OpenVPN cannot access remote network
-
First post here - please treat me gently.
Headline:
- I can remotely connect to OpenVPN,
- I can access the web interface of the pfSense/OpenVPN server, which is 192.168.11.10
- I cannot get further (my target network is 192.168.11.*) from my remote client
- All implementation was done manually, not using a Wizard.
- The pfSense/OpenVPN server is not running DHCP for the target network (192.168.11.), and is distributing addresses for the tunner network (192.168.80.).
Network picture:
- Public IP address a.b.c.d reaches a router, which port-forwards UDP 1194 to the WAN side of the pfSense/OpenVPN VM
- The VM has two network adapters. The WAN is 192.168.99.10/24, the LAN is 192.168.11.10/24
- The tunnel network is 192.168.80.0/24. After I remotely connect, my desktop has an address of 192.168.80.2
- The network I want to reach is 192.168.11.*/24. This is specified in VPN > OpenVPN > Servers > IPv4 Local network(s)
- I have not created any Route statements.
After I connect my Windows 10 desktop shows a Route Print (there is much more - my local IP address is 192.168.0.*):
192.168.11.0 255.255.255.0 192.168.80.1 192.168.80.2 281
192.168.80.0 255.255.255.0 On-link 192.168.80.2 281
192.168.80.2 255.255.255.255 On-link 192.168.80.2 281
192.168.80.255 255.255.255.255 On-link 192.168.80.2 281From my desktop (after connecting):
- I can enter the WebConfigurator using Chrome and 192.168.11.10. This appears to be the only 192.168.11.* device I can remotely reach.
- Inside the web page Diagnostics I can Ping various other devices I know are on the remote network (192.168.11.1, .8, .9, .246, .248, ...). So the pfSense/OpenVPN server can reach the local network.
- From my remote desktop I cannot ping any of these x.x.11.* addresses.
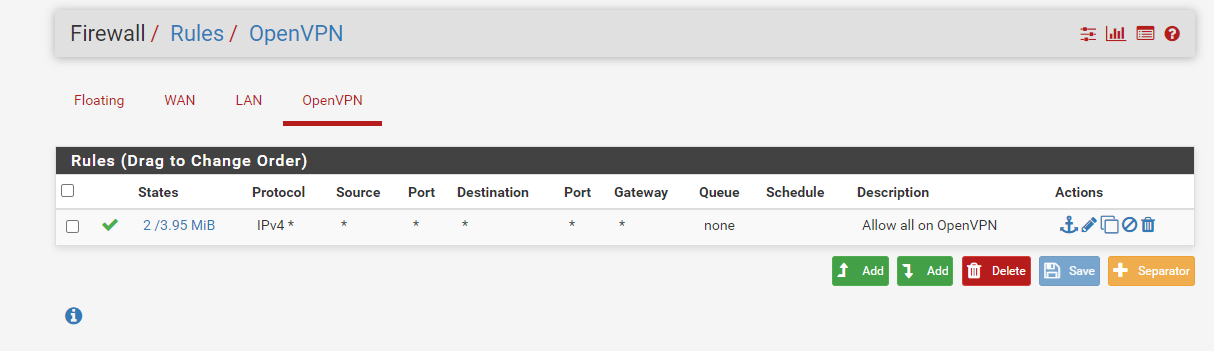
pfSense Firewall
- There is a rule under both the WAN firewall, and the OpenVPN firewall.
- The OpenVPN rule allows everything to get to everywhere, both TCP+UDP, all ports, all sources, all destinations, TCP4+6.
- The WAN firewall rull allows UDP 1194 destination WAN, TCP 4.
-
@jasmantle said in OpenVPN cannot access remote network:
The VM has two network adapters. The WAN is 192.168.99.10/24, the LAN is 192.168.11.10/24
Is the pfSense LAN IP the default gateway in this LAN?
-
From the perspective of the rest of the network, the 192.168.11.* LAN's gateway is 192.168.11.1
The pfSense/OpenVPN server, 192.168.11.10, is just another computer on the that network.
-
@jasmantle
So you will either need static routes for the OpenVPN network on the LAN devices pointing to the OpenVPN server to direct response packets back, or do a workaround with masqerading on pfSense.However, the masqerading (s-NAT) solution can only be recommended if the VPN is for your own purposes, but not for multiple users. You won't be able to determine the real user on the destination device.