Lots of errors in suricata log
-
just upgraded to pfsense 2.4.5
- rebooted
- removed packages that required an upgrade (suricata & avahi)
- upgrade (from console)
- reinstalled suricata & avahi
the suricata log shows a lot of errors, I don't know if this was the case with earlier version(s)
<Notice> -- This is Suricata version 5.0.2 RELEASE running in SYSTEM mode <Info> -- CPUs/cores online: 4 <Info> -- HTTP memcap: 67108864 <Notice> -- using flow hash instead of active packets <Info> -- Netmap: Setting IPS mode <Info> -- fast output device (regular) initialized: alerts.log <Info> -- http-log output device (regular) initialized: http.log <Info> -- stats output device (regular) initialized: stats.log <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - bad option value formatting (possible missing semicolon) for keyword content: '"FileReader|28|",nocase' <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET any -> $SMTP_SERVERS 25 ( msg:"BROWSER-CHROME Google Chrome FileReader use after free attempt"; flow:to_server,established; file_data; content:"FileReader|28|",nocase; content:"Blob|28|",within 200,fast_pattern,nocase; content:".result",within 300,nocase; content:"readAsArrayBuffer|28|",within 200,nocase; metadata:policy balanced-ips drop,policy max-detect-ips drop,policy security-ips drop; service:smtp; reference:bugtraq,107213; reference:cve,2019-5786; reference:url,chromium-review.googlesource.com/c/chromium/src/+/1495209; classtype:attempted-user; sid:49360; rev:1; )" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 7072 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - bad option value formatting (possible missing semicolon) for keyword content: '"FileReader|28|",nocase' <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET $FILE_DATA_PORTS -> $HOME_NET any ( msg:"BROWSER-CHROME Google Chrome FileReader use after free attempt"; flow:to_client,established; file_data; content:"FileReader|28|",nocase; content:"Blob|28|",within 200,fast_pattern,nocase; content:".result",within 200,nocase; content:"readAsArrayBuffer|28|",within 200,nocase; metadata:policy balanced-ips drop,policy max-detect-ips drop,policy security-ips drop; service:ftp-data, http, imap, pop3; reference:bugtraq,107213; reference:cve,2019-5786; reference:url,chromium-review.googlesource.com/c/chromium/src/+/1495209; classtype:attempted-user; sid:49361; rev:1; )" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 7073 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - bad option value formatting (possible missing semicolon) for keyword content: '"[144,144,144,144,101,72,139,4,37,48,0,0,0,72,139,96,8,72,129,236,8,16,0,0,144,144,144,144",fast_pattern,nocase' <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET $FILE_DATA_PORTS -> $HOME_NET any ( msg:"BROWSER-CHROME Google Chrome blink webaudio module use after free attempt"; flow:to_client,established; file_data; content:"[144,144,144,144,101,72,139,4,37,48,0,0,0,72,139,96,8,72,129,236,8,16,0,0,144,144,144,144",fast_pattern,nocase; metadata:policy balanced-ips drop,policy connectivity-ips drop,policy max-detect-ips drop,policy security-ips drop; service:ftp-data, http, imap, pop3; reference:cve,2019-13720; reference:url,chromereleases.googleblog.com/2019/10/stable-channel-update-for-desktop_31.html; classtype:attempted-user; sid:52068; rev:1; )" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 7074 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - bad option value formatting (possible missing semicolon) for keyword content: '"[144,144,144,144,101,72,139,4,37,48,0,0,0,72,139,96,8,72,129,236,8,16,0,0,144,144,144,144",fast_pattern,nocase'the list goes on,
<Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET any -> $HOME_NET [1024:] ( msg:"SERVER-OTHER HP OpenView Storage Data Protector - initiate connection"; flow:to_server,established; content:"H|00|P|00| |00|O|00|p|00|e|00|n|00|V|00|i|00|e|00|w|00| |00|O|00|m|00|n|00|i|00|B|00|a|00|c|00|k",fast_pattern,nocase; flowbits:set,hp_openview_sdp; flowbits:noalert; metadata:policy max-detect-ips drop; classtype:protocol-command-decode; sid:27121; rev:9; )" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/flowbit-required.rules at line 1396 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - bad option value formatting (possible missing semicolon) for keyword content: '"HP OpenView OmniBack",fast_pattern,nocase' <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET any -> $HOME_NET [1024:] ( msg:"SERVER-OTHER HP OpenView Storage Data Protector - initiate connection"; flow:to_server,established; content:"HP OpenView OmniBack",fast_pattern,nocase; flowbits:set,hp_openview_sdp; flowbits:noalert; metadata:policy max-detect-ips drop; classtype:protocol-command-decode; sid:32345; rev:9; )" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/flowbit-required.rules at line 1399 <Info> -- 2 rule files processed. 7127 rules successfully loaded, 11503 rules failed <Warning> -- [ERRCODE: SC_ERR_EVENT_ENGINE(210)] - can't suppress sid 2000419, gid 1: unknown rule <Info> -- Threshold config parsed: 1 rule(s) found <Info> -- 7127 signatures processed. 52 are IP-only rules, 1824 are inspecting packet payload, 5132 inspect application layer, 103 are decoder event only <Warning> -- [ERRCODE: SC_WARN_FLOWBIT(306)] - flowbit 'et.http.PK' is checked but not set. Checked in 2019835 and 1 other sigs <Info> -- cleaning up signature grouping structure... complete <Notice> -- rule reload completewhat is wrong (using ETopen and snortrules-snapshot-3000.tar.gz).
-
@jpgpi250 said in Lots of errors in suricata log:
the list goes on,
Hi Bro,
DO NOT specify a Snort3 rules file! Snort3 rules are incompatible witih Suricata 4.x and will break your installation!
-
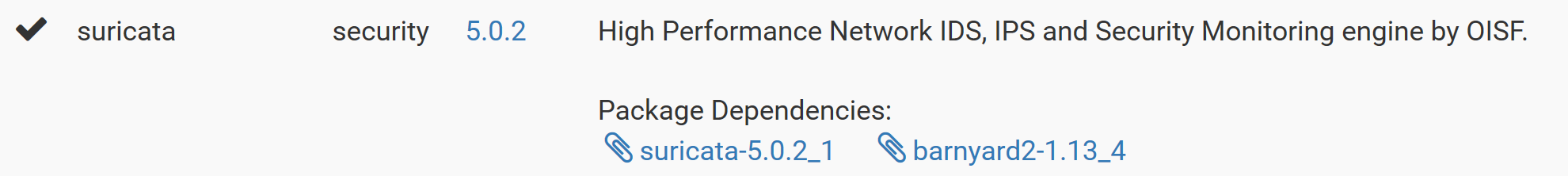
after upgrade of pfsense to 2.4.5 and reinstall of suricata, the suricata version is 5.0.2. Are Snort3 rules also incompatible with this version of suricata?
-
sorry now i see that it is 5 versions
-
Bill could be the solution
-
@jpgpi250 said in Lots of errors in suricata log:
just upgraded to pfsense 2.4.5
- rebooted
- removed packages that required an upgrade (suricata & avahi)
- upgrade (from console)
- reinstalled suricata & avahi
the suricata log shows a lot of errors, I don't know if this was the case with earlier version(s)
<Notice> -- This is Suricata version 5.0.2 RELEASE running in SYSTEM mode <Info> -- CPUs/cores online: 4 <Info> -- HTTP memcap: 67108864 <Notice> -- using flow hash instead of active packets <Info> -- Netmap: Setting IPS mode <Info> -- fast output device (regular) initialized: alerts.log <Info> -- http-log output device (regular) initialized: http.log <Info> -- stats output device (regular) initialized: stats.log <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - bad option value formatting (possible missing semicolon) for keyword content: '"FileReader|28|",nocase' <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET any -> $SMTP_SERVERS 25 ( msg:"BROWSER-CHROME Google Chrome FileReader use after free attempt"; flow:to_server,established; file_data; content:"FileReader|28|",nocase; content:"Blob|28|",within 200,fast_pattern,nocase; content:".result",within 300,nocase; content:"readAsArrayBuffer|28|",within 200,nocase; metadata:policy balanced-ips drop,policy max-detect-ips drop,policy security-ips drop; service:smtp; reference:bugtraq,107213; reference:cve,2019-5786; reference:url,chromium-review.googlesource.com/c/chromium/src/+/1495209; classtype:attempted-user; sid:49360; rev:1; )" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 7072 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - bad option value formatting (possible missing semicolon) for keyword content: '"FileReader|28|",nocase' <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET $FILE_DATA_PORTS -> $HOME_NET any ( msg:"BROWSER-CHROME Google Chrome FileReader use after free attempt"; flow:to_client,established; file_data; content:"FileReader|28|",nocase; content:"Blob|28|",within 200,fast_pattern,nocase; content:".result",within 200,nocase; content:"readAsArrayBuffer|28|",within 200,nocase; metadata:policy balanced-ips drop,policy max-detect-ips drop,policy security-ips drop; service:ftp-data, http, imap, pop3; reference:bugtraq,107213; reference:cve,2019-5786; reference:url,chromium-review.googlesource.com/c/chromium/src/+/1495209; classtype:attempted-user; sid:49361; rev:1; )" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 7073 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - bad option value formatting (possible missing semicolon) for keyword content: '"[144,144,144,144,101,72,139,4,37,48,0,0,0,72,139,96,8,72,129,236,8,16,0,0,144,144,144,144",fast_pattern,nocase' <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET $FILE_DATA_PORTS -> $HOME_NET any ( msg:"BROWSER-CHROME Google Chrome blink webaudio module use after free attempt"; flow:to_client,established; file_data; content:"[144,144,144,144,101,72,139,4,37,48,0,0,0,72,139,96,8,72,129,236,8,16,0,0,144,144,144,144",fast_pattern,nocase; metadata:policy balanced-ips drop,policy connectivity-ips drop,policy max-detect-ips drop,policy security-ips drop; service:ftp-data, http, imap, pop3; reference:cve,2019-13720; reference:url,chromereleases.googleblog.com/2019/10/stable-channel-update-for-desktop_31.html; classtype:attempted-user; sid:52068; rev:1; )" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 7074 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - bad option value formatting (possible missing semicolon) for keyword content: '"[144,144,144,144,101,72,139,4,37,48,0,0,0,72,139,96,8,72,129,236,8,16,0,0,144,144,144,144",fast_pattern,nocase'the list goes on,
<Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET any -> $HOME_NET [1024:] ( msg:"SERVER-OTHER HP OpenView Storage Data Protector - initiate connection"; flow:to_server,established; content:"H|00|P|00| |00|O|00|p|00|e|00|n|00|V|00|i|00|e|00|w|00| |00|O|00|m|00|n|00|i|00|B|00|a|00|c|00|k",fast_pattern,nocase; flowbits:set,hp_openview_sdp; flowbits:noalert; metadata:policy max-detect-ips drop; classtype:protocol-command-decode; sid:27121; rev:9; )" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/flowbit-required.rules at line 1396 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - bad option value formatting (possible missing semicolon) for keyword content: '"HP OpenView OmniBack",fast_pattern,nocase' <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET any -> $HOME_NET [1024:] ( msg:"SERVER-OTHER HP OpenView Storage Data Protector - initiate connection"; flow:to_server,established; content:"HP OpenView OmniBack",fast_pattern,nocase; flowbits:set,hp_openview_sdp; flowbits:noalert; metadata:policy max-detect-ips drop; classtype:protocol-command-decode; sid:32345; rev:9; )" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/flowbit-required.rules at line 1399 <Info> -- 2 rule files processed. 7127 rules successfully loaded, 11503 rules failed <Warning> -- [ERRCODE: SC_ERR_EVENT_ENGINE(210)] - can't suppress sid 2000419, gid 1: unknown rule <Info> -- Threshold config parsed: 1 rule(s) found <Info> -- 7127 signatures processed. 52 are IP-only rules, 1824 are inspecting packet payload, 5132 inspect application layer, 103 are decoder event only <Warning> -- [ERRCODE: SC_WARN_FLOWBIT(306)] - flowbit 'et.http.PK' is checked but not set. Checked in 2019835 and 1 other sigs <Info> -- cleaning up signature grouping structure... complete <Notice> -- rule reload completewhat is wrong (using ETopen and snortrules-snapshot-3000.tar.gz).
I've posted here in the past about this. DO NOT use the Snort3 rules. They are incompatible with Suricata and with Snort 2.9.x.
Since you have installed those rules, you are going to have to remove the Suricata package and reinstall it because the Snort3 rules package will have corrupted some critical config files by overwriting them with Snort3 stuff. You won't lose your configuration, but you must delete the package and reinstall it. And this time, DO NOT enable the Snort3 rules. Use the Snort 2.9.15.1 rules (
snortrules-snapshot-29151.tar.gz). Fix this BEFORE you remove the package, otherwise when you remove and reinstall it will just download the Snort3 rules again and corrupt the new install.Snort3 stuff will break both the Snort and Suricata packages on pfSense. Here is a post I made about this: https://forum.netgate.com/topic/138277/suricata-snort-vrt-rules-problem-missing-fixed. There are other posts as well.
-
@bmeeks changed rules file, uninstalled, installed.
Content of suricata log - Is there anything else I need to change (errors and flowbit warnings)?:<Notice> -- This is Suricata version 5.0.2 RELEASE running in SYSTEM mode <Info> -- CPUs/cores online: 4 <Info> -- HTTP memcap: 67108864 <Notice> -- using flow hash instead of active packets <Info> -- Netmap: Setting IPS mode <Info> -- fast output device (regular) initialized: alerts.log <Info> -- http-log output device (regular) initialized: http.log <Info> -- stats output device (regular) initialized: stats.log <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - "http_header" keyword seen with a sticky buffer still set. Reset sticky buffer with pkt_data before using the modifier. <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET $HTTP_PORTS -> $HOME_NET any (msg:"EXPLOIT-KIT Flashpack/Safe/CritX exploit kit jar file download"; flow:to_client,established; file_data; content:"filename="; http_header; content:".jar"; within:4; distance:24; pcre:"/filename\=[a-z0-9]{24}\.jar/H"; metadata:policy balanced-ips drop, policy max-detect-ips drop, policy security-ips drop, service http; reference:url,www.malwaresigs.com/2013/06/06/flashpack-exploit-kit-safepack/; classtype:trojan-activity; sid:26892; rev:3;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 8627 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - "http_header" keyword seen with a sticky buffer still set. Reset sticky buffer with pkt_data before using the modifier.list continues...
<Error> -- [ERRCODE: SC_ERR_RULE_KEYWORD_UNKNOWN(102)] - unknown rule keyword 'byte_math'. <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET $FILE_DATA_PORTS -> $HOME_NET any (msg:"FILE-OTHER Adobe Acrobat Pro EMF EmfPlusDrawRects record out of bounds read attempt"; flow:to_client,established; file_data; content:"|46 00 00 00|"; content:"|45 4D 46 2B|"; within:4; distance:8; fast_pattern; content:"|0B 40|"; distance:0; content:"|00|"; within:1; distance:1; byte_math:bytes 4,offset 4,oper /,rvalue 8,result total_rects,relative,endian little; byte_test:4,>,total_rects,8,relative,little; metadata:policy balanced-ips drop, policy max-detect-ips drop, policy security-ips drop, service ftp-data, service http, service imap, service pop3; reference:cve,2018-4896; reference:url,helpx.adobe.com/security/products/acrobat/apsb18-02.html; classtype:attempted-user; sid:45821; rev:1;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 11677 <Error> -- [ERRCODE: SC_ERR_RULE_KEYWORD_UNKNOWN(102)] - unknown rule keyword 'byte_math'. <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET any -> $SMTP_SERVERS 25 (msg:"FILE-OTHER Adobe Acrobat Pro EMF EmfPlusDrawRects record out of bounds read attempt"; flow:to_server,established; file_data; content:"|46 00 00 00|"; content:"|45 4D 46 2B|"; within:4; distance:8; fast_pattern; content:"|0B 40|"; distance:0; content:"|00|"; within:1; distance:1; byte_math:bytes 4,offset 4,oper /,rvalue 8,result total_rects,relative,endian little; byte_test:4,>,total_rects,8,relative,little; metadata:policy balanced-ips drop, policy max-detect-ips drop, policy security-ips drop, service smtp; reference:cve,2018-4896; reference:url,helpx.adobe.com/security/products/acrobat/apsb18-02.html; classtype:attempted-user; sid:45820; rev:1;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 11678 <Error> -- [ERRCODE: SC_ERR_RULE_KEYWORD_UNKNOWN(102)] - unknown rule keyword 'byte_math'. <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET $FILE_DATA_PORTS -> $HOME_NET any (msg:"FILE-OTHER Adobe Acrobat Pro EMF EmfPlusDrawRects record out of bounds read attempt"; flow:to_client,established; file_data; content:"|46 00 00 00|"; content:"|45 4D 46 2B|"; within:4; distance:8; fast_pattern; content:"|0B 40|"; distance:0; content:"|02|"; within:1; distance:1; byte_math:bytes 4,offset 4,oper /,rvalue 16,result total_rects,relative,endian little; byte_test:4,>,total_rects,8,relative,little; metadata:policy balanced-ips drop, policy max-detect-ips drop, policy security-ips drop, service ftp-data, service http, service imap, service pop3; reference:cve,2018-4896; reference:url,helpx.adobe.com/security/products/acrobat/apsb18-02.html; classtype:attempted-user; sid:45819; rev:1;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 11679 <Error> -- [ERRCODE: SC_ERR_FLAGS_MODIFIER(103)] - cannot set DETECT_FLOW_FLAG_TOSERVER flag is already set <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET any -> $SMTP_SERVERS 25 (msg:"FILE-OTHER Microsoft SharePoint deserialization attempt"; flow:to_server,to_server,established; file_data; content:"executeQueryAsync"; nocase; content:"<DynamicType"; fast_pattern:only; content:"<ObjectInstance"; nocase; content:"<MethodName>Deserialize</MethodName>"; within:100; nocase; content:"xsd:string"; within:100; base64_decode:bytes 1000,relative; base64_data; content:"|FF 01 32 BC 06|"; within:5; content:"<ObjectDataProvider"; within:550; content:"cmd.exe"; within:250; metadata:policy balanced-ips drop, policy max-detect-ips drop, policy security-ips drop, service smtp; reference:cve,2019-1257; reference:url,portal.msrc.microsoft.com/en-us/security-guidance/advisory/CVE-2019-1257; classtype:attempted-admin; sid:51475; rev:1;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 11856 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - previous keyword has a fast_pattern:only; set. Can't have relative keywords around a fast_pattern only content <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $HOME_NET any -> $EXTERNAL_NET $HTTP_PORTS (msg:"MALWARE-CNC Bancos fake JPG encrypted config file download"; flow:to_server,established; content:".com.br|0D 0A 0D 0A|"; fast_pattern:only; content:"/imagens/"; depth:9; http_uri; content:".jpg"; distance:0; http_uri; pcre:"/\.jpg\x20HTTP\/1\.[01]\r\nUser\x2dAgent\x3a\x20[a-z]+\r\nHost\x3a\x20[a-z0-9\x2d\x2e]+\.com\.br\r\n\r\n$/"; metadata:impact_flag red, policy balanced-ips drop, policy security-ips drop, ruleset community, service http; classtype:trojan-activity; sid:26722; rev:1;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 13051 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - "http_header" keyword seen with a sticky buffer still set. Reset sticky buffer with pkt_data before using the modifier. <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET $HTTP_PORTS -> $HOME_NET any (msg:"MALWARE-CNC Osx.Trojan.Janicab runtime traffic detected"; flow:to_client,established; file_data; content:"content=|22|just something i made up for fun, check out my website at"; fast_pattern:only; content:"X-YouTube-Other-Cookies:"; nocase; http_header; metadata:impact_flag red, policy balanced-ips drop, policy max-detect-ips drop, policy security-ips drop, service http; reference:cve,2012-0158; reference:url,www.virustotal.com/file/3bc13adad9b7b60354d83bc27a507864a2639b43ec835c45d8b7c565e81f1a8f/analysis/; classtype:trojan-activity; sid:27544; rev:3;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 13473 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - previous keyword has a fast_pattern:only; set. Can't have relative keywords around a fast_pattern only content <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $HOME_NET any -> $EXTERNAL_NET $HTTP_PORTS (msg:"MALWARE-CNC Win.Trojan.Injector variant outbound connection"; flow:to_server,established; urilen:9; content:"/load.exe HTTP/1.1|0D 0A|User-Agent: Mozilla/"; fast_pattern:only; content:"|3B 20|MSIE|20|"; http_header; content:")|0D 0A|Host: "; distance:0; http_header; content:!"Accept"; http_header; metadata:impact_flag red, policy balanced-ips drop, policy security-ips drop, ruleset community, service http; reference:url,urlquery.net/search.php?q=%5C%2Fload%5C.exe%24&type=regexp&start=2013-08-24&end=2013-11-22&max=400; reference:url,www.virustotal.com/en/file/032572ea1f34a060ecac98a8e2899dc0f2a41dff199e879050481ddd3818b4d0/analysis/; classtype:trojan-activity; sid:28807; rev:2;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 13628 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - previous keyword has a fast_pattern:only; set. Can't have relative keywords around a fast_pattern only content <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $HOME_NET any -> $EXTERNAL_NET $HTTP_PORTS (msg:"MALWARE-CNC Win.Trojan.Bancos variant outbound connection"; flow:to_server,established; content:"Content-Length: 166"; content:".php HTTP/1.1|0D 0A|Accept: */*|0D 0A|Content-Type: application/x-www-form-urlencoded|0D 0A|User-Agent: Mozilla/5.0 (Windows NT 6.1|3B| Trident/7.0|3B| rv:11.0) like Gecko|0D 0A|Host: "; fast_pattern:only; content:"v="; depth:2; http_client_body; content:"&c="; within:7; http_client_body; pcre:"/\x3d\x3d$/P"; metadata:impact_flag red, policy balanced-ips drop, policy security-ips drop, ruleset community, service http; reference:url,www.virustotal.com/en/file/51540d7c9a4bc2a430bc50c85cf9cec5c6f2bb755e800a3f3575ba34fe5f008c/analysis; classtype:trojan-activity; sid:29895; rev:2;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 13816 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - Can't use file_data with flow:to_server or flow:from_client with http. <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $HOME_NET any -> $EXTERNAL_NET $HTTP_PORTS (msg:"MALWARE-CNC ANDR.Trojan.FakeApp outbound connection"; flow:to_server,established; content:"/cp/server.php"; fast_pattern:only; http_uri; content:"Content-Type: multipart/form-data|3B| boundary=Aab03x"; http_header; content:"User-Agent: Dalvik"; http_header; file_data; content:"AaB03x"; content:"name=|22|phone"; distance:0; content:"name=|22|type"; distance:0; metadata:impact_flag red, policy balanced-ips drop, policy security-ips drop, service http; reference:url,securityaffairs.co/wordpress/22465/cyber-crime/banking-trojan-hit-islamic-mobile.html; reference:url,www.virustotal.com/file/66911EE32FC4777BB9272F9BE9EB8970B39440768B612FBAB4AC01D8E23F9AA1/analysis/; classtype:trojan-activity; sid:29978; rev:3;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 13843 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - previous keyword has a fast_pattern:only; set. Can't have relative keywords around a fast_pattern only content <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $HOME_NET any -> $EXTERNAL_NET $HTTP_PORTS (msg:"MALWARE-CNC Win.Trojan.Rehtesyk outbound connection"; flow:to_server,established; content:"User-Agent: Firefox|0D 0A|"; fast_pattern:only; content:"first="; depth:6; http_client_body; content:"&data="; within:7; http_client_body; metadata:impact_flag red, policy balanced-ips drop, policy security-ips drop, service http; reference:url,www.virustotal.com/en/file/b1347df8f8940039cb68bd4e2568e8c68b1f1a0067ac9a0fb1a5f1aef2df61ea/analysis/; classtype:trojan-activity; sid:32311; rev:2;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 14189 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - "http_header" keyword seen with a sticky buffer still set. Reset sticky buffer with pkt_data before using the modifier. <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET $HTTP_PORTS -> $HOME_NET any (msg:"MALWARE-CNC Win.Trojan.Sodebral HTTP Response attempt"; flow:to_client,established; file_data; isdataat:!193; content:"BRASIL"; depth:6; content:!"Content-Length"; http_header; content:"Transfer-Encoding: chunked"; http_header; metadata:impact_flag red, policy balanced-ips drop, policy security-ips drop, ruleset community, service http; reference:url,www.virustotal.com/en/file/e0290c3900445dc00ca24888924e37fa6ac17ecaddc60591e32b81536b9f5ef7/analysis/; classtype:trojan-activity; sid:32608; rev:2;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 14253 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - "http_header" keyword seen with a sticky buffer still set. Reset sticky buffer with pkt_data before using the modifier. <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET $HTTP_PORTS -> $HOME_NET any (msg:"MALWARE-CNC Win.Trojan.Sodebral HTTP Response attempt"; flow:to_client,established; file_data; isdataat:!193; content:"INTERNACIONAL"; depth:13; content:!"Content-Length"; http_header; content:"Transfer-Encoding: chunked"; http_header; metadata:impact_flag red, policy balanced-ips drop, policy security-ips drop, ruleset community, service http; reference:url,www.virustotal.com/en/file/e0290c3900445dc00ca24888924e37fa6ac17ecaddc60591e32b81536b9f5ef7/analysis/; classtype:trojan-activity; sid:32607; rev:2;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 14254 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - previous keyword has a fast_pattern:only; set. Can't have relative keywords around a fast_pattern only content <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $HOME_NET any -> $EXTERNAL_NET $HTTP_PORTS (msg:"MALWARE-CNC Win.Trojan.Teabevil variant outbound connection"; flow:to_server,established; content:"&syspath="; fast_pattern:only; content:"/script"; http_uri; urilen:7; content:"CONTENT-TYPE:"; http_header; content:"&macid="; nocase; http_client_body; content:"&os1="; distance:0; nocase; http_client_body; content:"&os2="; distance:0; nocase; http_client_body; content:"&syspath="; distance:0; nocase; http_client_body; metadata:impact_flag red, policy balanced-ips drop, policy security-ips drop, service http; reference:url,virustotal.com/en/file/9bcf7fbd2123d7085ce5e3e699c9347c48f4c2ec6f26371852a01cf597a96968/analysis/; classtype:trojan-activity; sid:36630; rev:2;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 14743 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - previous keyword has a fast_pattern:only; set. Can't have relative keywords around a fast_pattern only content <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $HOME_NET any -> $EXTERNAL_NET $HTTP_PORTS (msg:"MALWARE-CNC Win.Trojan.Teabevil variant outbound connection"; flow:to_server,established; content:"&vs="; fast_pattern:only; content:"/script"; http_uri; urilen:7; content:"CONTENT-TYPE:"; http_header; content:"v="; nocase; http_client_body; content:"&id="; distance:0; nocase; http_client_body; content:"&uid="; distance:0; nocase; http_client_body; content:"&vs="; distance:0; nocase; http_client_body; metadata:impact_flag red, policy balanced-ips drop, policy security-ips drop, service http; reference:url,virustotal.com/en/file/9bcf7fbd2123d7085ce5e3e699c9347c48f4c2ec6f26371852a01cf597a96968/analysis/; classtype:trojan-activity; sid:36629; rev:2;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 14744 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - previous keyword has a fast_pattern:only; set. Can't have relative keywords around a fast_pattern only content <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $HOME_NET any -> $EXTERNAL_NET $HTTP_PORTS (msg:"MALWARE-CNC Win.Trojan.GateKeylogger initial exfiltration attempt"; flow:to_server,established; content:"/gate.php"; fast_pattern:only; content:"pc="; nocase; http_client_body; content:"&admin="; distance:0; nocase; http_client_body; content:"&os="; distance:0; nocase; http_client_body; content:"&hid="; distance:0; nocase; http_client_body; content:"&arc="; distance:0; nocase; http_client_body; content:"User-Agent|3A 20|"; http_header; pcre:"/User-Agent\x3a\x20[A-F0-9]{32}\x0d\x0a/H"; metadata:impact_flag red, policy balanced-ips drop, policy security-ips drop, ruleset community, service http; reference:url,attack.mitre.org/techniques/T1020; reference:url,attack.mitre.org/techniques/T1056; reference:url,www.virustotal.com/en/file/77c802db1731fa8dae1b03d978f89b046309adfa1237b1497a69ccb9c2d82c16/analysis/1459520578/; classtype:trojan-activity; sid:38562; rev:3;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 14880 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - previous keyword has a fast_pattern:only; set. Can't have relative keywords around a fast_pattern only content <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $HOME_NET any -> $EXTERNAL_NET $HTTP_PORTS (msg:"MALWARE-CNC Win.Trojan.Helminth variant outbound connection"; flow:to_server,established; content:"UIET9fWR"; fast_pattern:only; content:"User-Agent: Mozilla/5.0"; http_header; content:"|20|Trident/5.0|0D 0A|"; within:14; distance:39; http_header; metadata:impact_flag red, policy balanced-ips drop, policy security-ips drop, service http; reference:url,www.virustotal.com/en/file/632be0a3d8d298f2ded928a4ac27846904ed842ad08b355acab53132d31eaf24/analysis/; classtype:trojan-activity; sid:39176; rev:1;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 14935 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - previous keyword has a fast_pattern:only; set. Can't have relative keywords around a fast_pattern only content <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $HOME_NET any -> $EXTERNAL_NET $HTTP_PORTS (msg:"MALWARE-CNC Osx.Trojan.OceanLotus outbound connection attempt"; flow:to_server,established; content:"/sigstore.db?"; fast_pattern:only; content:"k="; http_uri; content:"?q="; distance:0; http_uri; metadata:impact_flag red, policy balanced-ips drop, policy security-ips drop, ruleset community, service http; reference:url,www.alienvault.com/blogs/labs-research/oceanlotus-for-os-x-an-application-bundle-pretending-to-be-an-adobe-flash-update; classtype:trojan-activity; sid:45400; rev:1;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 15420 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - depth or urilen 11 smaller than content len 17 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $HOME_NET any -> $EXTERNAL_NET $HTTP_PORTS (msg:"MALWARE-CNC Win.Trojan.Scranos variant outbound connection"; flow:to_server,established; content:"/fb/apk/index.php"; fast_pattern:only; http_uri; urilen:<10; metadata:impact_flag red, policy balanced-ips drop, policy max-detect-ips drop, policy security-ips drop, service http; reference:url,www.virustotal.com/gui/url/02736e4c0b9fe923602cfe739f05d82c7141fd36581b3dc7cec65cf20f9cc1a0/detection; classtype:trojan-activity; sid:50525; rev:1;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 16183 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - previous keyword has a fast_pattern:only; set. Can't have relative keywords around a fast_pattern only content <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET $HTTP_PORTS -> $HOME_NET any (msg:"MALWARE-OTHER Win.Trojan.Zeus Spam 2013 dated zip/exe HTTP Response - potential malware download"; flow:to_client,established; content:"-2013.zip|0D 0A|"; fast_pattern:only; content:"-2013.zip|0D 0A|"; http_header; content:"-"; within:1; distance:-14; http_header; file_data; content:"-2013.exe"; content:"-"; within:1; distance:-14; metadata:impact_flag red, policy balanced-ips drop, policy max-detect-ips drop, policy security-ips drop, ruleset community, service http; reference:url,www.virustotal.com/en/file/2eff3ee6ac7f5bf85e4ebcbe51974d0708cef666581ef1385c628233614b22c0/analysis/; classtype:trojan-activity; sid:26470; rev:2;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 16364 <Error> -- [ERRCODE: SC_ERR_PCRE_PARSE(7)] - parse error, ret -1, string 1,=,3,0,relative,bitmask 0xF0 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET $FILE_DATA_PORTS -> $HOME_NET any (msg:"OS-OTHER Intel x64 side-channel analysis information leak attempt"; flow:to_client,established; file_data; flowbits:isset,file.exe|file.elf; content:"|0F 01 F9|"; content:"|0F 01 F9|"; within:50; content:"|0F AE|"; byte_test:1,=,3,0,relative,bitmask 0xF0; content:"|0F AE|"; within:75; byte_test:1,=,3,0,relative,bitmask 0xF0; metadata:policy balanced-ips drop, policy max-detect-ips drop, policy security-ips drop, service ftp-data, service http, service imap, service pop3; reference:cve,2017-5715; reference:cve,2017-5753; reference:cve,2017-5754; classtype:attempted-recon; sid:45444; rev:2;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 16918 <Error> -- [ERRCODE: SC_ERR_PCRE_PARSE(7)] - parse error, ret -1, string 1,=,3,0,relative,bitmask 0xF0 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET any -> $SMTP_SERVERS 25 (msg:"OS-OTHER Intel x64 side-channel analysis information leak attempt"; flow:to_server,established; file_data; flowbits:isset,file.exe|file.elf; content:"|0F 01 F9|"; content:"|0F 01 F9|"; within:50; content:"|0F AE|"; byte_test:1,=,3,0,relative,bitmask 0xF0; content:"|0F AE|"; within:75; byte_test:1,=,3,0,relative,bitmask 0xF0; metadata:policy balanced-ips drop, policy max-detect-ips drop, policy security-ips drop, service smtp; reference:cve,2017-5715; reference:cve,2017-5753; reference:cve,2017-5754; classtype:attempted-recon; sid:45443; rev:2;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 16919 <Error> -- [ERRCODE: SC_ERR_RULE_KEYWORD_UNKNOWN(102)] - unknown rule keyword 'byte_math'. <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp any any -> $HOME_NET 445 (msg:"OS-WINDOWS Microsoft Windows Trans Secondary kernel address write attempt"; flow:to_server,established; content:"|FF|SMB|26 00 00 00 00|"; depth:9; offset:4; content:"|08 00|"; within:2; distance:34; byte_math:bytes 2,offset 0,oper +,rvalue 8, result data_Offset,relative,endian little; byte_test:4,>=,0xffff0800,data_Offset,little; metadata:policy balanced-ips drop, policy max-detect-ips drop, policy security-ips drop, service netbios-ssn; classtype:attempted-admin; sid:50628; rev:2;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 17393 <Error> -- [ERRCODE: SC_ERR_RULE_KEYWORD_UNKNOWN(102)] - unknown rule keyword 'byte_math'. <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET any -> $HOME_NET 4786 (msg:"SERVER-OTHER Cisco Smart Install invalid init discovery message denial of service attempt"; flow:to_server,established; content:"|00 00 00|"; depth:3; content:"|00 00 00 07|"; within:4; distance:5; fast_pattern; content:"|00 00 00 01|"; within:4; distance:4; byte_math:bytes 4,offset 0,oper +,rvalue 8,result sub_len_plus_eight,relative; byte_test:4,!=,sub_len_plus_eight,-8,relative; metadata:policy balanced-ips drop, policy connectivity-ips drop, policy max-detect-ips drop, policy security-ips drop; reference:cve,2018-0171; reference:url,tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20180328-smi2; classtype:attempted-dos; sid:46468; rev:1;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 17810 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - Can't use file_data with flow:to_server or flow:from_client with http. <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET any -> $HOME_NET 8500 (msg:"SERVER-OTHER Hashicorp Consul services API remote code execution attempt"; flow:to_server,established; content:"/v1/agent/service/register"; fast_pattern:only; http_uri; content:"PUT"; http_method; file_data; content:"check"; content:"script"; within:25; metadata:policy balanced-ips drop, policy max-detect-ips drop, policy security-ips drop, service http; reference:url,www.rapid7.com/db/modules/exploit/multi/misc/consul_service_exec; classtype:attempted-admin; sid:49670; rev:2;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 17829 <Error> -- [ERRCODE: SC_ERR_PCRE_PARSE(7)] - parse error, ret -1, string 2,=,0,1,relative,little,bitmask 0x8000 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp any any -> $HOME_NET 445 (msg:"SERVER-SAMBA Samba is_known_pipe arbitrary module load code execution attempt"; flow:to_server,established; flowbits:isset,smb.tree.connect.ipc; content:"|FF|SMB|A2 00 00 00 00|"; depth:9; offset:4; byte_test:2,=,0,1,relative,little,bitmask 0x8000; byte_extract:2,72,len,relative,little; content:"/"; within:1; content:"/"; within:len; distance:1; metadata:policy balanced-ips drop, policy max-detect-ips drop, policy security-ips drop, ruleset community, service netbios-ssn; reference:cve,2017-7494; reference:url,www.samba.org/samba/security/CVE-2017-7494.html; classtype:attempted-user; sid:43004; rev:5;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 17835 <Error> -- [ERRCODE: SC_ERR_PCRE_PARSE(7)] - parse error, ret -1, string 1,=,0x05,6,relative,bitmask 0x14 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET any -> $HOME_NET 445 (msg:"SERVER-SAMBA Samba unsigned connections attempt"; flow:to_server, established; content:"|FF|SMB"; depth:4; offset:4; byte_test:1,=,0x05,6,relative,bitmask 0x14; content:"|00 00 00 00 00 00 00 00|"; within:8; distance:10; metadata:policy balanced-ips drop, policy max-detect-ips drop, policy security-ips drop; reference:cve,2017-12150; reference:url,samba.org/samba/security/CVE-2017-12150.html; classtype:attempted-user; sid:45074; rev:3;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 17836 <Error> -- [ERRCODE: SC_ERR_PCRE_PARSE(7)] - parse error, ret -1, string 1,=,1,2,relative,bitmask 0x01 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET any -> $HOME_NET 445 (msg:"SERVER-SAMBA Samba tree connect andx memory corruption attempt"; flow:to_server,established; content:"|FF|SMB|75|"; fast_pattern:only; content:"|04 75 00|"; byte_test:1,=,1,2,relative,bitmask 0x01; metadata:policy balanced-ips drop, policy max-detect-ips drop, policy security-ips drop; reference:cve,2017-14746; classtype:attempted-user; sid:45255; rev:2;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 17837 <Error> -- [ERRCODE: SC_ERR_PCRE_PARSE(7)] - parse error, ret -1, string 2,=,1,1,relative,little,bitmask 0x8000 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp any any -> $HOME_NET 445 (msg:"SERVER-SAMBA Samba is_known_pipe arbitrary module load code execution attempt"; flow:to_server,established; flowbits:isset,smb.tree.connect.ipc; content:"|FF|SMB|A2 00 00 00 00|"; depth:9; offset:4; byte_test:2,=,1,1,relative,little,bitmask 0x8000; byte_extract:2,72,len,relative,little; content:"/"; within:2; content:"/"; within:len; distance:2; metadata:policy balanced-ips drop, policy max-detect-ips drop, policy security-ips drop, ruleset community, service netbios-ssn; reference:cve,2017-7494; reference:url,www.samba.org/samba/security/CVE-2017-7494.html; classtype:attempted-user; sid:49090; rev:1;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 17838 <Error> -- [ERRCODE: SC_ERR_RULE_KEYWORD_UNKNOWN(102)] - unknown rule keyword 'http_raw_cookie'. <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET any -> $HOME_NET $HTTP_PORTS (msg:"SERVER-WEBAPP Multiple products DVR admin password leak attempt"; flow:to_server,established; content:"/device.rsp"; fast_pattern:only; http_uri; content:"uid="; http_raw_cookie; content:"cmd=list"; metadata:policy balanced-ips drop, policy max-detect-ips drop, policy security-ips drop, service http; reference:cve,2018-9995; classtype:web-application-attack; sid:46825; rev:1;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 18090 <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - previous keyword has a fast_pattern:only; set. Can't have relative keywords around a fast_pattern only content <Error> -- [ERRCODE: SC_ERR_INVALID_SIGNATURE(39)] - error parsing signature "alert tcp $EXTERNAL_NET any -> $HOME_NET $HTTP_PORTS (msg:"SERVER-WEBAPP Citrix ADC and Gateway arbitrary code execution attempt"; flow:to_server,established; content:"/vpns/"; fast_pattern:only; content:"NSC_USER:"; http_raw_header; content:"../"; within:10; http_raw_header; metadata:policy balanced-ips drop, policy connectivity-ips drop, policy max-detect-ips drop, policy security-ips drop, ruleset community, service http; reference:cve,2019-19781; reference:url,support.citrix.com/article/CTX267027; classtype:web-application-attack; sid:52620; rev:1;)" from file /usr/local/etc/suricata/suricata_47597_igb0/rules/suricata.rules at line 18163 <Info> -- 2 rule files processed. 18599 rules successfully loaded, 36 rules failed <Warning> -- [ERRCODE: SC_ERR_EVENT_ENGINE(210)] - can't suppress sid 2000419, gid 1: unknown rule <Info> -- Threshold config parsed: 1 rule(s) found <Info> -- 18600 signatures processed. 52 are IP-only rules, 3530 are inspecting packet payload, 8732 inspect application layer, 103 are decoder event only <Warning> -- [ERRCODE: SC_WARN_FLOWBIT(306)] - flowbit 'file.zip&file.silverlight' is checked but not set. Checked in 28579 and 6 other sigs <Warning> -- [ERRCODE: SC_WARN_FLOWBIT(306)] - flowbit 'file.swf|file.ole' is checked but not set. Checked in 25676 and 1 other sigs <Warning> -- [ERRCODE: SC_WARN_FLOWBIT(306)] - flowbit 'file.class|file.jar' is checked but not set. Checked in 31540 and 1 other sigs <Warning> -- [ERRCODE: SC_WARN_FLOWBIT(306)] - flowbit 'file.tiff|file.doc' is checked but not set. Checked in 28464 and 1 other sigs <Warning> -- [ERRCODE: SC_WARN_FLOWBIT(306)] - flowbit 'file.rtf|file.ole' is checked but not set. Checked in 37559 and 1 other sigs <Warning> -- [ERRCODE: SC_WARN_FLOWBIT(306)] - flowbit 'file.doc|file.docx' is checked but not set. Checked in 45370 and 1 other sigs <Warning> -- [ERRCODE: SC_WARN_FLOWBIT(306)] - flowbit 'file.ole|file.doc' is checked but not set. Checked in 30533 and 3 other sigs <Warning> -- [ERRCODE: SC_WARN_FLOWBIT(306)] - flowbit 'file.corel|file.doc' is checked but not set. Checked in 36500 and 1 other sigs <Warning> -- [ERRCODE: SC_WARN_FLOWBIT(306)] - flowbit 'file.pdf&file.ttf' is checked but not set. Checked in 28585 and 1 other sigs <Warning> -- [ERRCODE: SC_WARN_FLOWBIT(306)] - flowbit 'file.doc|file.rtf' is checked but not set. Checked in 45519 and 2 other sigs <Warning> -- [ERRCODE: SC_WARN_FLOWBIT(306)] - flowbit 'file.xls&file.ole' is checked but not set. Checked in 30990 and 1 other sigs <Warning> -- [ERRCODE: SC_WARN_FLOWBIT(306)] - flowbit 'file.doc|file.xls' is checked but not set. Checked in 44559 and 1 other sigs <Warning> -- [ERRCODE: SC_WARN_FLOWBIT(306)] - flowbit 'file.pyc|file.zip' is checked but not set. Checked in 45477 and 1 other sigs <Warning> -- [ERRCODE: SC_WARN_FLOWBIT(306)] - flowbit 'file.doc|file.docm' is checked but not set. Checked in 43975 and 1 other sigs <Warning> -- [ERRCODE: SC_WARN_FLOWBIT(306)] - flowbit 'et.http.PK' is checked but not set. Checked in 2019835 and 1 other sigs <Info> -- Using 2 live device(s). <Notice> -- opened netmap:igb0/R from igb0: 0x8130c9000 <Notice> -- opened netmap:igb0^ from igb0^: 0x8130c9300 <Notice> -- opened netmap:igb0^ from igb0^: 0x8134c9000 <Notice> -- opened netmap:igb0/T from igb0: 0x8134c9300 <Notice> -- all 6 packet processing threads, 2 management threads initialized, engine started. -
It is common for the Snort Subscriber Rules to generate errors in Suricata. Search this forum here for other posts about this. Suricata is not Snort. It does not process nor understand all of the Snort rule directives and keywords. For those it does not understand or support, it spits out an error like you see and discards that rule (so that rule is not loaded). Not all the Snort rules will fail, but several hundred will fail (I forget the actual number). Exactly how many fail for you depends on which particular categories and rules you enable (or that get enabled by choosing a Snort IPS Policy).
Emerging Threats has an optimized Suricata ruleset. The Suricata package loads those optimized ET rules when you enable ET rules. Unfortunately, the free ET rules are more limited. The paid ET rules (ET-Pro) which are up-to-date are way more expensive than the Snort rules. Last I checked the ET-Pro rules were $832 per year per device. Compare that to the Snort Subscriber Rules which cost $30 per year for an individual (non-business subscription). There is no corresponding individual subscription for ET-Pro.
Your flowbit errors are likely due to the failure of other dependent rules to load. You can't do anything about this when you run Snort rules with Suricata. This is one of the limitations of Suricata in my view for small non-business users. The only affordable rules packages are not complete in their coverage. Even when you use Snort Rules, several of them won't load in Suricata.
You may be better served to switch to Snort and use the paid Snort Subscriber Rules; unless you have the coin to pay Proofpoint $832 a year for an Emerging Threats Pro subscription.