Correct pfBlockerNG Set Up?
-
I've just been looking at the stats on the dashboard widget and I'm sure I must have something wrong based on what I'm seeing for the DNSBL stats?
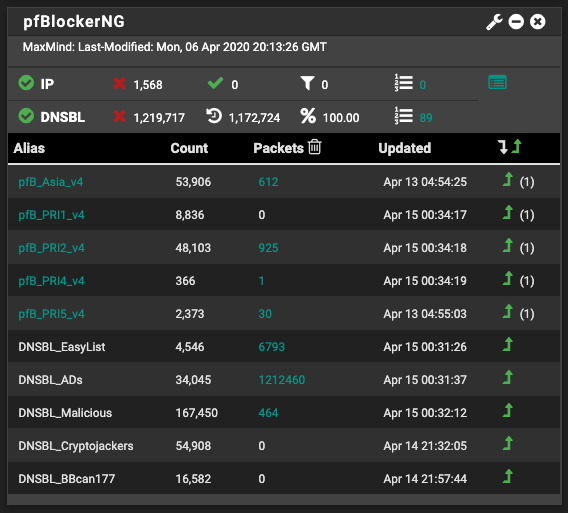
Does that look right, or have I got something in my set up wrong?
All other images I've seen, the % is much lower. I can still browse, ads are being blocked, but DNS resolution can take a few seconds to complete.
-
@WannabeMKII said in Correct pfBlockerNG Set Up?:
but DNS resolution can take a few seconds to complete.
That phrase can be rewritten as :
I completely overloaded the DSN Cache/resolver, and now is reacting somewhat slow.
I guess startup and restarts of unbound (DNS) will takes many seconds if not more, stopping all name resolution while doing so.
It's not possible to select all the DNSBL feeds. You have to limit your choice. Or use big Intel I9 / SSD's etc.
Up to you to balance your needs. -
@WannabeMKII said in Correct pfBlockerNG Set Up?:
I've just been looking at the stats on the dashboard widget and I'm sure I must have something wrong based on what I'm seeing for the DNSBL stats?
Does that look right, or have I got something in my set up wrong?
You screen shot looks similar to mine as far as DNSBL feeds go. You can let it reset the stats at what ever interval you chose or never reset which looks like what you are doing. No matter what the stats are doesn't mean it's not blocking things like you want it to.
-
@Gertjan said in Correct pfBlockerNG Set Up?:
@WannabeMKII said in Correct pfBlockerNG Set Up?:
but DNS resolution can take a few seconds to complete.
That phrase can be rewritten as :
I completely overloaded the DSN Cache/resolver, and now is reacting somewhat slow.
Ah OK, so I've clearly set things up wrong.
I guess startup and restarts of unbound (DNS) will takes many seconds if not more, stopping all name resolution while doing so.
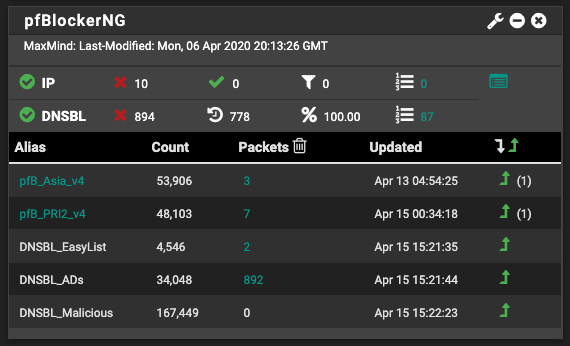
That makes sense, as I've just seen the restarting of the process in the logs.
It's not possible to select all the DNSBL feeds. You have to limit your choice. Or use big Intel I9 / SSD's etc.
Up to you to balance your needs.So is the issue the hardware? From the reviews I read before purchasing the SG-1100, I thought it would be more than capable to support, what I thought, were modest requirements. I see people running Snort or Suricata on the hardware and surely that's more hardware intensive?
In that case, what would you recommend for the hardware I have?
-
@WannabeMKII said in Correct pfBlockerNG Set Up?:
SG-1100
I'm amazed.
You are running this one : SG-1100 showing this :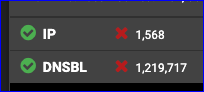
I'm impressed.
I don't own one, but I'll buy one of these SG-1100 ones.
But, the processor driving it is "smaller" as my smartphone.So, loading up a DNS look-up file with several megabytes of text host names is a no-no.
Recommanded hardware to put pfBlocker to the max ?
As said : https://store.netgate.com/pfSense/systems.aspx - go to the bottom of the page. -
OK, I've trimmed down the number of lists used. Does this look more reasonable?
Is there a general rule or guide of what hardware can support what, as I'm loving pfsense so far, but if I want it to 'do more', I'm guessing I'm going to have to up the hardware. Also, can the setting be saved and restored to new hardware?
-
I've just checked the logs and even with the list trimmed down, unbound appears to be restarting about every 1 minute?
Is there something else wrong here?
-
If you have a big network, or some stupid rogue device that asks a new DHCP lease every minute,
and this setting active :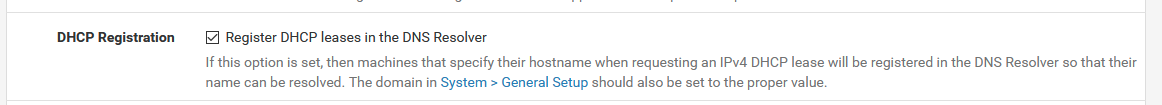
then yes.
All goes as planned.
Sort of.Having restarting unbound every xxx seconds is very counter productive.
It's worth spending some time to discover why .....
See you back here after that complete study of your logs.
-
@Gertjan said in Correct pfBlockerNG Set Up?:
If you have a big network, or some stupid rogue device that asks a new DHCP lease every minute,
and this setting active :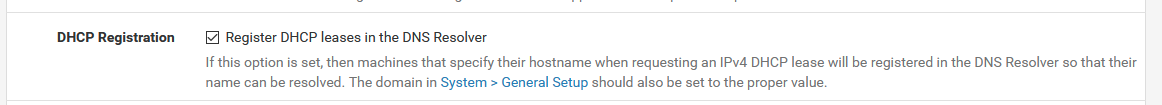
Ah ha, I did this about 10 minutes ago after reading about it on the forum and it's not restarted since.
then yes.
All goes as planned.
Sort of.Having restarting unbound every xxx seconds is very counter productive.
It's worth spending some time to discover why .....
See you back here after that complete study of your logs.
I've then checked the logs and I've found a device that is showing in the DHCP logs every 1 minute as DHCPOFFER. I'm guessing this is what's causing the issue? If so, is the resolution to reserve it an IP?
Many thanks for your continued help, much appreciated!!
-
@WannabeMKII said in Correct pfBlockerNG Set Up?:
I've then checked the logs and I've found a device that is showing in the DHCP logs every 1 minute as DHCPOFFER. I'm guessing this is what's causing the issue? If so, is the resolution to reserve it an IP?
A DHCPOFFER is an offer that the pfSense is sending after a DHCPDISCOVER, coming from a network client.
After the DHCPOFFER is received by the client, it will acknowledge with a DHCPREQUEST. Which is then granted with a DHCP..... from pfSense.
In that order.No other devices on your network should send out DHCPOFFER, If that happens, you have multiple DHCP servers on your network.
True, if some stupid device is actually REQUESTING a new lease, instaed of RENEWing it, then consider that device as pretty broken.
Assign it a Static DHCP lease (at least) or a classic static IP/Gateway/mask/DNS, or throw it out of the window (at bast). -
So the device in question was communication every minute! So I power cycled it and now it's behaving. I've also increased my lease time from 2 hours to 6 hours to limit the DHCP traffic as it's quite a settled environment, especially at the moment! I may eventually increase to 12 or even 24 hours...
Thanks again, I'll be back if I have any further issues, fingers crossed it's not soon!

-
If you absolutely need a client by name, reserve it an IP so its name will be known to unbound anyway and remove the setting that every dumb client will try to get its name into the DNS resolver - that will stop the endless restart orgy. Also your DNS cache gets lost every time that happens so not only it is restarting but getting slow every time it does. That's why you disable that option and if you really need a client to be known by its name (why should you?) get it a reservation via DHCP server. That is loaded into unbound per default - so no restarting after a dhcp registration. Also don't do that for OVPN clients, too. For obvious reasons :)
-
@JeGr said in Correct pfBlockerNG Set Up?:
If you absolutely need a client by name, reserve it an IP so its name will be known to unbound anyway and remove the setting that every dumb client will try to get its name into the DNS resolver - that will stop the endless restart orgy. Also your DNS cache gets lost every time that happens so not only it is restarting but getting slow every time it does. That's why you disable that option and if you really need a client to be known by its name (why should you?) get it a reservation via DHCP server. That is loaded into unbound per default - so no restarting after a dhcp registration. Also don't do that for OVPN clients, too. For obvious reasons :)
Superb advice! I've made the relevant changes and all seems well so far and nice and responsive, appreciated!
-
Actually, a quick question on this - Is there a way to add a client name to the resolver without adding an IP reservation and using just the MAC address? It's just useful when looking at the logs to have a meaningful hostname, or in some cases, just a hostname at all!
Many thanks.
-
@WannabeMKII said in Correct pfBlockerNG Set Up?:
to add a client name to the resolver without adding an IP reservation
There was a thread some time ago that asked for this.
Bassically, you're asking to have entered the device name in the DNS cache when it's DHCP-ing - before isn't possible : the IP isn't known.
You do understand that the DNS (unbound) has to be restarted to be aware of it, right ;)If your trusted devices network isn't that big, you static-mac all IP's (devices). This gives you also a nice formatted list will all your equipment on a page, known, even when they are not put on or available.
Other, more visitor like devices and untrusted devices should be put on a separate network. -
Thanks for the response.
50% of my network have reserved IP's anyway and other stuff is on a separate VLAN, it just to keep things looking nice. But it's all working fine as it is, was just a thought.
Many thanks once again!
-
@WannabeMKII said in Correct pfBlockerNG Set Up?:
Actually, a quick question on this - Is there a way to add a client name to the resolver without adding an IP reservation and using just the MAC address? It's just useful when looking at the logs to have a meaningful hostname, or in some cases, just a hostname at all!
Of course, just use the host override section of the DNS resolver.
-
@JeGr said in Correct pfBlockerNG Set Up?:
@WannabeMKII said in Correct pfBlockerNG Set Up?:
Actually, a quick question on this - Is there a way to add a client name to the resolver without adding an IP reservation and using just the MAC address? It's just useful when looking at the logs to have a meaningful hostname, or in some cases, just a hostname at all!
Of course, just use the host override section of the DNS resolver.
I did look at that, but that also needs static IP's to work unless I'm misunderstanding it?
-
That's what DNS is all about.
Throw in a host name, and get out an IP.
So, yes, these two should be known. -
@WannabeMKII said in Correct pfBlockerNG Set Up?:
Actually, a quick question on this - Is there a way to add a client name to the resolver without adding an IP reservation and using just the MAC address? It's just useful when looking at the logs to have a meaningful hostname, or in some cases, just a hostname at all!
Ah I didn't read the "MAC address" part. But why? If you want a specific Client (MAC) to have a name, give it a static or dhcp-reserved IP. Simple as that. Otherwise, no, you can't map MACs to DNS, that makes no sense as both are on different layers (MACs are on layer 2, IP is layer 3)