Setup wireless router with PfSense
-
I have 2, in fact 3 methods how I can setup my wifi router at home. I would like to have some advice or expert talk about these methods. The pro's and cons or if there is one that is the preferred way, or the opposite, something that I should not do.
I tested all three and they are all working.This is my Pfsense:
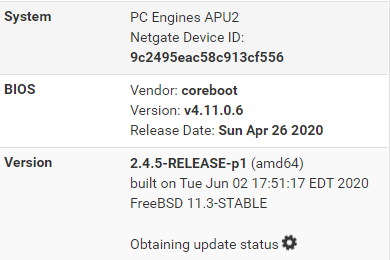
Interfaces:
My Wifi router is a TPLink Deco 9.
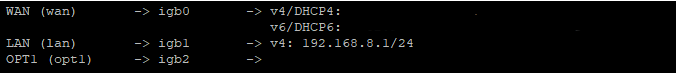
Method 1 - Wifi router connected to PfSense
I have an interface free on my PfSense, so I connect that with the master AP of my TPLINK. My PfSense is DHCP and gives an address to the TPLINK. It's a /30 network so only 2 available IP's. In this case Pfsense is 192.168.9.1 and TPLINK is 192.168.9.2. My TPLINK creates a subnet 192.168.10.0/24 for my wireless devices.Method 2 - wifi router interface in same subnet as LAN
TPLINK interface will be connected to the unmanaged switch like all other cabled devices and he will get an address from my dhcp pool (fixed dhcp address). The TPLINk interface gets a 192.168.8.x address and again my TPLINK creates a subnet 192.168.10.0/24 for my wireless devices.Method 3 - Briding mode
For me the less interesting because then I loose a lot of features that the TPLINK wifi router is offering like anti-virus, parental control, qos. Here my TPLINK becomes a stupid AP that gives all my wireless devices IP's in my 192.168.8.0/24 subnet.To make it a bit more clear (because a picture says more than 1000 words...):
METHOD 1
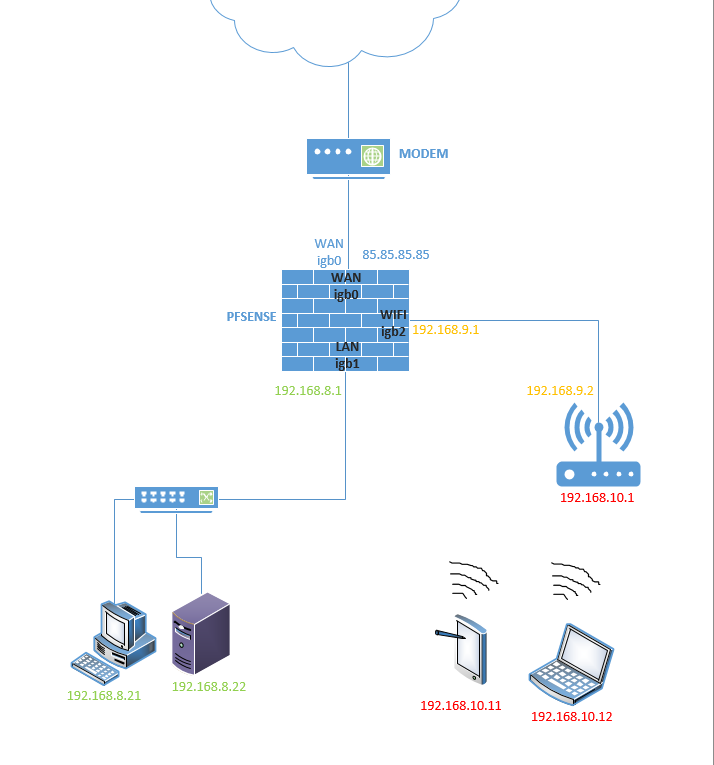
METHOD 2
METHOD 3 - No picture needed here.
Thank you for the advise.
-
Method 3 - Briding mode
For me the less interesting because then I loose a lot of features that the TPLINK wifi router is offering like anti-virus, parental control, qos. Here my TPLINK becomes a stupid AP that gives all my wireless devices IP's in my 192.168.8.0/24 subnet.I'd use bridge mode, as that gives you a flat network, where WiFi devices are on the same subnet as everything else.
Can't you find some other way to control your parents?

-
@JKnott said in Setup wireless router with PfSense:
Can't you find some other way to control your parents?
Haha.

But, yeah, if it was me I would also do with method 3. Run it as an access point only and connect it to igb2 so your can filter traffic between between wireless and wired clients. Assume the wireless key has been compromised and apply rules appropriately.
Steve
-
The only time I've used a separate interface for WiFi was back in the days of WEP. I had the WiFi outside my firewall and the only way in was with a VPN. I don't think I've ever seen a separate interface in any business installation. What I have seen is separate SSID & VLAN for guests, to connect only to the Internet.
-
BTW, for WiFi passwords, I use "Perfect Passwords" from www.grc.com. These are 63 random character strings and so are a bit hard to guess.
-
Yeah it's safe-ish. I've met a few guys who crack WPA keys as a hobby though and it's not as difficult as I once thought. Plus me wifi gear is not the newest.

But also the real issue in my mind is that I give the wifi key to someone here who needs it. They get a virus on their laptop or they give the key to someone else who has malware etc.
I try to separate as many things as possible, multiple SSIDs with different VLANs etc as you say. But as with many things the security vs convenience trade-off applies.A single LAN subnet with wifi connected to it directly is not an arrangement I would ever choose if I could avoid it.
Steve
-
Why are there only 3 options.. And why would you have your wifi nat? Just connect your wifi as AP to this 3 network you created on your opt.. Prevent that network from talking to your lan network, other than things you might want to access like media server (plex as example)..
Best option would be to get an accesspoint that can do vlans so you can have multiple wireless networks.. For your guest, for you, for iot, etc..
63 character psks are a bit over the top ;) But if your just using qr codes to access not a big deal.. Other than when you need to to type this in like on some iot device ;)
For my "trusted" wifi - I just use eap-tls, only my devices can connected to this wifi network. Iot devices don't support that though - they really should..
Even if the guest psk is compromised - can't do anything than access the internet, has no other access to anything else on my network.
Funny thing with long psks, I had setup my son's network in his new house.. And while the psk for his iot network not 63, it was somewhere like 28... You should of seen the face of the tech installing the alarm system when I gave it too him to type into the system ;) hehehehe
His tv was cool it just linked t your phone during setup and pulled the psk.. So no having to type it in.
I would really recommend isolation of wifi to its own segments, especially if your going to have "guests" or iot sort of devices..
-
@johnpoz said in Setup wireless router with PfSense:
63 character psks are a bit over the top ;) But if your just using qr codes to access not a big deal.. Other than when you need to to type this in like on some iot device ;)
I have only twice come across a problem with those passwords. One was with an Asus Eee PC, which would choke on some of the punctuation characters and my Sharp Roku TV, which I bought last year. It can't handle the full 63 character password, so I pressed an old Asus WL-330gE portable access point into service to allow that TV have it's own shorter password.
-
@JKnott , @stephenw10
Yes maybe I am making things unnecessary complicated. But like I said, if the wireless router is in bridge mode I lose the features of TPLink (for what it's worth of course). And thanks Jknott for the advise about my parents . You're right maybe I should let them explore the full potential of the Internet by now. Btw it is so ridiculously easy to circumvent... Let's say that in a first place I used it to play with it ;-) (I mean those features).
. You're right maybe I should let them explore the full potential of the Internet by now. Btw it is so ridiculously easy to circumvent... Let's say that in a first place I used it to play with it ;-) (I mean those features). -
@johnpoz
Thanks John for your reply. I just checked in the settings of my AP and it seems that there is a vlan option. I will look at it.
So what I am going to do now is follow the advise of @stephenw10 and @JKnott and put everything back to just one subnet in a first place (AP in bridge mode) and then have a look at that vlan option. It would be nice to have my "parents" on a different vlan a bit separated from my other devices. They both (two teenagers) are in a very experimental phase clicking and installing just everything what they see. On top of that they don't understand English yet and they even don't bother what warning they just received on their mobile or tablet. Just click on 'agree' they think
on a different vlan a bit separated from my other devices. They both (two teenagers) are in a very experimental phase clicking and installing just everything what they see. On top of that they don't understand English yet and they even don't bother what warning they just received on their mobile or tablet. Just click on 'agree' they think  . I tried to explain though. Few time already. But no success till now
. I tried to explain though. Few time already. But no success till now  .
. -
What AP do you have that supports vlans... I have never seen a home user AP support vlans.. The decos don't support them for different wifi ssids.. They have support if your ISP Is on a vlan - useless for this..
Users go and spend 100's of dollars on these what could be useful routers and AP, full mesh setups - and when it comes to the most basic of shit like a vlan - they have zero support..
You can pick up a 40$ 8 port gig switch that does vlans.. But your $600 wifi mesh system - nope... Its freaking ridiculous..
Why the unifi APs prob have so much support around here, people running pfsense normally like to do actual networking stuff ;) They support vlans.. And they are not cisco pricing ;) You can get an AC AP that does vlans for like 80$
-
@johnpoz
You are correct, just checked that vlan option and it just gives me a list of foreign ISP names.
And yes I should get rid of my unmanaged switch. -
A managed switch not really going to do much for you if your AP doesn't support vlans.. Unless you use different AP for your different networks.. Then sure you can have wired vlans, and just connect your different APs (using different ssids for sure) to different vlans via which port you connect them too.
Depending if your wifi router supports 3rd party firmware, like dd-wrt or openwrt add vlan support - if the under laying hardware actually supports it.. Many devices do - its just the makers didn't add in the ability with their native firmware. Boggles the mind to be sure ;) So if you use a device that supports such 3rd party firmware, you can leverage vlans on them that way.
I personally don't see why any one would buy a dumb switch, when for just a few dollars more you can something that at least can do vlans. I personally don't even get why they even sell such hardware any more.. If you don't configure a smart switch, it just defaults to being dumb.. So why would you not just buy smart, so at any future point you want/need to do vlans you already have the equipment in place. Dumb still have use sure, if everything connected to that switch is on the same vlan - you can place it downstream of your smart switch for more ports and all those devices can be on some specific vlan.. But is it really worth the few dollars difference in price? To be limited like that.. You never know where/when you might want to put a device on a different network..
I would think anyone that has graduated to using pfsense as there router would want to be able to do vlans. Its ease of use firewalling between segments is really one of its best features.. Which becomes pretty pointless if your switching infrastructure doesn't support vlans.
-
@johnpoz said in Setup wireless router with PfSense:
What AP do you have that supports vlans... I have never seen a home user AP support vlans..
Proper APs do, Routers configured as APs don't. I believe that is what he has, when he says "if the wireless router is in bridge mode".
-
@czar666 said in Setup wireless router with PfSense:
TPLink Deco 9
Is what I believe he has
https://www.tp-link.com/us/home-networking/deco/deco-m9-plus/so that going to be 1 router with wifi and then "nodes" or AP tied to that normally..
-
@czar666 said in Setup wireless router with PfSense:
And yes I should get rid of my unmanaged switch.
Avoid TP-Link, as some models don't handle VLANs properly and I have the same problem with my TP-Link (real) AP.
-
^ yeah I concur tp-link would not be my first choice for anything with vlans... There have been multiple threads here, and even on their own forums took them a couple of years to even admit there was an issue. And then when they came out with a firmware fix, they didn't back port it to older versions of hardware.
But it seems that you could install the v3 firmware onto their v2 hardware and correct the vlan issue... But yeah would prob be easier to avoid that brand all together. If your goal is ability to actually do vlans ;)
-
@johnpoz said in Setup wireless router with PfSense:
TPLink Deco 9
The specs don't mention VLANs on the LAN side. Apparently, it only supports them on the WAN side, for connecting to some ISPs.
-
@johnpoz said in Setup wireless router with PfSense:
But it seems that you could install the v3 firmware onto their v2 hardware and correct the vlan issue... But yeah would prob be easier to avoid that brand all together. If your goal is ability to actually do vlans ;)
Mine is V2, but it's not that critical and my next plans would be to update to 802.11ac or ax, though that's not a priority, as my ThinkPad can only do 2.4 GHz n. However, my phone can do ac and tablet n on both bands.