Re: Good practice small IT office - questions
-
Re: What are the best practices to protect small IT Office?
Hi all,
I've recently aquired SG-5100 for a small office environment. I don't have an IT background so I'm learning as I go and enjoying it(most of the time
 ).
).
Good refferences found so far:
https://forum.netgate.com/topic/136577/what-are-the-best-practices-to-protect-small-it-office/2
https://forum.netgate.com/topic/70170/taming-the-beasts-aka-suricata-blueprint
https://docs.netgate.com/pfsense/en/latest/book/firewall/ingress-and-egress-filtering.htmlCould someone help me out with a few questions:
1.Which ports should I open for the different VPN clients that are running.
2. If I run all my traffic through a OpenVPN setup on pfsense can I not close most outgoing ports on my WAN? If so, which would need to stay open and why would those not go through the OpenVPN?
3. Would you expect outbound traffic on ports 23,264and389?Cheers
Walter -
1.: If you mean by that OpenVPN-Clients connecting to your pfSense appliance, you have the option to let pfSense automatically create the firewall rules for you. Default is UDP Port 1194 for OpenVPN.
2.: If you choose to route all traffic through OpenVPN (depends on your configuration), then all traffic goes through it. That'd be the most secure way, but also slower. You could only route some local subnets through OpenVPN, for example, if you want to. Tho, for business, I generally recommend forcing everything through the tunnel, this way you can make sure nothing's going somewhere it shouldn't.
Regarding outbound rules: Of course you could lock it down to only some ports being open, like DNS, NTP, HTTP(S), but that'll immensly limit what you can do, obviously. If that's what you want, go for it - but if you don't have a specific reason for it, rather don't. A proxy blocking access to certain websites would be more reasonable (again, depends on your usecase).3.: Port 23 is Telnet - as long as you don't connect via Telnet to anything outside your local network, no, that Port shouldn't be needed. Same goes for 389 (LDAP). I can't speak for 264, tho, since I'm not experienced with BGMP.
-
Thanks Tenou!
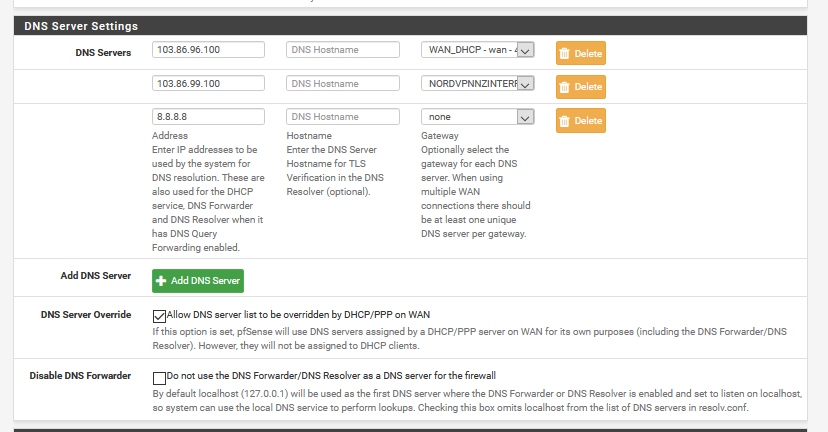
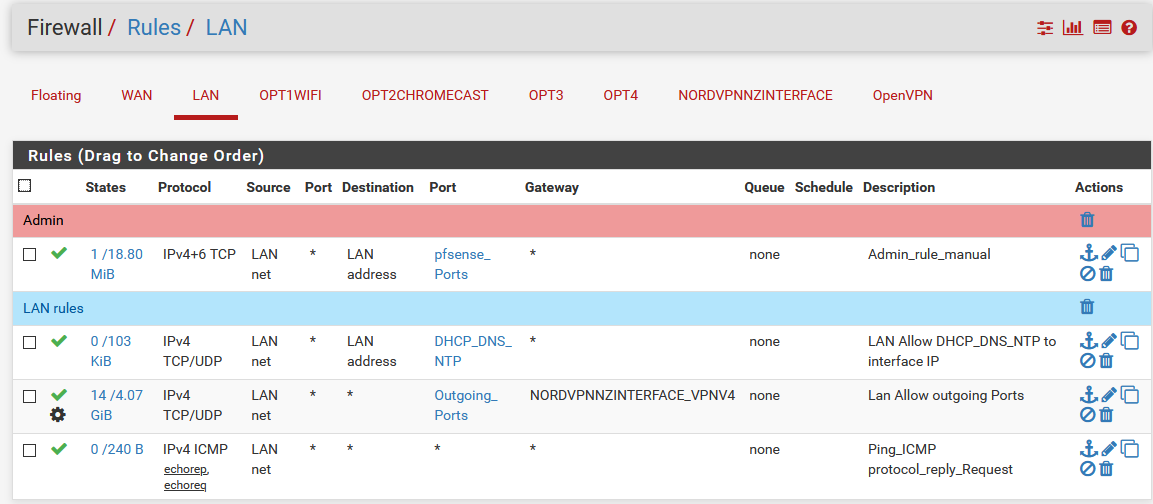
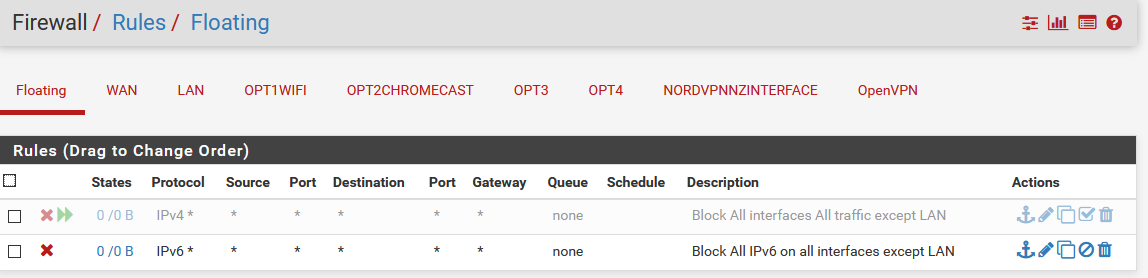
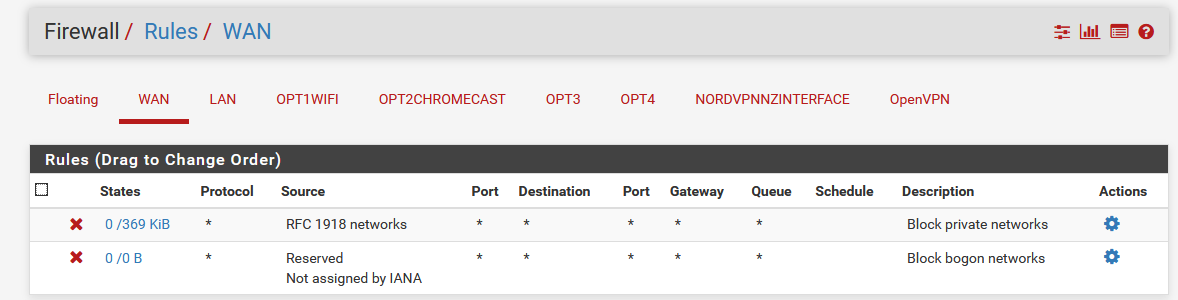
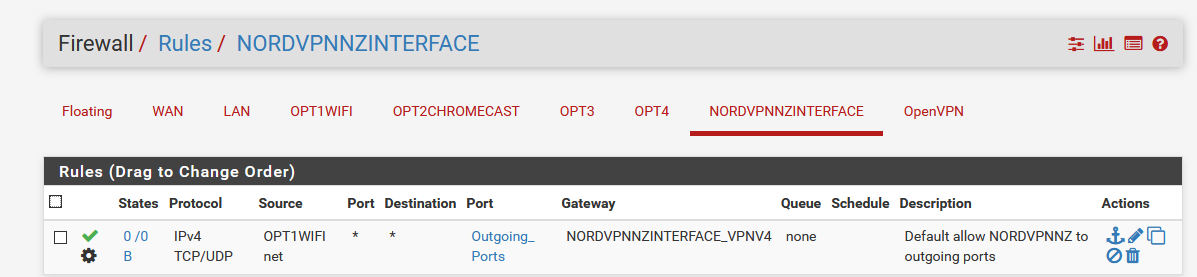
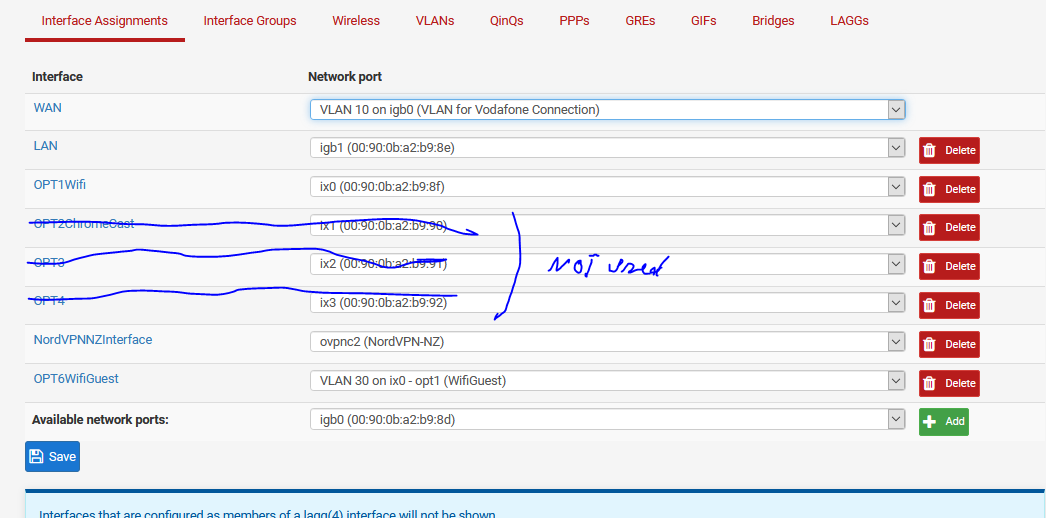
I've gotten a bit further. Everything should go through VPN except Chromecast. Here is my config currently. It is working well. Just not sure how well it is setup:
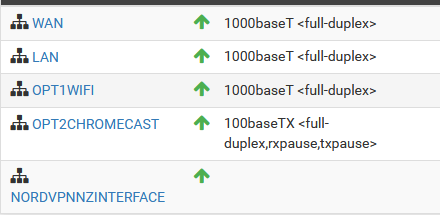
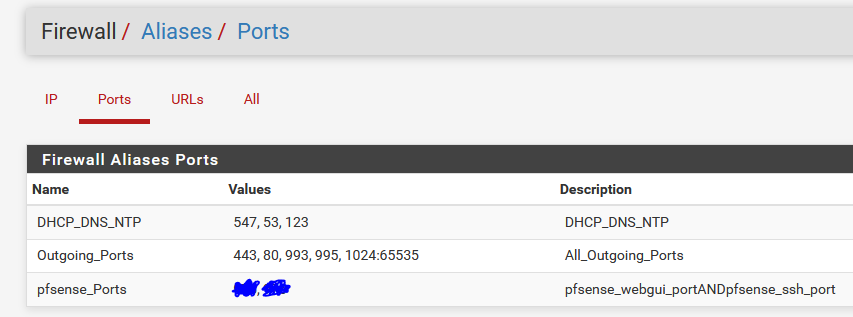
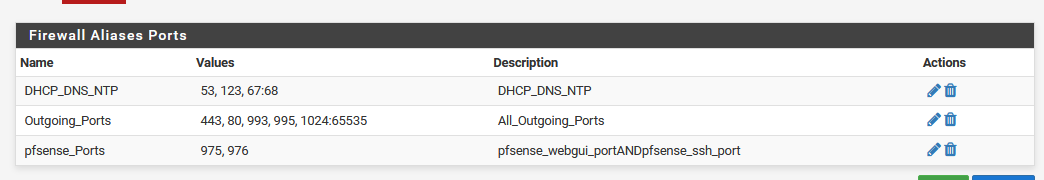
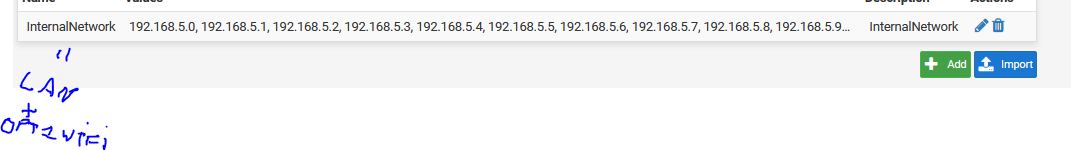
All interfaces relatively similar firewall settings
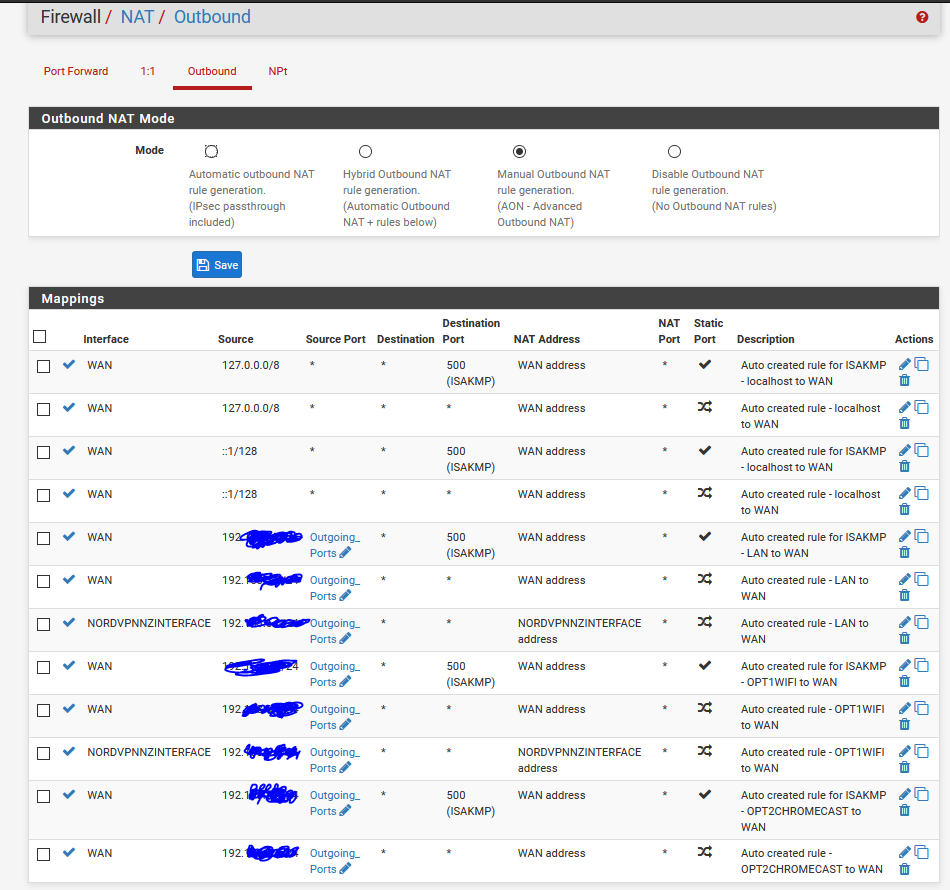
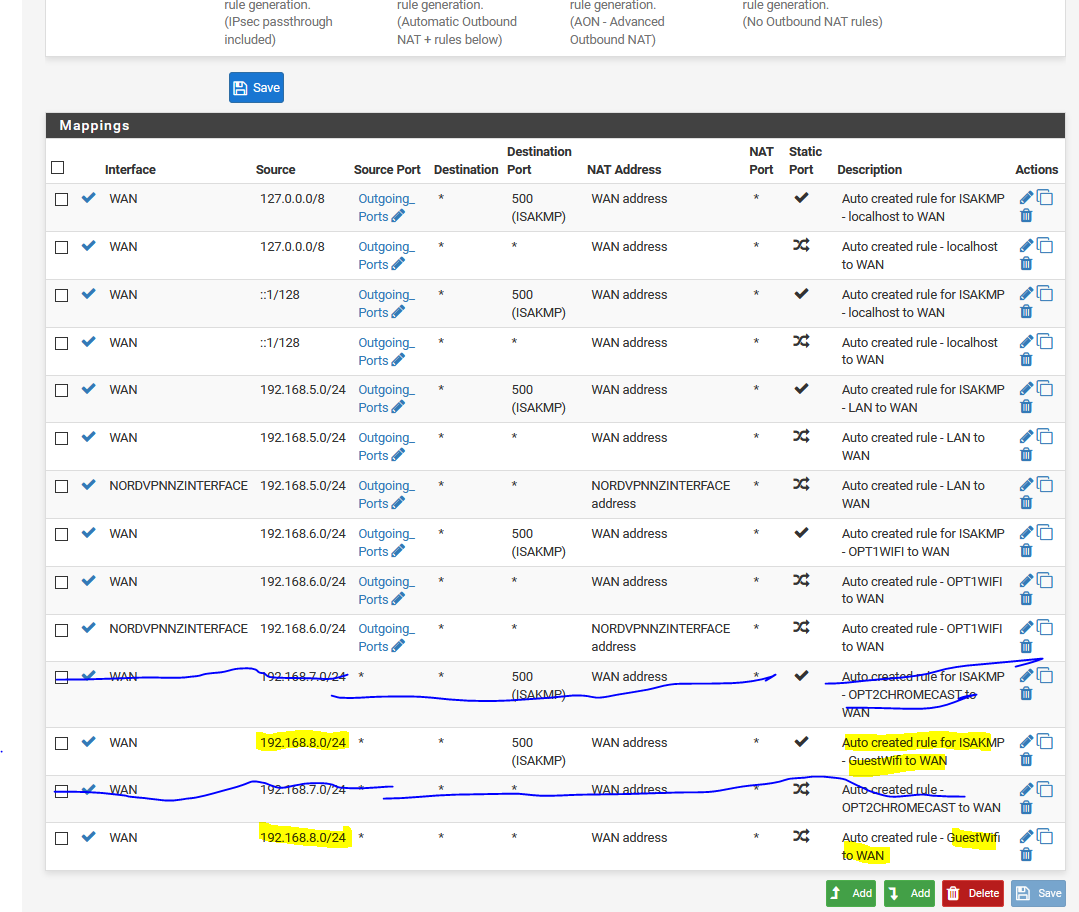
NAT:
I guess my questions are:
- What is still open what shouldn't be? Anything else wrong?
- Somehow my ping/tracert doesn't work anymore between interfaces. Firewall allows it. May be NAT that is the issue?
- Why do I need those first 4 NAT rules?
- Nex step in my mind is create 2 VLANs on Wifi. one guest and one other. Do I need to bridge the guest wifi VLAN network with Chromecast to make it work? Or would firewall settings do the trick?
Any advise is welcome :)
Cheers
Walter -
I don't know enough about the whole idea behind your networks, so I can't really comment on your first question. Sorry for that :/
In general it looks fine, however I've never needed to explicitly allow DHCP (you also only allowed DHCPv6, not v4?).
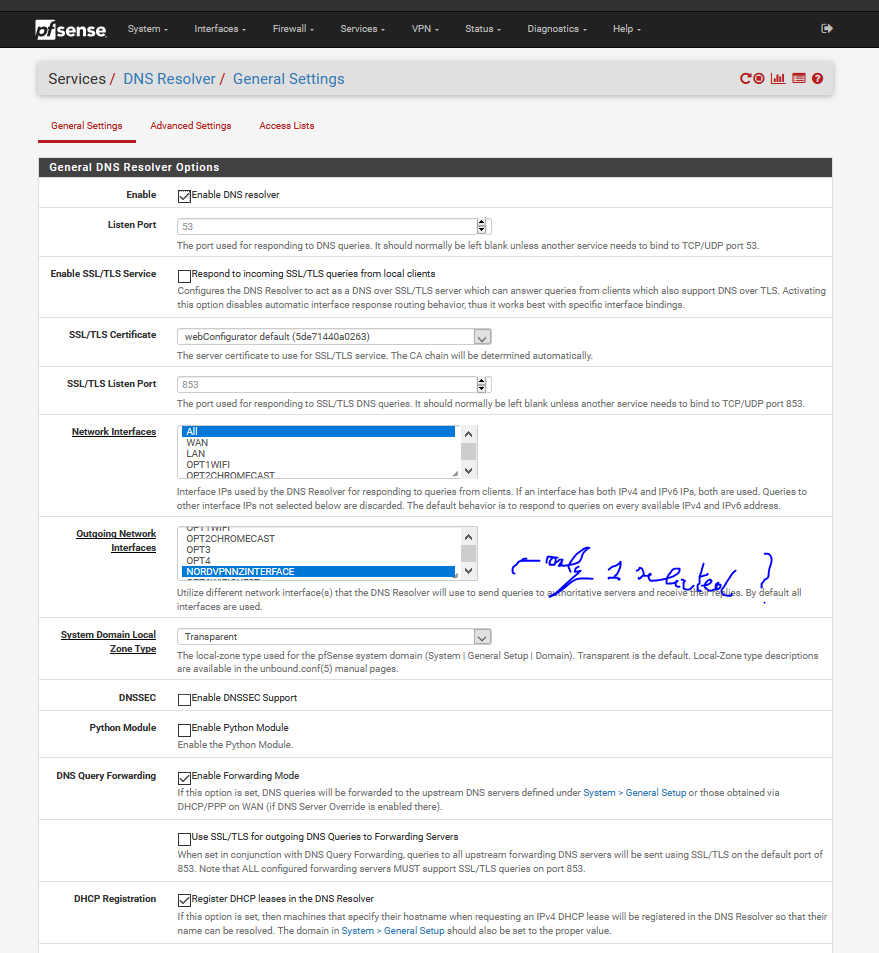
Regarding your Ping-Problem, are you trying to ping hostnames or IPs? Are all your Gateways, Subnet Masks and, eventually, DNS-Configs setup correctly? NAT shouldn't be a factor here, since it all stays internal.Those four Outbound NAT-Rule are better explained here than I could possibly manage it: Klick!
And regarding the last question: Chromecast heavily relies on Multicast, so it's not that easy to route between subnets. You essentially need a UDP Packet Broadcast Relay.
This has been done for Ubiquity (see this post) but I don't know about pfSense. Maybe it'll be helpful anyways. -
Thanks!! Almost there :)
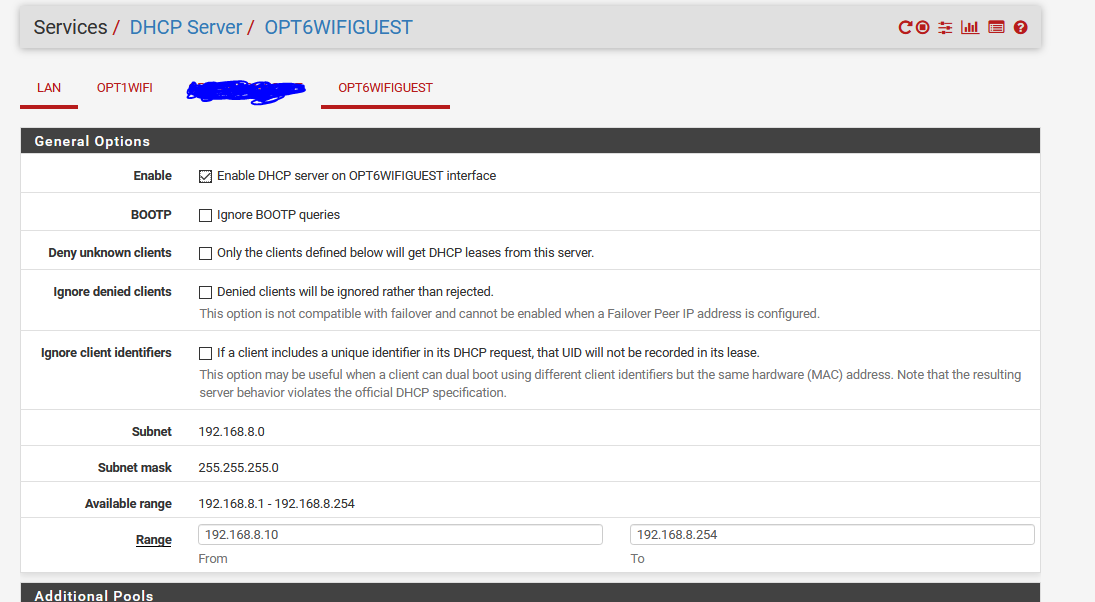
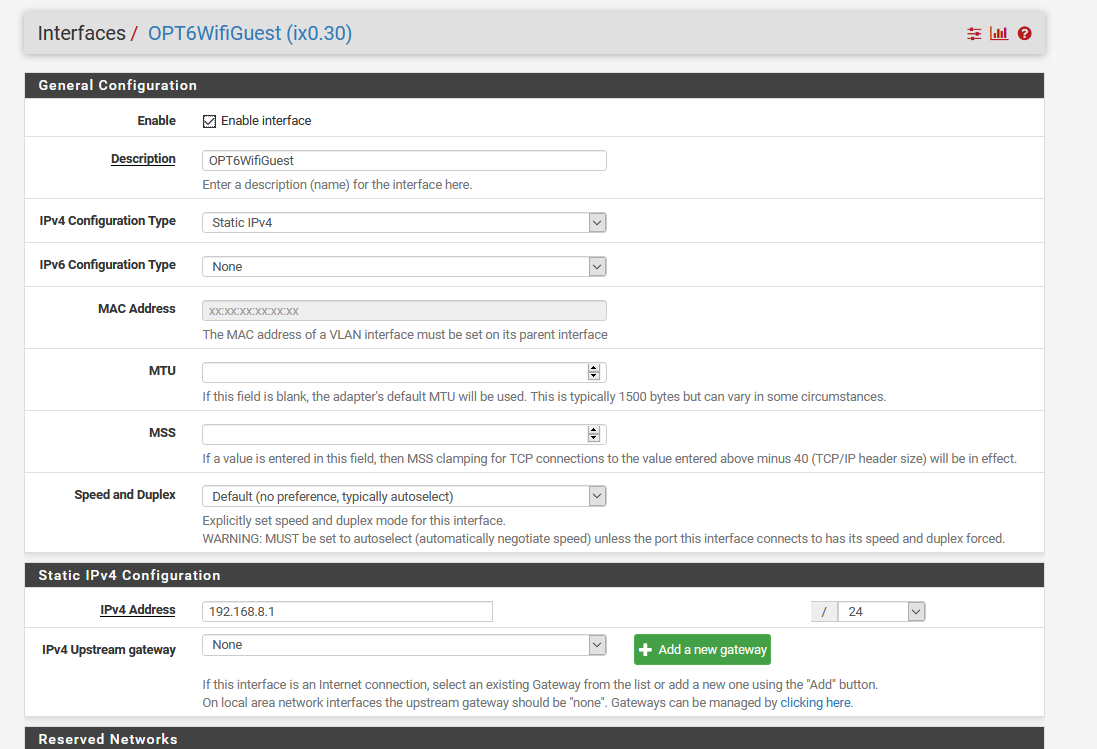
I've added a Guest Vlan on my wifi. I've got internet everywere.
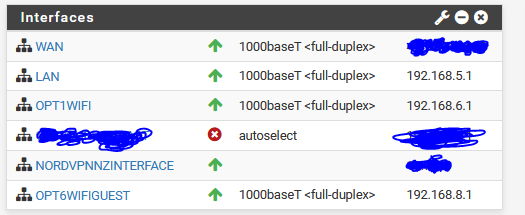
The idea is that LAN and OPT1WIFI all go over VPN gateway. My WIFIGUEST shoudn't since Netflix/chrome doesn't like it :) I have no issues with LAN and Opt1Wifi for what I'm using it.
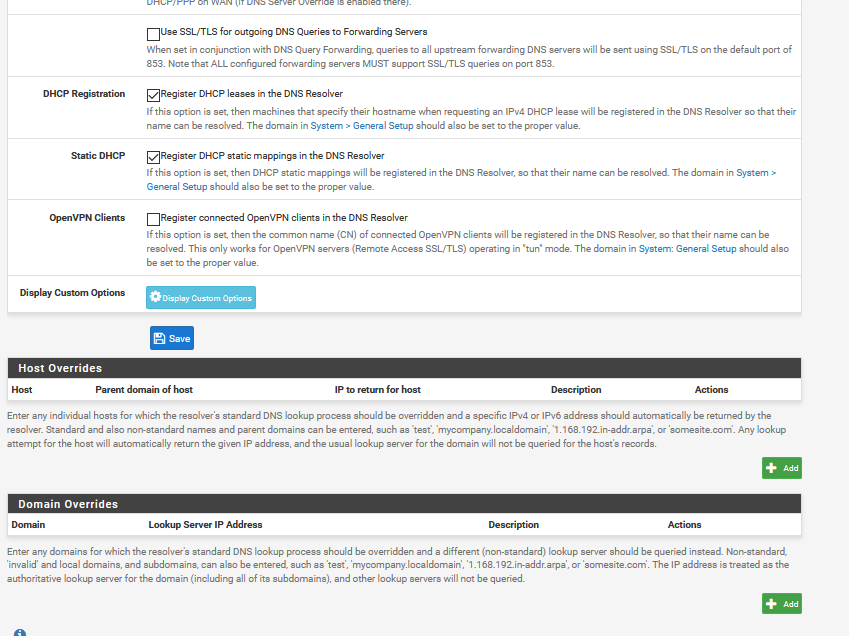
However apps like netflix and others don't load properly on the GuestWifi. I've openend up the Firewall more and restricted NAT less. Also just assume that cellphone and chrome are all on this network. In a later step i'll split it up using avahi package. So could this come from DNS? I'll give a bit better view of my setup:
 .
.
-
This post is deleted! -