Harden security for outbound ports
-
Hello everyone,
I am looking to harden security for outbound traffic from my LAN to the internet and was wondering if maybe people on here could give me a little guidance. I have no problem learning and configuring myself, but would like to better understand how to do this from security standpoint.
As of now, I pretty much have no restrictions for outbound traffic. What can I do to change this? Would I use Floating Rules? If so, I assume I could set something that would allow well known ports out (0-1023)? I guess what I am trying to accomplish would be something similar to how a corporate office has their outbound ports locked down. Obviously http/https/NTP/DNS would be allowed. Do they have ports 0-1023 set to allow out, or only specific ports in that range (I don't have a mail server do 25 would be disabled)? Any guidance/advice given would be greatly appreciated, as I love how pfSense works...I would just like to learn more about it's capabilities. TIA
-
Hello!
The netgate docs are a great place to start.
https://docs.netgate.com/pfsense/en/latest/book/firewall/ingress-and-egress-filtering.html
John
-
So a thought as I am new to PFsense as well.. I have filtering between Vlans, but let all traffic out, but I run Suricata on top of this for IDS/IPS.. I think it is a good compromise unless you have specific requirements..
-
@serbus thanks for the link. I have read most of it and it has provided me with some great info which has allowed me to configure as needed. Still have some questions, however most I have been able to find online. Thanks again.
@Ssaven I am looking into that as well. I would prefer to only allow certain ports/IPs for outbound, however Suricata sounds great for monitoring. Thanks for your recommendation.
-
@simon_lefisch said in Harden security for outbound ports:
Do they have ports 0-1023 set to allow out
No they do not... Normally a corp setup would only allow the proxy direct outbound anyway.. And filtering would be done at the proxy for what websites. Ie normally block known malware, p0rn, etc.. inappropriate for the work place sort of stuff.
Anything that would allow direct access out, say something that won't work through the proxy would require special permission and setup to be excluded from proxy, etc.
To be honest this is mostly overkill for a home network.. Your mostly going to fixing shit that doesn't work because your accomplish what exactly? You do understand that pretty much anything you infect yourself with is just going to go out the normal allowed ports anyway ;) http/https..
While I applaud an attempt to learn.. Be prepared to be just causing yourself grief with little or any added security benefit to be honest. If you want to lock down your outbound ports - sure have at it...What I would suggest is just log all outbound traffic, then filter through it for odd ports other than 80/443.. So you can create your rules with your known used ports before you possible break stuff and have the wife and kids screaming X doesn't work..
Better option might be to filter your dns, so bad shit doesn't resolve.. Been in the security business for many many years, this is what I do for my home network.
-
"Better option might be to filter your dns, so bad shit doesn't resolve.. Been in the security business for many many years, this is what I do for my home network."
PfblockerNG would resolve this or help I am guessing..
-
@Ssaven said in Harden security for outbound ports:
PfblockerNG would resolve this or help I am guessing..
Exact.
But make that "pfBlockerNG-devel" - not "PfblockerNG" .
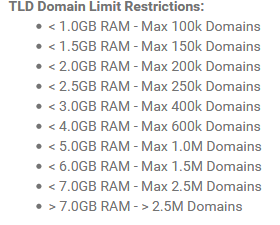
Just keep in mind : is a big package and can, depending on how you use it, eat a lot of resources. When you decide to use it, be ready to discover what DNS really is, and that you have to check upon it very regularity. If you are doing your job well, you'll be spending most of your time looking at ... the logs.
And keep on eye on used system resources like RAM and CPU usage.When you want to take the road of IDS/IPS, ask yourself the question : between your LAN device device, let's say, your PC, and some remote web server on the net, let say : your bank's web site, how do you want to make these Internet packets readable for programs so they can inspect the data traffic (the so called pay load) ?
SSL/TLS is not accessible to anyone between these mentioned devices. Plain "http" is pretty inexistent these days, it's all https these days.
There is a way : have all your devices trust your pfSense, using certificates to be installed on all your all (ALL !) your devices, and set up some proxy system on pfSense. Devices that don't cooperate have to be treated as exceptions, thus you have to create risk vectors in your setup. Maintaining such a system is a close-to daily job. And be ready to throw hardware resources on it. -
@Gertjan said in Harden security for outbound ports:
you'll be spending most of your time looking at ... the logs.
And keep on eye on used system resources like RAM and CPU usagethis is a true statement !
to keep in mind RAM is the issue when you start to play around with pfB