User authentication
-
Hello Guys,
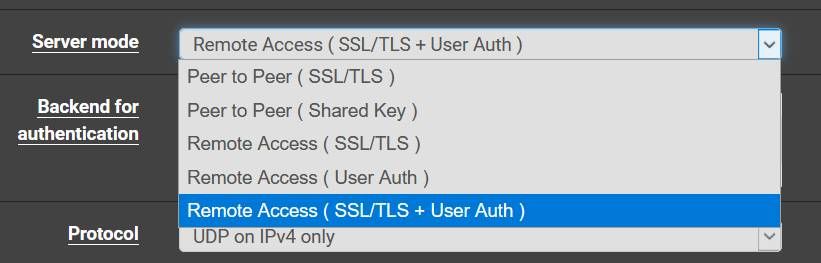
i've created 7 VPN Server into my PFsense version 2.4.3 with local database authentication, so if a create an user X it is working in any certificate !!!! , i would like to know how to force the user X to connect just in the VPN Server that he belongs ?
best regards,
-
Well why/how would the user connect to the wrong one? Wouldn't the client config point the user to specific IP or Port for the instance.. Are you saying if they manually change the to different IP, port or tcp/udp that other instance is listening on he can auth?
-
Maybe create different CA for every Server/User.
-
^ exactly you have to make sure your not sharing auth and or server settings (certs and ca) or yeah clients would be able to connect to anything that uses shared authing..
You should be able to prevent users from connecting to different instances just by using different TLS keys even if the same CA for example.. So curious how you have these different instances setup.
-
@johnpoz said in User authentication:
by using different TLS keys even if the same CA for example..
But the TLS Key is Server specific, not user?
-
the TLS key is instance specific... How would he be creating 7 servers if he didn't create 7 different instances..
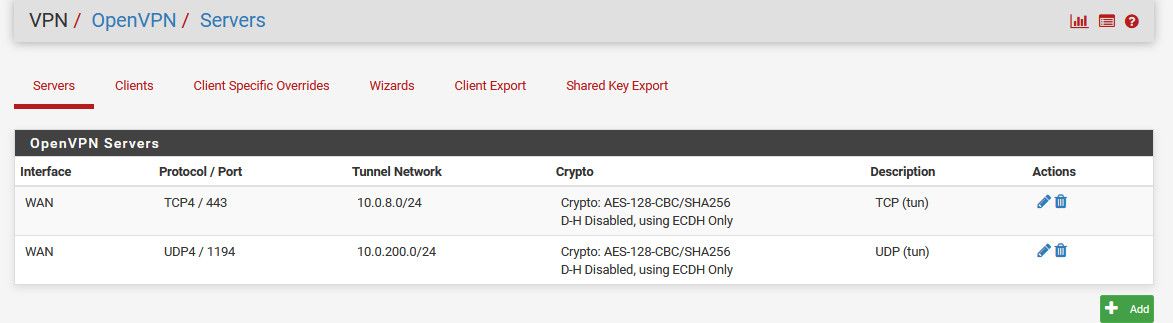
For example I have 2, one that runs on port 443 tcp, and another that runs on UDP 1194... They have different TLS keys.. Even if the same user can connect to both..
The user has 2 different config files to connect to either instance... If the client only has the TCP info, then he could only connect to the TCP instance - because even if he changed the port and protocl, etc. etc. his TLS key would be wrong for that instance... He would need to have that other TLS key.
This is why I am confused at how he has this setup.
-
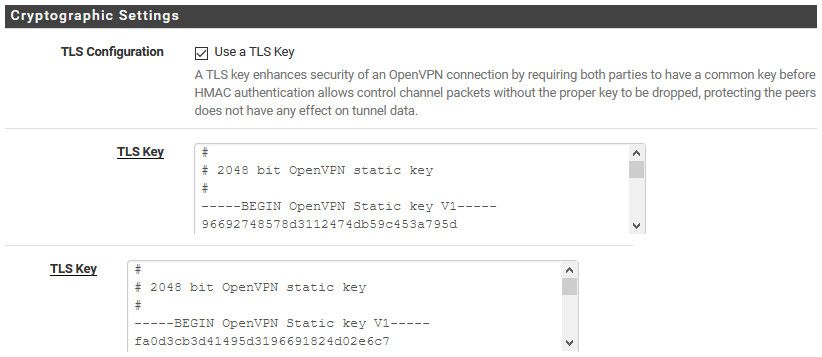
@johnpoz Right. I created two server but deliberately (as far as I can say with my little knowledge) with the same TLS Key, so that I could use the same Client-config file for both.
-
Thaaks Guys,
Reading all anwser i could figure out that the mistake was create on CA_root and vinculate to all my others certificated even Server/User , so it means any user could access any certifcate chain !!!! i will fix it creating one CA for each Server/User
thanks for helping
-
@Bob-Dig said in User authentication:
TLS Key, so that I could use the same Client-config file for both.
Unless you did a manual input of the TLS key - it would be self generated and different! when you create the new instance.
If you wanted say your client to auto check both and connect to the first one that works, then sure you would need to do that.
-
@johnpoz said in User authentication:
Unless you did a manual input of the TLS key - it would be self generated and different! when you create the new instance.
Yeah, I copied it over from the first instance.
-
Yeah see mine are different
I don't want auto search for connection, etc. But user would have to have done that on PURPOSE!!! So why would there be a question to how its happening?
If you only want your users connecting to instance X... Why would you even give them the info in their config for the other instances, and the use the same TLS key... You can use the same CA for each instance... Not going to matter - because the TLS keys wouldn't match for their config.
So users can have certs signed by same CA, they could even all use the same backend to auth.. But locking them to a specific instance of your vpn server should be prevented by the config you give them and the TLS key... Give them config with only X tls key and only port and IP of instance(s) you want them to be able to connect too. If they on purpose change to different info - say they got it from their coworker.. That coworker wold also have to give them the TLS key.. In such a case there is really nothing you can do if uses are going to share their info.
-
@johnpoz there are so many options...
-
Well if there only using user auth, then yeah they have a problem.. ;)