Policy Based Routing to single Remote IP
-
Hello, I'm trying to use policy based routing to send all traffic to a single remote ip address over a VPN.
I'm a novice user so I'm using and adapting tutorials i have found in various places. However i have never found a guide that does exactly what i'm looking for so part of me thinks that its not possible for some reason that is beyond my understanding :) all guides i have found focus on routing traffic from a local machine over the vpn.
This https://www.infotechwerx.com/blog/Creating-Policy-Route-to-Send-All-Traffic-Host-Through-OpenVPN is what i have most recently been trying to follow and i have done everything up to the final stage of configuring the outbound NAT.
here i have replaced their final mapping with this where my remote ip has been included in the referenced alias.

however it still doesn't work...
so:
question 1 - is this possible? or is it just not possible to configure outbound NAT like this?
2 - if it is would someone be so kind as to highlight where i have gone wrong?cheers!
-
@spaceboy
The NAT rule seems to be correct. But that is NAT and does no routing.Policy routing is done by firewall rule with having a gateway set: https://docs.netgate.com/pfsense/en/latest/multiwan/policy-route.html
You have to assign an interface to the OpenVPN client instance first. Then you get a gateway which you can use in the policy routing rule.
-
@viragomann thanks. yep sorry i should have said. i previously:
1 set up the vpn and confirmed it got an ip address
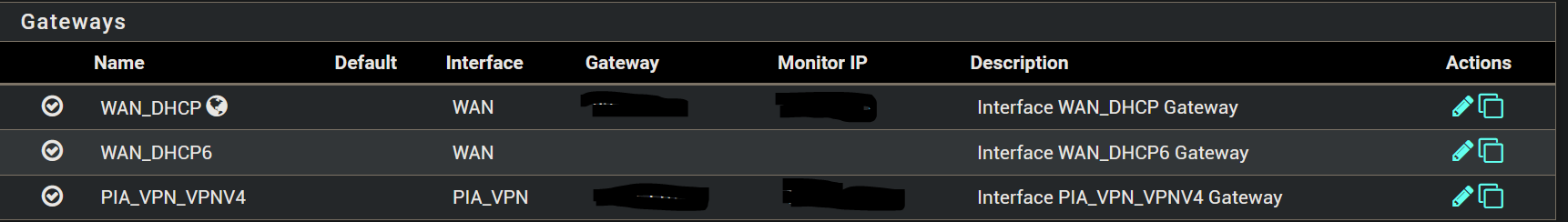
2 assigned the vpn to a interface and verified that the gateway existed
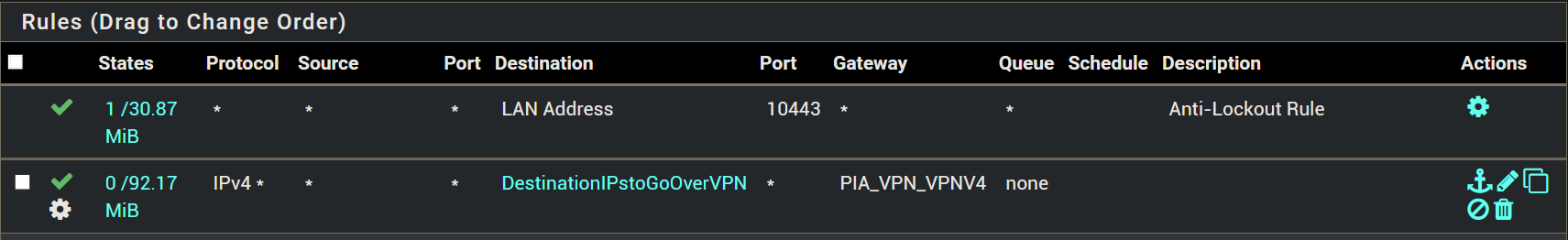
3 set the following firewall on LAN
4 and then tried to configure outbound NAT but adapting the instructions in the linked thread as per my first postcheers!
-
@spaceboy
From what I can see, all look well.
Is the outbound NAT set to hybrid mode?How did you determine that it doesn't work? No connection does not necessarily mean that it is not routed over the VPN.
For testing add a public show-your-IP site to your alias like whatismyipaddress.com or whatever and check your IP. -
@viragomann hmmm you are right. it does work :) when i add the ip address for whatismyipaddress.com to the alias the vpn ip address is reported.
ok there's something else flawed in my logic somewhere. its probably more complicated than i'm thinking.
i'm trying to access something on a site, lets call it myurl.com. if i ping that i get the ip address which i have added to the alias. but i note that i can ping the url and ip address regardless of whether the vpn is up or not. but streaming from myurl.com is only possible when the vpn is up. therefore i guess there is some redirect from myurl.com to some other site/ipaddress and its actually the secondary address that is being blocked by my isp.
i've also run tracert on myurl.com and it gives me a load of other ip addresses but i'm not really sure what that is telling me.
any ideas? no worries if not, there is a more complicated workaround :)
thanks for your help!
-
@spaceboy said in Policy Based Routing to single Remote IP:
therefore i guess there is some redirect from myurl.com to some other site/ipaddress and its actually the secondary address that is being blocked by my isp.
Don't know, how you access it, but yes, that's possible. For instance when accessing an HTTP site, there may be external links in the HTML, which should also be accessed from the same source IP.
To investigate, route the whole traffic from the client device over the vpn, then assess myurl.com while you sniff its traffic. So you will get all IPs you need to route over the VPN.
-
@viragomann with wireshark or something similar? i don't know it but i'm sure i can work it out. ta
-
@spaceboy
You can do that on pfSense directly with Diagnostic > Packet Capture.
Select the interface the client is connected to and enter its IP and start the capture. Access the remote site, then stop the capture to see the result. You will find all IPs the client had called.However, it would be more reliable to know the host names, because a host name can be resolved to multiple IP, while the client only call one of it on a single access.
Since I don't know what your client really tries to access, I'm in the dark here.