Need help with my VLAN firewall rules to make sure they do what I think they do
-
Yeah I agree with the comments on that - that is a HORRIBLE solution to an issue of some local dns sucking..
Looks like they are changing it to output info, for those that block dns..
Since when does MS dns fail to return txt records? I don't see any SRV mentioned in that?
-
@johnpoz
My bad assumed they used a SRV not a TXT -
My main dns'es are two local bind9 servers.
Everything else , including pihole & unbound uses thosePrimary reason i had them running before pfSense was installed.
Use them for DNS & DHCP , and get the full ISC features.And i can do dynamic DHCP updates wo. the dreaded unbound dead time
-
My pihole is currently up to date..
root@pi-hole:/home/pi# pihole -up [i] Checking for updates... [i] Pi-hole Core: up to date [i] Web Interface: up to date [i] FTL: up to date [✓] Everything is up to date! root@pi-hole:/home/pi#But I will for sure try and test this next time an update is out.. I have just added a block any other dns on the piholes vlan.. I was blocking dot and doh.. It didn't attempt to check any other dns when I asked it to see if update - but maybe it only does that if there is an update?
-
@bingo600 said in Need help with my VLAN firewall rules to make sure they do what I think they do:
Re: Lan net vs Lan address (pulldown selections)
Lan address is the specific interface adresss : ie. 192.168.1.1Oh! I see my mistake now.
Lan net is the defined network : ie. 192.168.1.0/24
For allowing any (on the Lan) to send DNS req. to the interface i would do.
IF : LAN
AF: IPv4
Proto: TCP/UDP
SRC: Lan net
Dest: Lan address (Only matches The interface ip)
Port: DNSAwesome. Thank you!
@bingo600 said in Need help with my VLAN firewall rules to make sure they do what I think they do:
If DNS to "any" was allowed (while the DNS forward rule was in place) , the request to 8.8.8.8 would be rewritten to 127.0.0.1 once the package was entering the pfSense , and the APP would still get a DNS answer (from pfSense).
Wouldn't a port forward rule take care of this? Any request from a client on
:53gets redirected to127.0.0.1(pfSense)?@johnpoz said in Need help with my VLAN firewall rules to make sure they do what I think they do:
Not saying you can not stop something from talking to DNS you don't want it to - my point is redirection of traffic hiding from the client that it not talking to who it thinks it is talking to is not good practice.
Totally fair. But as I am just starting out in my journey, I will set it like this for a while and see how ti works. I'll redo everything in a few months anyway -- once I understand things better -- and then I'll see how I set up my DNS.
--
I really do appreciate all of the time y'all have been putting in to help me. I am a big fan/supporter of paying those who help when I can. Teachers in schools get paid, so should teachers elsewhere. LMK if I can return the fair monetarily.
Also, Happy Holidays everyone!
-
I have localhost as resolver on the pihole DEB10
dns-nameservers 127.0.0.1And pihole is using my bind9's as upstream resolvers (on the same L2) - That failed during the updates.
Then i made a specific allow pihole/32 to any - dns
And it updated.After update i disabled that one again
-
@imthenachoman said in Need help with my VLAN firewall rules to make sure they do what I think they do:
LMK if I can return the fair monetarily.
My (adequate) payment is to know i helped someone else that has an issue. - We have all been there.
And i hope they will help someone else in the same way.Also, Happy Holidays everyone!
You too
Edit: There is an implicit "thank you" method here on the forum.
Click the "Thumbs up icon" in the bottom of the post you like.
That gives the poster a +1 on helpfull posts./Bingo
-
I have been a naughty boy

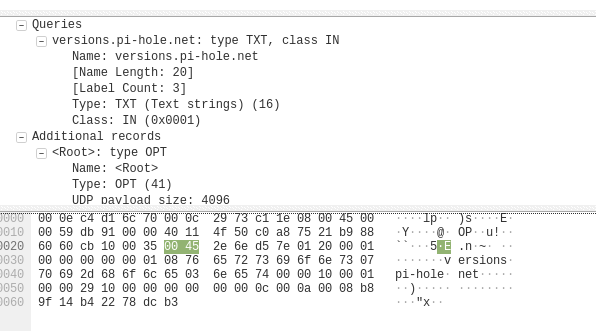
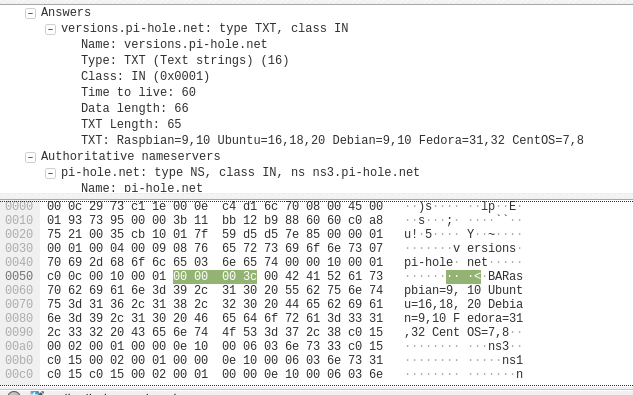
And hadn't updated mine.Here's a "sniff" of my pihole ip , w. port 53 tcp/udp during a "NS1 allowed" update.
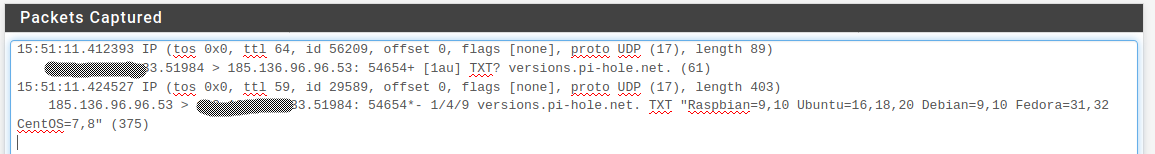
Wo. allowing "NS1" it barfs.
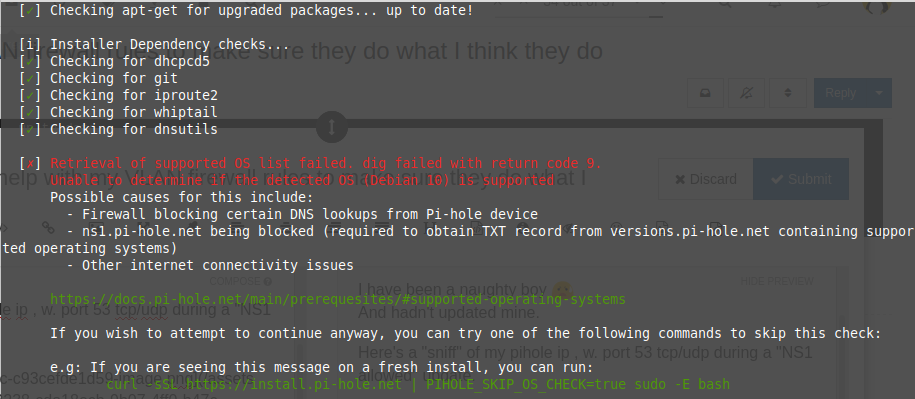
/Bingo -
Why are they doing a directed query? What reason is given - that AD or MS dns does not allow for TXT queries? That is utter BS plain and simple..
I am not buying the reason for doing this at all..
-
@johnpoz
I don't have anything w M$ DNS
If you do you could try the dig they use here.https://github.com/pi-hole/pi-hole/commit/0ff32c3629220f386a45c14d8982aaaf128aa47f
If working it should give the same answer as in my sniff above i suppose.
Or the pcap here
-
-
My dig works fine.. My question - is why are they doing a directed query vs just doing a normal query for the TXT record.. from the one statement it seems that AD dns has some issue? Which is BS..
Do a query using whatever dns the OS is currently set to use - if that fails, then tell the user.. Hard coding some directed query to some specific NS is just utter BS.
That is exactly what applications are doing - to bypass pihole ;) That they would do the same thing is nuts.
-
Yes if you want want network X to talk to ssh to anything on network Y, then the dest would net Y..
-
@johnpoz Rock on. Thanks!
-
@johnpoz said in Need help with my VLAN firewall rules to make sure they do what I think they do:
Do a query using whatever dns the OS is currently set to use - if that fails, then tell the user.. Hard coding some directed query to some specific NS is just utter BS.
Seems like you're right for my OS (here linux mint)
Having pfSense unbound as DNS (that forwards to my bind9's)$ dig +short -t txt versions.pi-hole.net "Raspbian=9,10 Ubuntu=16,18,20 Debian=9,10 Fedora=31,32 CentOS=7,8"That they would do the same thing is nuts.
Yes ... Seems a bit contradictive to their own purpose
/Bingo
-
Wonder if the pfSense DNS forward would have caught that one , and made the problem go away ....
-
Yeah a redirect would of worked here.. But what sucks is why and the F should you have to do that.. What is wrong with these people?
If you want to check some dns txt entry for something that is fine. But there is ZERO reason to direct that specifically to some ns..
Do your query - using whatever DNS the OS is pointed to... If it doesn't resolve - then post up an error.. Could not resolve xyz..
Hard coding trying to talk to some specific NS is not the way to go about it.. I just don't get how the makers of a software that allows users to control their own local dns thinks its a smart idea to bypass the local dns? WTF???
If you want to say point to some public dns, when NO local dns is provided - ok, I mean you are setting up dns software and all.. And you never know what some user might have borked up.. But if the box has local dns - bypassing that to check something is just plain wrong.
-
@johnpoz Its very simple.
Its called ad marketing.
The more people tend to use piholes, the more ad engines would query hard coded ip's for dns.Needles to say that ipv6 has no way to redirect port 53 requests, making it all too difficult.
And I have seen mobile phones just doing an ipv6 dns request to google v6 dns to see if ipv6 connectivity exists.
If it doesn't succeed, ipv6 is switched off silently. -
IMHO that doesn't make sense.
I was thinking maybe it was some kind of tracking, to get the "real" ip of the pihole machine. But since you do an update right after, you are going to reveal your ip to them anyway.
So that doesn't make sense either.It seems to be a "klugde" to circumvent a problem that doesn't exist.
/Bingo
-
And I have seen mobile phones just doing an ipv6 dns request to google v6 dns to see if ipv6 connectivity exists.
Thats not what its doing - its doing a specific query to a specific IPv4 address.. I am curious if the query is done via hard coded IP, of if it has to lookup ns1.pihole.net first?
I'm thinking @bingo600 is on the right track with its some kludge to work around something that is not actually a problem..