Allowing another interface to communicate b/w primary LAN
-
Hi everyone!
So first post, and Hello!And I will get right to the brass tax.
I have a installed instance of pfSense with 4 NICs(1WAN, 1 Primary DHCPd LAN, 1 NIC specifically for 802.1Q VLAN Trunking, and one going to another network, which i can not change vlan on to match new scheme as of yet)So I got(Either by luck or I did something right) working one of my inter-vlan links working thru the firewall(by adding pass from primary lan to vlan 2, and vice versa) and the obvious WAN to internet working, while blocking internet to the VLANed networks(those must remain isolated for security and company policies)
Now I have a network with the scheme of 192.168.0.xxx/24 on native vlan of default 1. I obviously cant use the vlan I want directly(vlan3) and at this moment, cant change it. So I connected the network to another NIC onboard, as a temp solution.
I have a primary network of 10.10.10.0 /24 , the network that is able to communicate to primary on vlan2, 10.250.250.xxx/24, and the one i need to build a route to at 192.168.0.xxx/24.So, if i didnt confuse anyone here, if I build a firewall rule between the nets of my primary, and the 192.168.0.xxx, should I see, and be able to ping hosts from the 10.10.10 network, or is there something im missing? I have checked the network by pinging a known host in the adapter in the diag menus in pfsense, and 100% success rate
-
As you bring up new networks/vlans directly attached to pfsense. The only thing that needs to happen is firewall rules need to be created on the new interfaces for the traffic you want to allow from that network.
If your having issues with vlan X talking to Y.. Its either the rules are wrong, or very common issue that comes up is users forget that devices on these network quite often have their own host firewalls. And might not allow anything from other than their own local network.
-
Hi John,
The network I'm attempting to route has no firewalling of any type. The network is truly a "Closed-loop" network. And I did try above, but because maybe I goofed, let me rebuild the rule.
-
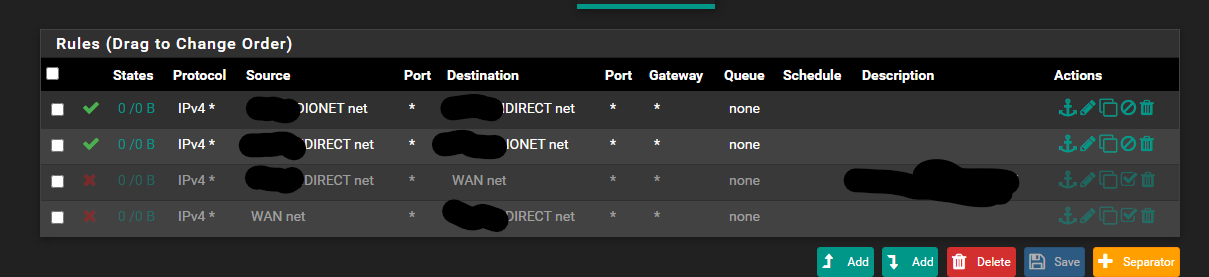
I blocked out the names, for security reasons.
So IONET is my primary net 10.10.10.xx (vlan here is 1-default)
DirectNET is the net at 192.168.0.xxx (vlan here is also 1, but im bypassing the vlan mismatch by using the extra NIC onboard my pfSense install) I want to access from 10.10.10.xx
In addition, blocking WAN to DirectNet, and vice versa
Now, same firewall rule on my 10.250.250.xxx adapter to IOnet allows perfect routing to and from its associated vlan, on VLAN_NET adapter, specifically laid out for 802.1Q trunking. Pings to hosts on that lan are good.Sorry if I repeated myself, just trying to get the info out there, because I am stumped, or maybe its the back to back double shifts getting to me.
-
And which interface are these rules on ionet or direct? Can tell you for sure right now that both of those rules are not needed. Only 1 of those are needed.. What interface are these rules on?
That would be the source net.. And the dest would be the other network.
How and the F would wan net ever be source as traffic into this enterface - be it io or direct?
You understand also that wan net, is just that the network attached to the wan - it does not = internet... It equals the network the wan is connected to via its mask.. For example mine is
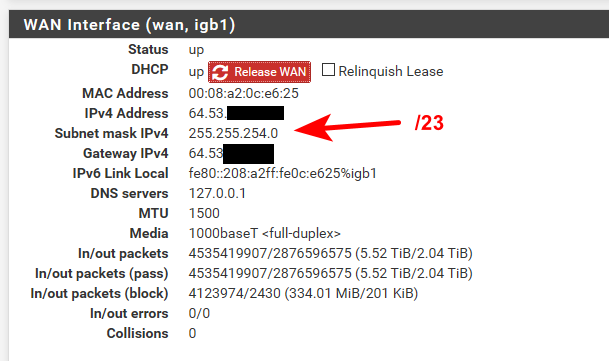
How could your wan net ever be a source into the interface your showing which is either ionet or direct? 10.10.10 or 192.168.0??
On the network that wants to create traffic to the other net.. Create a rule that allows that net to the dest net. Done! That is all that is needed to be done.
If it is not working.. Then look to your dest device - is it running a firewall, does it point to pfsense as its gateway?
I show no hits on any of these rules at all.. Where did you put them?? On which interface?
Simple test.. From source network can you ping pfsense IP on that network? Can you ping pfsense IP of the dest Network? If so... And you can not ping your dest IP in that dest network.
Sniff on pfsense interface in the dest network - do you see it send your ping on to your device? If so then pfsense is doing what you told it to do... It can not make the device answer, be it has a firewall? Be it not pointing to pfsense as its gateway?
-
Got it resolved. You were right, fudged a firewall rule!