adding link to my shop
-
I hope this is the proper sub-group.
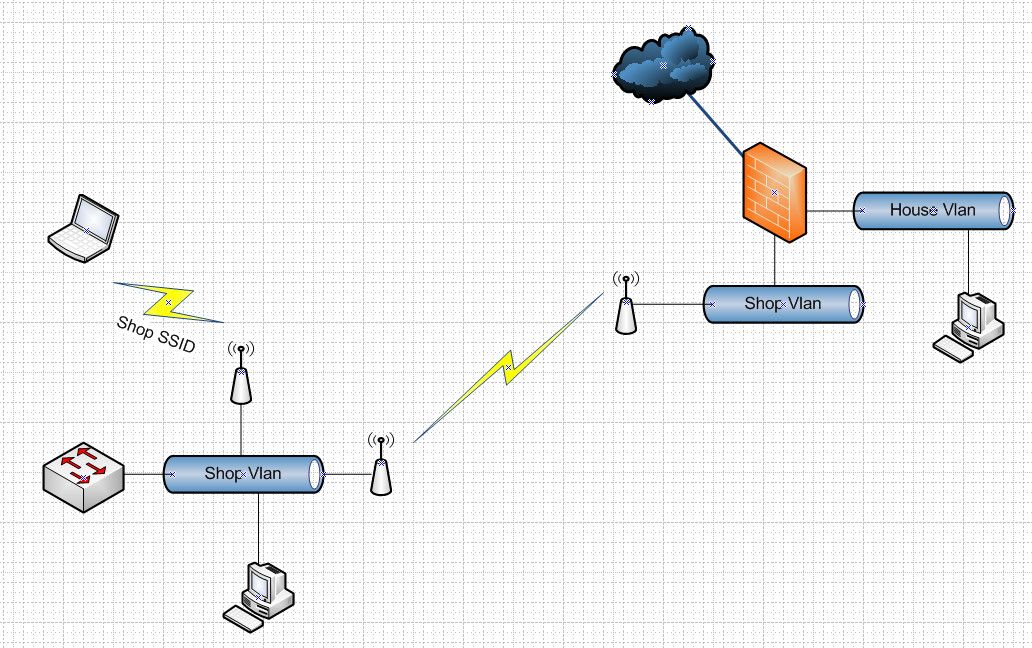
I would like to get internet from my house over to my shop. I want the shope to be separated, VLAN is fine, from my home LAN and have its own router/WAP to handle the computers, etc in the shop. Double NATting is OK as it is mainly just web stuff. Today I have my LAN and two VLANs setup.
I plan to use two Ubiquiti Nano Beam antenna connected to one of the 4 ports on my pfsense box.
In the shop I want to use install an off the shelf router, where I can setup VLANs, and a DHCP server for everything in the shop.
I would know how to do this if I were to just create a new VLAN, but I want the local router to handle the shop devices. Can I just create the VLAN, and hook the router to it?
Essentially I want to get internet to the shop, but have the shop completely separated from the house behind its own router.
If double NATting is an issue I can buy another IP from my ISP, but would have to figure out how to get pfsense to handle that. I could put a switch in front of the router and plug the switch into two of the router ports and have two WAN gateways. Though there is probably a way to do that switching internal to pfsense?
Buying a separate ISP connection and installing fiber to the shop is an expensive proposition when compared to the ~$200 for the nano beams.
hopefully this makes sense, I"m open to ideas/suggestions.
david -
for as much sense as it makes, and assuming "shop" is connected with ethernet, then things are very simple.
Forget everything about vlans, double natting, local routers etc.
You dont need any of these, it just makes things complicated.What you need is 3 Lan interfaces.
One for your home
One for your shop
and one for the wifi feed
Three different subnets, assigned to each one, dhcp server on pf configured to lease ip's accordingly, rules not permitting traffic between interfaces, and nat for all three ranges for internet accessIf you need vlans for cabling reasons, or second wan ip for security is another story and can be added, but its rather irrelevant to the basic setup.
-
Currently I have a T1 line at the shop. It is really slow, and honestly struggles even web browsing now. Don't even think about downloading windows updates . . . but it is reliable. Often a truck has rolled to fix the problem before I even know there was one.
I has a WISP at my home and it was faster, but unreliable. Now that I just got fiber at the house, I thought I could just hook up a link to the shop, bring it in as a separate WAN for the existing setup at the shop, plug and play. If every thing works well for a few months, I may look into getting fiber to the shop. Or if it works really well, just keep it and skip the extra fees for a dedicated line, installation etc.
That was my reasoning for keeping the router at the shop. It already has my VLANs setup and running etc. I was hoping to just add another "WAN" connection
david
-
@lovingHDTV said in adding link to my shop:
Currently I have a T1 line at the shop. It is really slow,
That is the understatement of the week for sure ;)
If you have a pfsense in your house, you don't really even need a router in your shop.. Just need a switch, or an AP or both.. Your shop would just become another vlan off your house pfsense. Your wireless bridge setup is just a long wire over wifi.
Or sure you could use just some soho wifi router as AP to provide switch ports and wifi in your shop.
-
What is the distannce between shop and house?
-
With the nano beams your talking KM range so not sure that would be an issue ;) Line of site could be a problem.
BTW - example setup
-
I completely missed the nanobeams part...
Yes, line of sight is the issue.
If you have fiber then it would be faster to access the internet over the nano and fiber connection
And then use the t1 as a backup...
So another pfsense at the shop, and gateway groups, for automatic failover.It depends what you really want to do
-
You really don't need any sort of smart switch or router in your shop even - as long as you just want everything in the shop to be on a "shop" network..
You could prob just cancel the T1 - I mean really its kind of useless in this day an age from a speed point of view.
-
@lovingHDTV said in adding link to my shop:
Currently I have a T1 line at the shop.
Ouch!!!
I remember when a T1 was considered fast, but those days are long gone. As mentioned by someone else, all you need ais a subnet and the means to connect it. I don't know how far your shop is or whether it's reachable over your own property, but there are a variety of ways. Fibre has been mentioned. If you have a couple of phone line pairs, you can use SHDSL to pass a few Mb and there's also point to point WiFi. There is some WiFi gear available that's designed just for that purpose.
-
The shop is about 1000 feet, and line of site is good enough. I went with the nano beams because they have great distance and are pretty cheap. There are some trees, but they are not dense enough to pose a problem.
The picture John posted is fairly accurate. For the interim I still want to have the T1 as a failover at the router in the shop. When everything is running nicely it will go away, saving me about $400 per month :)
Today at the shop my LAN and VLAN are the same setup as my house. That is what is confusing me, is there a way to setup this link to the shop and not have to redo everything in the shop?
For example. My house and shop are setup as LAN is 192.168.1.0, VLANs are 192.168.10.0 (IOT) and 192.168.20.0 (Guest). I'd like to not have to reconfigure my shop to something different, just provide a different internet feed.
Is this possible with the picture above?
thanks,
david -
@lovingHDTV said in adding link to my shop:
about $400 per month :)
For that kind of money, you can get fibre, running @ 1 GB and have lots of change left over. Where I live, 1 Gb over fibre is $114/month from my ISP.
-
OK I finally go the link between the two nano beams.
I run them through the ig2 interface on the router. I can ping the dishes from both sides, I can dhcp an IP from the router, from the router in the shop. so that part is working.
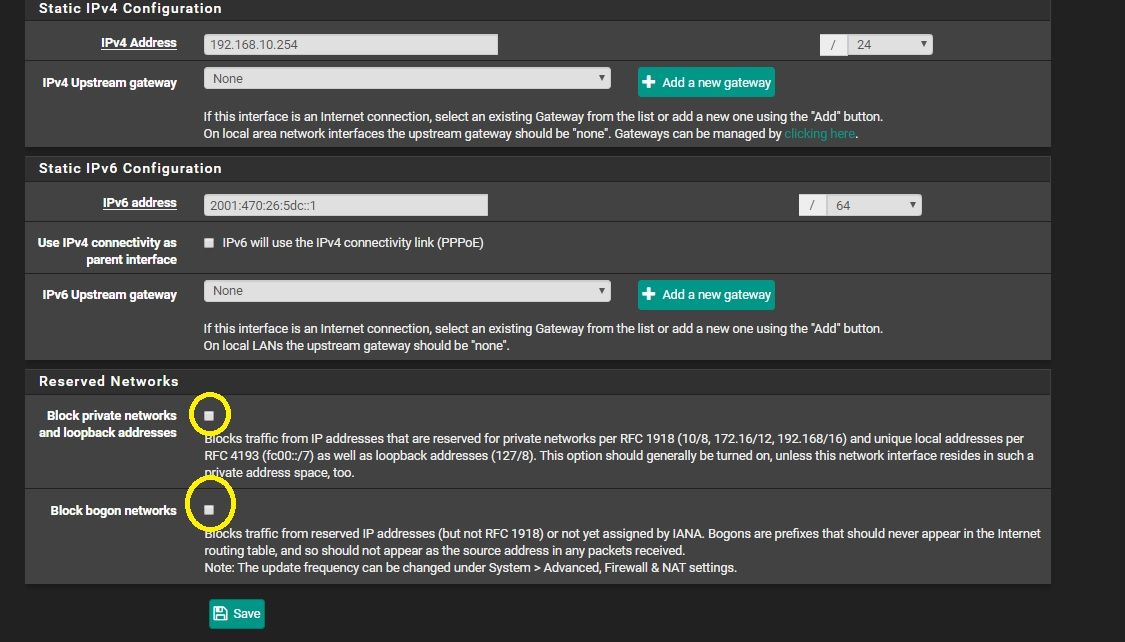
However I cannot ping anything outside the local network from the shop. I looked at my shop_link interface and the IPV4 gateway is set to none. I went to add a gateway, but my router gateway didn't show up.
It seems that I may need to add a gateway for the shop_link interface?
thanks,
david -
no IPv4 Upstream gateway must be none
you have to check firewall rules for that interface
out of the box only LAN is open and can go everywhere if you have a new interface like OPT you need to set the firewall rules yourself first
you can ping your own vlan network because the traffic is not passing through pfsense yet -
I can ping from my lan to the shop_link. I can ping all the nano beam dishes and the router in the shop, all 10.10.1.0/24 ip addresses.
In the shop I can ping the nano beam dishes, but I cannot ping anything else.
The only firewall rules for the shop_link are:
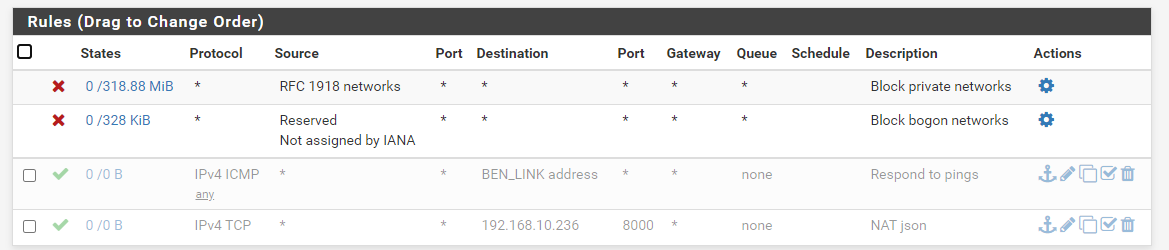
For my gateway interface I just see the port forwarding rules to get to my LAN services. There is nothing there for the shop_link.
Do I add rules to the shop_link interface or the gateway inteface?
thanks
david -
Well your shop firewall rules block everything.. So why would you think you could ping anything?
Why would you be blocking bogon? And blocking rfc1918 is going to prevent you from going to any of your other networks for sure.
-
the last 2 rules are disabled from what i can see
maybe start with a rule that permit any to any and see if it work
you can adjust it later eventually -
@johnpoz
These settings are just the defaults it gets created with. I didn't change any of them.I don't understand what the RFC 1918 or bogon networks are so I didn't change them.
At my shop I don't need access to my LAN, just to get to the internet.
david
-
Pfsense sure and the hell does not create rfc1918 or bogon block on a new lan interface.. Only if you made pfsense think this was a wan interface would it do that.. Which this is not to be honest.. it would be just a transit network to your other router.. Which you don't have or even need..
I even gave a drawing of how you would set this up..
-
@johnpoz
Interesting. i just added the new interface, named it, put in the static IP (10.10.1.1), setup a dhcp server for it.the block bogon and RFC1918 boxes come pre-checked, so I left them that way.
david
-
well anyway remove this from the interface