Filtering based on TTL or Packet Length
-
Hi,
This is probably an unusual case, but I need drop UDP packets based on TTL or packet length. I found this post: https://forum.netgate.com/topic/51318/packet-size-filtering
Showing it is possible using IPFW. Does anyone have any example commands for ipfw for something like this? The ipfw syntax is rather daunting to me, I have something like: ipfw -q add drop udp from any to any iplen 100Just looking to see if anyone has any experience with ipfw who can throw a couple of good example lines.
Thanks.
-
You could do it with snort and a custom ttl rule.
http://manual-snort-org.s3-website-us-east-1.amazonaws.com/node33.html
-
see https://forum.netgate.com/topic/155187/how-to-block-mobile-teethering-in-pfsense
-
alert ip 172.16.5.0/24 any -> !$HOME_NET any (msg: "IP with TTL>=100"; ttl:100-255; sid:20000012; rev:001;classtype: policy-violation;)
Where 172.16.5.0/24 is the local subnet, if you have it set to any it will block multicast packets.
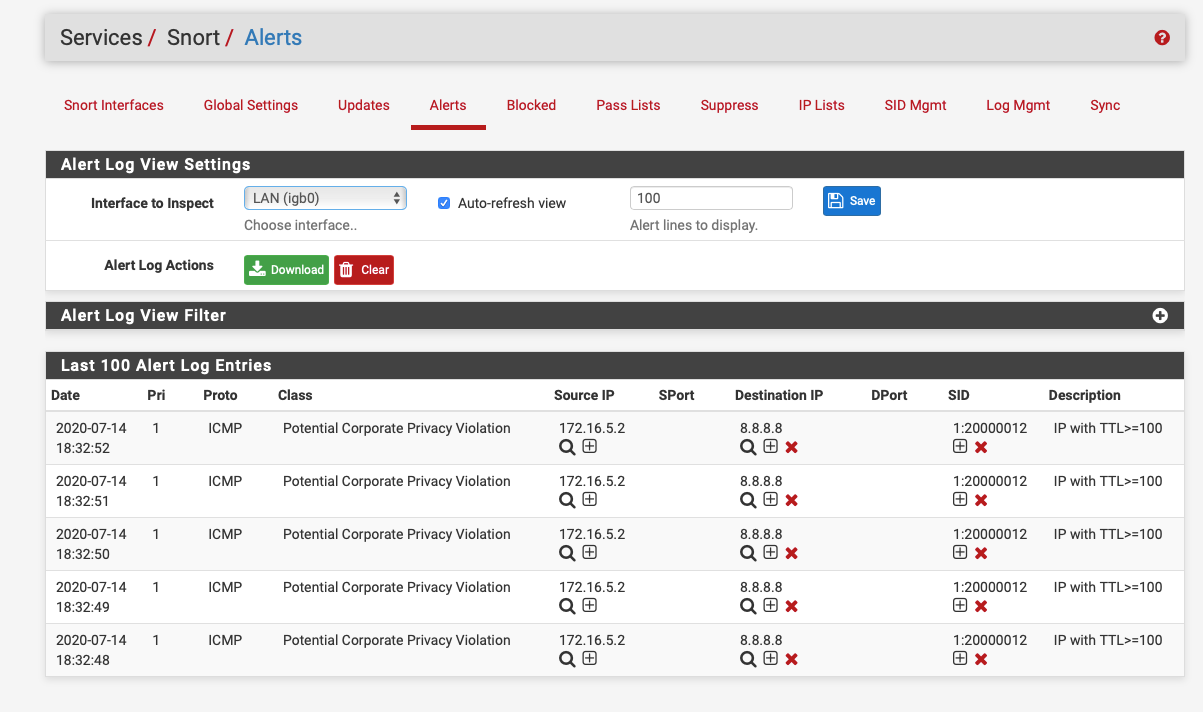
A ping to google.com with a ttl of 100:-
ping -m100 8.8.8.8 -
Just alert on the first packet in 300 seconds:-
alert ip 172.16.5.0/24 any -> !$HOME_NET any (msg: "IP with TTL>=100"; ttl:100-255; threshold:type limit, track by_dst, count 1 , seconds 300; sid:20000012; rev:001;classtype: policy-violation;)