pfSense and meraki z3
-
The reason it works behind some other firewall is that most SOHO style so not randomise the source port for NAT'd connections. pfSense does that to increase security and to prevent multiple outbound states all using the same port which could conflict. For some reason the remote Meraki device is unable to cope with more than one source port.

https://docs.netgate.com/pfsense/en/latest/nat/static-port.htmlIf you don't know what ports it needs then you can just set and outbound NAT rule with static source ports for all connections from the Z3 IP. At least as a test.
Steve
-
@stephenw10 said in pfSense and meraki z3:
NAT rule with static source ports for all connections from the Z3 IP. At least as a test.
Great test for sure!
But doesn't matter if the random ports on nat were were the problem or not - he still should see states or traffic.. Where you could see what it was doing from a sniff..
That they would setup some sort of vpn solution that required static port natting seems pretty unthoughtful on where this might or could get deployed.
But yeah just setting all outbound natting to static would be a simple test if you can not see which ports its actually using via states or a sniff..
My pfsense LAN is set to 192.168.x.x The box is set to something different then that
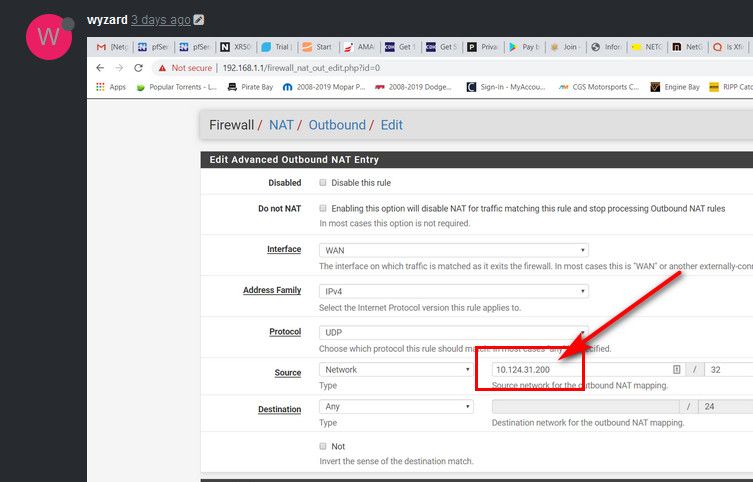
Than what was that 10.124 nonsense for an outbound nat? That would of never done anything. Where did you get the 10.124 address from?
-
It seemed to me that the 10.124.x.x was the static IP of the Meraki.
So here's what I know:
- The IT department at my wife's work can "see" the Meraki when it is behind the pfsense. For some reason the Meraki can't get "back" to them.
- The PC that is connected to the Meraki is not getting an IP address.
- The PC indicates "attempting to authenticate"
- It then says "authentication failed".
From what I can see in the logs on pfsense (states and packet capture) nothing seems out of the ordinary.
I agree with everyone that this should not be that hard. I my mind should be a simple plug and play. Really not sure what is going on?
About to call it a TKO
-
@wyzard said in pfSense and meraki z3:
I agree with everyone that this should not be that hard. I my mind should be a simple plug and play.
As I mentioned, this appears to be a device intended to replace a consumer router/firewall, not be used behind it. That it works without pfSense shows this. Another thing you could try is put a consumer grade router/firewall ahead of it. If that works, then some investigation may reveal what the problem is.
-
@wyzard said in pfSense and meraki z3:
It seemed to me that the 10.124.x.x was the static IP of the Meraki.
Where did you get that from? It wouldn't be able to do anything if that was its IP of its wan, and if that is is lan IP, your outbound nat wouldn't do shit..
The IT department at my wife's work can "see" the Meraki when it is behind the pfsense. For some reason the Meraki can't get "back" to them.
If they can see it, then it CAN get back to them..
The PC that is connected to the Meraki is not getting an IP address.
Then how would it be saying its attempting to authenticate...
Answer some basic questions.. from pfsense does it hand out an IP address to this device? If so what is it?
When you connect a PC to the lan side of it.. lets see the IPconfig /all from this device...
-
@JKnott said in pfSense and meraki z3:
@wyzard said in pfSense and meraki z3:
I agree with everyone that this should not be that hard. I my mind should be a simple plug and play.
As I mentioned, this appears to be a device intended to replace a consumer router/firewall, not be used behind it. That it works without pfSense shows this. Another thing you could try is put a consumer grade router/firewall ahead of it. If that works, then some investigation may reveal what the problem is.
I agree about it replacing a router/firewall. I don't want to send all my traffic through that though. Not that I have anything to hide, but according to the installation instructions that were sent home with my wife, this should plug into the existing router and work. And, as I said, her IT department is pretty much useless.
-
Yeah, where exactly did the 10.124.31.200 IP address come from?
That cannot be the Z3 WAN side since it is connecting out partly. It must, therefore, be it's LAN.
In which case, as johnpoz said, you need to find what IP address in your LAN subnet the Z3 is pulling and add that as the source address in the outbound NAT rule(s).
I'm pretty that static outbound NAT rule is all you need to make this work. It just has to be the right rule.
Steve
-
@stephenw10 said in pfSense and meraki z3:
It just has to be the right rule.
Or as you already stated just set all to static.. That would be a great test..
-
Thank you everyone for your help! Finally figured what the IP it was getting from my network. Entered a rule with the information and it's working!
Thanks again to everyone for the help and guidance.
-
Nice.

-
Would you mind sharing the rule you made? I seem to be having the same issue but with a Meraki MX68.
Thanks
-
It was a static source port outbound NAT rule specific to the source IP the Meraki was using.
It seems as though the Meraki VPN chokes if the source port changes.
Steve
-
@stephenw10 said in pfSense and meraki z3:
It seems as though the Meraki VPN chokes if the source port changes.
Which is just a horrible horrible design!!
Not sure which one ticks me off more, static source ports or hard coding IPs
-
Thanks, I got it with the above mentioned rules. Had to sift through states to find port #'s but once I added all of them to the alias I created for the rule, it was good to go.
-
Lets throw a 3rd one in to my list of pet peeves ;)
Game companies that are unable to correctly document the ports needed for their game to work.. They list ports, but don't say if its inbound or outbound, like 53 - that sure and the F is not needed inbound!! Same with 80... If that was required inbound most people wouldn't be able to play, since most home connections the isp blocks 80 inbound.
How hard would it be to list the ports required outbound, and inbound (port forward) and if any traffic requires static ports..
And a side to that - how about just actually leveraging IPv6 so all this nat shit goes away for your games where the users have IPv6.
-
Yup, and not restricted to games either. I can't tell the number of times I've seen a huge list of forwarded ports that have zero business being there.

Steve
-
I mean really, I create an app that talk to another app via port X.. How about listing these X ports - I mean really you wrote the freaking thing... Are you not using the same internet that everyone else on the planet is using where ports inbound are blocked via nat?
Its just freaking crazy - how F'king hard is that - I mean really!!! Its not like we using different shit here.. Your isp does really the same thing that isp Y does down the street.. Clearly list
Port forward
X
Y
ZOutbound
A
B
C..Is that asking that much??
-
I have one addition to instructions above.
First, thank you all for contributing to this forum. You guys helped me get my Meraki Z3 working with my Pfsense. Wanted to share some additional info, in the hopes it will save somebody else time. To make it work for the Meraki Z3 I got from my company. These servers are owned by my company and apparently we do something special - so just FYI.
Additonal outbound NAT rules for the Meraki to the following destinations:
- UDP to IP:XXX.XXX.XXX.XXX port 50881
- UDP to IP:XXX.XXX.XXX.XXX port 48708
Tally ho!
-
@wyzard said in pfSense and meraki z3:
Thank you everyone for your help! Finally figured what the IP it was getting from my network. Entered a rule with the information and it's working!
Thanks again to everyone for the help and guidance.
Could you please screenshot and post exactly what all you opened to get it working including inbound and outbound? TIA
-
The only thing that was required was an outbound NAT rule for the devices internal IP with static source ports set.
Steve