Vlans and pfBlockerNG implementation
-
I have just started adding Vlans to my network and trying to figure out the proper way to have them also go through pfBlockerNG. From what I have read it seems there might be a few different ways to do it so looking more for the proper.
It is currently working on my main LAN so now I need to add it to my Vlans.Thanks
-
Ticking the floating rules options, you will get it enabled to all vlans.
Selecting the interfaces, would enable it only for the vlans selected.
-
I have that like you mentioned before but when I am on Vlan4 I can't ping or browse the DNSBL VIP Alias.
-
@cburbs That happens because you blocked 10.10.10.1 when you blocked internal networks.
You can simple change your internal networks block rule, to allow only your vlans and not the entire rfc1918.Or, create a rule allowing connections to 10.10.10.1
Did you understand how firewall rules work in our previous conversation?
-
Yeah I just added a rule at the top now.
I just saw this and assume it would be simliar if enabled.
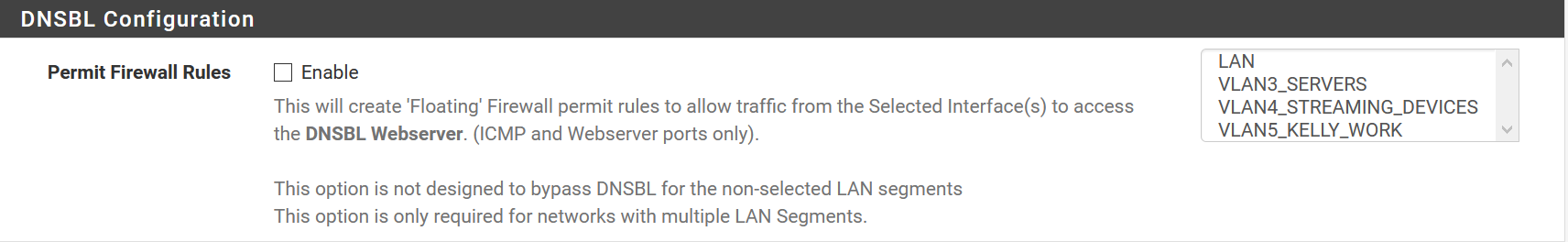
The Floating rule would be easier for setup but I have read people avoid them as it is easier to troubleshoot issues per lan/vlan by assigning rules per lan/vlan. Thoughts/opinions on this one?
-
@cburbs Actually, that is totally up to the user..
In my case, I only filter one VLAN through pfblocker/dnsbl, so I don't use the floating rule feature of pfblocker. I have it only in my LAN.
Guest, wifi and etc are not being filtered by pfblocker/dnsbl.
I wouldn't enable that, because if one day, a new vlan is added and this VLAN wouldn't need the pfblocker filter, I would have to change pfblocker setup, instead of just ticking or removing the vlan from pfblocker configuration.
As I said, that is totally up to the user..
-
I never thought about the logs perspective..
I think that wouldn't be an issue, as you have the reports tab in pfblocker, which would give you a pretty good summary about what is happening..
-
@mcury
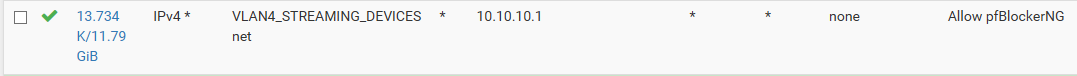
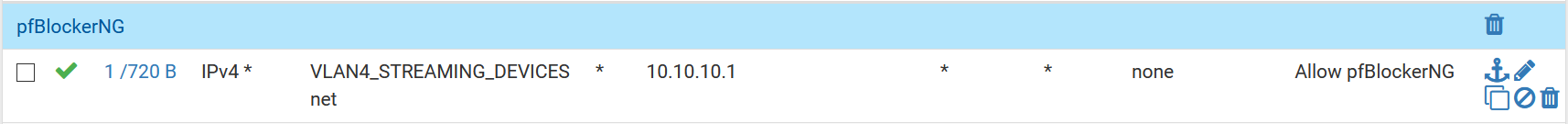
I am just adding each Vlan to the "Outbound Firewall Rules" under the IP tab in pfBlockerNG.Then Each Vlan has this rule towards the top before the block firewall/Internal rules