pfsense OpenVPN client behind firewall (2 firewalls)
-
Hi all,
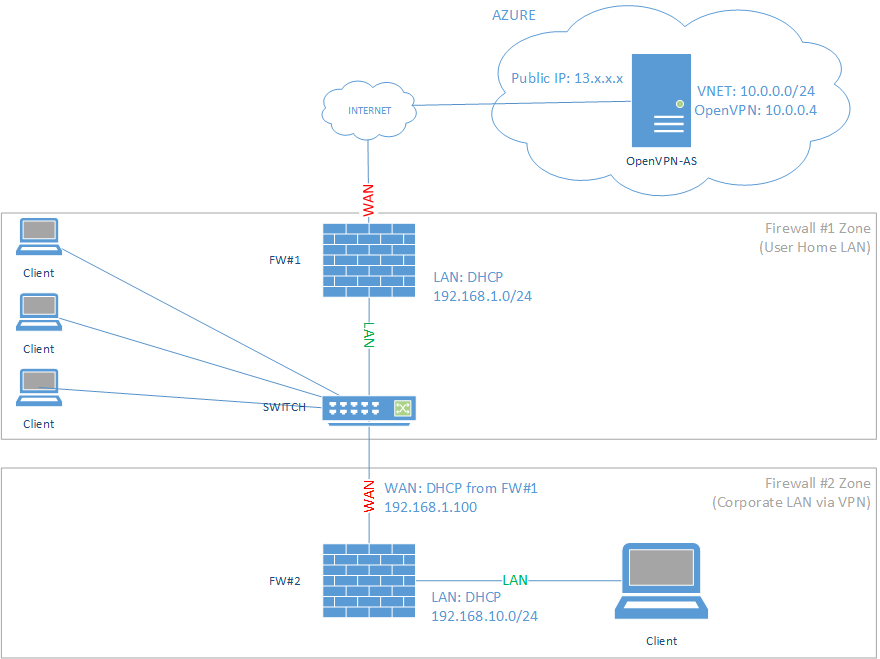
here is my problem, i want to be able to setup a pfsense machine and plug it into an existing network and have that device connect to an OpenVPN Access Server using the client method in pfsense. It is a little hard to explain but the below may help...
[OpenVPN-AS]<--[ISP]<--[pfsense #1]<--[switch]<--[pfsense #2]<--[clients]
OpenVPN client connection originates on fw#2 and is outbound to the OpenVPN server.
i have my primary firewall (#1) which has a switch on the LAN side, connected to the switch is the secondary firewall (#2) which is connected via the WAN interface, on the LAN side of this firewall is a client (client #1).
If i set this all up on firewall #1 i can pass traffic just fine however when i try the configuration on fw#2 i can see the tunnel comes up but am unable to pass any traffic.
My initial thoughts are it has something to do with double NAT or it could require some sort of transparent mode for fw#2.
What I am trying to achieve is, send a pre-configured pfsense box to a user and all they need to do is plug it into their existing network then connect their laptop to the LAN side of that firewall. The VPN should establish automatically and they'll be on the corporate LAN essentially.
I know there are better ways to do this however it isn't about remote access, more about remote infrastructure. We're using Azure AutoPilot to build new PC's and we need to be on the corporate network in order to do this as there is a limitation with hybrid deployments. You need to be able to see the domain controller with the Intune connector installed, normally this isn't a problem however COVID happened and doing this from home is a mission with IPSEC VPNs which are not user friendly.Thanks in advance.
-
I put something into Visio to help explain