HAproxy connection reset
-
Hi,
I was wondering if someone could shed some light on the issue im having. Currently i have HAproxy redirecting to my IIS, everything is working but many users complaining about the connection reset. I check the stats and found this
Only issue with subdomain webservices, and CO there both on IIS and they have SSL but because on HA proxy i have SSL/TCPmode which goes direct to the SSL of letsencrypt of the VM running the IIS.my question is how i can make the reset connection longer?
Thank you
This is my config
# Automaticaly generated, dont edit manually. # Generated on: 2020-09-14 12:02 global maxconn 500 stats socket /tmp/haproxy.socket level admin gid 80 nbproc 1 hard-stop-after 15m chroot /tmp/haproxy_chroot daemon server-state-file /tmp/haproxy_server_state listen HAProxyLocalStats bind 127.0.0.1:2200 name localstats mode http stats enable stats admin if TRUE stats show-legends stats uri /haproxy/haproxy_stats.php?haproxystats=1 timeout client 5000 timeout connect 5000 timeout server 5000 frontend SharesFrontend-merged bind 181.57.xx.xxx:443 name 181.57.xx.xxx:443 mode tcp log global timeout client 30000 tcp-request connection set-src str(192.168.3.254) if { src 192.168.0.0/22 } tcp-request inspect-delay 5s acl ng req.ssl_sni -i ng.mydomain.com acl inventory req.ssl_sni -i inventory.mydomain.com acl gitlab req.ssl_sni -i gitlab.mydomain.com acl remote req.ssl_sni -i remote.mydomain.com acl apps req.ssl_sni -i apps.mydomain.com acl basedatos req.ssl_sni -i basedatos.mydomain.com acl b2c req.ssl_sni -i b2c.mydomain.com acl cloud req.ssl_sni -i cloud.mydomain.com acl webservices req.ssl_sni -i webservices.habicicletas.co acl mail req.ssl_sni -i mail.mydomain.com acl co req.ssl_sni -i co.mydomain.com acl correo req.ssl_sni -i correo.mydomain.com tcp-request content accept if { req.ssl_hello_type 1 } use_backend Backend1_ipv4 if ng use_backend Backend2_ipv4 if inventory use_backend Backend3_ipv4 if gitlab use_backend Backend4_ipv4 if remote use_backend Backend5_ipv4 if apps use_backend Backend6_ipv4 if basedatos use_backend Backend7_ipv4 if b2c use_backend Backend8_ipv4 if cloud use_backend Backend9_ipv4 if webservices use_backend Backend10_ipv4 if mail use_backend Backend11_ipv4 if co use_backend Backend12_ipv4 if correo frontend HTTPTOHTTPS bind 181.57.xx.xxx:80 name 181.57.xx.xxx:80 mode http log global option http-keep-alive timeout client 30000 tcp-request connection set-src str(192.168.3.254) if { src 192.168.0.0/22 } acl ng var(txn.txnhost) -m str -i ng.mydomain.com acl inventory var(txn.txnhost) -m str -i inventory.mydomain.com acl gitlab var(txn.txnhost) -m str -i gitlab.mydomain.com acl remote var(txn.txnhost) -m str -i remote.mydomain.com acl apps var(txn.txnhost) -m str -i apps.mydomain.com acl basedatos var(txn.txnhost) -m str -i basedatos.mydomain.com acl b2c var(txn.txnhost) -m str -i b2c.mydomain.com acl cloud var(txn.txnhost) -m str -i cloud.mydomain.com acl webservices var(txn.txnhost) -m str -i webservices.habicicletas.co acl mail var(txn.txnhost) -m str -i mail.mydomain.com acl co var(txn.txnhost) -m str -i co.mydomain.com acl correo var(txn.txnhost) -m str -i correo.mydomain.com http-request set-var(txn.txnhost) hdr(host) http-request redirect scheme https if ng http-request redirect scheme https if inventory http-request redirect scheme https if gitlab http-request redirect scheme https if remote http-request redirect scheme https if apps http-request redirect scheme https if basedatos http-request redirect scheme https if b2c http-request redirect scheme https if cloud http-request redirect scheme https if webservices http-request redirect scheme https if mail http-request redirect scheme https if co http-request redirect scheme https if correo backend Backend1_ipv4 mode tcp id 10100 log global timeout connect 30000 timeout server 30000 retries 3 source ipv4@ usesrc clientip server ng 192.168.3.217:443 id 10101 check inter 1000 backend Backend2_ipv4 mode tcp id 10102 log global timeout connect 30000 timeout server 30000 retries 3 source ipv4@ usesrc clientip server inventory 192.168.3.218:443 id 10101 check inter 1000 backend Backend3_ipv4 mode tcp id 10103 log global timeout connect 30000 timeout server 30000 retries 3 source ipv4@ usesrc clientip server gitlab 192.168.3.101:443 id 10101 check inter 1000 backend Backend4_ipv4 mode tcp id 10104 log global timeout connect 30000 timeout server 30000 retries 3 source ipv4@ usesrc clientip server remote 192.168.3.100:443 id 10101 check inter 1000 backend Backend5_ipv4 mode tcp id 10105 log global timeout connect 30000 timeout server 30000 retries 3 source ipv4@ usesrc clientip server apps 192.168.3.97:443 id 10101 check inter 1000 backend Backend6_ipv4 mode tcp id 10106 log global timeout connect 30000 timeout server 30000 retries 3 source ipv4@ usesrc clientip server basedatos 192.168.3.97:443 id 10101 check inter 1000 backend Backend7_ipv4 mode tcp id 10107 log global timeout connect 30000 timeout server 30000 retries 3 source ipv4@ usesrc clientip server b2c 192.168.3.97:443 id 10101 check inter 1000 backend Backend8_ipv4 mode tcp id 10108 log global timeout connect 30000 timeout server 30000 retries 3 source ipv4@ usesrc clientip server cloud 192.168.3.95:443 id 10101 check inter 1000 backend Backend9_ipv4 mode tcp id 10109 log global timeout connect 30000 timeout server 30000 retries 3 source ipv4@ usesrc clientip server webservices 192.168.3.210:443 id 10101 check inter 1000 backend Backend10_ipv4 mode tcp id 10110 log global timeout connect 30000 timeout server 30000 retries 3 source ipv4@ usesrc clientip server mail 192.168.3.213:443 id 10101 check inter 1000 backend Backend11_ipv4 mode tcp id 10111 log global timeout connect 30000 timeout server 30000 retries 3 source ipv4@ usesrc clientip server co 192.168.3.252:443 id 10101 check inter 1000 backend Backend12_ipv4 mode tcp id 10112 log global timeout connect 30000 timeout server 30000 retries 3 source ipv4@ usesrc clientip server correo 192.168.3.213:443 id 10101 check inter 1000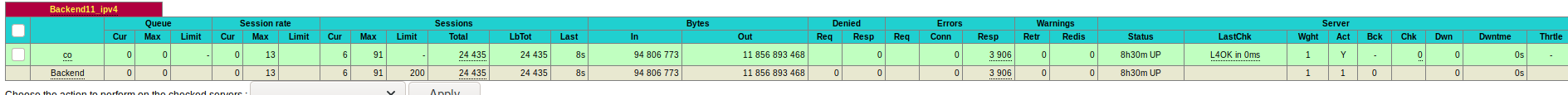
Thank you
-
@killmasta93
Maybe try increasing client-timeout and server-timeout values on frontend / backend. Currently you have them configured as 30 seconds. Perhaps something like 5 minutes = 300000 ms would work better.?. -
Thanks for the reply, as whats the rule of thumb or recommendation to normally have it?
Going to try it out and post back how it goes -
Correct answer: stop use tcp mode for http backend. This stupid tbh! You lose all benefits of haproxy you can have.
Haproxy also can have letsencrypt (acme). More over it more good way to handle ssl on haproxy frontend then on iis where you simply at black hole with tls setup which apply only after reboot, not correctly working http/2 and much more stuff about what benefits haproxy have with http and miss with tcp... If you want have full encryption this also not an issue: you create own CA at pfsense and issue own certificate from this CA for 10years and put them on iis. Haproxy connect to iis over https and also validate that ssl is not faked. For frontend you use same lets encrypt...