OpenVPN CA lifetime too short howto fix ? [SOLVED]
-
if you are lost and this happens ?
with your openVPN CA on your box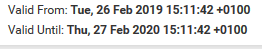
does anyone have a hint how to fix / solve this
i am pretty shure its simple but i cant find it like the forrest and the tree they say.
hope someone can help me out here.
thx in advance! -
You will need to make a new CA and reissue new certificates to everything that was signed by that CA.
2.5.0 has the option to renew CA and Certificate entries. You could spin up a 2.5.0 VM, import that CA and its private key, renew it, then export the certificate and copy that back to your live system. Just make sure to retain the key when renewing (Check Reuse Key)
AFAIR as long as the private key remains the same the signatures should still be valid for entities signed by that CA.
-
Hi Jimp,
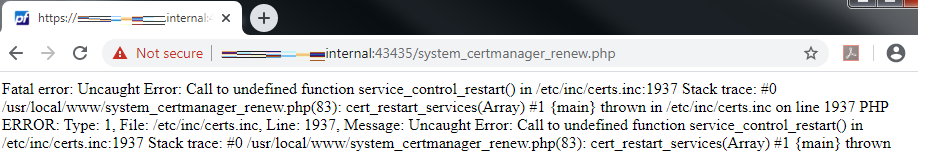
I got his error when i try to renew/reissue the CA.
Thanks,
A -
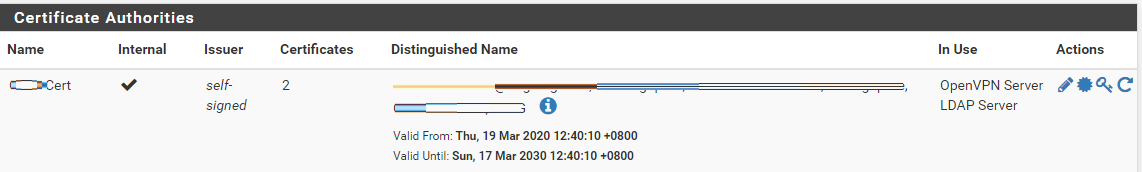
hmm... looking on the CA looks like it was renews already the validity date change already despite of the error..
-
thank you.
1st things first ... coffeeeeeee 6am not the time for doin open-heart surgerybut spinnin up a 2.5.0 VM great / awesome / wonderful idea
on my waythank you
i'll keep you posted -
hahaha.. i managed to copy over the latest CA to my production environment and clients are still able to connect w/ out any issue… Thanks!!
-
@albertmiclat
done that with the exported CA from a 2.5.0 in a vm ? -
@noplan, Yes, but I didn't start from scratch I always have a test environment ready just in case anything I want to test, just make sure to do snapshot so i can revert anytime.
Basically I just upgrade my test environment from 2.4.4 to 2.5.0 Development release.
Since my test environment contains identical configuration as my production system I jump straight to System > Cert. Manager >Click on the Renew/Reissue button, although it show some error but CA has been renewed.
Then, I proceed to export the key and cert. Then, on my production system I basically copied both key and cert accordingly.
To make sure everything works stop/start OpenVPN service then try to connect to test.
-
Good to see that worked!
You may still need to get an updated copy of the CA to clients, though.
For that PHP error, I can't reproduce it here, but I opened https://redmine.pfsense.org/issues/10360 and checked in a change that should fix it.
-
so i've done it the old school way
kind of doing some clean up in user name and settings and cleaning up style.- Certificate Manager --> Certificate Revocation --> Certificate Revocation List
- added CRL to openVpn Server
- revoked all vpn-user Certs via CRL
- revoked openVpnServerCert
- controlled via System --> Certificate Manager --> Certificates
- disabed vpn-users System --> User Manager --> Users
so far ...
- added new Certs
- changed Certs on openVpn Server
- adden new CRL to openVpn Server
- created new users
- testet
works like a Charm and it feels good ;)
so [solved]Thanks for helpin me out.