OpenVPN TAP Issues
-
So, I have an odd issue with OpenVPN while configuring a TAP interface. Before you all say it.....I KNOW TAP configurations are generally discouraged, but in this particular case the only option is a TAP interface.
Back story why I need TAP: There is a Site-to-Site IPSec VPN tunnel that has my LAN network NAT'ed to a different subnet with another company for our accounting software to work. This accounting software can also work over their Cisco AnyConnect VPN software, but that VPN is not a split tunnel and the company providing it refuses to change it to one. As such, my users can't use the software because some resources exist on my LAN on a SMB host for the software and others exist on an SMB host on the other company's network. If clients are bridged to my LAN while on the VPN vs. using a private network, they can access these resources because they're connecting as if on my LAN and the NAT for the IPSec tunnel and everything works just fine.
Now on to my issue: I setup everything per the instructions and spent several hours Googling to try and find a similar problem, but whenever someone connected to the OpenVPN TAP server, they get an IP address from the pool I setup in OpenVPN, but only one person can connect at a time. If someone else connects, they get the same IP address as the first person, the first person gets booted off the OpenVPN tunnel, and everything breaks. Then they keep fighting over that connection.
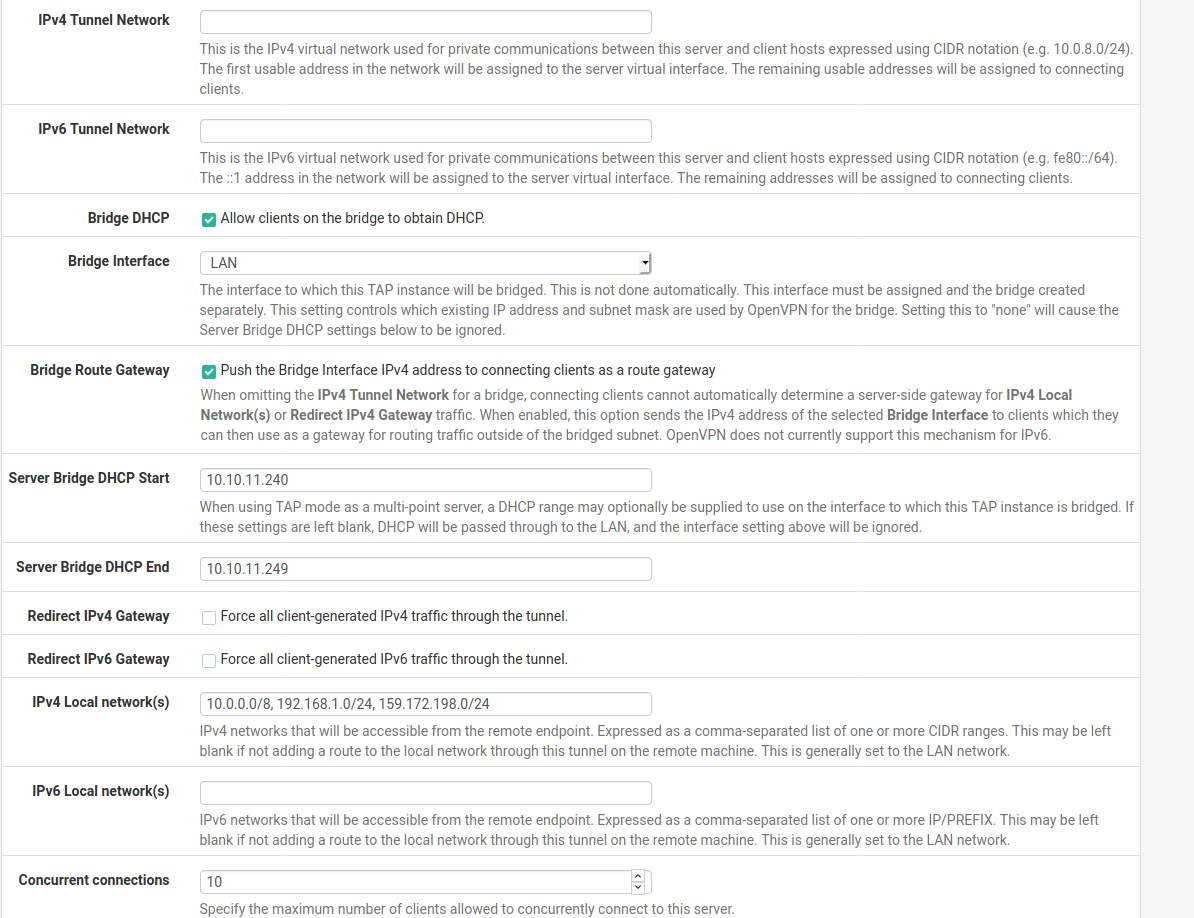
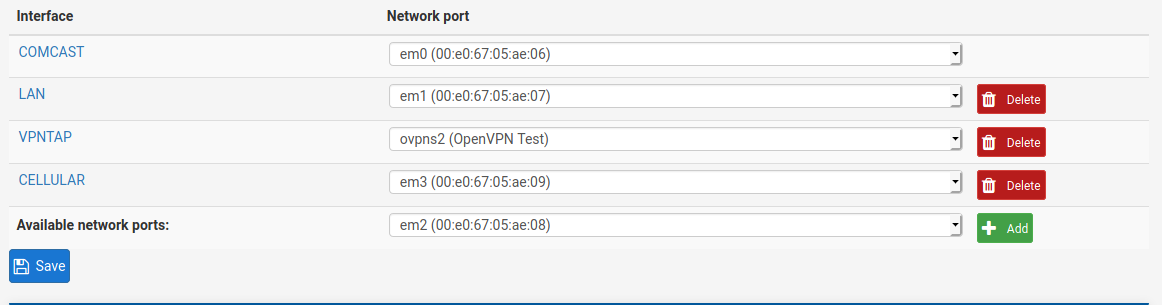
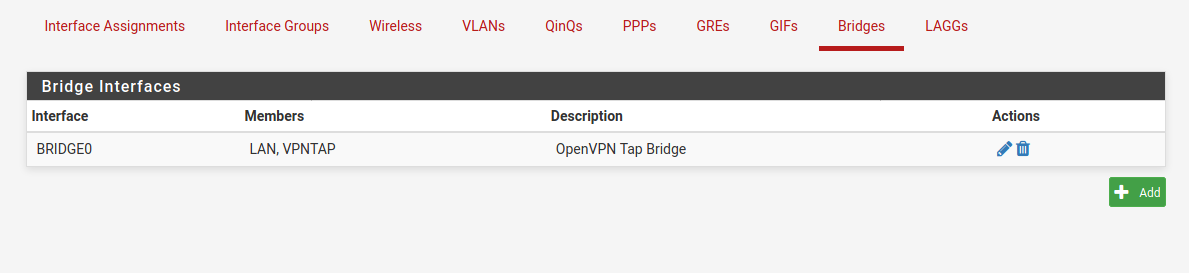
I'm using LDAP authentication to my Domain Controller for logging in. Below are my configuration screenshots from OpenVPN, my bridge interface, and my OpenVPN TAP interface that I assigned in interface assignments. If anyone has any ideas, I'd appreciate them very much.
-
What Server mode are you running, RA (SSL/TLS + User Auth) ?
I know of the problem with all clients getting the same IP address when sharing the same certificate in tun mode, I think in tap it's the same.
The screenshot is only showing a snip of your settings...-Rico
-
Yes. Using Remote Access (SSL/TLS + User Auth).
-
Ok so let me pull out of the nose... are your Users all share the same certificate?
-Rico
-
@Rico They are. I believe they have to with LDAP authentication. However, I had a TUN network setup this way as well and they all got unique IPs on my virtual subnet for the TUN network.
-
Try with the Server Option Duplicate Connections
But this is NOT recommended, you should use a unique Cert per User or switch to User Auth only.-Rico
-
I'll give it a shot. I was actually playing around with using a TUN network this morning and figured out how I can assign the same NAT'ed subnet to the TUN OpenVPN network, so I MIGHT have gotten it to work without messing with TAP at all. Fingers crossed.