Segmenting between two physical LAN ports
-
Hi, I am using a Netgate SG1100 box, running pfsense 2.4.5. This box comes with three RJ-45 ports: WAN, LAN, and OPT. Until recently, I was only using the LAN and WAN ports, but now I am trying to put the OPT port to use, so as to segment my wireless devices (on OPT) from my wired devices (on LAN). The LAN port's firewall has been running with the default "allow all" rule from it to anywhere, thus enabling WAN (and now OPT) access. When I enabled the OPT port, I set a similar firewall rule, just to get it going. That worked fine. However, when I changed the rule to be "Allow all from OPT net to WAN net" everything was suddenly blocked. I couldn't access the firewall from the OPT port, nor the internet, nor the devices on the LAN port. So after tinkering around a bit more, I finally in desperation changed the rule to "allow all from OPT net to LAN net". And just like that, I could again access the Internet, the firewall, and all devices on the LAN port. The only catch is that for some reason, ICMP is being blocked, so while I can use HTTP/S, I can't ping anything. (For the record, I have never set any blocks on ICMP)
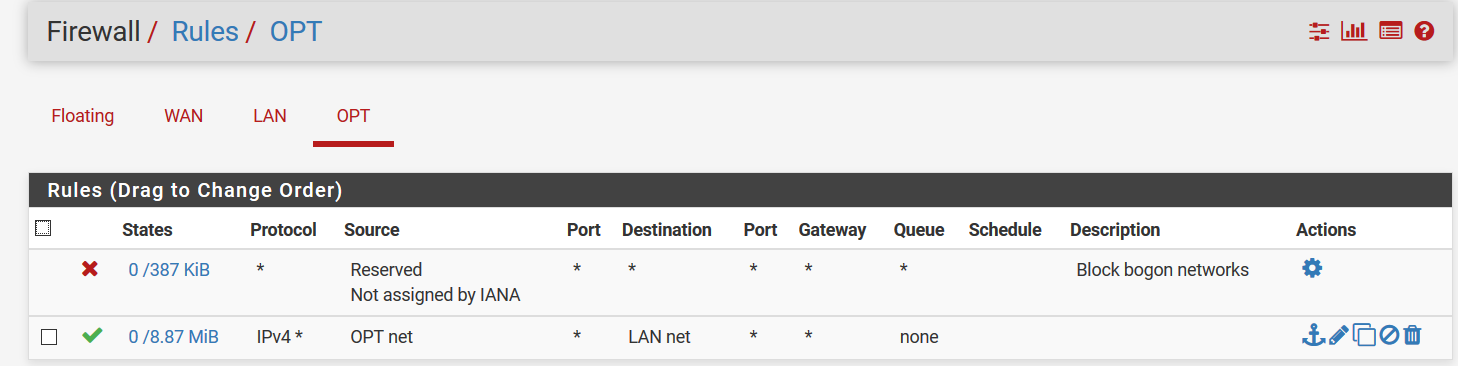
Here are my OPT firewall rules at present, which allow full access to both the Internet and the devices on the LAN port:
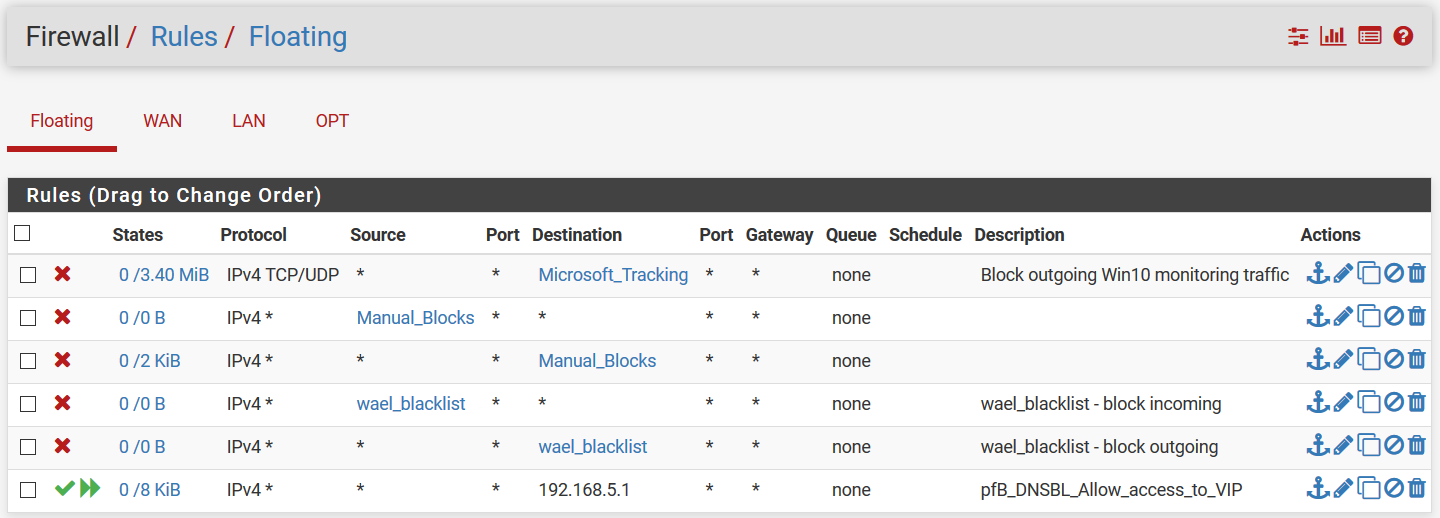
My floating rules are a bit of a mess, but they shouldn't be interfering. Here they are:
Does this make sense to anyone?
Thanks! -
I think you are saying you want OPT to be able to access internet but NOT LAN ??
On OPT you need to :
Block ANY to LAN Network
Allow OPT LAN Network to AnyAllow Any to WAN , is NOT allow Any to Internet
/Bingo
-
And just like that, it works.
I was starting to suspect that when the software said "WAN net" it didn't mean the network connected to the WAN port, but rather WAN IPs. I was still stuck in a rut trying to do everything with one rule, though.
Thank you for the help!