(IPsec outbound NAT to interface address) Reply traffic destination IP not being translated back to original source IP
-
@stephenw10 said in (IPsec outbound NAT to interface address) Reply traffic destination IP not being translated back to original source IP:
If the initial connection to the other side was outbound on that peer (there is no server/client in wg) then return traffic there will use the open state. That firewall rule would not be used to create a state that would that show traffic on it.
Steve
Yup, I'm aware that there is no server/client in WG but in my use case one side is "acting" like a server and the other side is acting like a client by initiating the outbound connection. No, the initial connection was outbound from the client side (the one behind an ISP NAT, naturally) so the WAN rule I'm showing is for inbound traffic (forward traffic, not return).
-
Hmm, well I would certainly expect to see traffic on that rule then.
Check the state table for a state open on WAN with that traffic on it.
Something else must be opening it. -
I do see an open state:
client dynamic public IP:random port -> server static public IP:51820
I then disabled the WAN rule and surprisingly the tunnel still worked. This is consistent with the behavior in the Youtube video above wherein he accidentally specified a wrong destination port in the WAN rule but it still worked. Although, the only difference in this case is the open state goes like the other way around:
server static public IP:51820 -> client dynamic public IP:random port
Why did the open state reverse?
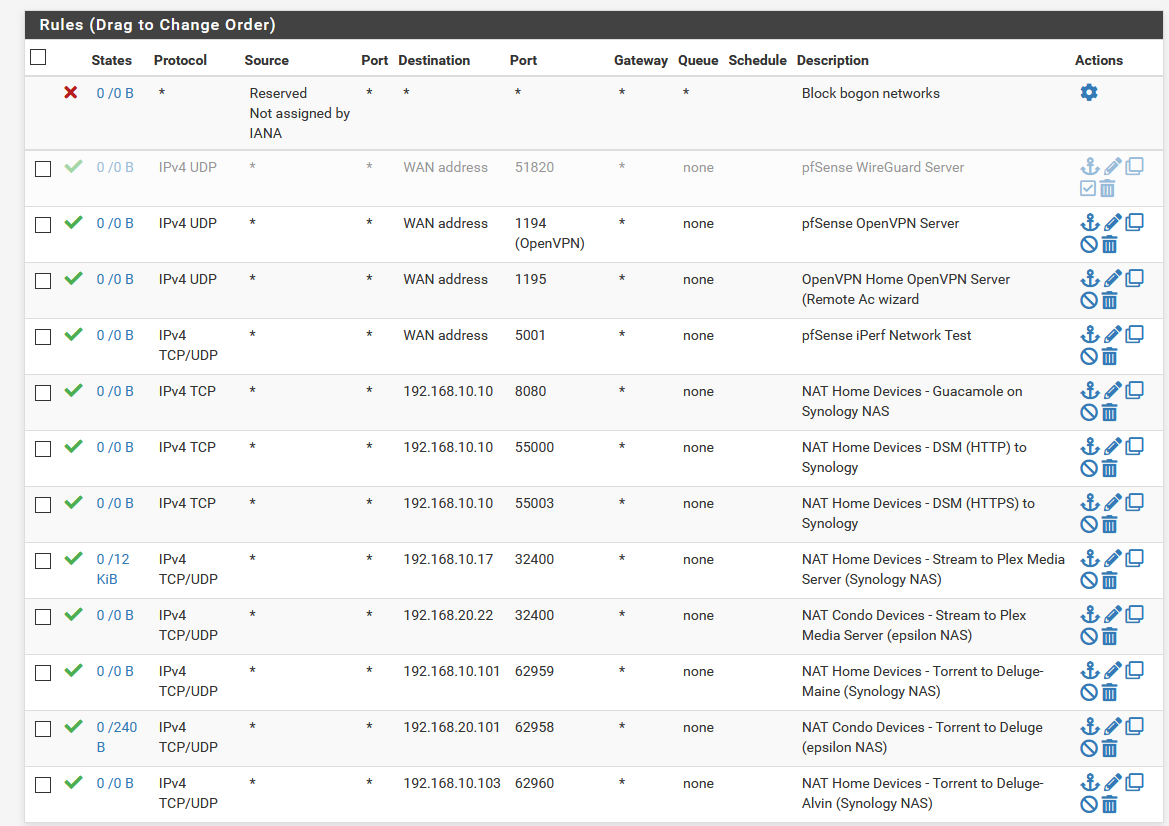
I don't have any other rules for dst_port=51820. Here are all my WAN rules:
-
Run:
pfctl -ss -vvvvFind the state(s) open with port 51820. Note the rule number that opened them.
Now run:
pfctl -sr -vvvvCheck what rule opened the state.
Steve
-
With the WAN rule enabled, running "pfctl -sr -vvvv" shows the user rule I created and like I said, the open state is as expected:
pfctl -ss -vvvv | grep 51820 igb0 udp {server public IP}:51820 <- {client public IP}:19988 MULTIPLE:MULTIPLE pfctl -sr -vvvv @68(1613966106) pass in quick on igb0 reply-to (igb0 {server WAN gateway IP}) inet proto udp from any to {server public IP} port = 51820 keep state label "USER_RULE: pfSense WireGuard Server" [ Evaluations: 21757 Packets: 6025 Bytes: 4078532 States: 1 ] [ Inserted: pid 28901 State Creations: 1 ]Right after disabling the rule and deleting the open state on the server, it opens a new state but this time in reverse and naturally no rules are triggered because it becomes an outbound call:
pfctl -ss -vvvv | grep 51820 igb0 udp {server public IP}:51820 -> {client public IP}:19988 MULTIPLE:MULTIPLE pfctl -sr -vvvv @68(1613966106) pass in quick on igb0 reply-to (igb0 {server WAN gateway IP}) inet proto udp from any to {server public IP} port = 51820 keep state label "USER_RULE: pfSense WireGuard Server" [ Evaluations: 24229 Packets: 6933 Bytes: 4638020 States: 0 ] [ Inserted: pid 28901 State Creations: 1 ]So how do both sides have outbound connections and still achieve a tunnel? I'm just curious here. The open state on the client side never changes direction. It's always client to server and the source and destination port is always 51820.
-
You have
client IPtwice in the second state. I assume that's a typo?Are you saying the state that opens without the WAN rule enabled shows it was created by the same rule number?
Steve
-
@stephenw10 said in (IPsec outbound NAT to interface address) Reply traffic destination IP not being translated back to original source IP:
You have
client IPtwice in the second state. I assume that's a typo?Are you saying the state that opens without the WAN rule enabled shows it was created by the same rule number?
Steve
Edited, sorry about that.
No. After I disable the WAN rule and delete the open state on the server side, a new state in the server side is recreated but seems to be outbound. So the same rule number does not show it was used because naturally it is outbound. But then after a while (like how I checked again now), the open state on the server seems to be as expected again BUT the rule state details under the WAN tab does not reflect the correct "bytes".
-
Ok, but the rule that is creating that state is not '@68' I assume?
I imagine the WireGuard process has a record of the client IP and source port and start sending traffic back to it. The 'allow everything out' rule will pass that and create a new state. Since that isn't the rule on WAN that doesn't show the traffic.
If you removed the rule on the server side WAN and then restarted WireGuard or rebooted I would expect it to fail to come back up.
Steve
-
@stephenw10 said in (IPsec outbound NAT to interface address) Reply traffic destination IP not being translated back to original source IP:
Ok, but the rule that is creating that state is not '@68' I assume?
I imagine the WireGuard process has a record of the client IP and source port and start sending traffic back to it. The 'allow everything out' rule will pass that and create a new state. Since that isn't the rule on WAN that doesn't show the traffic.
If you removed the rule on the server side WAN and then restarted WireGuard or rebooted I would expect it to fail to come back up.
Steve
Correct, it's not '@68' for sure because the connection was outbound.
What you're saying makes sense. Since the client side has an open state, the server can reach it on that client IP and source port outbound. That's actually clever.
That will be a good test. I will expect it to fail too. I'll try later and report back.
However, do you have any ideas on the inaccurate "bytes" on the rule state details?
And why I see the "matchaddr failed" errors on both sides now?
-
@kevindd992002 said in (IPsec outbound NAT to interface address) Reply traffic destination IP not being translated back to original source IP:
matchaddr failed
Yeah that should not be there. Do you have more that one peer defined?
https://redmine.pfsense.org/issues/11502Steve
-
Not at all. I only have one peer serup on both sides.
-
Hmm

-
@stephenw10 said in (IPsec outbound NAT to interface address) Reply traffic destination IP not being translated back to original source IP:
Hmm

Can I file it as a bug?
-
Yes, if you have details there and can replicate it.
-
I think I'm seeing the same behavior.
My setup might be a bit different but I have two netgate appliances: SG-3100 & SG-5100 and site2site wireguard vpn setup according to the howto. After disabling the WAN inbound firewall rules for 51820 on both devices and even killing states the link still comes online.Since disabling the rules didn't work I set an explicit reject instead of allow, but connection still comes up... So it seems wireguard doesn't care about my WAN rules.
-
That is expected if both sides have a remote IP and there in nothing NATing in between them. Both ends open an outbound UDP state with 51280 as the source and destination port. The traffic arriving from the other side can use that open state to connect.
This should be a new thread in the WireGuard or Firewall subs at this point. It's no longer IPSec related at all.

Steve
-
@stephenw10
Thanks for the answer, not my intention to hijack the post. It just seemed relevant to the WG related questions. You are correct both sides have remote IP defined, but also explicit firewall WAN -rules to reject the connection.Is this expected, even though I restarted one of the firewalls (e.g no active states)
-
If the reject rules are inbound they won't do anything over the default block rule. The default outbound allow rules will still allow the state to open on each end letting the traffic enter from the remote side.
Steve
-
Thanks again for the clarification, so this basically means that the WAN inbound rules as in howto are not necessary at all in this scenario?
https://docs.netgate.com/pfsense/en/latest/recipes/wireguard-s2s.html
Wish you a great day.
-
There is no harm in adding them to the specific remote IPs and it may allow the tunnel to come up faster. Without then it can only establish once both sides are sending outbound traffic.
Steve