Can the SG-3100 work as a hand off firewall to the same WAN?
-
I've got several servers in a colo facility where I only needed a switch. Trouble makers got IP banned in the web server and we only had to ban all IPs from China and Russia a few times in the past.
Lately, we've gotten huge spikes in traffic from port scanning and UDP floods. I never noticed because we're locked down and it didn't show up in the web logs, but my ISP didn't like it.
Apache status would give us 30 plus requests and peaks of 100 or more. Over time a couple hundred waiting slots is not rare.
So, is the 3100 robust enough and will pfSense do what I need?
Thank you
-
@testflight Well, if your isp doesn't like the udp traffic, there is nothing you can do to stop it at your perimeter. Even if you drop it, it will reach you.
Pfsense IS robust, and any decent hardware is also robust.
However, there is no one size fits all solution, and certainly, depending on the technique ddos is done, there are no guarantees that any device will cope with it.On the other hand, adding a firewall in front would definitely ease some load from the servers.
What kind of traffic are you dealing with? -
Traffic spikes are often crazy. A 2 minutes and 44 second tcpdump shows 187,516 requests and replies. UDP entries amount to 128,499, 68%, 783/second. One IP generated 103,264. Roughly 60,000 entries are normal web traffic to ports 80 or 443.
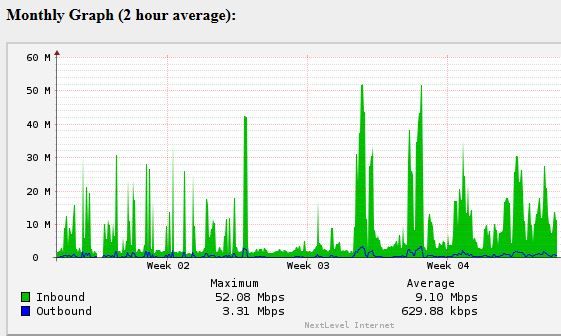
You can see the spikes. Normal traffic is using 3-5Mbps. These UDP scans push it way up as one request gets a 1K response which is the 50 Mbps spikes.
Thank you for the reply. I assume that setting up the SG-3100 for the LAN to be on the same subnet as the WAN is not a problem.
-
Your colo facility doesn't offer up any firewall or perimeter solutions for this kind of stuff?
Jeff
-
Yeah, I offered to pay a bit more. Their concern was unintended consequences that might affect other customers doing VOIP or video chat or what not. I'll pick up an SG-3100 and hope it will do the trick.