Default deny rule all of sudden blocking all dns traffic
-
Hi so I'm having an issue where my firewall is working well for multiple days without any changes but then all of sudden the network loses internet. However, when I look at the firewall logs the default deny rule is blocking all dns traffic at both 853 and 53. I can't seem to understand why it's blocking these ports all of sudden, of course I don't have a filter rule in my WAN to open this port but should I? If I reboot the firewall this seems to fix it but if I try reloading the rules and state table the problem persists, why would only a reboot fix this? Is there something else I should look at that may be breaking the firewall?
Thanks in advance, I tried looking at the forums but I didn't really see anything that matched this case, though I could have missed something.
-
More info is needed. Are you using unbound resolver? Is the problem related with direct accesing public dns? Is pfsense using forwarders?
Any errors reloading filters?
Any floating rules?
Are yu allowing dns requests on your lan interface? -
Yes I am using a dns resolver, this is set to listen to port 53 and translate to port 853.
Yes it seems that in my firewall log connections to my outbound dns host were being blocked "1.1.1.2:853".I don't receive any errors when I reload the filters.
Yes, I have pfblocker set up so I only have those floating rules, which none of these rules are blocking this traffic.
I also have suricata setup but again not blocking the traffic in this service.What do you mean by this "are you allowing dns request on your lan"?
It was my impression that pfsense allows the source inside the lan to initiate outgoing connections so it wouldn't need to have a rule-specific for dns or https. I do have an allow all traffic just below my block rules.I didn't copy the firewall log but next time it happens I'll remember to save it.
Hope this helps, I appreciate the reply. -
@nightrider9870 If you allow all, then you don't need specific dns rules.
However it helps, because it lets you see if it matches any traffic.
so you are using unbound with
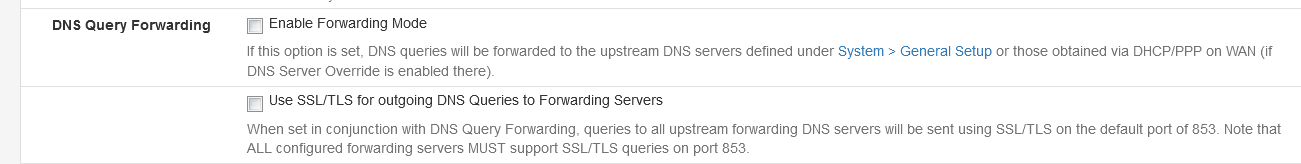
settings enabled? -
@netblues
Right, that was my impression as well and yes I have dns forwarding enabled and use ssl/tls for outgoing dns queries. My upstream dns servers are set to 1.1.1.2 and 1.0.0.2. -
@nightrider9870 When it happens, try
telnet 1.1.1.2 853
Trying 1.1.1.2...
Connected to 1.1.1.2.
Escape character is '^]'.Both from pf cli and a host inside your network
and see if it connects from both.Limiting pfsense box to outbound resources is tricky and requires floating rules, and sometimes is difficult to grasp.
Having said that, rebooting/reloading rules shouldn't make any difference, so we need to make sure its not a transient external issue too.
'
Do verify telnet works when you don't have an issue and we take it from there. -
This post is deleted! -
@netblues Thank you for the instructions.
I was able to telnet from both a host and the cli. -
@nightrider9870 Has the issue re-appeared ?