable disabling the DNS-BL on WAN for a longer time.
Thanks again sir.
Andy -
Steve,
Looks like I got littler closer now..
As soon as I completely disable DNS-BL (not pfBlocker), it starts working.
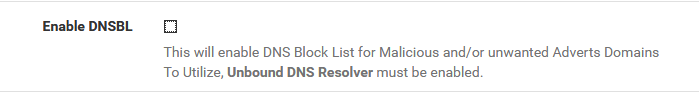
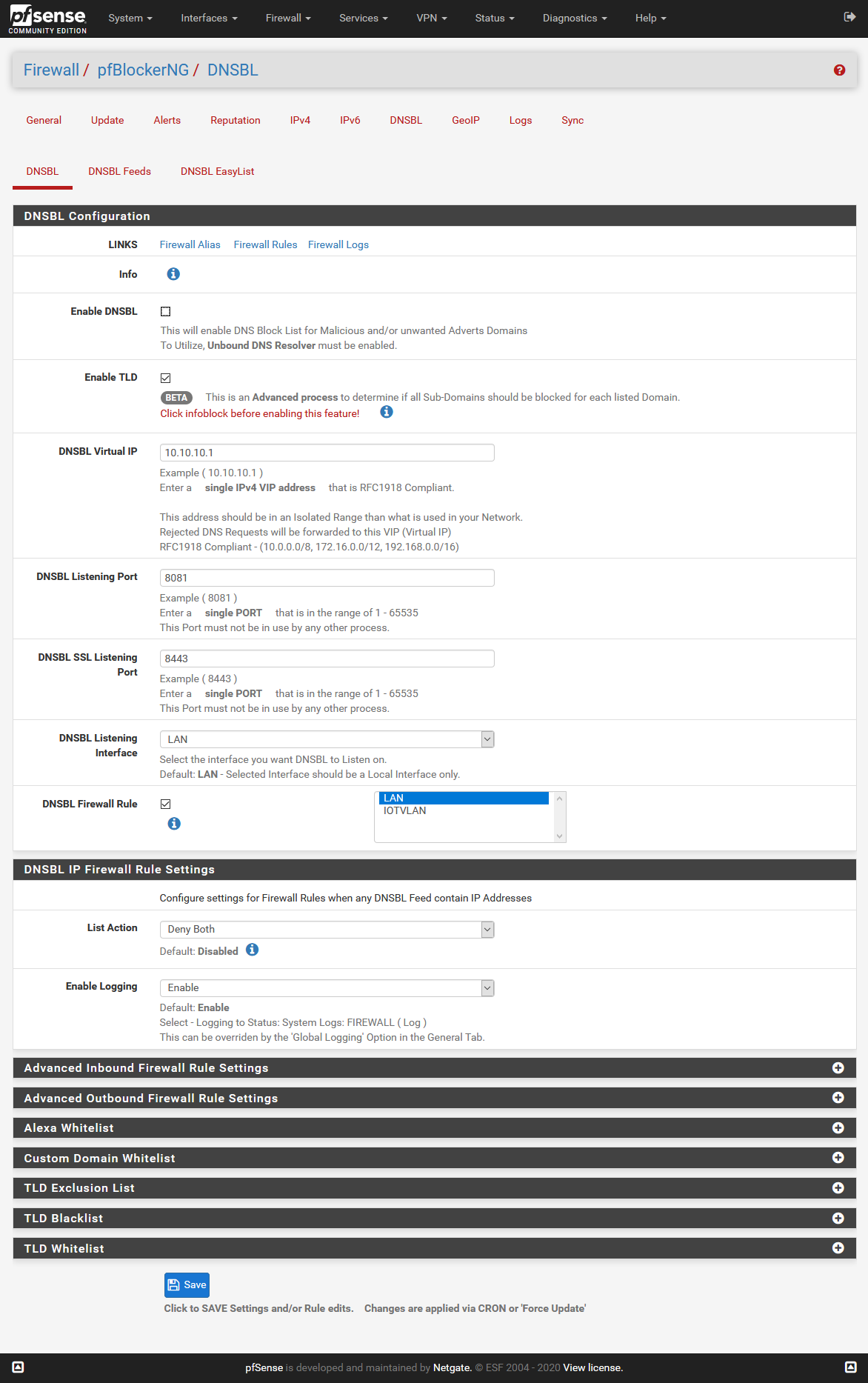
But as you see below, I only selected DNS-BL for my LAN and not IOTVLAN.
I am still scratching my head on why it wouldn't work while I am connected to IOTVLAN. None of the DNS-BL should apply on my IOTVLAN (I would like to apply on that interface as well eventually if I can pinpoint the issue with google play and when I know how to debug an issue with url access)
So looks like, something is applied somewhere as soon as I enable DNS-BL and it is applying on all interfaces even if that interface is not selected. as seen in above picture.
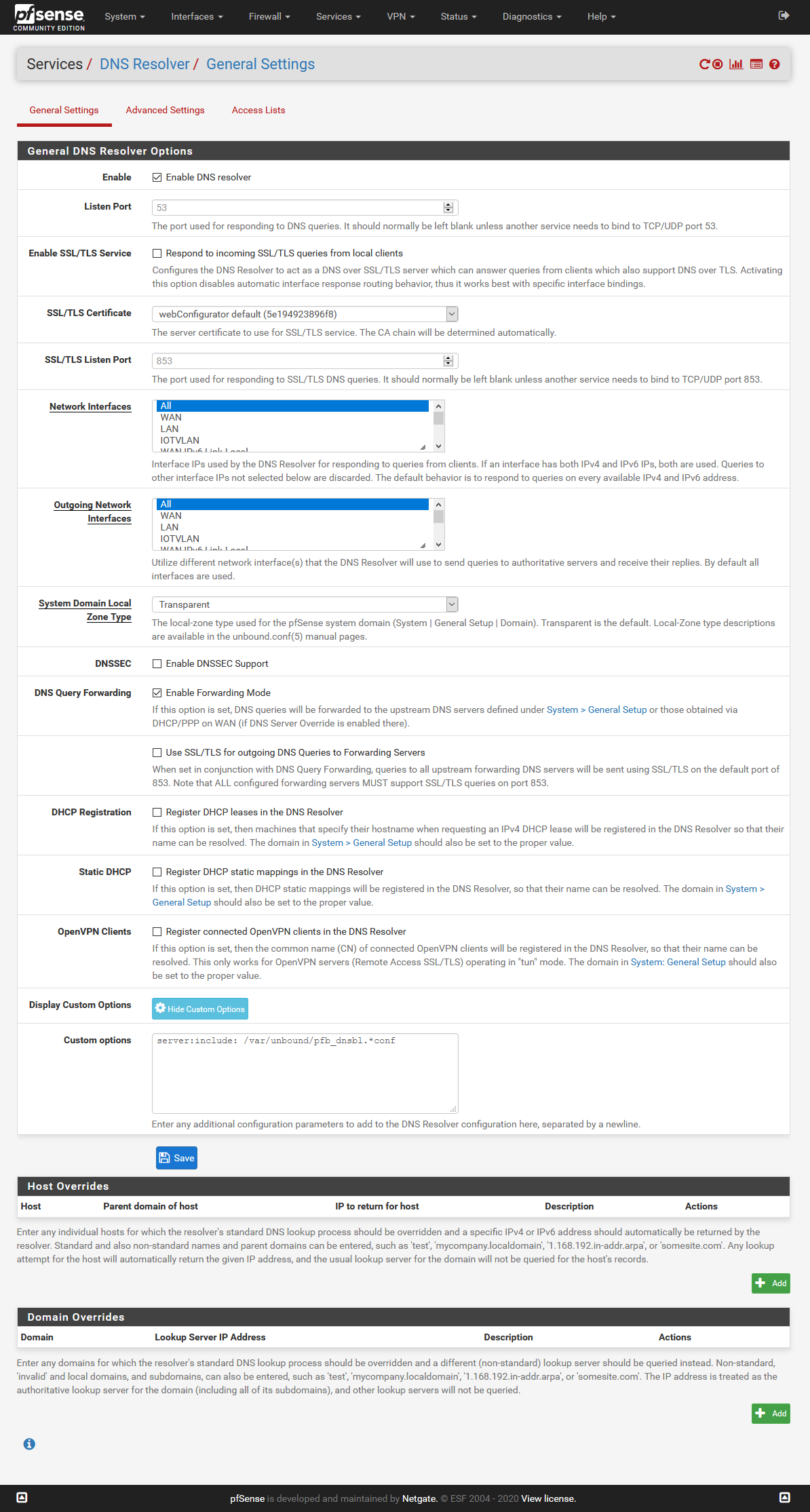
Now I enabled DNS-BL back and download from google play store is blocked back again in IOTVLAN as well as LANHere is my DNS Resolver settings..
This is a learning process for me as I am new to the pfsense.
Thanks
Andy -
That setting only selects where to add firewall rules which DNS-BL will add for any IPs in the lists. The main purpose of DNS-BL though is to add lists to the DNS resolver to prevent it resolving bad fqdns. Mostly ad sites and malware but could be anything in the lists. Those apply to Unbound which all interfaces use identically.
By checking 'TLD' you also block any subdomains of listed domains from being resolved.One of you lists has a domain in it that is required by the play store and it cannot be resolved. I would expect it to show in the alerts though where it would show which list contains the domain.
Steve
-
Steve,
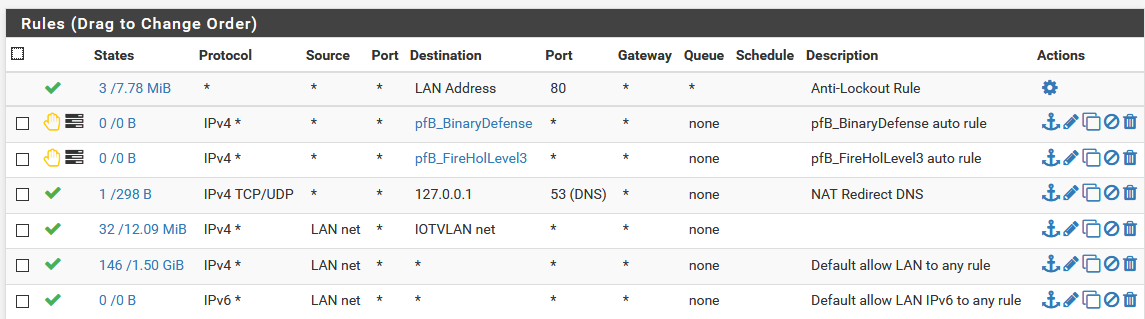
I see the following in the alerts:
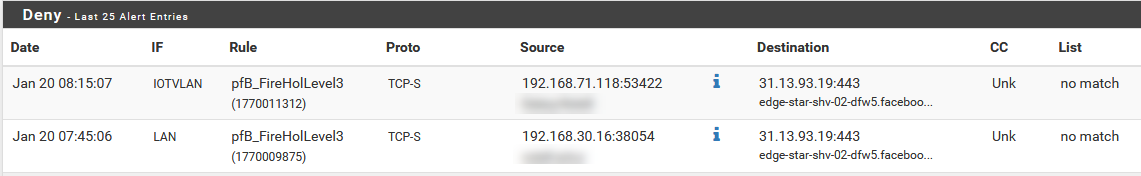
I think the offending list is FireHoLevel3? I don't know if denied list is for the Google play..
But this is the first time something showed up in the Deny list.. I was watching it since you mentioned about it.
Do you want me to disable that list and see if it makes any difference?
Do I have to run update manually after disabling this list OR it is just a time game?Thanks
Andy -
I have disabled the FireHoLevel3 and Reload all with no avail
-
Mmm, unlikely access to facebook would be required for Google Play.
One of those lists is the issue. If it comes to it disable them one at a time until you find it.
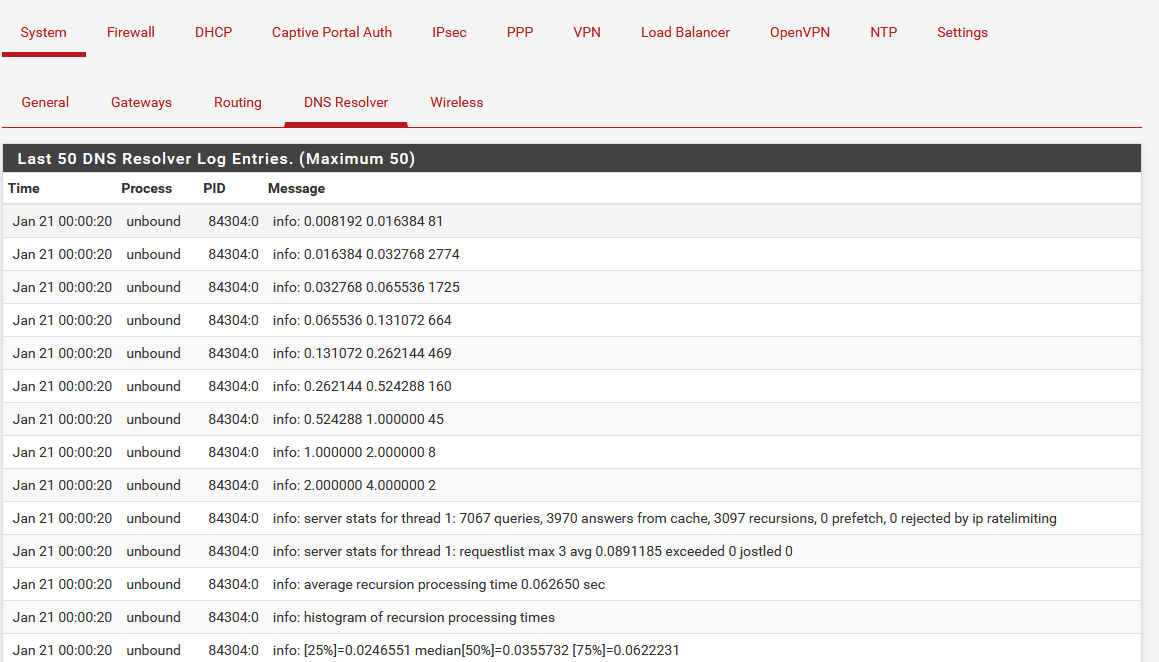
You could try turning up the logging in Unbound to query level then filter the resolver logs by IP of the host trying to connect.
Looks for urls resolving the 10.10.10.1. If you find them you can create a whitelist in pfBlocker to allow them to resolve correctly.Steve
-
Steve,
How can I turn up the logging to query. This was the option I am looking for so that I can query each host real-time and see what is being blocked.
Also How can I see filter resolver logs? what I see is just this in system logs:Here are pfblocker logs
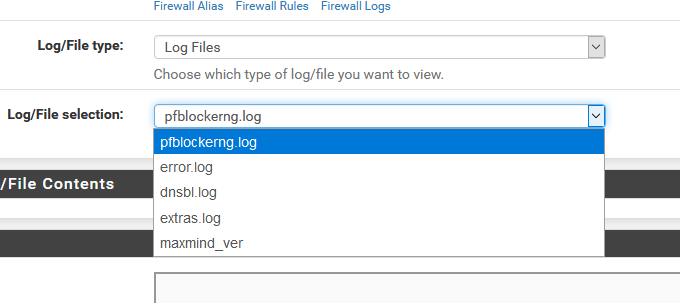
Here are system logs for Resolver
-
In the Unbound Advanced Settings:
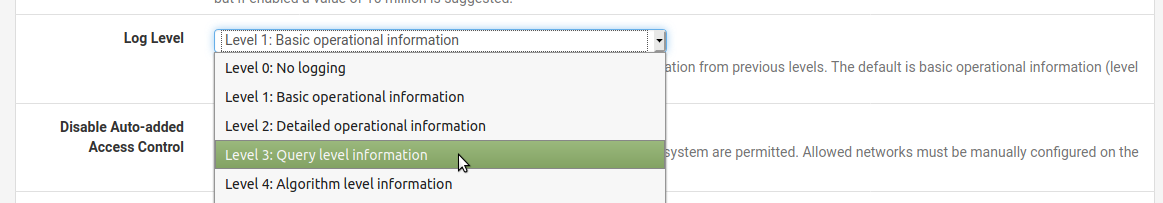
The logs will get VERY busy when you enable that so you will need to check them immediately after trying to connect.
Steve