Is this possible with VPN?
-
Hi,
I'm wondering if anyone could help me, I have the following situation:
I have a Watchguard xtm5 with Pfsense at the datacenter and one Watchguard xtm5 with Pfsense at home,
(both latest versions of Pfsense installed)
I have setup a Openvpn tunnel between both instances which is up and running correctly.The XTM5/Pfsense at the datacenter WAN port is connected to a switch (187.x.x.0/30 network), the XTM5/Pfsense WAN port has a static public IP: 187.x.x.8, I can control Pfsense from the internet, all other ports on the XTM5/Pfsense in de datacenter are not connected.
What I would like to have is, that I can use the public ip adresses from the datacenter at home, this is neccesary for some servers I would like to migrate, so I can test them at home before I install them at the datacenter..
Any Ideas?
-
Yeah, that's possible. Just port forward or route the ip through to your pfSense at home.
-
Thanks..!
Can you guide me how to do that? I'm a still a Noob In Pfsense ;-) -
Depends on how this IP you want to - let's call it - forward reaches your DC pfSense. As you wrote your port ist connected to a /30 network I assume it's a simple 2 IP transfer network and you get another IP range or single IPs routed to that? Otherwise I don't know how that .x.x.8 will reach you?
If that is routed and you can see it reach you pfSense on the DC side of things (easy to check: just look into your firewall logs and try to call the .x.x.8:443 via browser - you should see a hit for .x.x.8:443 there with your home IP) then you can simply add a static route and route the .x.x.8/32 IP to the other side of your OVPN tunnel.
For the interface and IP to be availabe you should use a simple shared-key type OVPN tunnel and add the ovpns/c interface via "Interfaces assignments" to a new OPTx interface. Just select the correct ovpnXn interface, add it, and save. Then head to the newly created OPTx interface, rename it to like VPN_DC or something and click the "activate" box. Don't switch any other setting! No static IP or something, that interface gets handled by OVPN so leave it. Simply activate it and be done. Do that again on the other side pfSense. Then you should perhaps "restart" the tunnel by reconnecting OVPN, as it tends to get a little lost over the mapping of the ovpn interfaces. Just restart it on both sides and it should be good.
With that, you should also see the new OPTx interface and an automagically appearing OVPN gateway that shows up in your Routing/Gateway section. Now you have the OVPN GW available on both sides to route traffic.
All you have to do now is to route the IP.8/32 you want to the newly created OVPN gateway (aka the other side of your tunnel). Then add firewall rules on the DC side to let traffic pass (and add logging to it for further debugging) coming from any to the .8 IP. Then check again with a .x.x.8:443 call from your browser. You should again see a hit to .8:443 in your firewall logs on the DC side but with a pass now and if everything went fine should also see a blocked one on incoming on the OVPN interface on your home firewall (if you didn't already have a pass any rule in place on the OpenVPN interface). If that's the case your're almost done as you have the .8 in your home network and can now port forward, route or answer it on your pfsense at home as you like.
Just watch out on the DC side of things: if you create a pass any rule for the .8 check if you can accidentally access your WebUI from the outside world. It shouldn't be, but if something went wrong or you previously had the .8 configured somewhere in the DC pfsense it may still react to that IP and expose your HTTP(S)/SSH/any ports to the web. So double-check that.
That procedere is slightly different, if that IP isn't routed. Then instead of routing it with a static /32 route you can simply create a port forward to the IP on your home LAN side you want it to have and then check, that this IP is correctly routed via your OVPN tunnel. If you created the site2site tunnel correctly (pushed the lan network from home to DC as route) it should simply work.
We have that stuff running for very old IP ranges from other ISPs where we hosted customer projects years ago but they hardcoded their IPs into special apps and can't switch them out. So we nowadays just have a simple pfSense instance running there to just route that old network segment to our new infrastructure and make it available so the customer can still use it. With added latency and delay and a bit of overhead through the tunnel, but hey, in that application usage they have, that's barely noticable at all. :)
-
Thanks,
Sadly, I could not get this to work.... am i doing something wrong?
I setup a TUN vpn with shared key and tunnel network 10.0.8.0/24 (datacenter = 10.0.8.1 <-----------------> home = 10.0.8.2)
I can ping both ip's remotly (10.0.8.x) from both Pfsense, I see the OVPN gateways and they are online, next to the default Datacenter and home ISP gateway.Here the situation: Datacenter network 187.x.x.0/30
Datacenter Pfsense
WAN IP 187.x.x.8, Gateway 187.x.x.1 (up)
OVPN tunnel 10.0.8.2 (up)Home Pfsense
WAN IP 192.168.2.247, Gateway 192.168.2.254 (up)
OVPN tunnel 10.0.8.1 (up)I connected a laptop to a added port, (opt3), I would like to have this laptop use a ip 187.x.x.23, and 187.x.x.24
how can I setup this network? -
The IPs you mention (.23, .24, .8) aren't within the /30 on your WAN so how do they get to your pfSense in the first place? are they routed?
-
I'm sorry it isn't /30 didn't no why I typed that.. ;-)
Here is the correct (and full) situation..We have 2 lines (spanning tree) in the Datacenter, and can use 187.x.x.4 until 187.x.x.23 with Gateway 187.x.x.1 netmask 255.255.255.0
There is also a VLAN25 active for 187.x.25.153 until 187.x.25.159 with Gateway 187.x.25.1 netmask 255.255.255.0
We also have a 2A00:xxxx:x:31::/64 all these networks are connected to a HP Procurve switch. (VLAN25 tagged).The Gateway is on 187.x.x.1, and I believe 187.x.x.2 and 187.x.x.3 are routers because they are also reserved.
(they told us, we can't use these 3 ip's because of the datacenter infrastructure)187.x.x.4 until 187.x.x.15 are not free, 187.x.x.16 until 187.x.x.23 are free for use!
187.x.25.x no free ip!
2A00:xxxx:x:31::/64 are free for use!The Pfsense WAN port is connected to the switch on the 187.x.x.8 network.
WAN ---> DC Pfsense ---> tunnel 10.0.8.2 ---> Internet <--- 10.0.8.1 tunnel <--- Home Pfsense --->Laptop (opt1)
I would like the laptop (or a switch) to use any IP from the free 187.x.x.16 until 187.x.x.23 ip's -
@mangelot said in Is this possible with VPN?:
We have 2 lines (spanning tree) in the Datacenter, and can use 187.x.x.4 until 187.x.x.23 with Gateway 187.x.x.1 netmask 255.255.255.0
There is also a VLAN25 active for 187.x.25.153 until 187.x.25.159 with Gateway 187.x.25.1 netmask 255.255.255.0OK bear with me :)
So that are 2 WANs I assume? Both are /24 and in both your upstream/ISP has a gateway on .1 and your pfSense has the .8 on one WAN as in the other there are no IPs left to use? Or does your pfSense has another IP configured as its WAN and you only want to use the .8 IP in addition to that?I would like the laptop (or a switch) to use any IP from the free 187.x.x.16 until 187.x.x.23 ip's
OK so in addition to my question above: the pfSense seems to have the .8 and you want e.g. .16 to use as additional IP and forward that to your Laptop. Is that correct?
-
The pfsense in Datacenter has 187.x.x.8 on the WAN, thats correct (there are no other ip's or cables attached)
Yes, I would like to use the .16 till .23 IP's on mij laptop or a switch at home (throught to vpn tunnel).
So I can setup servers at home with the datacenter IP's, and migrate them after setup to the datacenter.But If it also possible to also use the VLAN25 also as a extra WAN, throught to tunnel to my home, it would be really helpful, but not necessary...
-
So if your pfSense in the DC has .8 on its WAN, you add .16/.17/... or any address you want to use as an Virtual IP / Alias IP first. Otherwise pfSense will not get traffic for that IP. After adding it as alias, (as it isn't routed) you can only port forward or BiNAT this IP to your home network. All you have to do is set up your tunnel and routes correctly so that your pfSense at DC loc knows/can ping your network/laptop at home. If that works, it's simply adding a NAT/BiNAT or Port Forward rule to use e.g. the .16 IP and map it to your laptop IP.
If you set up the tunnel correctly (e.g. on the DC side: as local network you could use the 187.x.x.x/24 network and the remote network is you OPT1 laptop network) that shouldn't be hard to achieve.
-
Thanks,
Okay, so it has to be done with BiNat
So I must setup a internal network on the laptop 192.168.1.x and 1:1 Nat this throught the tunnel to DC and back with routing rules....There is no other way to let the laptop use: 187.x.x.8, subnet 255.255.255.0 and gateway 187.x.x.1 ?
There will be software running on the laptop, that needs to use the IP from the software license.
should this give any problem, you think? -
@mangelot said in Is this possible with VPN?:
So I must setup a internal network on the laptop 192.168.1.x and 1:1 Nat this throught the tunnel to DC and back with routing rules....
Nah, you just setup 1:1 NAT on your DC pfSense with 187.x.x.Y to <IPofYouLaptopAtHome>. If the routing in your tunnel setup between home/DC is correct, there's nothing else needed in terms of "routing with rules" (Policy based routes) as traffic for the .Y IP will automatically travel through the tunnel and as OVPN tunnels have a reply-to statement set in the filter, answering traffic should flow back the same way without problems.
As said, we have used that for customers ourselves and routed whole IP spaces via an OVPN tunnel to another location. It isn't that complex to set up :)
-
Hello JeGr,
Its been a while ago, I had some medical issues that took some time.
Now I feeling quitte better and I would really like to take up my project again.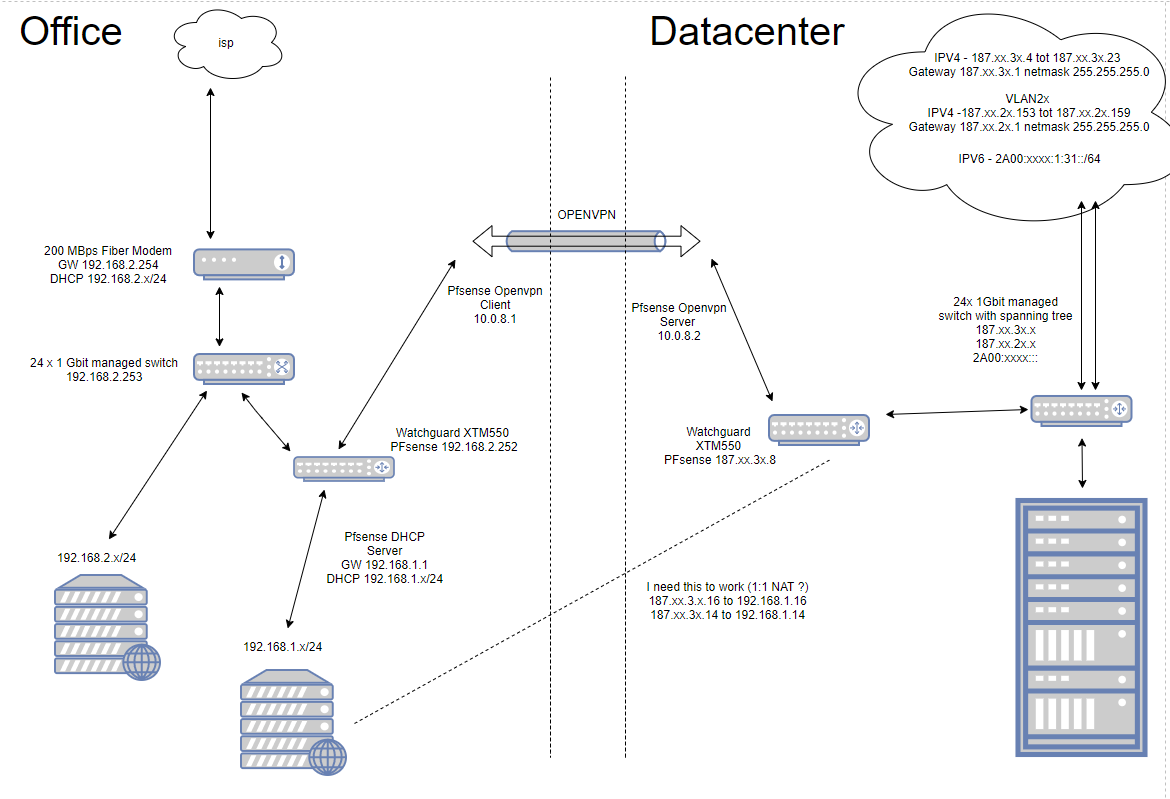
See the image for my current network setup, the dotted line is still the issue.
I have setup the VPN and I can ping Both Pfsense Appliances throught the VPN tunnel.
I temporary opened all (any) protocols on both appliances (WAN, LAN, VPN, just to be sure no firewall rules where the issue!)I added a virtual IP (Proxy ARP) to the Datacenter Pfsense (187.xx.3x.16), and setup a 1:1 NAT from external IP 187.xx.3x.16 to internal IP 192.168.1.16 (This is a laptop at the office, with a webserver installed)
I can Ping this laptop from Office Pfsense, and I can check for open ports (80) both with succesfull result.
I cannot Ping this laptop from datacenter (?), but I can check for open ports (80) with succesfull result.
Do you have any idea, what could go wrong here?
-
@jegr
ping