Suricata is blocking LAN and WAN IPs
-
@bob-dig yes, the _3 version doesn't have any fix for this problem. Later in the day I'll try the new binary for bmeeks and in a day I'll post back here the results
-
@bmeeks said in Suricata is blocking LAN and WAN IPs:
I noticed in your previously posted logs that some firewall interface IPs were logged as changing. It looked like maybe an interface cycled, or perhaps it's a VPN tunnel coming up and down ???
I looked at my log and there where some changes but concerning 192.168.1.* I can't see a problem.
2/10/2021 -- 07:02:56 - <Info> -- alert-pf -> adding firewall interface hn1 IPv4 address 192.168.1.1 to automatic interface IP Pass List. 2/10/2021 -- 07:02:56 - <Info> -- alert-pf -> Added IPv4 address 192.168.1.0/24 from assigned Pass List. 2/10/2021 -- 07:10:04 - <Info> -- alert-pf -> deleted address 192.168.1.1 from automatic firewall interface IP Pass List. 2/10/2021 -- 07:10:04 - <Info> -- alert-pf -> Received notification of IP address change on interface hn1. 2/10/2021 -- 07:10:04 - <Info> -- alert-pf -> added address 192.168.1.1 to automatic firewall interface IP Pass List.I have to run those cron jobs on a daily bases:
2 7 * * * root /usr/bin/nice -n20 /etc/rc.reboot 4 7 * * * root /usr/bin/nice -n20 /etc/rc.dyndns.update 8 7 * * * root /usr/bin/nice -n20 /etc/rc.reload_allPS: Running it on WAN seems to work for now, tomorrow I will know more...
-
-
@xm4rcell0x said in Suricata is blocking LAN and WAN IPs:
@bmeeks bad news




Well, crap! I guess it's back to pondering what could be going on. I really thought that change might do it. I so wish I could duplicate this on my test systems. Then I could identify the root cause and fix it instead of having to guess what may be happening.
There just must be something weird going on in Suricata's Radix Tree code, or else I am using that utility code improperly. The documentation on it is sparse.
I think I will try abandoning the Radix Tree and work on copying code over from the Snort binary package. That will take me a bit to get done and tested as not all the same supporting routines that exist in the Snort binary are present in the Suricata binary.
-
@bmeeks For me, I don't run snort because it has no Block On DROP Only mode.
-
@bob-dig me too.
It's such a big feature in suricata !
@bmeeks can it be implemented in snort package? -
@xm4rcell0x said in Suricata is blocking LAN and WAN IPs:
@bob-dig me too.
It's such a big feature in suricata !
@bmeeks can it be implemented in snort package?No, because at the API hook where the custom output plugin gets called by the parent binary, Snort does not make the rule action available to test. Plus, Snort only updates its internal "drop" variables when true inline IPS mode operation is enabled in the Snort DAQ. So the short answer is "no", Snort cannot implement a "block on DROP only" option when using Legacy Mode blocking. The Snort binary is just not plumbed up the same as Suricata.
-
@bmeeks ok, and what do you think about the "checksum offload" ? Disabling it seems has resolved the OP's problem. @Bob-Dig do you have this option enabled?
-
@xm4rcell0x said in Suricata is blocking LAN and WAN IPs:
@Bob-Dig do you have this option enabled?
Yes,tried both, didn't changed anything.
-
@bmeeks
I don't know why but I've tried to unlock my internal IP, but before that i have changed the Drop action from Drop to Alert.
Cleared the Block Table, restarted suricata on the LAN interface , but it continues to trigger the Drop action instead if the Alert one, so i have uninstalled Suricata (i've followed your instructions)Now i would a fresh install but there are some files in
usr/local/etc/suricata usr/local/etc/snort /suricata-6.0.3_2.txz /root/suricata-6.0.3_2.txz(also see the email)
How can i remove these files and folders ? I'm not a linux guy but i know there is the "remove" command, but i don't want to mess anything, that's my production environment.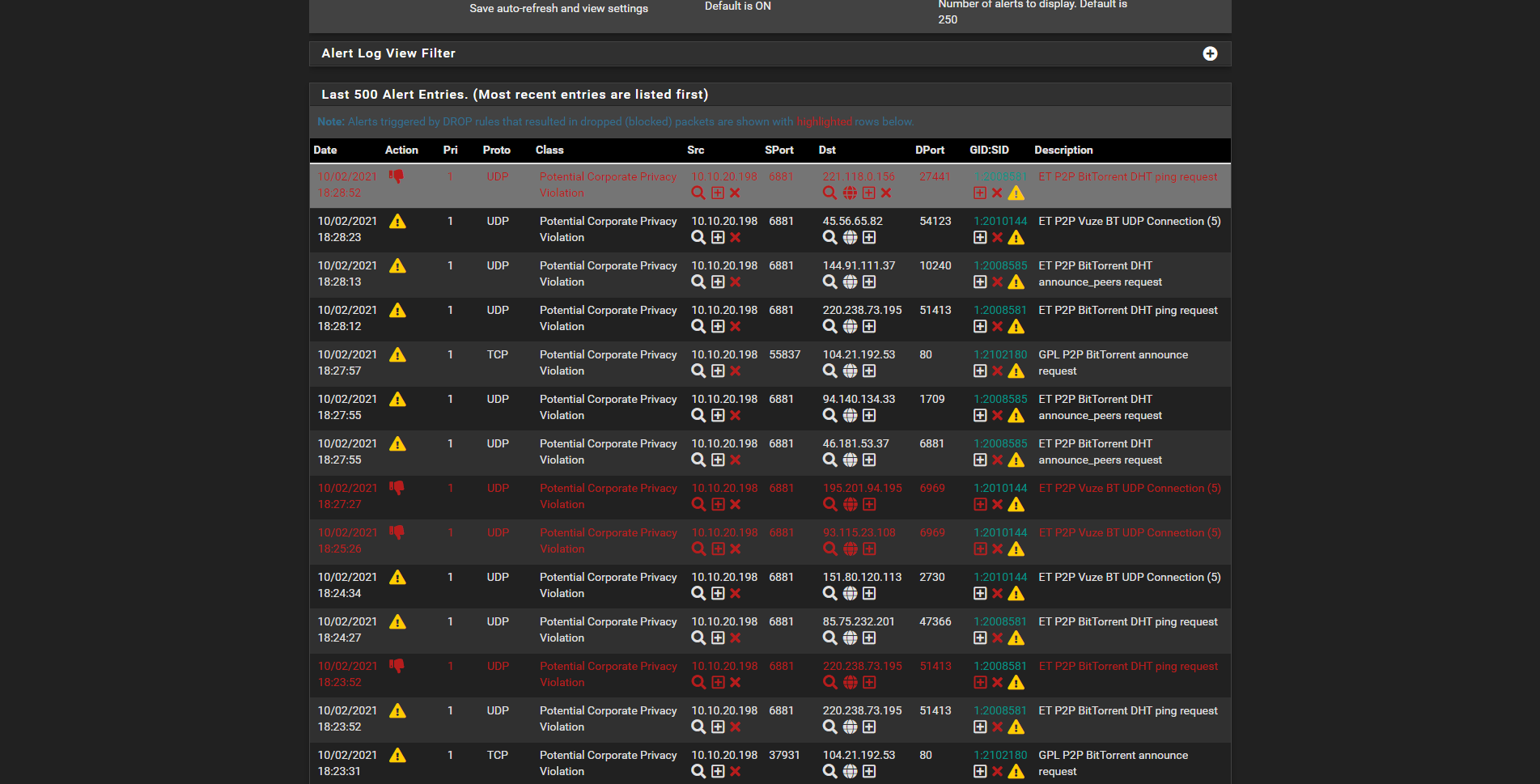
As you can see, on the right corner there the Alert action selected, but on the left for some rules it is still on the Drop action (already tried to change from that corner).
-
@xm4rcell0x said in Suricata is blocking LAN and WAN IPs:
@bmeeks ok, and what do you think about the "checksum offload" ? Disabling it seems has resolved the OP's problem. @Bob-Dig do you have this option enabled?
All of the hardware options for checksum offloading, TCP Segmentation, and Large Receive should be disabled. Check the corresponding boxes under SYSTEM > ADVANCED > Networking in the pfSense menu. I belive a reboot is required for all of those changes to become effective.
-
@xm4rcell0x said in Suricata is blocking LAN and WAN IPs:
@bmeeks
I don't know why but I've tried to unlock my internal IP, but before that i have changed the Drop action from Drop to Alert.
Cleared the Block Table, restarted suricata on the LAN interface , but it continues to trigger the Drop action instead if the Alert one, so i have uninstalled Suricata (i've followed your instructions)Now i would a fresh install but there are some files in
usr/local/etc/suricata usr/local/etc/snort /suricata-6.0.3_2.txz /root/suricata-6.0.3_2.txz(also see the email)
How can i remove these files and folders ? I'm not a linux guy but i know there is the "remove" command, but i don't want to mess anything, that's my production environment.
As you can see, on the right corner there the Alert action selected, but on the left for some rules it is still on the Drop action (already tried to change from that corner).
I sent you a reply via email about removing the files. They are harmless, but removing them is easy. See the email I sent.
For your DROP versus ALERT problem, how did you initially change the rule or rules to DROP? Did you use SID MGMT, or did you click the icon on the ALERTS tab or on the RULES tab when listing the contents of that category? Whichever of those methods you used, simply reverse the process.
On the RULES tab, when listing the contents of a category, there is a reset-to-defaults button that will restore all the rules in the currently selected category to the rule vendor's defaults. That would mean all the rules in the category would be reset to ALERT. If you don't want to do that, go find the SID in question in the list and click the icon under the Action column. In the pop-up dialog, choose the option to restore the default action. Then click Save. Back on the RULES tab, click Apply to send the change to the running Suricata process.
-
@bmeeks thank you for the email :)
I have changed from the Alert tab, i usually don't change the values from the Rules tab.
If I can help you in any way, let me know Bill! -
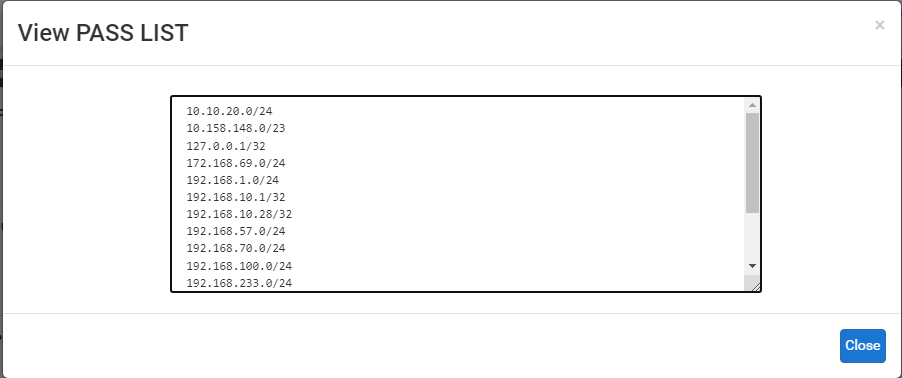
I'm sorry, but I just absolutely cannot duplicate this issue. I've cloned your firewall as closely as possible by including every single IPv4 subnet you have listed in your Pass List. I created 4 interfaces on a virtual machine. I assigned all of your IP subnets to either physical ports on the virtual machine or VLANs defined on a port.
Here is the Pass List I'm using on my test virtual machine. Notice that it explicitly lists the 10.10.20.0/24 subnet which you say is your LAN. I have that IP subnet configured on a firewall interface. The firewall is 10.10.20.1, and I have a Kali Linux virtual machine on the same virtual network at 10.10.20.198 duplicating the IP address of your blocked LAN host.
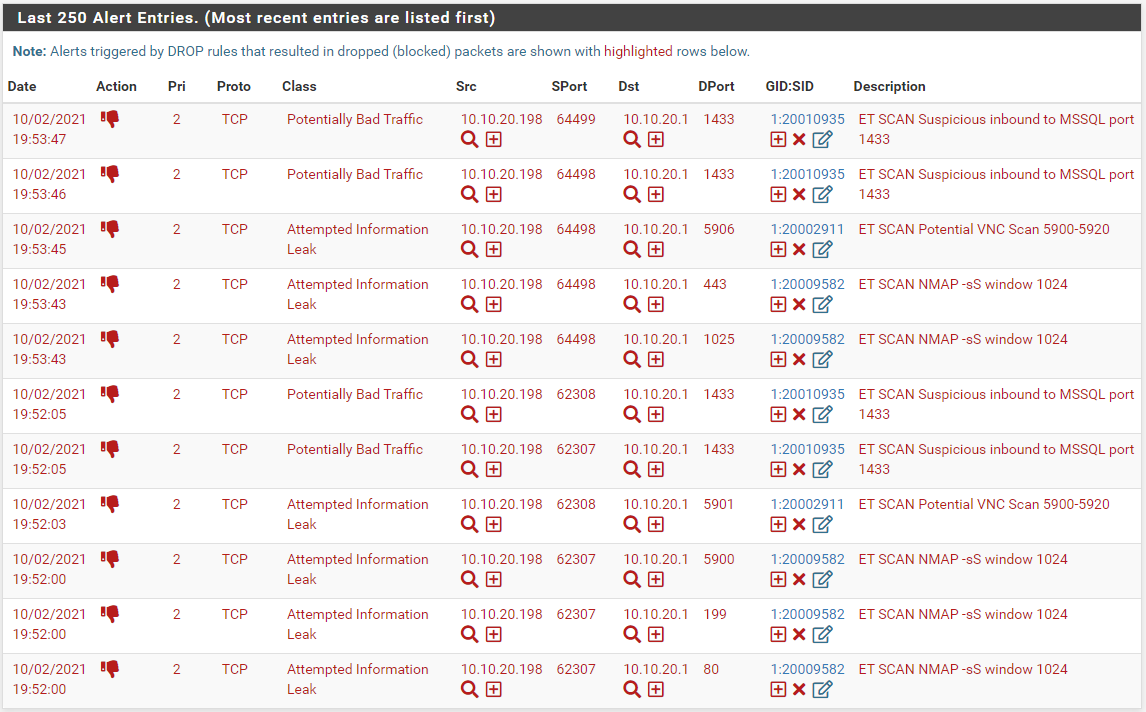
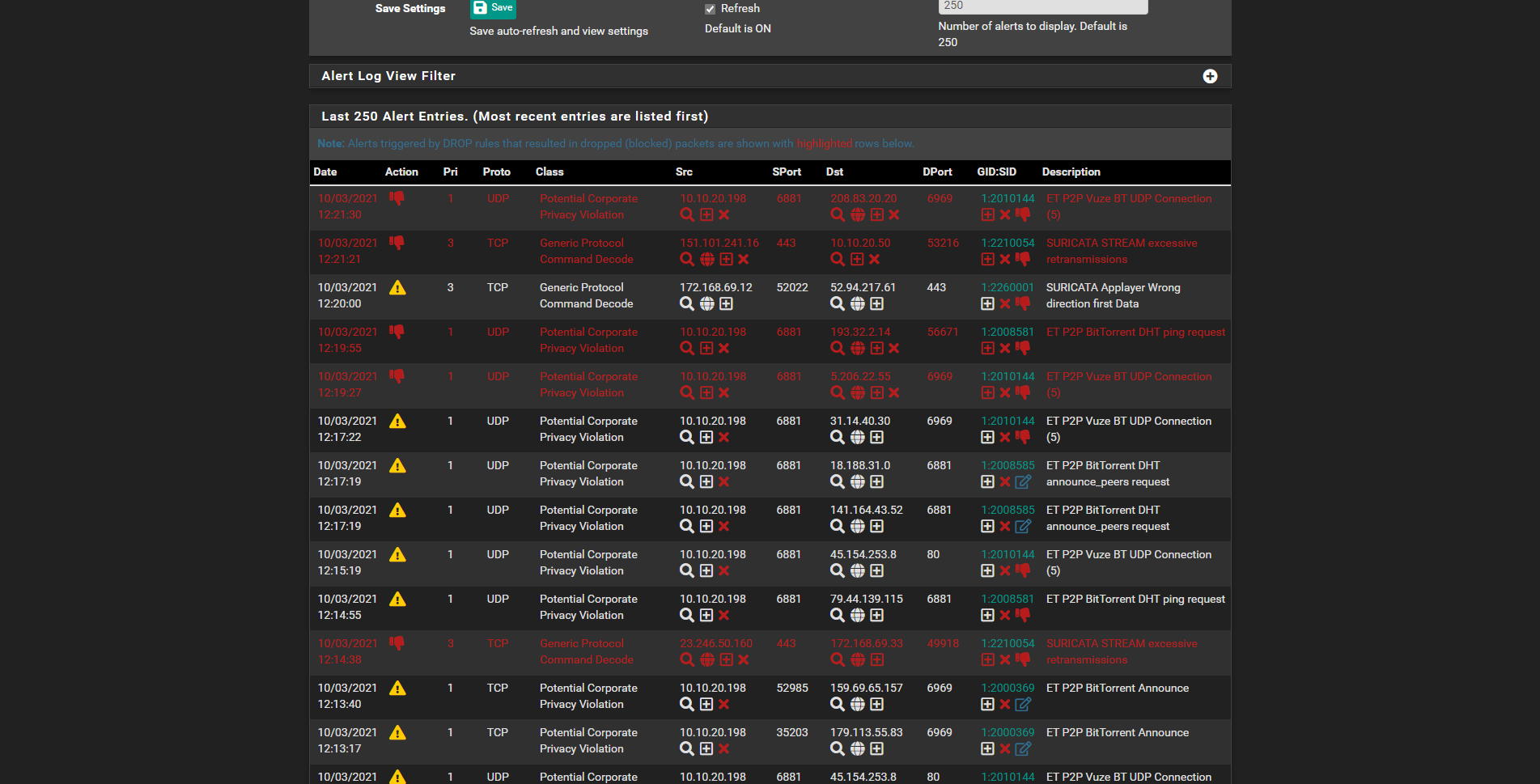
I have the ET Scan rules enabled with some of them set to DROP. Here are the alerts generated by an nmap scan of the firewall's LAN interface (the 10.10.20.1 IP address) from that Kali Linux machine at IP 10.10.20.198.
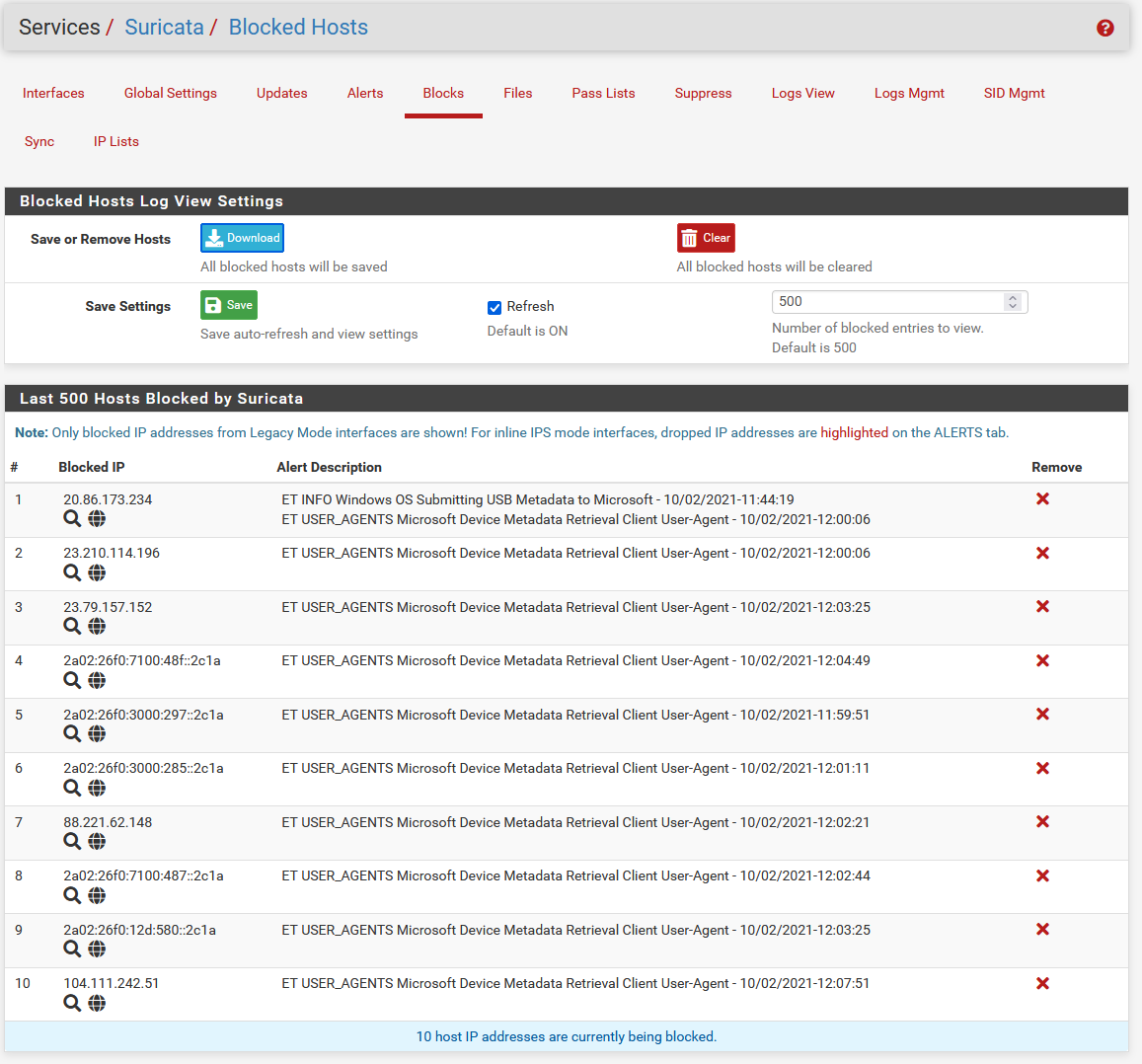
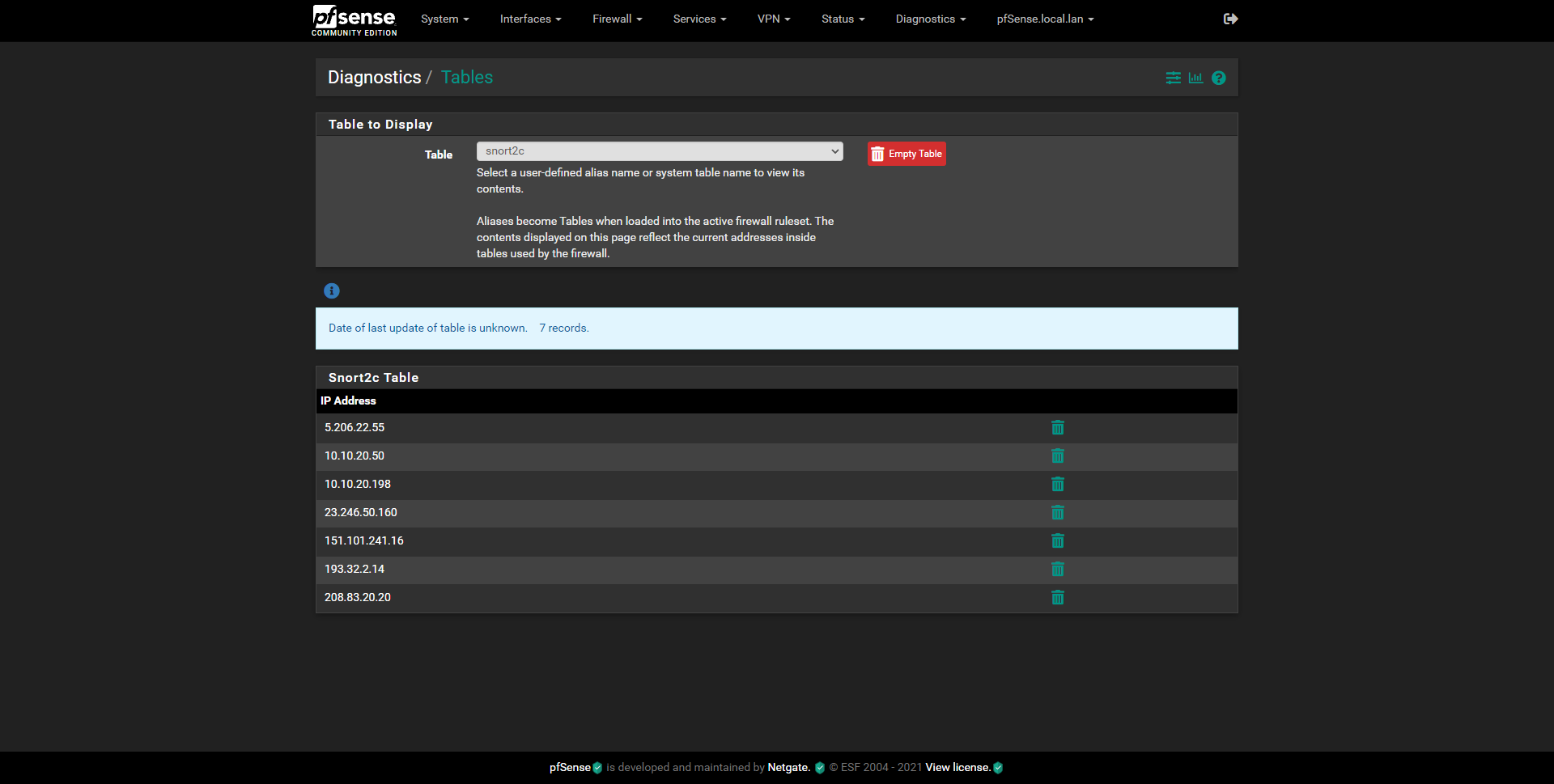
I received no block of the Kali Linux host at IP 10.10.20.198. Here is the BLOCKS tab after running the scan (and generating the alerts shown above).
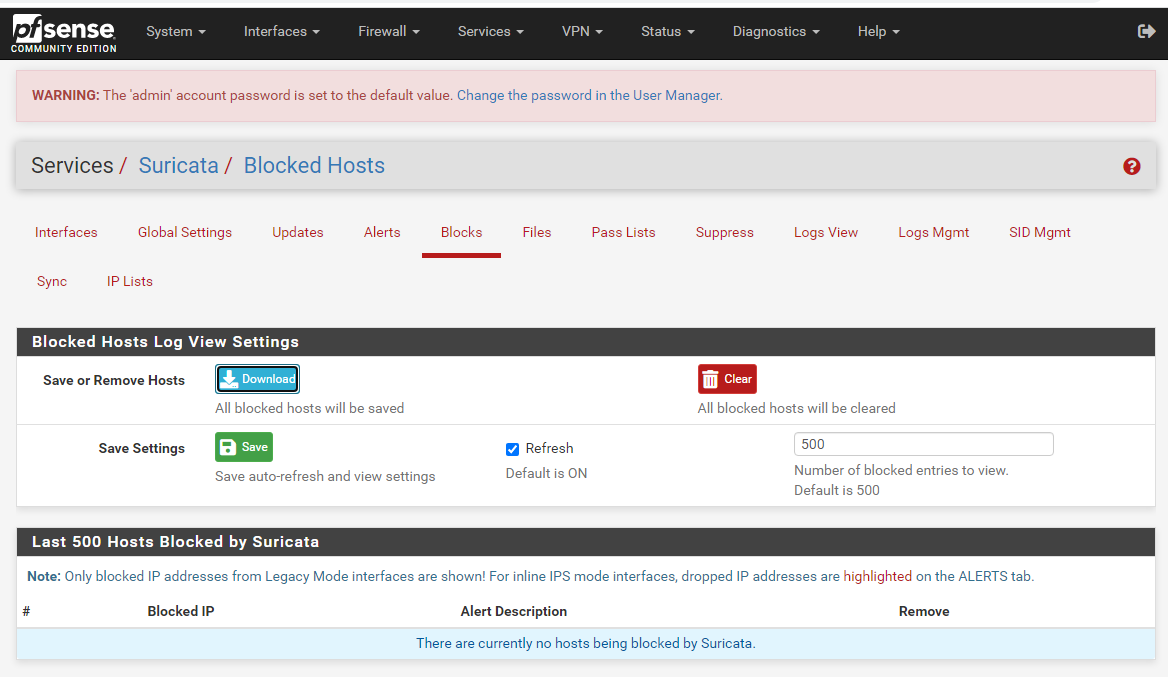
As you see, the Kali Linux host is not being blocked. This is expected as its IP address is within the subnet 10.10.20.0/24 defined in the Pass List.
The direction of traffic will not matter, meaning it is not material whether the LAN host is the source of the traffic, or the destination of the traffic. The blocking plugin simply looks at the IP address in the packet. But just to be sure, I tested three times with the Which IP to Block parameter set to each possible value (SRC, DST, BOTH). They all worked properly. The LAN host was not blocked.
-
Another test for you to try for me. What kind of machine is that 10.10.20.198 host? Is it just a workstation -- perhaps Windows?
If so, and you can access a COMMAND prompt on that PC, I want to run this test.
- Go to the RULES tab for the LAN interface in the Suricata GUI on the firewall.
- In the Category drop-down, choose "custom.rules".
- In the blank textbox that opens, copy and paste in this simple rule:
drop icmp any any -> $HOME_NET any (msg:"Test drop of icmp-request"; flow:to_server; classtype:bad-unknown; sid:20010936; rev:1;)- Click Save when you are done.
- Back on the INTERFACES tab in Suricata, restart the LAN instance (I am assuming that is the 10.10.20.0/24 interface).
- Clear the BLOCKS tab in Suricata.
- Now go to that 10.10.20.198 host, and in a COMMAND prompt window type:
ping 10.10.20.1or whatever the firewall's LAN IP address is. The idea is to ping the firewall's LAN interface from a host on the LAN to trigger the custom DROP rule.
Check if the host is immediately blocked, or if the first ping succeeds. I would like to establish if it takes some time for the IP to get blocked when triggering DROP rules, or if it gets blocked immediately.
If you can't use the 10.10.20.198 host, then any other host on that network will work as well.
-
I did have one other idea pop into my head after my previous posts above. There is one more place in the custom blocking plugin code I just found where I think some random data could cause the errant blocks.
I am creating an additional "fix" I would like for you to test same as you did the first time. Check your email for another test binary package arriving soon. I will include the installation instructions again in the email.
Thanks
-
@bmeeks Interestingly for me the problem is not occurring if I run those rules on the WAN-Interface with Suricata. Also please note that in my case the "offender" is a local Windows, as those rules are privacy-focused rules and not against attacks from outside.
So maybe this is part of the problem in my case.1:2025275 emerging-info.rules drop http $HOME_NET any -> $EXTERNAL_NET any (msg:"ET INFO Windows OS Submitting USB Metadata to Microsoft"1:2027390 emerging-user_agents.rules drop http $HOME_NET any -> $EXTERNAL_NET any (msg:"ET USER_AGENTS Microsoft Device Metadata Retrieval Client User-Agent";You can trigger those if you (re-)connect a bluetooth device to Windows.
-
@bob-dig me too, on the WAN side no problem at all.
I'm testing the newer binary from @bmeeks and i have some news.
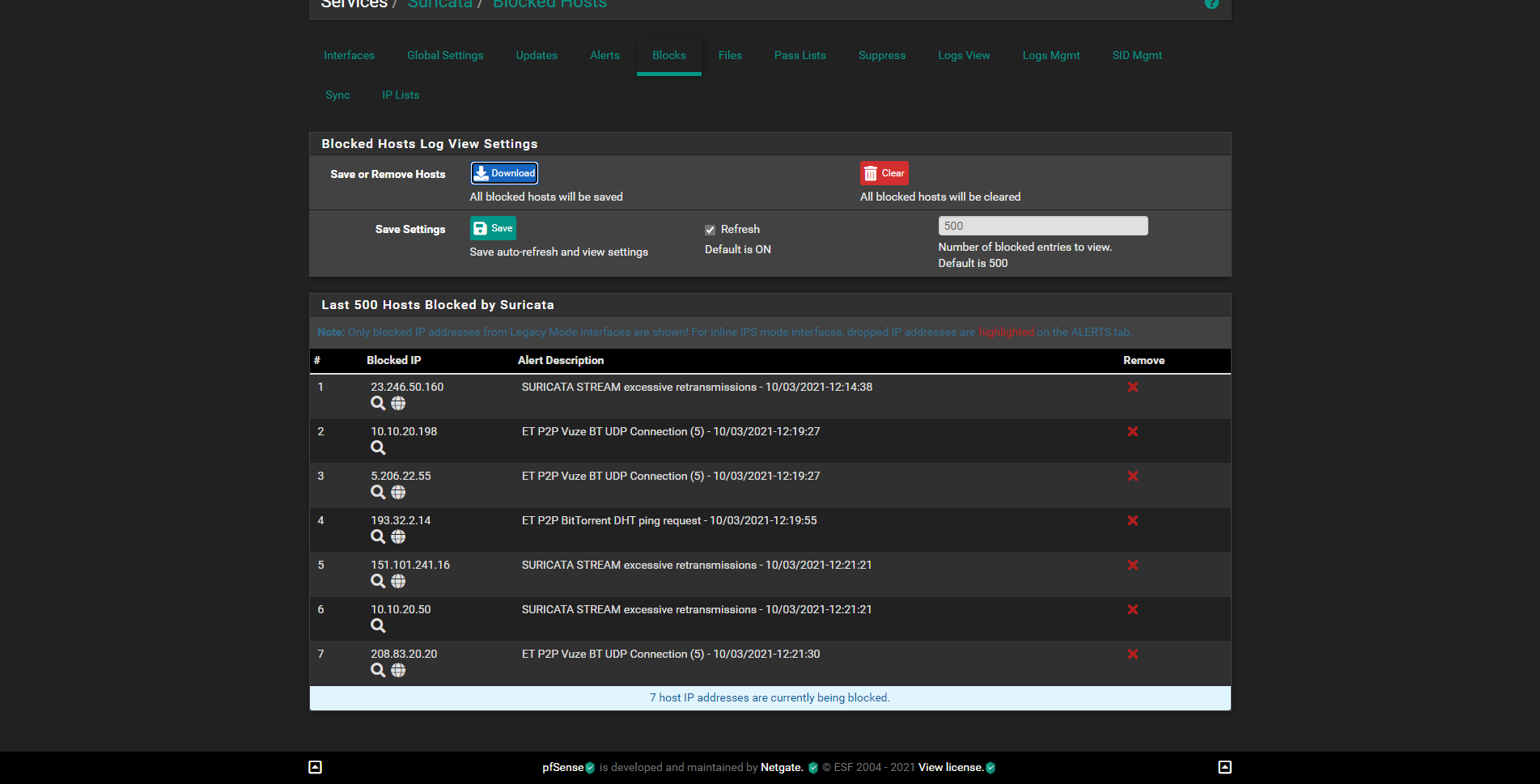
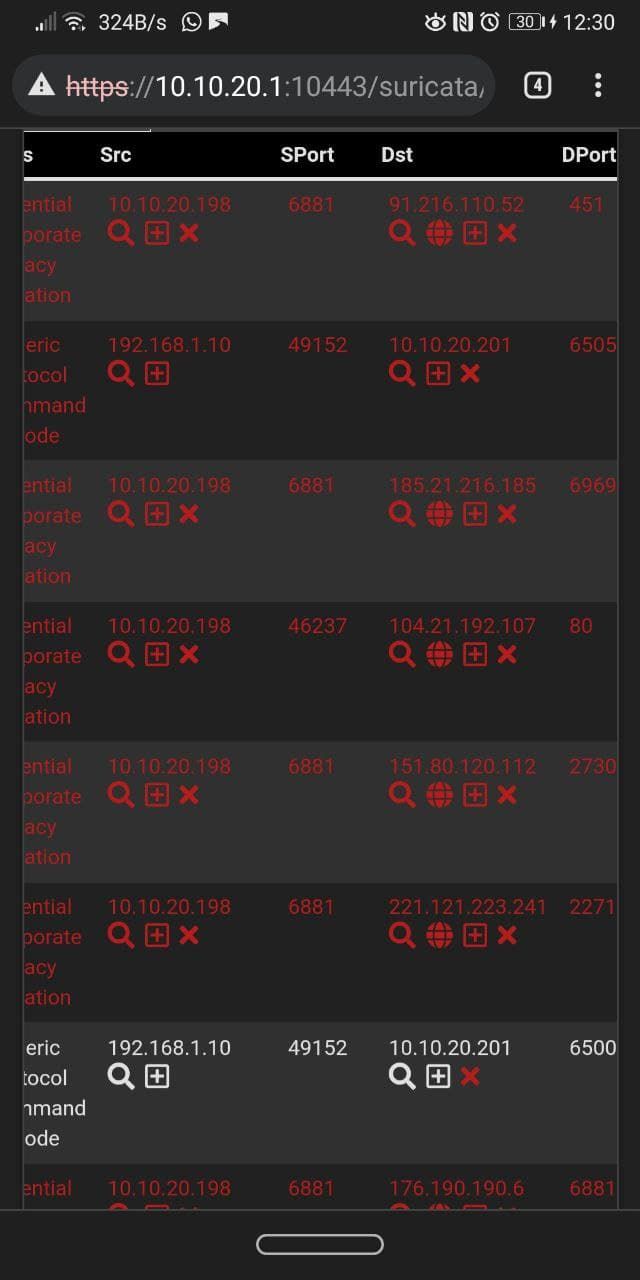
Suricata only blocks the parent interface's IPs, so in my case the subnet 10.10.20.0/24, but not the VLAN on that interface as you can see in the screenshot.
I have also tried to Drop a Rule where the Src is 192.168.1.10 (igb0 interface, that's my ISP modem) and the destination is 10.10.20.201 (my desktop), 192.168.1.10 wasn't blocked.
That's another rule, where the VLAN 69 (an IOT device, ip: 172.168.69.33) wasn't blocked by suricata.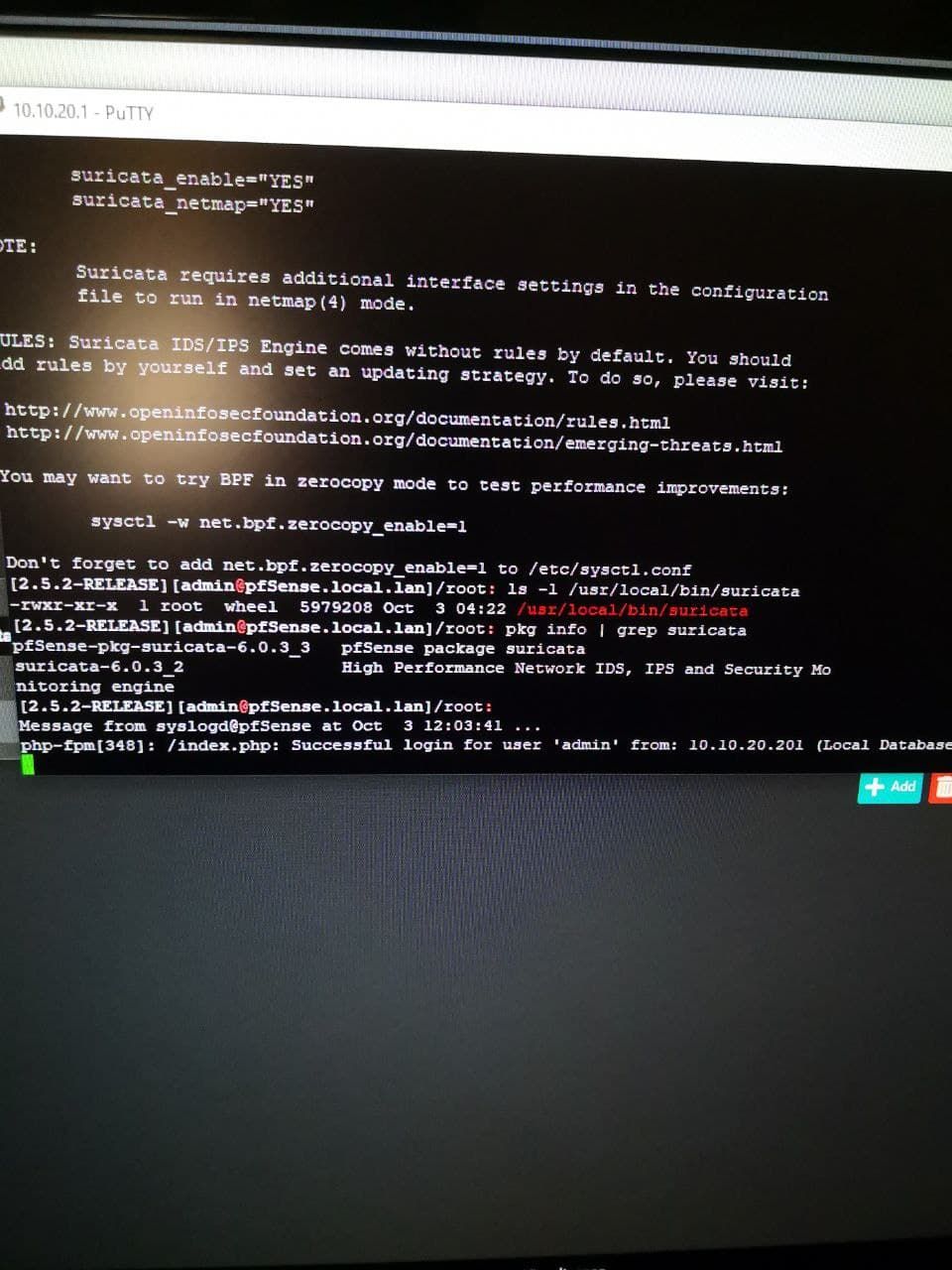

-
@xm4rcell0x Thanks. Kinda the same here, I only noticed it on parent interface or interface without vlans. But also could be a coincidence.
-
@bob-dig said in Suricata is blocking LAN and WAN IPs:
@bmeeks Interestingly for me the problem is not occurring if I run those rules on the WAN-Interface with Suricata. Also please note that in my case the "offender" is a local Windows, as those rules are privacy-focused rules and not against attacks from outside.
So maybe this is part of the problem in my case.1:2025275 emerging-info.rules drop http $HOME_NET any -> $EXTERNAL_NET any (msg:"ET INFO Windows OS Submitting USB Metadata to Microsoft"1:2027390 emerging-user_agents.rules drop http $HOME_NET any -> $EXTERNAL_NET any (msg:"ET USER_AGENTS Microsoft Device Metadata Retrieval Client User-Agent";You can trigger those if you (re-)connect a bluetooth device to Windows.
The type of rule and the direction of traffic flow have no significance. What is happening is that when the IP addresses from the rule are compared to the IPs and subnets stored in the Pass List Radix Tree, the comparison seems to fail for you. I don't know why, because it does not fail for me. When the comparison fails, the blocking code thinks the IP address is not in the Pass List and thus blocks it. That's the problem. At the point this decision is made in the code, it is not looking at anything other than the IP address. Nothing else.