IPv6 over OpenVPN
-
As the title says I would like to give IPv4 OpenVPN clients access to the IPv6 internet. I have an internet connection that gives me IPv4 and a tunnel broker that gives me IPv6. I am relatively new to IPv6 and OpenVPN, so I was hopping for some advice and configuration instructions.
Thank You
-
Have you looked at the IPv6 settings on the OpenVPN client and server pages. They're pretty self explanatory.
-
I configured IPv6 and IPv4 on the VPN but when I check my IP address I get only IPv4. Why is this?
-
@User42 said in IPv6 over OpenVPN:
check my IP
Your browser picks whatever A or AAAA it has available in it's local cache, or upstream DNS cache, like the one pfSense is using. Or even farther up.
Use site like https://test-ipv6.com/ to force the detection.
The what-is-my-IP are to stupid. They should been called "do-I-have-a-conenction".Also, I've set up pfSense so it offers my networks a IPv4 and IPv6 connection.
When I VPN into my pfSense from a remote, IPv4 only place, I do have a IPv4 and IPv6 from my pfSense VPN server.
This is because :
I have a dual IPv4 IPv6 stack at my disposal
I control the pfSense VPN server
I control the VPN client, but I'm actually just using the VPN client export utility from pfSense and stock VPN software.
and that does the job.@User42 said in IPv6 over OpenVPN:
a tunnel broker that gives me IPv6.
tunnel.he.net ? That's the one I'm using also. If so, I be glad to post my settings.
-
I also use HE, In my internal network I have IPv6 working it connects and the https://test-ipv6.com/ test passes but over the VPN I only get IPv6 and I fail the test.
-
I have a tunnel provided by HE as well, but I am not routing v6 from that tunnel across my VPN. My ISP also provides me native v6. I am routing a subnet from that allocation over VPN. I have no reason to believe you can't get this working across your tunnel though.
You have to allocate a v6 subnet to your vpn and that is configured in the "IPv6 Tunnel Network". If that is done check your FW rules. There is not a rule auto generated for v6 on the VPN, you would need to create that.
If my memory serves me correctly, I don't believe there was any other trickery to the config.
-
I do not have expertise to configure IPv6 on OpenVPn but I have a link where you can get a proper solution. https://www.purevpn.com/what-is-vpn/protocols/openvpn
-
@calvinsteel @User42 was asking about how to connect its OpenVPN clients to his pfSense OpenVPN server.
And you throw in a "commercial VPN solution" that has nothing to do with the subject of this thread. -
User42 : if you have IPv6 working using tunnel.het.net, you can ping from your LAN any IPv6 enabled host, like :
C:\Users\Left>ping -6 netgate.com Envoi d'une requête 'ping' sur netgate.com [2610:160:11:11::73] avec 32 octets de données : Réponse de 2610:160:11:11::73 : temps=166 ms Réponse de 2610:160:11:11::73 : temps=166 ms Réponse de 2610:160:11:11::73 : temps=166 ms Réponse de 2610:160:11:11::73 : temps=166 ms(sorry, french systems here)
To make IPv6 work for OpenVPN warrior access :
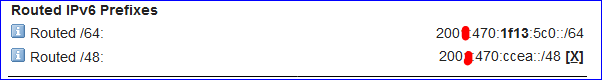
I already used the above mentioned /64 for my LAN.
So I took the fourth /64 from the /48block to assign it to the OpenVPN server :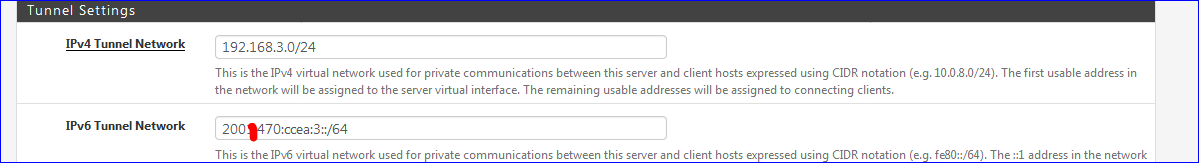
Note ......ccea.3:: == fourth /64 block, ......ccea.0::64 being block 1
This :
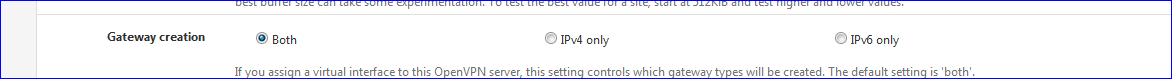
doesn't need any explanation.
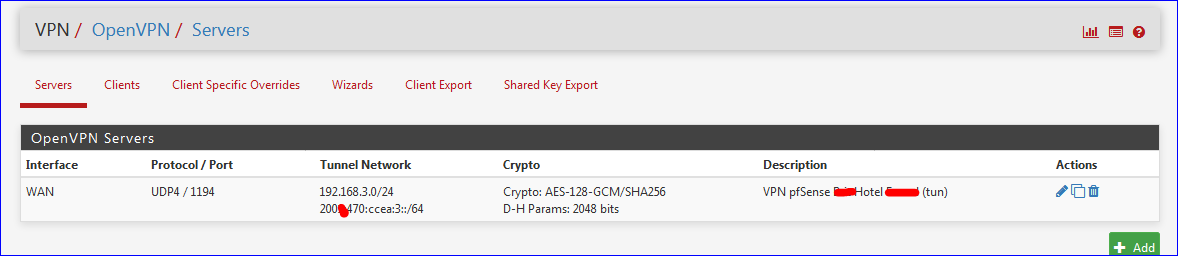
The server setup looks like this :
I'm not using the OpenVPN "placeholder" interface. I created a OPENVPN 'per VPN server instance' interface, and added these rather logic rules :
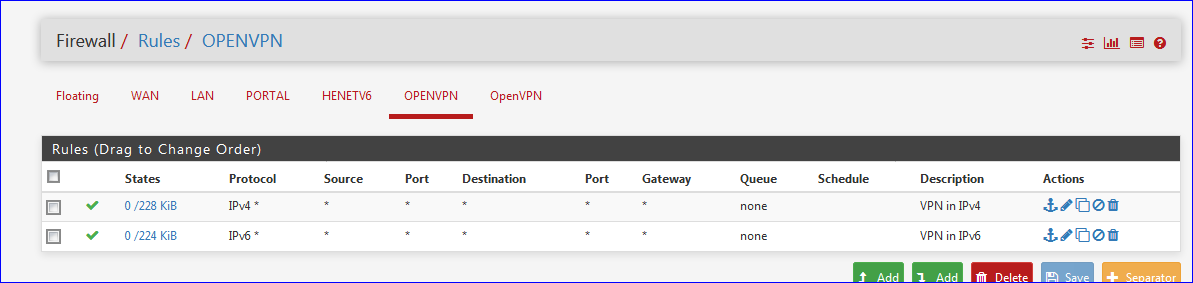
so that any foreign traffic can actually enter.
And, from memory, that's all I did no make it work.
From that point I can remote login using OpenVPN into pfSense, and use it's IPv6 facilities.
-
Thank You for your help on everything, it works now! :)