Device not getting IP from DHCP - VLAN miscoonfiguration or what?
-
I'm trying to have mobile phones in the home network get IP from different, isolated subnet of the network. It just doesn't work.
The LAN is 192.168.0.1/22. I created VLAN4 and made a virtual interface (VLAN_mobile) out of it with 192.168.5.1/24 and DHCP server running on it. I also addded two basic firewall rules to this interface (according to this video).
Obviously there is VLAN4 on the switch (TP-Link T1700G-28TQ) as well. VLAN4 has port 1 (tagged, because it's the one that plugs into the router, right?) and port 8 (untagged, where the wifi AP is connected) in them. I also changed the PVID of port 8 from 2 to 4.The main network VLAN is VLAN2 from which I removed port 8.
Here are screenshots of all the relevant settings I can think of: https://imgur.com/a/qpOFVox
The problem is the wifi AP (Netgear WNDR3700v4 running Openwrt) is not getting any IP at all.
Now I am a networking noob and all this is new to me and result of much trial and error and cursing, but all of the above seems correct to me after checking numerous sources.
Can anyone tell me whether I am misconfiguring the switch or something in pfSense, ore both?
I have no idea what else to try after three days. -
Becareful with TP-Link switches. Some models don't properly handle VLANs. If you're running multiple VLANs through a switch, you need a trunk port back to pfSense, which will pass all or at least specified VLANs.
Also, I didn't see any mention of configuring DHCP on the VLANs. You need to do that for each LAN interface in pfSense, including VLANs.
-
As far as I understand, trunk port is one that is member of multiple VLANs and which is used to connect to the router. That would be port1 in this case I believe, being member of the main VLAN2 and VLAN4 as well.
I specifically wrote I created a DHCP server for the virtual interface under LAN on pfSense so that shouldn't be a problem. -
This is on esxi? You need to set the vswitch in esxi that is connected to the physical interface that will have your vlans on it to 4095 if you don't want it stripping tags..
-
Oh? What the...

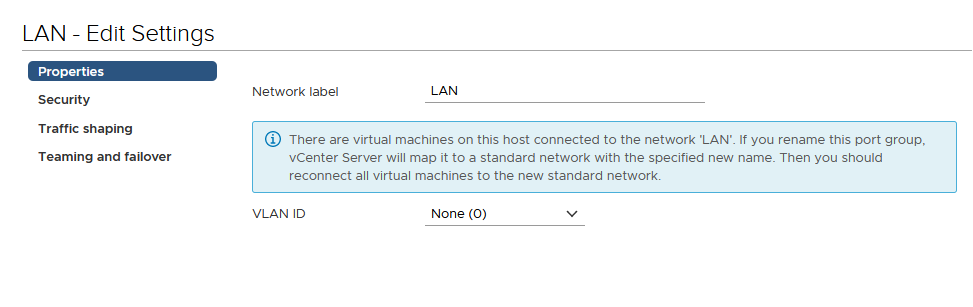
I guess this is explained somewhere, but it's definitely not something that'd cross my mind.We talking about this, right?
-
yes in esxi on your vswitch/port group if you do not set 4095 it will strip tags... Query VGT mode in the esxi docs.
There are 2 different ways to skin this cat with esxi... You can can let the vswitches/portgroups do the vlans for you - and then have multiple interfaces on your pfsense VM that will be in your different vlan port groups and will see traffic untagged. Or you can pass the tags to pfsense virtual interface vmx? and let pfsense handle the tagging.
-
I'll give that a shot once I'm back home.
I guess if you're not an ESXi expert you're done like me. I've spent several days on this crap and was ready to give up and return the switch.Which one of the two ways you suggest and why? Personally I like to keep things centralized or something, with as many relevant settings being done in one place as possible.
-
How you skin the cat is up to you.. Either way works.. All depends how you want to go about it. Do you want to dick with portgroups and vlans tags in esxi, or do you just want to do it all on pfsense and the switch.
Also comes down to how many physical interfaces you have in your esxi host, etc. And you might want to do a combination of VGT, EST or VST..
-
No idea what those acronyms stand for, but I only have two NICs in the server, WAN and LAN. It's just a small home server with no special needs.
I am a lot more familiar with pfSense now than I am with ESXi so I guess I'll be sticking with what I know badly instead of going trial and error again :D -
Virtual Switch Tagging (VST) External Switch Tagging (EST) Virtual Guest Tagging (VGT)Then just set 4095 as vlan ID in your vswitch/port group on esxi and it will pass the tags it gets to your guest (pfsense).
-
OMG IT WORKS!! Yes!!!
Thanks a TON. I specifically mentioned running ESXi everytime I asked on reddit and always got mostly just responses along the lines of "learn subnets, lean VLANs, blabla". -
What group were you in, were you asking in a specific esxi sub or pfsense? Anyone that uses esxi at all will understand this ;)
Glad you got it sorted!
Most of the VM software has their own way to dealing with vlan tags.. hyper-v does it differently - and shitty part of about that system is there is not gui to do it, you have to do it via a powershell command to do trunking, etc.
So when you asked elsewhere you specifically mentioned what you were doing on esxi? In your post here you make no mention of esxi... I saw the vmx in your screenshots, is only way anyone would know you were taking about VM on esxi host.
-
pfSense and homenetworking I think. But I thought virtualized pfSense was not that uncommon so someone would have an idea. Oh well.
Now I just need to figure out what kind of firewall rules for each interface should I have, or what rules are handy in general (like the guy the video I mentioned added DNS blocking rules for virtual interfaces, but this is outside of my expertise). -
@johnpoz said in Device not getting IP from DHCP - VLAN miscoonfiguration or what?:
Then just set 4095 as vlan ID
I thought 4095 was reserved and shouldn't be used.
-
It's not being used as tag.. Its what you set in esxi to let it know not to strip tags where you set the vlan id in the switch... It just puts it in a special trunk mode.. You don't actually use the tag anywhere else.
-
This post is deleted!