how to access from outside to server (teamspeak)
-
hi folks,
I would like to have access from the www to my teamspeak server
Network topology:
ISP Router - pfSense - Teamspeak ServerTeamspeak seems to use udp port 9987, so I did a port forward on ISP router to pfSense.
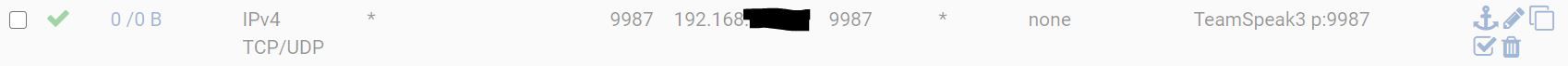
Within pfsense i created a rule on WAN:
*rule was activated during testing
but for some reason I am not able to access it.
Did I miss something?I have on that server also another http/https service running via HAproxy (reverse) HAproxy cannot coop with UDP isnt it?
thanks for your feedback
-
Are you sure you need to set a source port?
-
@Derelict
thanks for your feedback. Maybe I have an understanding problem.teamspeak (TS) client tries to connect to my public ip.
I have opened ports from 1000 to 65000 on isp router forwarding to WAN interface of pfSense.within pfSense I create a wan rule from port 1000 to 65000, with direction to server ip and port 9987
how does pfSense know which traffic belongs to where?
imagine there are overlaping ports for different services.btw. above mentioned port range on ISP router and pfsense did not fix my issue.
-
Sounds like you are significantly misunderstanding what teamspeak needs.
Post what they have to say regarding forwarding ports to an inside teamspeak server through a NAT router.
Matching on a source port is almost NEVER necessary and most often breaks the port forward. You have a source port set here:
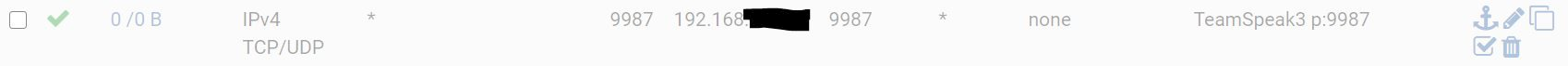
That will not forward the port unless the connecting host is setting 9987 as the source port. Almost certainly not the case (knowing nothing about how teamspeak actually works, specifically.).
Is that port forward disabled?
-
@Derelict
okay, i think i got it, just creating a rule is insufficient I have to to it via NATit is working right now.
since this is the 1st time I am using NAT port forward and have not other WAN NAT rules, do I need to consider something to avoid putting my server at CS risk?
-
Whenever you port forward into a server you are essentially bypassing the protections the firewall brings and then rely on the protections, and are vulnerable to the deficiencies the application forwarded to brings.
-
@pooperman said in how to access from outside to server (teamspeak):
since this is the 1st time I am using NAT port forward
Noop. The second time.
Your ISP router (should) contains the same NAT rule.
"All incoming UDP traffic on port 9987 is redirected to the PfSense IP - this is a LAN IP from an ISP router point of view."
Then, on pfSense :
"All incoming UDP traffic on port 9987 is redirected to the TS SERVER IP - this is a LAN IP from an pfSense point of view."You could chain on like that if needed.
It is a wise thing to change your ISP router setup so it NAT's only port 9987 to the inside (to the pfSense IP). Right now, no big deal as you have a second firewall : pfSense.
Security :
Every TS server which is globally accessible should expose it's 9987 port on the Internet.
The server only recognizes TS voice traffic, it will discard everything else. After more then 10 years of development they should be rather good at that. If not, every TS server would be getting exploited - and there are a lot of TS servers in the world.
Web servers do the same thing. Mail servers do the same thing. You should trust them, or not using them.